Embed presentation
Download to read offline

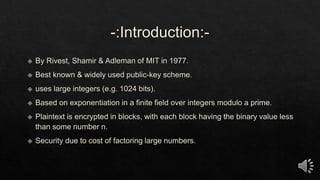
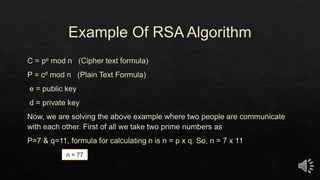
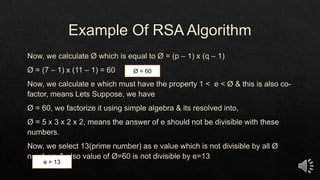
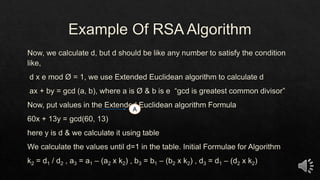
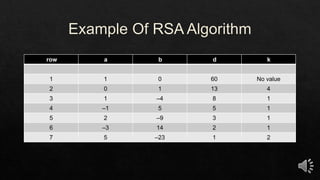
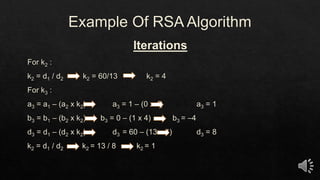
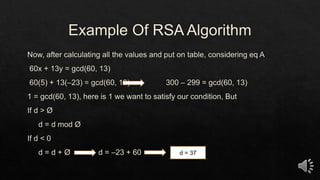

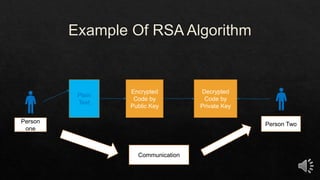
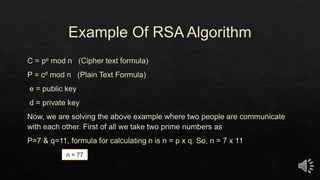
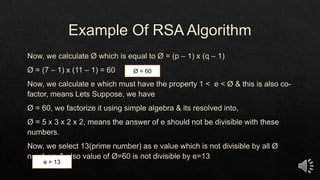
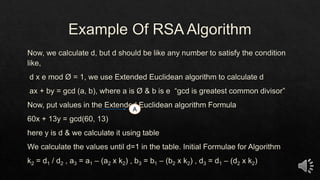
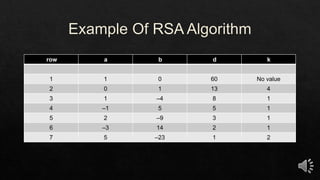
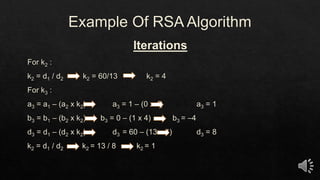
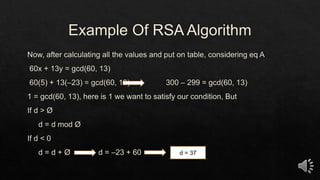
This document describes public-key cryptography and the encryption and decryption process using a public and private key. It includes an example of encrypting and decrypting messages between two people and a table that seems to show encryption values using parameters like n, e, d and different row values.