Recommended
Recommended
More Related Content
Viewers also liked
Viewers also liked (9)
Modul teknologi sepeda motor (oto225 02)- pengisian

Modul teknologi sepeda motor (oto225 02)- pengisian
Amazon EC2
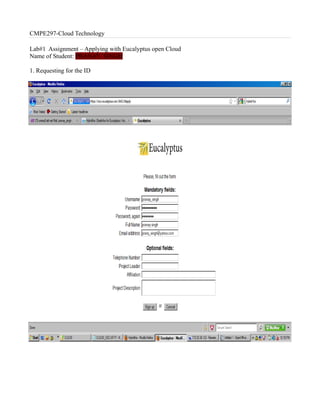
- 1. CMPE297-Cloud Technology Lab#1 Assignment – Applying with Eucalyptus open Cloud Name of Student: PRANAY SINGH 1. Requesting for the ID
- 2. 2. Logging after receiving the account
- 3. 3. The credentials page
- 4. 4. Downloading the credentials zip
- 5. 5. Navigating to Hybrid fox after install the hybridfox plugin
- 6. 6. Adding the region
- 7. 7. Adding the credentials
- 8. 8. Closed the hybrid fox and open it
- 9. 9. Launching one of the instances
- 10. 10. Creating the key pair
- 11. 11 Instance launched and is in running state
- 12. 12. Installed java on the remote machine ( machine in the cloud and ran HelloWord program in Java )