16 owasp top 10 - a4-insecure direct object references
•
0 likes•475 views
owasp top 10 - a4-insecure direct object references
Report
Share
Report
Share
Recommended
More Related Content
More from appsec
More from appsec (11)
10 application security fundamentals - part 2 - security mechanisms - encry...

10 application security fundamentals - part 2 - security mechanisms - encry...
11 application security fundamentals - part 2 - security mechanisms - summary

11 application security fundamentals - part 2 - security mechanisms - summary
09 application security fundamentals - part 2 - security mechanisms - logging

09 application security fundamentals - part 2 - security mechanisms - logging
08 application security fundamentals - part 2 - security mechanisms - error...

08 application security fundamentals - part 2 - security mechanisms - error...
06 application security fundamentals - part 2 - security mechanisms - sessi...

06 application security fundamentals - part 2 - security mechanisms - sessi...
07 application security fundamentals - part 2 - security mechanisms - data ...

07 application security fundamentals - part 2 - security mechanisms - data ...
04 application security fundamentals - part 2 - security mechanisms - authe...

04 application security fundamentals - part 2 - security mechanisms - authe...
05 application security fundamentals - part 2 - security mechanisms - autho...

05 application security fundamentals - part 2 - security mechanisms - autho...
02 application security fundamentals - part 1 - security priciples

02 application security fundamentals - part 1 - security priciples
01 Application Security Fundamentals - part 1 - introduction and goals

01 Application Security Fundamentals - part 1 - introduction and goals
Recently uploaded
Recently uploaded (20)
08448380779 Call Girls In Greater Kailash - I Women Seeking Men

08448380779 Call Girls In Greater Kailash - I Women Seeking Men
TrustArc Webinar - Stay Ahead of US State Data Privacy Law Developments

TrustArc Webinar - Stay Ahead of US State Data Privacy Law Developments
Axa Assurance Maroc - Insurer Innovation Award 2024

Axa Assurance Maroc - Insurer Innovation Award 2024
The Role of Taxonomy and Ontology in Semantic Layers - Heather Hedden.pdf

The Role of Taxonomy and Ontology in Semantic Layers - Heather Hedden.pdf
Powerful Google developer tools for immediate impact! (2023-24 C)

Powerful Google developer tools for immediate impact! (2023-24 C)
Workshop - Best of Both Worlds_ Combine KG and Vector search for enhanced R...

Workshop - Best of Both Worlds_ Combine KG and Vector search for enhanced R...
Handwritten Text Recognition for manuscripts and early printed texts

Handwritten Text Recognition for manuscripts and early printed texts
Automating Google Workspace (GWS) & more with Apps Script

Automating Google Workspace (GWS) & more with Apps Script
08448380779 Call Girls In Friends Colony Women Seeking Men

08448380779 Call Girls In Friends Colony Women Seeking Men
Strategies for Unlocking Knowledge Management in Microsoft 365 in the Copilot...

Strategies for Unlocking Knowledge Management in Microsoft 365 in the Copilot...
Bajaj Allianz Life Insurance Company - Insurer Innovation Award 2024

Bajaj Allianz Life Insurance Company - Insurer Innovation Award 2024
The 7 Things I Know About Cyber Security After 25 Years | April 2024

The 7 Things I Know About Cyber Security After 25 Years | April 2024
Understanding Discord NSFW Servers A Guide for Responsible Users.pdf

Understanding Discord NSFW Servers A Guide for Responsible Users.pdf
Boost Fertility New Invention Ups Success Rates.pdf

Boost Fertility New Invention Ups Success Rates.pdf
16 owasp top 10 - a4-insecure direct object references
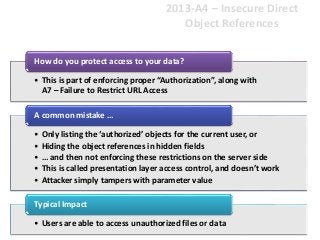
- 1. 2013-A4 – Insecure Direct Object References • This is part of enforcing proper “Authorization”, along with A7 – Failure to Restrict URL Access How do you protect access to your data? • Only listing the ‘authorized’ objects for the current user, or • Hiding the object references in hidden fields • … and then not enforcing these restrictions on the server side • This is called presentation layer access control, and doesn’t work • Attacker simply tampers with parameter value A common mistake … • Users are able to access unauthorized files or data Typical Impact
- 2. Insecure Direct Object References Illustrated • Attacker notices his acct parameter is 6065 ?acct=6065 • He modifies it to a nearby number ?acct=6066 • Attacker views the victim’s account information https://www.onlinebank.com/user?acct=6065
- 3. A4 – Avoiding Insecure Direct Object References • Eliminate the direct object reference – Replace them with a temporary mapping value (e.g. 1, 2, 3) – ESAPI provides support for numeric & random mappings • IntegerAccessReferenceMap & RandomAccessReferenceMap • Validate the direct object reference – Verify the parameter value is properly formatted – Verify the user is allowed to access the target object • Query constraints work great! – Verify the requested mode of access is allowed to the target object (e.g., read, write, delete) http://app?file=1 Report123.xls http://app?id=7d3J93 Acct:9182374http://app?id=9182374 http://app?file=Report123.xls Access Reference Map