Azure landing zones - Terraform module design considerations - Azure Architecture Center _ Microsoft Learn.pdf
- 1. 22/04/2023, 13:07 Azure landing zones - Terraform module design considerations - Azure Architecture Center | Microsoft Learn https://learn.microsoft.com/en-us/azure/architecture/landing-zones/terraform/landing-zone-terraform 1/12 Th hit t t k d t f th fi bl t f T f d i d f i h t ti d l Thi
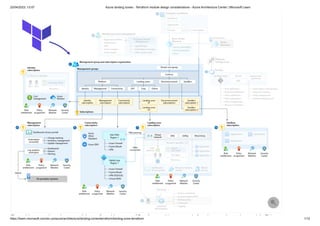
- 2. 22/04/2023, 13:07 Azure landing zones - Terraform module design considerations - Azure Architecture Center | Microsoft Learn https://learn.microsoft.com/en-us/azure/architecture/landing-zones/terraform/landing-zone-terraform 2/12 The architecture takes advantage of the configurable nature of Terraform and is composed of a primary orchestration module. This module encapsulates multiple capabilities of the Azure landing zones conceptual architecture. You can deploy each capability individually or in part. For example, you can deploy just a hub network, or just the Azure DDoS Protection, or just the DNS resources. When doing so, you need to take into account that the capabilities have dependencies. The architecture utilizes an orchestrator approach to simplify the deployment experience. You might prefer to implement each capability using one or more dedicated module instances where each is dedicated to a specific part of the architecture. This is all possible with the correct configuration. A core concept in Terraform is the use of modules. Modules enable you to organize deployments into logical groupings. With modules, you improve the readability of your Terraform files by encapsulating complex details of your deployment. You can also easily reuse modules for different deployments. The ability to re-use modules offers a real benefit when defining and deploying landing zones. It enables repeatable, consistent environments in code while reducing the effort required to deploy at scale. The Terraform implementation of Azure landing zones is delivered using a single module that acts as an orchestration layer. The orchestration layer allows you to select which resources are deployed and managed using the module. The module can be used multiple times in the same environment to deploy resources independently from each other. This can be useful in organizations where different teams are responsible for the different capabilities, or collections of sub-resources. The implementation focuses on the central resource hierarchy of the Azure landing zone conceptual architecture. The design is centered around the following capabilities: C Modules Layers and staging
- 3. 22/04/2023, 13:07 Azure landing zones - Terraform module design considerations - Azure Architecture Center | Microsoft Learn https://learn.microsoft.com/en-us/azure/architecture/landing-zones/terraform/landing-zone-terraform 3/12 Core resources Management resources Connectivity resources Identity resources The module groups resources into these capabilities as they are intended to be deployed together. These groups form logical stages of the implementation. You control the deployment of each of these capabilities by using feature flags. A benefit of this approach is the ability to add to your environment incrementally over time. For example, you can start with a small number of capabilities. You can add the remaining capabilities at a later stage when you’re ready. The core resources capability of the module aligns to the resource organization design area of the Cloud Adoption Framework. It deploys the foundational resources of the conceptual architecture for Azure landing zones. Core resources
- 4. 22/04/2023, 13:07 Azure landing zones - Terraform module design considerations - Azure Architecture Center | Microsoft Learn https://learn.microsoft.com/en-us/azure/architecture/landing-zones/terraform/landing-zone-terraform 4/12 An important concept within the core resources capability is the inclusion of archetypes. A h t id bl d b d h t d fi i hi h li d fi iti li t d fi iti li i t Archetypes
- 5. 22/04/2023, 13:07 Azure landing zones - Terraform module design considerations - Azure Architecture Center | Microsoft Learn https://learn.microsoft.com/en-us/azure/architecture/landing-zones/terraform/landing-zone-terraform 5/12 Archetypes provide a reusable, code-based approach to defining which policy definitions, policy set definitions, policy assignments, role definitions and role assignments must be applied at a given scope. In the Terraform implementation, these decisions are encapsulated as Archetype Definitions . To create a landing zone, management groups are associated with an archetype definition. In the below example for a corp landing zone, the archetype_config has a pointer to the "es_corp" archetype definition. That definition contains all the policy and role configurations which will be added to this management group. Terraform When the built-in archetypes don't align to your requirements, the module provides options to either create new archetypes or make changes to existing . The management resources capability of the module aligns to the management design area of the Cloud Adoption Framework. This capability provides the option to deploy management and monitoring resources to the management platform landing zone. es_corp_landing_zones = { "contoso-corp" = { display_name = "Corp" parent_management_group_id = "contoso-landing-zones" subscription_ids = [] archetype_config = { archetype_id ="es_corp" parameters = {} access_control = {} } } Management resources i i
- 6. 22/04/2023, 13:07 Azure landing zones - Terraform module design considerations - Azure Architecture Center | Microsoft Learn https://learn.microsoft.com/en-us/azure/architecture/landing-zones/terraform/landing-zone-terraform 6/12 The connectivity resources capability of the module provides the option to deploy the network topology and connectivity of the conceptual architecture for Azure landing zones. The identity resources capability of the module aligns to the Azure identity and access management design area of the Cloud Adoption Framework. This capability provides the option to configure policies on the Identity platform landing zone. This section provides a high-level overview of the resources deployed by this module. Layer Resource Type(s) Description Useful Links Core Management Groups Management groups are the highest level resources in an Azure tenant. Management groups allow you to more easily manage your resources. You can apply policy at the management group level and lower level resources will inherit that policy. Specifically, you can apply the following items at the management group level that will be inherited by subscriptions under the management group: Management groups - Cloud Adoption Framework (CAF) documentation Connectivity resources Identity resources 7 Note No resources are deployed with this capability. When the deploy_identity_resources variable is set to true, Azure Policy assignments are configured that protect resources in the identity platform landing zone subscription. Module descriptions
- 7. 22/04/2023, 13:07 Azure landing zones - Terraform module design considerations - Azure Architecture Center | Microsoft Learn https://learn.microsoft.com/en-us/azure/architecture/landing-zones/terraform/landing-zone-terraform 7/12 Layer Resource Type(s) Description Useful Links Azure Policies Azure Role Based Access Controls (RBAC) role assignments Cost controls Core Policy definitions, policy assignments, and policy set definitions DeployIfNotExists (DINE) or Modify policies help ensure the subscriptions and resources that make up landing zones are compliant. Policies are assigned to management groups through policy assignments. The policies ease the burden of management of landing zones. Policy set definitions group sets of policies together. Not all customers are able to use DINE or Modify policies. If that is the case for you, CAF guidance on custom policies provides guidance. Adopt policy-driven guardrails - CAF documentation Custom policy definitions deployed in reference implementations Core Role definitions and role assignments Role-based access control (RBAC) simplifies the management of user rights within a system. Instead of managing the rights of individuals, you determine the rights required for different roles in your system. Azure RBAC has several built-in roles. Custom role definitions allow you to create custom roles for your environment. Identity and access management (IAM) is the key security boundary in cloud computing. Azure RBAC allows you to perform role assignments of built-in roles or custom role definitions to Service Principals, Managed Identities or security groups across management groups and subscriptions. Azure role-based access control - CAF documentation Azure identity and access management design area - CAF documentation Custom policy definitions deployed in reference implementations Management Azure Monitor, Azure Automation, and Microsoft Sentinel Azure Monitor, Azure Automation and Microsoft Sentinel allow you to monitor and manage your infrastructure and workloads. Azure Monitor is a solution that allows you to collect, analyze and act on telemetry from your environment. Microsoft Sentinel is a cloud-native security information and event management (SIEM). It allows you to: Workload management and monitoring - CAF documentation
- 8. 22/04/2023, 13:07 Azure landing zones - Terraform module design considerations - Azure Architecture Center | Microsoft Learn https://learn.microsoft.com/en-us/azure/architecture/landing-zones/terraform/landing-zone-terraform 8/12 Layer Resource Type(s) Description Useful Links Collect - Collect data across your entire infrastructure Detect - Detect threats that were previously undetected Respond - Respond to legitimate threats with built-in orchestration Investigate - Investigate threats with artificial intelligence Azure Automation is a cloud-based automation system. It includes: Configuration management - Inventory and track changes for Linux and Windows virtual machines and manage desired state configuration Update management - Assess Windows and Linux system compliance and create scheduled deployments to meet compliance Process automation - Automate management tasks Connectivity Core networking resource types listed here Network topology is a key consideration in Azure landing zone deployments. CAF focuses on two core networking approaches: Topologies based on Azure Virtual WAN Traditional topologies Define an Azure network topology - CAF Documentation Connectivity Azure DDoS Protection Azure landing zone guidance recommends enabling Azure DDoS Network Protection. This service offers turnkey protection against DDoS attacks. Azure DDoS Network Protection Connectivity DNS Zones, Private DNS Zones, and Private DNS Zone Virtual Network Link Private DNS zones can be deployed to support the use of private endpoints. A private endpoint is a NIC that is assigned a private IP address from your virtual network. You can use the private IP address to securely communicate to services that supports Azure Private Link. Private DNS zones can be configured to resolve the fully qualified domain name (FQDN) of the service to the private endpoint private IP address. Azure Private Endpoint DNS configuration
- 9. 22/04/2023, 13:07 Azure landing zones - Terraform module design considerations - Azure Architecture Center | Microsoft Learn https://learn.microsoft.com/en-us/azure/architecture/landing-zones/terraform/landing-zone-terraform 9/12 By default, the module will deploy the following hierarchy, which is the core set of landing zone management groups: Root Platform Identity Management Connectivity Landing zones Decommissioned Sandbox The SAP, Corp and Online landing zone management groups don't apply to everyone so they aren't deployed by default. The following are ways to deploy these: 1. For demo purposes, you can set the deploy_demo_landing_zones variable to true that will deploy SAP, Corp and Online landing zones 2. For production purposes, you can turn on the management groups you want by setting the following variables to true: deploy_corp_landing_zones deploy_online_landing_zones deploy_sap_landing_zones 3. You can deploy your own custom landing zone management groups by creating a custom landing zone definition Using the Terraform module https://www.youtube-nocookie.com/embed/vFO_cyolUW0 Deploying core resources l i
- 10. 22/04/2023, 13:07 Azure landing zones - Terraform module design considerations - Azure Architecture Center | Microsoft Learn https://learn.microsoft.com/en-us/azure/architecture/landing-zones/terraform/landing-zone-terraform 10/12 To deploy the management resources, the deploy_management_resources variable must be set to true and the subscription_id_management variable must be set to the ID of the management subscription where the resources are to be deployed. Bash Deploy Connectivity Resources provides guidance on how to deploy these topologies. To deploy the identity capability, the deploy_identity_resources variable must be set to true and the subscription_id_identity variable must be set to the ID of the identity subscription where the policies are to be configured. Bash Th A l di i l t ti id d t f th Cl d Ad ti F k it id i t f i t d Deploying management resources deploy_management_resources = true subscription_id_management = <management subscription id> Deploying connectivity resources Deploying identity resources deploy_identity_resources = true subscription_id_identity = <identity subscription id> Customizing the Terraform implementation https://www.youtube-nocookie.com/embed/ct2KHaA7ekI
- 11. 22/04/2023, 13:07 Azure landing zones - Terraform module design considerations - Azure Architecture Center | Microsoft Learn https://learn.microsoft.com/en-us/azure/architecture/landing-zones/terraform/landing-zone-terraform 11/12 The Azure landing zone implementations provided as part of the Cloud Adoption Framework suit a wide variety of requirements and use cases. However, there are often scenarios where customization is required to meet specific business needs. The Azure landing zones Terraform module can be used as the basis of your customized deployment. It provides you a way to accelerate your implementation by removing the need to start from scratch because of a specific required change that rules a ready- made option out. Information on customizing the modules is available in the GitHub repo wiki GitHub: Azure landing zones Terraform module - Wiki . You can use it as a starting point and configure it as per your needs. Tip See Tailor the Azure landing zone architecture to meet requirements for further information.
- 12. 22/04/2023, 13:07 Azure landing zones - Terraform module design considerations - Azure Architecture Center | Microsoft Learn https://learn.microsoft.com/en-us/azure/architecture/landing-zones/terraform/landing-zone-terraform 12/12