Report
Share
Download to read offline
Recommended
Recommended
More Related Content
Viewers also liked
Viewers also liked (13)
More from Ivan Rados
More from Ivan Rados (8)
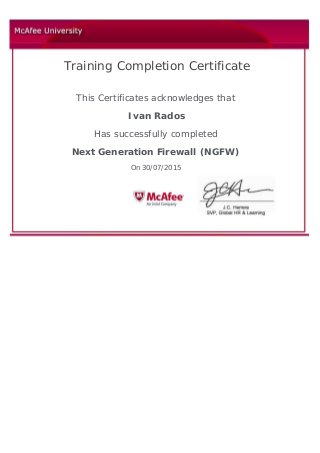
Next Generation Firewall (NGFW)
- 1. Training Completion Certificate This Certificates acknowledges that Ivan Rados Has successfully completed Next Generation Firewall (NGFW) On 30/07/2015
