Report
Share
Download to read offline
Recommended
Story Tellers: Hartford Crime Analysis

We chose to address the issue of misinformation with the general public when it comes to the crime and its patterns in the Hartford region. Dataset which we chose for this is from the publicly available Police Incidents registered in Hartford area from 2005 till date with the time stamp. Pattern of the crime can be analyzed like e.g. Robbery incidents mainly happen during holiday season. Using the API we built a live tableau dashboard and also forecasted the drug offenses as per neighborhood.
Open Source and Cyber Security: Open Source Software's Role in Government Cyb...

Great Wide Open - Day 2
Dr. Douglas Maughan - HSARPA
10:30 AM - Security
Recommended
Story Tellers: Hartford Crime Analysis

We chose to address the issue of misinformation with the general public when it comes to the crime and its patterns in the Hartford region. Dataset which we chose for this is from the publicly available Police Incidents registered in Hartford area from 2005 till date with the time stamp. Pattern of the crime can be analyzed like e.g. Robbery incidents mainly happen during holiday season. Using the API we built a live tableau dashboard and also forecasted the drug offenses as per neighborhood.
Open Source and Cyber Security: Open Source Software's Role in Government Cyb...

Great Wide Open - Day 2
Dr. Douglas Maughan - HSARPA
10:30 AM - Security
2Cloud computing threats One of the biggest challenges informa.docx

2
Cloud computing threats
One of the biggest challenges information security leaders have is being able to effectively communicate the value of their team’s efforts across the organization .Here the ability to accurately report on their organization’s state of security and communicate the benefits of a proactive security effort in a language the rest of the organization can understand. This session will draw from the experience of seasoned CISOs with proven track records in enabling core business objectives by influencing key stakeholders in the organization. These risk and information security leaders will share their advice on how to effectively create and demonstrate security’s value. The security function is often seen as doing security for its own sake, rather than for the benefit of the business, and so misses the point of security entirely which is about managing risk to acceptable levels.
The security function all too often acts in a condescending manner thinking it knows what is best for the business when in fact it is just one of the various functions in which they have the organizations for business decisions. Business executives are far more interested in what is happening with information security than ever, thanks to a plethora of high-profile, very visible breaches and security incidents.
In recent years the level of attention paid to cybersecurity issues by organizations has skyrocketed. Cyber risk is now a board-level concern, and IT security budgets have risen accordingly. Despite the increased attention, it is not clear whether firms have become more sophisticated in how they manage cyber risks. Historically, most firms have made cybersecurity investment decisions by adhering to industry best practices, without necessarily developing a detailed understanding of their overall cyber risk first. Risk management is predicated on risk quantification, and many researchers have attempted to quantify cyber risks using quantitative metrics such as return on investment.
Components
Transportation management centers (TMCs)
Ramp metering
Incident management
Motorist assistance systems
Communications systems
Radio communications
Changeable message signs (CMSs)
1
Transportation management centers
Organization
Combine traffic operations personnel with law enforcement
and dispatch
Locally, joint Caltrans-CHP operation
Functions
Traffic surveillance
Incident management
Data collection
Other FMS functions (e. g. ramp metering, CCTV systems, I-
15 Express Lanes Operation)
2
The San Diego Regional Transportation Management Center
(CHP Border Communications Center)
QUESTION: WHY DO WE NEED TMC?
ANSWER: TRAFFIC
CHP/Caltrans Joint Operation
The CHP is responsible for state highway incident
management and law enforcement, and Caltrans, for
the operation and management of the state highway
system.
Both departments remain permanent and equal
partners in each TM ...
Using Data Integration to Deliver Intelligence to Anyone, Anywhere

Data integration makes it possible to deliver intelligence and keep decision makers, first responders, and civilians informed. For over 20 years, FME has been trusted by federal governments to move data from nearly any source to the target destination, while saving time and budget resources.
With FME, federal governments can deliver open data, improve emergency & disaster response, enhance land management, turn public safety and defense into actionable results, and integrate & deliver location intelligence.
Rutkowski OASIS CTI F2F Cybersecurity Act Preso 20160115

Shared with permission from author. Analysis from individual members of OASIS, presented at a recent meeting of the OASIS Cyber Threat Intelligence TC (the development platform for STIX/TAXII). Extracted from a broader set posted to: https://lists.oasis-open.org/archives/cti/201601/msg00000/_cybersecurity_act_reference-model_1.1.pptx
This information is provided for information, but does not represent the output or official views of OASIS or its technical committees..
A-Strategic-Vision-for-Americas-Quantum-Networks-Feb-2020.pdf

A-Strategic-Vision-for-Americas-Quantum-Networks-Feb-2020
Comprehensive U.S. Cyber Framework Final Report

This project is a product of the Class of 2019 Bush School of Government and Public Service, Texas A&M University Capstone Program. The project lasted one academic year and involved eight second-year master students. It intends to synthesize and provide clarity in the realm of issues pertaining to U.S. Internet Protocol Space by demonstrating natural partnerships and recommendations for existing cyber incident response. The project was produced at the request of PointStream Inc., a private cybersecurity contractor.
Cloud Computing for DoD & Government 

IDGA is pleased to announce the return of the 5th Annual Cloud Computing for DoD & Government. The Draft Agenda is now available for you to view. Get your copy at www.CloudComputingEvent.com or request a copy via email at idga@idga.org
This summit is unique from the rest as it allows you to look at both sides of the Cloud - the fluid and functional aspect of Cloud services for government agencies, as well as with the tactical capabilities of the Cloud.
IT Security Services

In a globally connected world, technology brings new opportunities to collaborate and conduct business like never before. However, this increased connectivity can also leave organizations vulnerable to a host of new and unique threats. Federal agencies in particular must secure critical infrastructure, comply with regulations, and both protect and share sensitive information. With no room for system error, agencies require absolute certainty regarding the confidentiality, integrity, and availability of their information. PwC has the experience to meet the information-security needs of the federal government.
www.pwc.com/publicsector
Cleared Job Fair Job Seeker Handbook May 2, 2019, Tysons Corner, VA

Please pre-register at https://clearedjobs.net/job-fair/fair/94/. An active or current security clearance is required for admittance.
Homeland Open Security Technologies (HOST)

Homeland Open Security Technologies (HOST)
Douglas Maughan,
Program Manager, DHS S&T Cyber Security R&D Program
How Better Data Can Change the World

Millions of people around the world have been impacted by the power of FME, which has allowed our customers to power the flow of their data for when, and where they need it. From ocean cleanups and tracking the spread of wildfires, to helping defend endangered species: FME has helped people do it all.
In this webinar, we’ll walk you through inspiring stories of what others have accomplished with FME, and what you can too. We’ll also introduce you to our grant program, and how you can determine your eligibility and apply if applicable.
Don’t miss out on the chance to make an impact within your local community, or around the globe. FME is the data integration tool that can help you get there. Join us to learn how.
More Related Content
Similar to 2015_Intern_Symposium_Thomas_Freeman_Final
2Cloud computing threats One of the biggest challenges informa.docx

2
Cloud computing threats
One of the biggest challenges information security leaders have is being able to effectively communicate the value of their team’s efforts across the organization .Here the ability to accurately report on their organization’s state of security and communicate the benefits of a proactive security effort in a language the rest of the organization can understand. This session will draw from the experience of seasoned CISOs with proven track records in enabling core business objectives by influencing key stakeholders in the organization. These risk and information security leaders will share their advice on how to effectively create and demonstrate security’s value. The security function is often seen as doing security for its own sake, rather than for the benefit of the business, and so misses the point of security entirely which is about managing risk to acceptable levels.
The security function all too often acts in a condescending manner thinking it knows what is best for the business when in fact it is just one of the various functions in which they have the organizations for business decisions. Business executives are far more interested in what is happening with information security than ever, thanks to a plethora of high-profile, very visible breaches and security incidents.
In recent years the level of attention paid to cybersecurity issues by organizations has skyrocketed. Cyber risk is now a board-level concern, and IT security budgets have risen accordingly. Despite the increased attention, it is not clear whether firms have become more sophisticated in how they manage cyber risks. Historically, most firms have made cybersecurity investment decisions by adhering to industry best practices, without necessarily developing a detailed understanding of their overall cyber risk first. Risk management is predicated on risk quantification, and many researchers have attempted to quantify cyber risks using quantitative metrics such as return on investment.
Components
Transportation management centers (TMCs)
Ramp metering
Incident management
Motorist assistance systems
Communications systems
Radio communications
Changeable message signs (CMSs)
1
Transportation management centers
Organization
Combine traffic operations personnel with law enforcement
and dispatch
Locally, joint Caltrans-CHP operation
Functions
Traffic surveillance
Incident management
Data collection
Other FMS functions (e. g. ramp metering, CCTV systems, I-
15 Express Lanes Operation)
2
The San Diego Regional Transportation Management Center
(CHP Border Communications Center)
QUESTION: WHY DO WE NEED TMC?
ANSWER: TRAFFIC
CHP/Caltrans Joint Operation
The CHP is responsible for state highway incident
management and law enforcement, and Caltrans, for
the operation and management of the state highway
system.
Both departments remain permanent and equal
partners in each TM ...
Using Data Integration to Deliver Intelligence to Anyone, Anywhere

Data integration makes it possible to deliver intelligence and keep decision makers, first responders, and civilians informed. For over 20 years, FME has been trusted by federal governments to move data from nearly any source to the target destination, while saving time and budget resources.
With FME, federal governments can deliver open data, improve emergency & disaster response, enhance land management, turn public safety and defense into actionable results, and integrate & deliver location intelligence.
Rutkowski OASIS CTI F2F Cybersecurity Act Preso 20160115

Shared with permission from author. Analysis from individual members of OASIS, presented at a recent meeting of the OASIS Cyber Threat Intelligence TC (the development platform for STIX/TAXII). Extracted from a broader set posted to: https://lists.oasis-open.org/archives/cti/201601/msg00000/_cybersecurity_act_reference-model_1.1.pptx
This information is provided for information, but does not represent the output or official views of OASIS or its technical committees..
A-Strategic-Vision-for-Americas-Quantum-Networks-Feb-2020.pdf

A-Strategic-Vision-for-Americas-Quantum-Networks-Feb-2020
Comprehensive U.S. Cyber Framework Final Report

This project is a product of the Class of 2019 Bush School of Government and Public Service, Texas A&M University Capstone Program. The project lasted one academic year and involved eight second-year master students. It intends to synthesize and provide clarity in the realm of issues pertaining to U.S. Internet Protocol Space by demonstrating natural partnerships and recommendations for existing cyber incident response. The project was produced at the request of PointStream Inc., a private cybersecurity contractor.
Cloud Computing for DoD & Government 

IDGA is pleased to announce the return of the 5th Annual Cloud Computing for DoD & Government. The Draft Agenda is now available for you to view. Get your copy at www.CloudComputingEvent.com or request a copy via email at idga@idga.org
This summit is unique from the rest as it allows you to look at both sides of the Cloud - the fluid and functional aspect of Cloud services for government agencies, as well as with the tactical capabilities of the Cloud.
IT Security Services

In a globally connected world, technology brings new opportunities to collaborate and conduct business like never before. However, this increased connectivity can also leave organizations vulnerable to a host of new and unique threats. Federal agencies in particular must secure critical infrastructure, comply with regulations, and both protect and share sensitive information. With no room for system error, agencies require absolute certainty regarding the confidentiality, integrity, and availability of their information. PwC has the experience to meet the information-security needs of the federal government.
www.pwc.com/publicsector
Cleared Job Fair Job Seeker Handbook May 2, 2019, Tysons Corner, VA

Please pre-register at https://clearedjobs.net/job-fair/fair/94/. An active or current security clearance is required for admittance.
Homeland Open Security Technologies (HOST)

Homeland Open Security Technologies (HOST)
Douglas Maughan,
Program Manager, DHS S&T Cyber Security R&D Program
How Better Data Can Change the World

Millions of people around the world have been impacted by the power of FME, which has allowed our customers to power the flow of their data for when, and where they need it. From ocean cleanups and tracking the spread of wildfires, to helping defend endangered species: FME has helped people do it all.
In this webinar, we’ll walk you through inspiring stories of what others have accomplished with FME, and what you can too. We’ll also introduce you to our grant program, and how you can determine your eligibility and apply if applicable.
Don’t miss out on the chance to make an impact within your local community, or around the globe. FME is the data integration tool that can help you get there. Join us to learn how.
Similar to 2015_Intern_Symposium_Thomas_Freeman_Final (20)
2Cloud computing threats One of the biggest challenges informa.docx

2Cloud computing threats One of the biggest challenges informa.docx
Using Data Integration to Deliver Intelligence to Anyone, Anywhere

Using Data Integration to Deliver Intelligence to Anyone, Anywhere
Rutkowski OASIS CTI F2F Cybersecurity Act Preso 20160115

Rutkowski OASIS CTI F2F Cybersecurity Act Preso 20160115
A-Strategic-Vision-for-Americas-Quantum-Networks-Feb-2020.pdf

A-Strategic-Vision-for-Americas-Quantum-Networks-Feb-2020.pdf
Cleared Job Fair Job Seeker Handbook May 2, 2019, Tysons Corner, VA

Cleared Job Fair Job Seeker Handbook May 2, 2019, Tysons Corner, VA
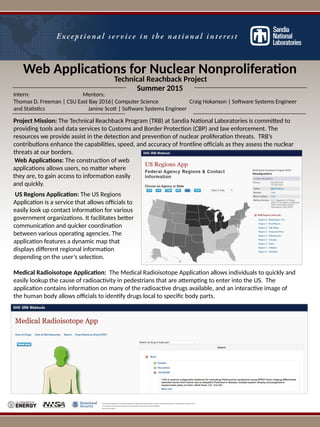
2015_Intern_Symposium_Thomas_Freeman_Final
- 1. Web Applications for Nuclear Nonproliferation Sandia National Laboratories is a multi-program laboratory managed and operated by Sandia Corporation, a wholly owned subsidiary of Lockheed Martin Corporation, for the U.S. Department of Energy’s National Nuclear Security Administration under contract DE-AC04-94AL85000. SAND No. 2015-318390 US Regions Application: The US Regions Application is a service that allows officials to easily look up contact information for various government organizations. It facilitates better communication and quicker coordination between various operating agencies. The application features a dynamic map that displays different regional information depending on the user’s selection. Technical Reachback Project Summer 2015 Intern: Mentors: Thomas D. Freeman | CSU East Bay 2016| Computer Science Craig Hokanson | Software Systems Engineer and Statistics Janine Scott | Software Systems Engineer Project Mission: The Technical Reachback Program (TRB) at Sandia National Laboratories is committed to providing tools and data services to Customs and Border Protection (CBP) and law enforcement. The resources we provide assist in the detection and prevention of nuclear proliferation threats. TRB’s contributions enhance the capabilities, speed, and accuracy of frontline officials as they assess the nuclear threats at our borders. Medical Radioisotope Application: The Medical Radioisotope Application allows individuals to quickly and easily lookup the cause of radioactivity in pedestrians that are attempting to enter into the US. The application contains information on many of the radioactive drugs available, and an interactive image of the human body allows officials to identify drugs local to specific body parts. Web Applications: The construction of web applications allows users, no matter where they are, to gain access to information easily and quickly.