4 E Dn D Char Sheet Writeable Gd
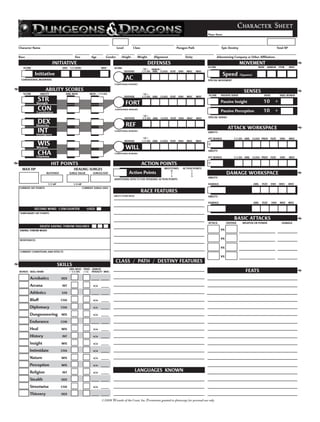
- 1. Print Form Character Sheet Player Name Character Name Level Class Paragon Path Epic Destiny Total XP Race Size Age Gender Height Weight Alignment Deity Adventuring Company or Other Affiliations INITIATIVE DEFENSES MOVEMENT SCORE DEX 1/2 LEVEL MISC SCORE SCORE BASE ARMOR ITEM MISC 10 + ARMOR / DEFENSE 1/2 LVL ABIL CLASS FEAT ENH MISC MISC Initiative Speed (Squares) CONDITIONAL MODIFIERS AC SPECIAL MOVEMENT CONDITIONAL BONUSES ABILITY SCORES SENSES SCORE ABILITY ABIL MOD MOD + 1/2 LVL 10 + SCORE PASSIVE SENSE BASE SKILL BONUS DEFENSE 1/2 LVL ABIL CLASS FEAT ENH MISC MISC STR Passive Insight 10 + Strength FORT CON Constitution CONDITIONAL BONUSES Passive Perception 10 + 10 + DEFENSE 1/2 LVL ABIL CLASS FEAT ENH MISC MISC SPECIAL SENSES DEX Dexterity REF ATTACK WORKSPACE INT Intelligence CONDITIONAL BONUSES ABILITY: 10 + ATT BONUS 1/2 LVL ABIL CLASS PROF FEAT ENH MISC DEFENSE 1/2 LVL ABIL CLASS FEAT ENH MISC MISC WIS + Wisdom WILL ABILITY: CHA Charisma CONDITIONAL BONUSES ATT BONUS 1/2 LVL ABIL CLASS PROF FEAT ENH MISC HIT POINTS ACTION POINTS + MAX HP HEALING SURGES MILESTONES ACTION POINTS 0 1 BLOODIED SURGE VALUE SURGES/DAY Action Points 1 2 DAMAGE WORKSPACE 2 3 ABILITY: ADDITIONAL EFFECTS FOR SPENDING ACTION POINTS 1/2 HP 1/4 HP DAMAGE ABIL FEAT ENH MISC MISC CURRENT HIT POINTS CURRENT SURGE USES RACE FEATURES ABILITY SCORE MODS ABILITY: DAMAGE ABIL FEAT ENH MISC MISC SECOND WIND 1/ENCOUNTER USED TEMPORARY HIT POINTS BASIC ATTACKS ATTACK DEFENSE WEAPON OR POWER DAMAGE DEATH SAVING THROW FAILURES SAVING THROW MODS vs RESISTANCES vs vs CURRENT CONDITIONS AND EFFECTS vs CLASS / PATH / DESTINY FEATURES SKILLS ABIL MOD TRND ARMOR BONUS SKILL NAME + 1/2 LVL (+5) PENALTY MISC FEATS Acrobatics DEX Arcana INT n/a Athletics STR Bluff CHA n/a Diplomacy CHA n/a Dungeoneering WIS n/a Endurance CON Heal WIS n/a History INT n/a Insight WIS n/a Intimidate CHA n/a Nature WIS n/a Perception WIS n/a Religion INT n/a LANGUAGES KNOWN Stealth DEX Streetwise CHA n/a Thievery DEX ©2008 Wizards of the Coast, Inc. Permission granted to photocopy for personal use only.
- 2. POWER INDEX MAGIC ITEM INDEX List your powers below. List your powers below. Check the box when the power is used. Check the box when the power is used. Clear the box when the power renews. Clear the box when the power renews. AT-WILL POWERS MAGIC ITEMS WEAPON WEAPON WEAPON WEAPON ARMOR ARMS FEET ENCOUNTER POWERS HANDS HEAD PERSONALITY TRAITS NECK RING RING WAIST DAILY POWERS MANNERISMS AND APPEARANCE UTILITY POWERS CHARACTER BACKGROUND Daily Item Powers Per Day Heroic (1-10) Milestone / / / COMPANIONS AND ALLIES NAME NOTES Paragon (11-20) Milestone / / / NAME NOTES Epic (21-30) Milestone / / / NAME NOTES NAME NOTES OTHER EQUIPMENT RITUALS NAME NOTES NAME NOTES NAME NOTES NAME NOTES SESSION AND CAMPAIGN NOTES COINS AND OTHER WEALTH ©2008 Wizards of the Coast, Inc. Permission granted to photocopy for personal use only.