CMMC 2.0 | What the changes mean for organizations in the DIB
•Download as PPTX, PDF•
0 likes•98 views
The improved CMMC 2.0 introduced multiple changes to the audit assurance process. What are those changes and what steps should you take to ensure the protection of Controlled Unclassified Information (CUI)? This deck describes the implications of the newly released Cybersecurity Maturity Model Certification, also known as CMMC 2.0, for businesses in the Defense Industrial Base, how SMBs can take the necessary steps to ensure they protect CUI, and how to tie all aspects of the CMMC 2.0 audit assurance process into centralized Governance, Risk, and Compliance platform. Watch the full webinar recording here: https://youtu.be/_szOCV1rp8s
Report
Share
Report
Share
Recommended
Recommended
Integrated Security for Software Development and Advanced Penetration Testing...

Integrated Security for Software Development and Advanced Penetration Testing...Symptai Consulting Limited
How CMMC Auditors Recommend You Defend Your Organization - Completed March, 2...

How CMMC Auditors Recommend You Defend Your Organization - Completed March, 2...Ignyte Assurance Platform
More Related Content
Similar to CMMC 2.0 | What the changes mean for organizations in the DIB
Integrated Security for Software Development and Advanced Penetration Testing...

Integrated Security for Software Development and Advanced Penetration Testing...Symptai Consulting Limited
Similar to CMMC 2.0 | What the changes mean for organizations in the DIB (20)
2023.06 - CompTIA Security+ Everything you need to know about the new exam .pptx

2023.06 - CompTIA Security+ Everything you need to know about the new exam .pptx
Check point sandblast threat-emulation-customer-success-presentation

Check point sandblast threat-emulation-customer-success-presentation
[ON-DEMAND WEBINAR] Security Wars: Episode 2 | CMMC: Return of The Process Fo...![[ON-DEMAND WEBINAR] Security Wars: Episode 2 | CMMC: Return of The Process Fo...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[ON-DEMAND WEBINAR] Security Wars: Episode 2 | CMMC: Return of The Process Fo...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
[ON-DEMAND WEBINAR] Security Wars: Episode 2 | CMMC: Return of The Process Fo...
CompTIA Security+ Training and Certification in deltails

CompTIA Security+ Training and Certification in deltails
Bridging the Gap Between Your Security Defenses and Critical Data

Bridging the Gap Between Your Security Defenses and Critical Data
Protecting Mission-Critical Source Code from Application Security Vulnerabili...

Protecting Mission-Critical Source Code from Application Security Vulnerabili...
CompTIA Security+: Everything you need to know about the SY0-601 update

CompTIA Security+: Everything you need to know about the SY0-601 update
Integrated Security for Software Development and Advanced Penetration Testing...

Integrated Security for Software Development and Advanced Penetration Testing...
2010 06 gartner avoiding audit fatigue in nine steps 1d

2010 06 gartner avoiding audit fatigue in nine steps 1d
How to Secure your Fintech Solution - A Whitepaper by RapidValue

How to Secure your Fintech Solution - A Whitepaper by RapidValue
IT Security at the Speed of Business: Security Provisioning with Symantec Dat...

IT Security at the Speed of Business: Security Provisioning with Symantec Dat...
More from Ignyte Assurance Platform
How CMMC Auditors Recommend You Defend Your Organization - Completed March, 2...

How CMMC Auditors Recommend You Defend Your Organization - Completed March, 2...Ignyte Assurance Platform
How the DoD’s Cyber Security Maturity Model (CMMC) will impact your business ...

How the DoD’s Cyber Security Maturity Model (CMMC) will impact your business ...Ignyte Assurance Platform
More from Ignyte Assurance Platform (18)
How CMMC Auditors Recommend You Defend Your Organization - Completed March, 2...

How CMMC Auditors Recommend You Defend Your Organization - Completed March, 2...
How the DoD’s Cyber Security Maturity Model (CMMC) will impact your business ...

How the DoD’s Cyber Security Maturity Model (CMMC) will impact your business ...
Midway Swiss Case Study: Journey towards CMMC Compliance with Ignyte

Midway Swiss Case Study: Journey towards CMMC Compliance with Ignyte
Fortifying Cyber Defense: How to Act Now to Protect Global Supply Chains

Fortifying Cyber Defense: How to Act Now to Protect Global Supply Chains
Laying the Foundation: The Need for Cybersecurity in U.S. Manufacturing

Laying the Foundation: The Need for Cybersecurity in U.S. Manufacturing
Full Cybersecurity Regulations Overview for DoD Prime and Subcontractors

Full Cybersecurity Regulations Overview for DoD Prime and Subcontractors
Recently uploaded
Recently uploaded (20)
Top 10 Most Downloaded Games on Play Store in 2024

Top 10 Most Downloaded Games on Play Store in 2024
AWS Community Day CPH - Three problems of Terraform

AWS Community Day CPH - Three problems of Terraform
From Event to Action: Accelerate Your Decision Making with Real-Time Automation

From Event to Action: Accelerate Your Decision Making with Real-Time Automation
2024: Domino Containers - The Next Step. News from the Domino Container commu...

2024: Domino Containers - The Next Step. News from the Domino Container commu...
Cloud Frontiers: A Deep Dive into Serverless Spatial Data and FME

Cloud Frontiers: A Deep Dive into Serverless Spatial Data and FME
Strategies for Landing an Oracle DBA Job as a Fresher

Strategies for Landing an Oracle DBA Job as a Fresher
Tata AIG General Insurance Company - Insurer Innovation Award 2024

Tata AIG General Insurance Company - Insurer Innovation Award 2024
Apidays New York 2024 - The value of a flexible API Management solution for O...

Apidays New York 2024 - The value of a flexible API Management solution for O...
Boost Fertility New Invention Ups Success Rates.pdf

Boost Fertility New Invention Ups Success Rates.pdf
Apidays New York 2024 - The Good, the Bad and the Governed by David O'Neill, ...

Apidays New York 2024 - The Good, the Bad and the Governed by David O'Neill, ...
Workshop - Best of Both Worlds_ Combine KG and Vector search for enhanced R...

Workshop - Best of Both Worlds_ Combine KG and Vector search for enhanced R...
The 7 Things I Know About Cyber Security After 25 Years | April 2024

The 7 Things I Know About Cyber Security After 25 Years | April 2024
Bajaj Allianz Life Insurance Company - Insurer Innovation Award 2024

Bajaj Allianz Life Insurance Company - Insurer Innovation Award 2024
Strategies for Unlocking Knowledge Management in Microsoft 365 in the Copilot...

Strategies for Unlocking Knowledge Management in Microsoft 365 in the Copilot...
CMMC 2.0 | What the changes mean for organizations in the DIB
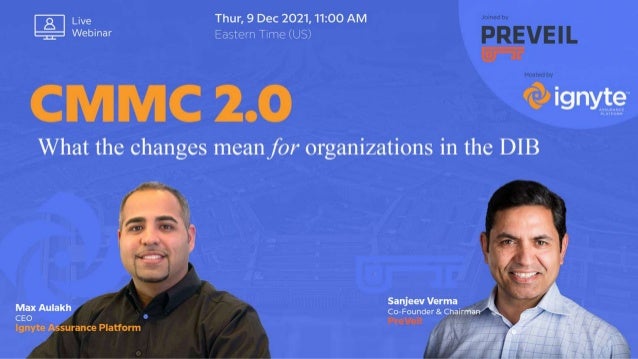
- 2. Sanjeev is a technology entrepreneur with a track record of building successful businesses. He is the co-founder of PreVeil, an end-to-end encrypted cloud file sharing and email platform that is used by hundreds of defense companies for compliance with DFARS 7012, NIST 800-171 and ITAR. Prior to PreVeil, he founded Airvana and led it from a start-up to a publicly-traded company. He earned a BS in EE from the Delhi College of Engineering, an MS in EE from University of Rhode Island and an MBA from the MIT Sloan School of Management. Max is a former U.S Air Force data security & compliance officer. After a successful 15 year career as an enterprise risk leader, he founded Ignyte Assurance Platform, a full-scale audit automation cyber risk company powered by a transformative GRC software engine. Ignyte has signed PLA with Air Force to share its risk assurance technology and improve government vulnerability detection software. Earlier this year, Ignyte became an accredited ISO/IEC 17020:2012 inspection body, and now, it’s pending approval to become one of the top 5 fully certified C3PAOs with top-level clearance. Meet our speakers Max Aulakh, MBA, CISSP, PMP, ITIL-F CEO I Ignyte Assurance Platform Sanjeev Verma Co-Founder & Chairman I PreVeil
- 3. Agenda • Intent of CMMC | Protect CUI • Getting through the Audit • Solutions to support the intent
- 4. Intent of CMMC 2.0 Data Protection CUI Protection & Flow Manage the Audit Process 1 2 3 What changed? • Level 2 Aligned w/110 Controls (NIST SP 800-171 Controls) • Time Bounds POA&Ms • Requires 3rd Party Audits or Self Attestation • Requires Executive Self Attestation
- 5. A small-to-medium defense company used PreVeil to meet 109 out of the 110 NIST 800-171 controls in a rigorous Department of Defense DIBCAC audit. CMMC & NIST 800-171 Audit Process ” For Midway Swiss Turn, it was not so much an IT decision but rather a strategic business step. Ignyte offered us a way to make sure that we’ve tightened everything up, feeling confident for the audit. ” Jayme Rahz CEO I Midway Swiss Turn, Inc.
- 6. & CUI Security & Protection SPRS Score, Evidence and Audit Management
- 8. Ignyte Platform Demo (3-5 mins)
- 9. Q&A Session CMMC 2.0 Framework Overview Have more questions after the event? Contact us www.ignyteplatform.com max@ignyteplatform.com 937-479-1689 W E B I N A R G I V E A W A Y
- 10. Company Assets Identities Hardware & Apps Emails, Documents, etc. Network Servers & Databases Cloud Storage Compliance & Audit Management Asset & Vulnerability Management Supplier Management Policy Management SCAP & Security Results Business Outcome Increase Federal Sales Audit & Compliance Work with more Primes Government-approved Cloud Storage CUI Protection Contract Management Protected CUI Ignyte’s Implementation of CMMC 2.0
