Key Benefits of IT and Cyber Risk Management Software | Infographics
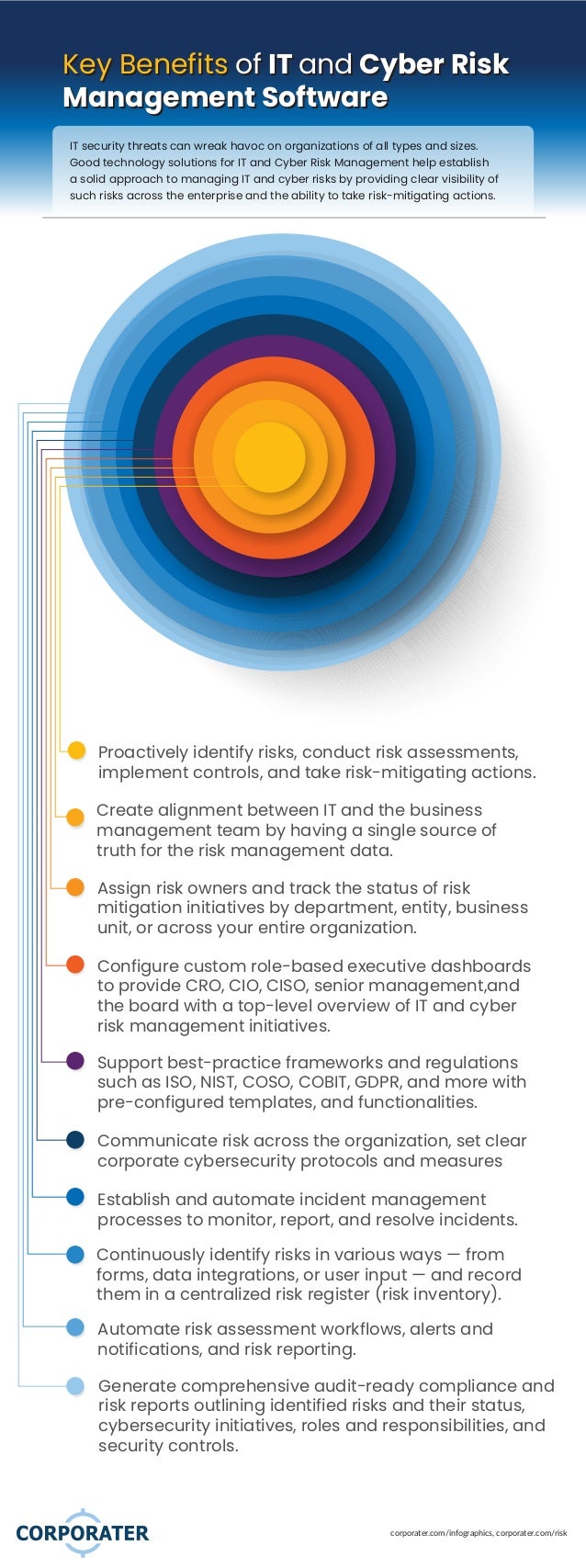
- 1. corporater.com/infographics, corporater.com/risk Key Benefits of IT and Cyber Risk Management Software Key Benefits of IT and Cyber Risk Management Software IT security threats can wreak havoc on organizations of all types and sizes. Good technology solutions for IT and Cyber Risk Management help establish a solid approach to managing IT and cyber risks by providing clear visibility of such risks across the enterprise and the ability to take risk-mitigating actions. Configure custom role-based executive dashboards to provide CRO, CIO, CISO, senior management,and the board with a top-level overview of IT and cyber risk management initiatives. Proactively identify risks, conduct risk assessments, implement controls, and take risk-mitigating actions. Create alignment between IT and the business management team by having a single source of truth for the risk management data. Assign risk owners and track the status of risk mitigation initiatives by department, entity, business unit, or across your entire organization. Support best-practice frameworks and regulations such as ISO, NIST, COSO, COBIT, GDPR, and more with pre-configured templates, and functionalities. Automate risk assessment workflows, alerts and notifications, and risk reporting. Generate comprehensive audit-ready compliance and risk reports outlining identified risks and their status, cybersecurity initiatives, roles and responsibilities, and security controls. Continuously identify risks in various ways — from forms, data integrations, or user input — and record them in a centralized risk register (risk inventory). Establish and automate incident management processes to monitor, report, and resolve incidents. Communicate risk across the organization, set clear corporate cybersecurity protocols and measures
