Report
Share
Recommended
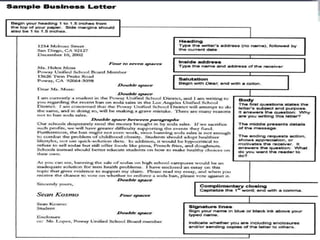
Sample of Business Document and Hierarchy

This document contains samples of various business documents and formats, organized in a hierarchy. It includes advertisements, memorandums, charts, reports, faxes, tables, announcements, notices, forms, letters and more. Each document provides an example of its format and purpose. The final section displays a hierarchy of a service firm and job descriptions for different functions within the company.
Digital marketing strategy and planning | About Business

Introduction
Respondent profiles
About Business
Adoption of digital transformation programs
Investing In Digital Marketing
Top Online Marketing Channels
What should the planning horizon for digital planning be?
Integration Of Digital And Traditional Marketing Activities
EXECUTIVE SUMMARY
Intro to social network analysis | What is Network Analysis? | History of (So...

Social network analysis examines the connections between individuals, groups, organizations, or other social entities. It focuses on interactions rather than individual behavior. Network analysis can be applied across many disciplines to study how the structure of relationships influences functioning. Early research in fields like sociology, anthropology, and educational psychology helped develop concepts still used today, such as examining homophily and interaction patterns. Key concepts in network analysis include nodes, edges, degree, clustering coefficients, and graph diameter. "Small world" networks are highly clustered with short path lengths, characteristics seen in many real-world networks. Social capital research also examines how network connections impact groups, organizations, and individuals.
Marketing ethics and social responsibility | Criticisms of Marketing

Identify the major social criticisms of marketing.
Define consumerism and environmentalism and explain how they affect marketing strategies.
Describe the principles of socially responsible marketing.
Explain the role of ethics in marketing.
understanding and capturing customer value | What Is a Price?

Discuss the importance of understanding customer value perceptions and company costs when setting prices.
Identify and define the other important internal and external factors affecting a firm’s pricing decisions.
Describe the major strategies for pricing imitative and new products.
Explain how companies find a set of prices that maximizes the profits from the total product mix.
Discuss how companies adjust their prices to take into account different types of customers and situations.
Discuss key issues related to initiating and responding to price changes.
The marketing environment | Suppliers | Marketing intermediaries

The document summarizes the key elements of a company's marketing environment including:
- The microenvironment comprised of a company's internal operations as well as suppliers, intermediaries, customers, competitors, and publics.
- The macroenvironment including demographic, economic, natural, technological, political, and cultural forces outside a company's control that shape opportunities and threats.
- How changes in these environments like population aging, income shifts, resource scarcity, regulations, and cultural values influence marketing decisions and strategies.
- Approaches companies take to proactively manage their environments like lobbying, partnerships, and influencing public opinion.
strategic planning | Customer Relationships | Partnering to Build 

Explain companywide strategic planning and its four steps.
Discuss how to design business portfolios and growth strategies.
Explain marketing’s role in strategic planning and how marketing works with its partners to create and deliver customer value.
Describe the elements of a customer-driven marketing strategy and mix, and the forces that influence it.
List the marketing management functions, including the elements of a marketing plan.
Digital marketing | what is marketing?

Define marketing and the marketing process.
Explain the importance of understanding customers and identify the five core marketplace concepts.
Identify the elements of a customer-driven marketing strategy and discuss the marketing management orientations.
Discuss customer relationship management and creating value for and capturing value from customers.
Describe the major trends and forces changing the marketing landscape.
Recommended
Sample of Business Document and Hierarchy

This document contains samples of various business documents and formats, organized in a hierarchy. It includes advertisements, memorandums, charts, reports, faxes, tables, announcements, notices, forms, letters and more. Each document provides an example of its format and purpose. The final section displays a hierarchy of a service firm and job descriptions for different functions within the company.
Digital marketing strategy and planning | About Business

Introduction
Respondent profiles
About Business
Adoption of digital transformation programs
Investing In Digital Marketing
Top Online Marketing Channels
What should the planning horizon for digital planning be?
Integration Of Digital And Traditional Marketing Activities
EXECUTIVE SUMMARY
Intro to social network analysis | What is Network Analysis? | History of (So...

Social network analysis examines the connections between individuals, groups, organizations, or other social entities. It focuses on interactions rather than individual behavior. Network analysis can be applied across many disciplines to study how the structure of relationships influences functioning. Early research in fields like sociology, anthropology, and educational psychology helped develop concepts still used today, such as examining homophily and interaction patterns. Key concepts in network analysis include nodes, edges, degree, clustering coefficients, and graph diameter. "Small world" networks are highly clustered with short path lengths, characteristics seen in many real-world networks. Social capital research also examines how network connections impact groups, organizations, and individuals.
Marketing ethics and social responsibility | Criticisms of Marketing

Identify the major social criticisms of marketing.
Define consumerism and environmentalism and explain how they affect marketing strategies.
Describe the principles of socially responsible marketing.
Explain the role of ethics in marketing.
understanding and capturing customer value | What Is a Price?

Discuss the importance of understanding customer value perceptions and company costs when setting prices.
Identify and define the other important internal and external factors affecting a firm’s pricing decisions.
Describe the major strategies for pricing imitative and new products.
Explain how companies find a set of prices that maximizes the profits from the total product mix.
Discuss how companies adjust their prices to take into account different types of customers and situations.
Discuss key issues related to initiating and responding to price changes.
The marketing environment | Suppliers | Marketing intermediaries

The document summarizes the key elements of a company's marketing environment including:
- The microenvironment comprised of a company's internal operations as well as suppliers, intermediaries, customers, competitors, and publics.
- The macroenvironment including demographic, economic, natural, technological, political, and cultural forces outside a company's control that shape opportunities and threats.
- How changes in these environments like population aging, income shifts, resource scarcity, regulations, and cultural values influence marketing decisions and strategies.
- Approaches companies take to proactively manage their environments like lobbying, partnerships, and influencing public opinion.
strategic planning | Customer Relationships | Partnering to Build 

Explain companywide strategic planning and its four steps.
Discuss how to design business portfolios and growth strategies.
Explain marketing’s role in strategic planning and how marketing works with its partners to create and deliver customer value.
Describe the elements of a customer-driven marketing strategy and mix, and the forces that influence it.
List the marketing management functions, including the elements of a marketing plan.
Digital marketing | what is marketing?

Define marketing and the marketing process.
Explain the importance of understanding customers and identify the five core marketplace concepts.
Identify the elements of a customer-driven marketing strategy and discuss the marketing management orientations.
Discuss customer relationship management and creating value for and capturing value from customers.
Describe the major trends and forces changing the marketing landscape.
Fundamentals of Computer Design including performance measurements & quantita...

This document provides an overview of the Computer Architecture course CNE-301 taught by Irfan Ali. The course outline covers topics like fundamentals of computer design, instruction set design, pipelining, memory hierarchy, multiprocessors, and case studies. Recommended books are also mentioned. The document then provides background on computer architecture and organization, the history of computers from first to fourth generations, and embedded systems.
Dealing with exceptions Computer Architecture part 2

The document discusses exceptions in computer architecture. It describes two types of exceptions - interrupts and traps. Interrupts are caused by external events like I/O requests, while traps are caused by internal events like arithmetic overflow. When an exception occurs, the pipeline must stop executing the offending instruction, save state like the program counter, and jump to an exception handler. Handling exceptions in a pipelined processor is challenging as it can disrupt instruction flow. The document outlines some of the techniques used to handle exceptions in a pipeline, like writing exception information to registers and flushing instructions after the exception.
Dealing with Exceptions Computer Architecture part 1

The document discusses exceptions in computer architecture. It describes two types of exceptions - interrupts and traps. Interrupts are caused by external events like I/O requests, while traps are caused by internal events like arithmetic overflow. When an exception occurs, the pipeline must stop executing the offending instruction, save state like the program counter, and jump to an exception handler. Handling exceptions in a pipelined processor is challenging as it can disrupt instruction flow. The document outlines some of the techniques used to handle exceptions in a pipeline, like writing exception information to registers and flushing instructions after the exception.
Pipelining of Processors

The document provides an overview of pipelining in computer processors. It discusses how pipelining works by dividing processor operations like fetch, decode, execute, memory, and write-back into discrete stages that can overlap, improving throughput. Key points made include:
- Pipelining allows multiple instructions to be in different stages of completion at the same time, improving instruction throughput.
- The document uses an example of a sequential laundry process versus a pipelined laundry process to illustrate how pipelining improves efficiency.
- It describes the five main stages of a RISC instruction set pipeline - fetch, decode, execute, memory, and write-back. The work done and data passed between each stage
Instruction Set Architecture (ISA)

This document discusses instruction set architectures (ISAs). It covers four main types of ISAs: accumulator, stack, memory-memory, and register-based. It also discusses different addressing modes like immediate, direct, indirect, register-indirect, and relative addressing. The key details provided are:
1) Accumulator ISAs use a dedicated register (accumulator) to hold operands and results, while stack ISAs use an implicit last-in, first-out stack. Memory-memory ISAs can have 2-3 operands specified directly in memory.
2) Register-based ISAs can be either register-memory (like 80x86) or load-store (like MIPS), which fully separate
differential equation Lecture#14

This lecture will improve your knowledge in differential equation
lecture is by Lecturer AZEEM INAAM of SMI university.
differential equation Lecture#12

This lecture will improve your knowledge in differential equation
lecture is by Lecturer AZEEM INAAM of SMI university.
differential equation Lecture#11

The document discusses higher order non-homogeneous linear differential equations and methods for finding their particular integrals. It defines a general higher order non-homogeneous differential equation and explains that the general solution is the sum of the complementary solution and particular solution. It then presents three rules for finding the particular integral when the forcing term F(x) is an exponential, sine, or cosine function. The rules involve taking derivatives of the differential operator f(D) evaluated at constants related to the exponential, sine, or cosine function.
differential equation Lecture#13

This lecture will improve your knowledge in differential equation
lecture is by Lecturer AZEEM INAAM of SMI university.
differential equation Lecture#10

This lecture will improve your knowledge in differential equation
lecture is by Lecturer AZEEM INAAM of SMI university.
differential equation Lecture#9

This lecture will improve your knowledge in differential equation
lecture is by Lecturer AZEEM INAAM of SMI university.
differential equation Lecture#8

This lecture will improve your knowledge in differential equation
lecture is by Lecturer AZEEM INAAM of SMI university.
differential equation Lecture#7

This lecture will improve your knowledge in differential equation
lecture is by Lecturer AZEEM INAAM of SMI university.
differential equation Lecture#5 

This lecture will improve your knowledge in differential equation
lecture is by Lecturer AZEEM INAAM of SMI university.
differential equation Lecture#3

This lecture will improve your knowledge in differential equation
lecture is by Lecturer AZEEM INAAM of SMI university.
differential equation Lecture #2

This document summarizes lecture 2 on differential equations of first order and first degree. It discusses the definition of a differential equation of first order and first degree as one of the form dy/dx = f(x,y). It then describes two types of these differential equations - variable separable form, where the equation can be written as f(x,y)=M(x)N(y) or f(x,y)=M(x)/N(y), and provides an example of solving this type by integrating both sides.
DIFFERENTIAL EQUATION Lecture #1

This document provides an overview of key concepts in differential equations:
- A differential equation involves independent variables, dependent variables, and their derivatives.
- An ordinary differential equation contains one independent variable and one or more dependent variables.
- A partial differential equation contains more than one independent variable and dependent variables and their partial derivatives.
- The order of a differential equation refers to the order of the highest differential coefficient. The degree refers to the power of the highest order differential coefficient.
- Differential equations can be linear or non-linear depending on whether the dependent variable and its derivatives occur only in the first degree.
- Differential equations can be formed by differentiating ordinary equations and eliminating arbitrary constants.
SOFTWARE ENGINEERING 

This slide is for software engineering subject which may help you to better understanding. You can also gain knowledge in software engineering subject.
Automata

This document provides information about a course on the theory of automata, including:
- The course title is Theory of Computer Science [Automata] and is intended for students pursuing a BCS degree in their fifth semester.
- Key topics that will be covered include finite automata, regular expressions, context-free grammars, pushdown automata, and Turing machines.
- Reference textbooks and materials are listed to support student learning in the course over 18 weeks of lectures and labs.
Automata

The document provides information about a course on the theory of automata. It includes details such as the course title, prerequisites, duration, lectures, laboratories, and topics to be covered. The topics include finite automata, deterministic finite automata, non-deterministic finite automata, regular expressions, properties of regular languages, context-free grammars, pushdown automata, and Turing machines. It also lists reference books and textbooks, and the marking scheme for the course.
Satta Matka Dpboss Matka Guessing Kalyan Chart Indian Matka Kalyan panel Chart

Satta Matka Dpboss Matka Guessing Kalyan Chart Indian Matka Kalyan panel Chart➒➌➎➏➑➐➋➑➐➐Dpboss Matka Guessing Satta Matka Kalyan Chart Indian Matka
SATTA MATKA SATTA FAST RESULT KALYAN TOP MATKA RESULT KALYAN SATTA MATKA FAST RESULT MILAN RATAN RAJDHANI MAIN BAZAR MATKA FAST TIPS RESULT MATKA CHART JODI CHART PANEL CHART FREE FIX GAME SATTAMATKA ! MATKA MOBI SATTA 143 spboss.in TOP NO1 RESULT FULL RATE MATKA ONLINE GAME PLAY BY APP SPBOSSCall 8867766396 Satta Matka Dpboss Matka Guessing Satta batta Matka 420 Satta...

CALL 8867766396 SATTA MATKA | DPBOSS | KALYAN MAIN BAZAR | FAST MATKA | DPBOSS GUESSING | TARA MATKA | KALYAN CHART | MATKA BOSS
More Related Content
More from Gaditek
Fundamentals of Computer Design including performance measurements & quantita...

This document provides an overview of the Computer Architecture course CNE-301 taught by Irfan Ali. The course outline covers topics like fundamentals of computer design, instruction set design, pipelining, memory hierarchy, multiprocessors, and case studies. Recommended books are also mentioned. The document then provides background on computer architecture and organization, the history of computers from first to fourth generations, and embedded systems.
Dealing with exceptions Computer Architecture part 2

The document discusses exceptions in computer architecture. It describes two types of exceptions - interrupts and traps. Interrupts are caused by external events like I/O requests, while traps are caused by internal events like arithmetic overflow. When an exception occurs, the pipeline must stop executing the offending instruction, save state like the program counter, and jump to an exception handler. Handling exceptions in a pipelined processor is challenging as it can disrupt instruction flow. The document outlines some of the techniques used to handle exceptions in a pipeline, like writing exception information to registers and flushing instructions after the exception.
Dealing with Exceptions Computer Architecture part 1

The document discusses exceptions in computer architecture. It describes two types of exceptions - interrupts and traps. Interrupts are caused by external events like I/O requests, while traps are caused by internal events like arithmetic overflow. When an exception occurs, the pipeline must stop executing the offending instruction, save state like the program counter, and jump to an exception handler. Handling exceptions in a pipelined processor is challenging as it can disrupt instruction flow. The document outlines some of the techniques used to handle exceptions in a pipeline, like writing exception information to registers and flushing instructions after the exception.
Pipelining of Processors

The document provides an overview of pipelining in computer processors. It discusses how pipelining works by dividing processor operations like fetch, decode, execute, memory, and write-back into discrete stages that can overlap, improving throughput. Key points made include:
- Pipelining allows multiple instructions to be in different stages of completion at the same time, improving instruction throughput.
- The document uses an example of a sequential laundry process versus a pipelined laundry process to illustrate how pipelining improves efficiency.
- It describes the five main stages of a RISC instruction set pipeline - fetch, decode, execute, memory, and write-back. The work done and data passed between each stage
Instruction Set Architecture (ISA)

This document discusses instruction set architectures (ISAs). It covers four main types of ISAs: accumulator, stack, memory-memory, and register-based. It also discusses different addressing modes like immediate, direct, indirect, register-indirect, and relative addressing. The key details provided are:
1) Accumulator ISAs use a dedicated register (accumulator) to hold operands and results, while stack ISAs use an implicit last-in, first-out stack. Memory-memory ISAs can have 2-3 operands specified directly in memory.
2) Register-based ISAs can be either register-memory (like 80x86) or load-store (like MIPS), which fully separate
differential equation Lecture#14

This lecture will improve your knowledge in differential equation
lecture is by Lecturer AZEEM INAAM of SMI university.
differential equation Lecture#12

This lecture will improve your knowledge in differential equation
lecture is by Lecturer AZEEM INAAM of SMI university.
differential equation Lecture#11

The document discusses higher order non-homogeneous linear differential equations and methods for finding their particular integrals. It defines a general higher order non-homogeneous differential equation and explains that the general solution is the sum of the complementary solution and particular solution. It then presents three rules for finding the particular integral when the forcing term F(x) is an exponential, sine, or cosine function. The rules involve taking derivatives of the differential operator f(D) evaluated at constants related to the exponential, sine, or cosine function.
differential equation Lecture#13

This lecture will improve your knowledge in differential equation
lecture is by Lecturer AZEEM INAAM of SMI university.
differential equation Lecture#10

This lecture will improve your knowledge in differential equation
lecture is by Lecturer AZEEM INAAM of SMI university.
differential equation Lecture#9

This lecture will improve your knowledge in differential equation
lecture is by Lecturer AZEEM INAAM of SMI university.
differential equation Lecture#8

This lecture will improve your knowledge in differential equation
lecture is by Lecturer AZEEM INAAM of SMI university.
differential equation Lecture#7

This lecture will improve your knowledge in differential equation
lecture is by Lecturer AZEEM INAAM of SMI university.
differential equation Lecture#5 

This lecture will improve your knowledge in differential equation
lecture is by Lecturer AZEEM INAAM of SMI university.
differential equation Lecture#3

This lecture will improve your knowledge in differential equation
lecture is by Lecturer AZEEM INAAM of SMI university.
differential equation Lecture #2

This document summarizes lecture 2 on differential equations of first order and first degree. It discusses the definition of a differential equation of first order and first degree as one of the form dy/dx = f(x,y). It then describes two types of these differential equations - variable separable form, where the equation can be written as f(x,y)=M(x)N(y) or f(x,y)=M(x)/N(y), and provides an example of solving this type by integrating both sides.
DIFFERENTIAL EQUATION Lecture #1

This document provides an overview of key concepts in differential equations:
- A differential equation involves independent variables, dependent variables, and their derivatives.
- An ordinary differential equation contains one independent variable and one or more dependent variables.
- A partial differential equation contains more than one independent variable and dependent variables and their partial derivatives.
- The order of a differential equation refers to the order of the highest differential coefficient. The degree refers to the power of the highest order differential coefficient.
- Differential equations can be linear or non-linear depending on whether the dependent variable and its derivatives occur only in the first degree.
- Differential equations can be formed by differentiating ordinary equations and eliminating arbitrary constants.
SOFTWARE ENGINEERING 

This slide is for software engineering subject which may help you to better understanding. You can also gain knowledge in software engineering subject.
Automata

This document provides information about a course on the theory of automata, including:
- The course title is Theory of Computer Science [Automata] and is intended for students pursuing a BCS degree in their fifth semester.
- Key topics that will be covered include finite automata, regular expressions, context-free grammars, pushdown automata, and Turing machines.
- Reference textbooks and materials are listed to support student learning in the course over 18 weeks of lectures and labs.
Automata

The document provides information about a course on the theory of automata. It includes details such as the course title, prerequisites, duration, lectures, laboratories, and topics to be covered. The topics include finite automata, deterministic finite automata, non-deterministic finite automata, regular expressions, properties of regular languages, context-free grammars, pushdown automata, and Turing machines. It also lists reference books and textbooks, and the marking scheme for the course.
More from Gaditek (20)
Fundamentals of Computer Design including performance measurements & quantita...

Fundamentals of Computer Design including performance measurements & quantita...
Dealing with exceptions Computer Architecture part 2

Dealing with exceptions Computer Architecture part 2
Dealing with Exceptions Computer Architecture part 1

Dealing with Exceptions Computer Architecture part 1
Recently uploaded
Satta Matka Dpboss Matka Guessing Kalyan Chart Indian Matka Kalyan panel Chart

Satta Matka Dpboss Matka Guessing Kalyan Chart Indian Matka Kalyan panel Chart➒➌➎➏➑➐➋➑➐➐Dpboss Matka Guessing Satta Matka Kalyan Chart Indian Matka
SATTA MATKA SATTA FAST RESULT KALYAN TOP MATKA RESULT KALYAN SATTA MATKA FAST RESULT MILAN RATAN RAJDHANI MAIN BAZAR MATKA FAST TIPS RESULT MATKA CHART JODI CHART PANEL CHART FREE FIX GAME SATTAMATKA ! MATKA MOBI SATTA 143 spboss.in TOP NO1 RESULT FULL RATE MATKA ONLINE GAME PLAY BY APP SPBOSSCall 8867766396 Satta Matka Dpboss Matka Guessing Satta batta Matka 420 Satta...

CALL 8867766396 SATTA MATKA | DPBOSS | KALYAN MAIN BAZAR | FAST MATKA | DPBOSS GUESSING | TARA MATKA | KALYAN CHART | MATKA BOSS
Creative Web Design Company in Singapore

At Techbox Square, in Singapore, we're not just creative web designers and developers, we're the driving force behind your brand identity. Contact us today.
-- June 2024 is National Volunteer Month --

Check out our June display of books on voluntary organisations
Tata Group Dials Taiwan for Its Chipmaking Ambition in Gujarat’s Dholera

The Tata Group, a titan of Indian industry, is making waves with its advanced talks with Taiwanese chipmakers Powerchip Semiconductor Manufacturing Corporation (PSMC) and UMC Group. The goal? Establishing a cutting-edge semiconductor fabrication unit (fab) in Dholera, Gujarat. This isn’t just any project; it’s a potential game changer for India’s chipmaking aspirations and a boon for investors seeking promising residential projects in dholera sir.
Visit : https://www.avirahi.com/blog/tata-group-dials-taiwan-for-its-chipmaking-ambition-in-gujarats-dholera/
Taurus Zodiac Sign: Unveiling the Traits, Dates, and Horoscope Insights of th...

Dive into the steadfast world of the Taurus Zodiac Sign. Discover the grounded, stable, and logical nature of Taurus individuals, and explore their key personality traits, important dates, and horoscope insights. Learn how the determination and patience of the Taurus sign make them the rock-steady achievers and anchors of the zodiac.
2024-6-01-IMPACTSilver-Corp-Presentation.pdf

IMPACT Silver is a pure silver zinc producer with over $260 million in revenue since 2008 and a large 100% owned 210km Mexico land package - 2024 catalysts includes new 14% grade zinc Plomosas mine and 20,000m of fully funded exploration drilling.
Mastering B2B Payments Webinar from BlueSnap

B2B payments are rapidly changing. Find out the 5 key questions you need to be asking yourself to be sure you are mastering B2B payments today. Learn more at www.BlueSnap.com.
Industrial Tech SW: Category Renewal and Creation

Every industrial revolution has created a new set of categories and a new set of players.
Multiple new technologies have emerged, but Samsara and C3.ai are only two companies which have gone public so far.
Manufacturing startups constitute the largest pipeline share of unicorns and IPO candidates in the SF Bay Area, and software startups dominate in Germany.
How MJ Global Leads the Packaging Industry.pdf

MJ Global's success in staying ahead of the curve in the packaging industry is a testament to its dedication to innovation, sustainability, and customer-centricity. By embracing technological advancements, leading in eco-friendly solutions, collaborating with industry leaders, and adapting to evolving consumer preferences, MJ Global continues to set new standards in the packaging sector.
2022 Vintage Roman Numerals Men Rings

Discover timeless style with the 2022 Vintage Roman Numerals Men's Ring. Crafted from premium stainless steel, this 6mm wide ring embodies elegance and durability. Perfect as a gift, it seamlessly blends classic Roman numeral detailing with modern sophistication, making it an ideal accessory for any occasion.
https://rb.gy/usj1a2
Income Tax exemption for Start up : Section 80 IAC

A presentation on the concept of Exemption of Profits of Start ups from Income Tax
Unveiling the Dynamic Personalities, Key Dates, and Horoscope Insights: Gemin...

Explore the fascinating world of the Gemini Zodiac Sign. Discover the unique personality traits, key dates, and horoscope insights of Gemini individuals. Learn how their sociable, communicative nature and boundless curiosity make them the dynamic explorers of the zodiac. Dive into the duality of the Gemini sign and understand their intellectual and adventurous spirit.
LA HUG - Video Testimonials with Chynna Morgan - June 2024

Have you ever heard that user-generated content or video testimonials can take your brand to the next level? We will explore how you can effectively use video testimonials to leverage and boost your sales, content strategy, and increase your CRM data.🤯
We will dig deeper into:
1. How to capture video testimonials that convert from your audience 🎥
2. How to leverage your testimonials to boost your sales 💲
3. How you can capture more CRM data to understand your audience better through video testimonials. 📊
Hamster Kombat' Telegram Game Surpasses 100 Million Players—Token Release Sch...

Hamster Kombat' Telegram Game Surpasses 100 Million Players—Token Release Schedule Unveiled
ModelingMarketingStrategiesMKS.CollumbiaUniversitypdf

Implicitly or explicitly all competing businesses employ a strategy to select a mix
of marketing resources. Formulating such competitive strategies fundamentally
involves recognizing relationships between elements of the marketing mix (e.g.,
price and product quality), as well as assessing competitive and market conditions
(i.e., industry structure in the language of economics).
Recently uploaded (20)
Satta Matka Dpboss Matka Guessing Kalyan Chart Indian Matka Kalyan panel Chart

Satta Matka Dpboss Matka Guessing Kalyan Chart Indian Matka Kalyan panel Chart
Call 8867766396 Satta Matka Dpboss Matka Guessing Satta batta Matka 420 Satta...

Call 8867766396 Satta Matka Dpboss Matka Guessing Satta batta Matka 420 Satta...
Tata Group Dials Taiwan for Its Chipmaking Ambition in Gujarat’s Dholera

Tata Group Dials Taiwan for Its Chipmaking Ambition in Gujarat’s Dholera
Training my puppy and implementation in this story

Training my puppy and implementation in this story
Taurus Zodiac Sign: Unveiling the Traits, Dates, and Horoscope Insights of th...

Taurus Zodiac Sign: Unveiling the Traits, Dates, and Horoscope Insights of th...
Income Tax exemption for Start up : Section 80 IAC

Income Tax exemption for Start up : Section 80 IAC
Unveiling the Dynamic Personalities, Key Dates, and Horoscope Insights: Gemin...

Unveiling the Dynamic Personalities, Key Dates, and Horoscope Insights: Gemin...
LA HUG - Video Testimonials with Chynna Morgan - June 2024

LA HUG - Video Testimonials with Chynna Morgan - June 2024
Hamster Kombat' Telegram Game Surpasses 100 Million Players—Token Release Sch...

Hamster Kombat' Telegram Game Surpasses 100 Million Players—Token Release Sch...
ModelingMarketingStrategiesMKS.CollumbiaUniversitypdf

ModelingMarketingStrategiesMKS.CollumbiaUniversitypdf
