WCIT Anupan Chander 1
•Download as PPTX, PDF•
0 likes•32 views
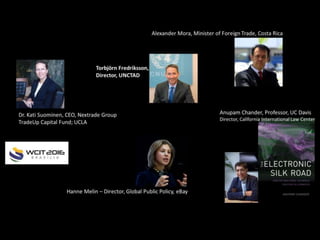
WCIT Anupan Chander 1
Report
Share
Report
Share
Recommended
Versa cloud slide-deck-03-security-aspects

This document summarizes the key aspects of VersaCloud's Transactions as a Service platform. It describes how VersaCloud securely manages cloud-based transactions across backend servers and various frontend devices. It outlines the use of unique identifiers, timestamps, and access controls to secure each transaction. It also provides examples of common transaction types like user registration, login, and method invocation. Finally, it summarizes VersaCloud's internal processing of transactions through four main steps: acceptance, validation, execution, and logging.
Versa cloud slide-deck-02-technical-introduction

This document introduces Transactions as a Service (TaaS) provided by VersaCloud, which offers cloud-based time-limited transactions. It discusses challenges with traditional transaction processing and how VersaCloud addresses them through its transaction manager and time limitation features. Key points include shielding backend servers from errors, managing server capacity, limiting user requests, and making transactions monetizable, developer-friendly, auditable, and reliable. VersaCloud aims to provide a simpler and more efficient transaction processing model compared to traditional relational approaches.
Versa cloud slide-deck-01-pitch

This document discusses cloud-based time-limited transactions as a service that can enable massive cloud and IoT solutions. It provides a simplified coding model where transactions will automatically rollback if the maximum duration is exceeded, unless committed before the time limit. This can help solve challenges of supporting developers, small transaction charges, global solutions, and auditability. Use cases include ticket apps, transportation services, and integrating IoT data sources with different quality of service needs.
2017 11-26-sete-chaves-da-oracao-da-serenidade

O documento apresenta as sete chaves da Oração da Serenidade, que são: serenidade, aceitação, coragem, sabedoria, força, fé e alegria. Cada uma dessas chaves é explicada e discutida em detalhes, com exemplos e citações. O documento também aborda temas como espiritualidade pluralista, desenvolvimento pessoal e autoconhecimento.
WCIT 2016 Calls to Action

The panel on the state of cybersecurity at WCIT 2016 called for organizations to commit to enterprise cybersecurity assessments, focus on governance to establish a culture of cybersecurity and ensure proper implementation, and recognize that resilience is integral to an effective cybersecurity posture. They also recommended measuring progress and maturity.
2016 WCIT Vint Cerf

The document discusses unfinished business related to further developing and improving the Internet. It identifies several areas that require ongoing work such as multistakeholder policy development, improving safety, security, privacy and reliability, facilitating international agreements, developing affordable local content, supporting education and healthcare applications, and continuing to advance technologies like IPv6 and the Internet of Things. The key messages are that the Internet invites continued evolution when open standards and applications foster growth, ensuring public trust and safety is critical, and enabling entrepreneurship should be a high priority.
WCIT 2016 Soumitra Dutta

The document discusses the state of global ICT readiness. It makes three key points: 1) The digital revolution is accelerating the need for continuous innovation and effective digital ecosystems. 2) Seven economies have a significantly higher digital innovation impact than others due to embracing digital interaction. 3) While the digital divide is growing, it is now defined more by the impact of ICT rather than just access to it. The document advocates for sound policies and investments to close gaps and ensure all can benefit from digital technologies.
WCIT 2016 Sérgio Paulo Gallindo

The document summarizes the state of broadband access in Brazil. It outlines the evolution of telecom services in Brazil including growth in voice, cable TV, and broadband internet lines. Specifically, it notes that broadband internet lines have grown at a rate of 35.6% annually. However, universal access to the internet remains a challenge due to issues of price and income levels of the population as well as coverage in rural areas. To address this, Brazil launched a National Broadband Plan to expand affordable broadband access to more cities and invest over $1 billion in infrastructure projects like fiber networks and satellites.
Recommended
Versa cloud slide-deck-03-security-aspects

This document summarizes the key aspects of VersaCloud's Transactions as a Service platform. It describes how VersaCloud securely manages cloud-based transactions across backend servers and various frontend devices. It outlines the use of unique identifiers, timestamps, and access controls to secure each transaction. It also provides examples of common transaction types like user registration, login, and method invocation. Finally, it summarizes VersaCloud's internal processing of transactions through four main steps: acceptance, validation, execution, and logging.
Versa cloud slide-deck-02-technical-introduction

This document introduces Transactions as a Service (TaaS) provided by VersaCloud, which offers cloud-based time-limited transactions. It discusses challenges with traditional transaction processing and how VersaCloud addresses them through its transaction manager and time limitation features. Key points include shielding backend servers from errors, managing server capacity, limiting user requests, and making transactions monetizable, developer-friendly, auditable, and reliable. VersaCloud aims to provide a simpler and more efficient transaction processing model compared to traditional relational approaches.
Versa cloud slide-deck-01-pitch

This document discusses cloud-based time-limited transactions as a service that can enable massive cloud and IoT solutions. It provides a simplified coding model where transactions will automatically rollback if the maximum duration is exceeded, unless committed before the time limit. This can help solve challenges of supporting developers, small transaction charges, global solutions, and auditability. Use cases include ticket apps, transportation services, and integrating IoT data sources with different quality of service needs.
2017 11-26-sete-chaves-da-oracao-da-serenidade

O documento apresenta as sete chaves da Oração da Serenidade, que são: serenidade, aceitação, coragem, sabedoria, força, fé e alegria. Cada uma dessas chaves é explicada e discutida em detalhes, com exemplos e citações. O documento também aborda temas como espiritualidade pluralista, desenvolvimento pessoal e autoconhecimento.
WCIT 2016 Calls to Action

The panel on the state of cybersecurity at WCIT 2016 called for organizations to commit to enterprise cybersecurity assessments, focus on governance to establish a culture of cybersecurity and ensure proper implementation, and recognize that resilience is integral to an effective cybersecurity posture. They also recommended measuring progress and maturity.
2016 WCIT Vint Cerf

The document discusses unfinished business related to further developing and improving the Internet. It identifies several areas that require ongoing work such as multistakeholder policy development, improving safety, security, privacy and reliability, facilitating international agreements, developing affordable local content, supporting education and healthcare applications, and continuing to advance technologies like IPv6 and the Internet of Things. The key messages are that the Internet invites continued evolution when open standards and applications foster growth, ensuring public trust and safety is critical, and enabling entrepreneurship should be a high priority.
WCIT 2016 Soumitra Dutta

The document discusses the state of global ICT readiness. It makes three key points: 1) The digital revolution is accelerating the need for continuous innovation and effective digital ecosystems. 2) Seven economies have a significantly higher digital innovation impact than others due to embracing digital interaction. 3) While the digital divide is growing, it is now defined more by the impact of ICT rather than just access to it. The document advocates for sound policies and investments to close gaps and ensure all can benefit from digital technologies.
WCIT 2016 Sérgio Paulo Gallindo

The document summarizes the state of broadband access in Brazil. It outlines the evolution of telecom services in Brazil including growth in voice, cable TV, and broadband internet lines. Specifically, it notes that broadband internet lines have grown at a rate of 35.6% annually. However, universal access to the internet remains a challenge due to issues of price and income levels of the population as well as coverage in rural areas. To address this, Brazil launched a National Broadband Plan to expand affordable broadband access to more cities and invest over $1 billion in infrastructure projects like fiber networks and satellites.
WCIT 2016 Manu Bhardwaj

The document outlines the goals and accomplishments of the Global Connect initiative, a US-led effort to accelerate international connectivity and make internet access fundamental to development efforts. It discusses two events in April - a working group with 160 experts and a high-level event with government and industry leaders - that focused on prioritizing connectivity, announcing over $20 billion in financial commitments, and agreeing to increase lending. The goals of Global Connect are to help institutions prioritize digital access lending, get countries to prioritize connectivity policies, and ensure expertise is available for capacity building. Next steps include an October stakeholders event and country-specific outreach efforts.
WCIT 2016 Manu Bhardwaj 2 

The Global Connect Initiative aims to bring an additional 1.5 billion people online by 2020 to support achieving UN Sustainable Development Goals. It encourages governments to prioritize internet connectivity in national development strategies, international organizations to finance internet infrastructure projects, and cross-sector working groups to accelerate progress and build capacity for faster digital inclusion. Despite growth, 60% of the global population remains offline due to challenges such as lack of funds, technical expertise, and political instability in some developing countries.
WCIT 2016 Julio Cesar Ribeiro

O documento discute diversas áreas tecnológicas como biotecnologia, nanotecnologia, saúde, cosméticos, energia, agricultura e segurança. Aponta que a inovação em TIC será fundamental para viabilizar o crescimento dessas tecnologias nos próximos anos.
WCIT 2016 Jan Ming Ho

1) Taiwan is working to build government-wide cybersecurity situation awareness through a defense-in-depth approach with cooperation between public and private sectors.
2) A hierarchical cybersecurity organization has been established in Taiwan with national, domain, and enterprise levels to enable early warning and continuous monitoring.
3) Taiwan has established taskforces and working groups to coordinate cybersecurity efforts across different government agencies and critical infrastructure sectors and promote information sharing.
WCIT 2016 George Newstrom

This document discusses opportunities for global IT companies in government contracting. It provides data on projected growth in global and US government IT spending. It also outlines some of the barriers foreign companies face in the US federal market, such as competition, ownership restrictions, and regulations. However, the document notes that foreign-owned companies can succeed through strategies like mergers/acquisitions, joint ventures, partnerships, and teaming arrangements.
WCIT 2016 Dr. William P. Magee Jr

This document discusses Operation Smile, a non-profit organization that provides cleft lip and palate surgery to patients around the world. It notes that Operation Smile has over 300 employees worldwide, 13,000 medical volunteers in over 60 countries, and has treated hundreds of thousands of patients through over 180 medical missions this year alone. The document also describes some of Operation Smile's work in areas like electronic medical records, volunteer management, genetics research, and using technology like 3D printing and voice/facial recognition to advance their efforts.
WCIT 2016 Dr. Ming Ji Wu

The document summarizes Taiwan's efforts to develop smart cities through integrating multiple technological solutions. It discusses issues facing modern cities like public safety, traffic, and education resources. Taiwan is using technologies like surveillance systems, smart lighting, electric vehicle sharing, and online education platforms to address these issues. Examples provided include a 170,000 camera surveillance network, smart lighting that also provides charging stations, and a program allowing small rural schools to share educational resources virtually. The goal is to improve quality of life through efficient, sustainable, and innovative smart city initiatives.
WCIT 2016 Amy Aussieker

Envision Charlotte is a public-private partnership in Charlotte, North Carolina that brings together the city, county, universities, businesses, and utilities to make Charlotte a global model for a smart city. Through innovative smart city projects, the partnership aims to increase economic competitiveness, environmental sustainability, and measurable community benefits. It was announced as part of the White House's Smart City Initiative and has held workshops to develop smart city projects since 2016.
WCIT 2016 Aline Sordilli

1. O documento discute como os estereótipos de gênero são introduzidos desde a infância e se perpetuam ao longo da vida, influenciando as percepções e oportunidades de homens e mulheres.
2. Mulheres tendem a atribuir seu sucesso a fatores externos como sorte e ajuda de outros, enquanto homens o atribuem a habilidades internas. Isso influencia a autoconfiança e ambições de cada gênero.
3. É necessário empoderar as mulheres e ensiná-las a neg
2016 it-census-2015-edition-main-results

The document summarizes the results of the 2015 IT Sector Census, which surveyed companies from 30 countries. Some key findings include:
- Most participating companies were small-to-medium enterprises, especially in Latin America and Europe. African companies tended to be the youngest.
- Top IT activities differed by region, with custom software development most common in Europe and application products in Africa.
- Financial services, governments, and telecom were among the most common client verticals across regions.
- Partnerships were most frequently with Microsoft, Oracle, and IBM.
- Sources of capital were mostly partners' own, while recurring revenues over 50% were most common for Latin American companies.
2016-08-31 Comorbidades e a Dependência Química

O documento fornece informações sobre Daniel Cordeiro, um psiquiatra especialista em dependência química. Ele descreve sua formação acadêmica, incluindo graduação, residência, especializações e mestrado. Também lista seus empregos anteriores em hospitais e centros de tratamento de dependência química.
Cloud iot novos requisitos software

O documento discute como a Internet das Coisas e a computação em nuvem estão criando novos requisitos de software. Muitos dispositivos agora se conectam à Internet e compartilham dados, exigindo software que pode lidar com transações globais, segurança, privacidade e atualizações de versão em larga escala. Além disso, os desenvolvedores precisam criar aplicativos que funcionam em vários ambientes culturais e permitem microtransações e auditoria.
Cloud iot-new-software-requirements

Cloud Computing and the Internet of Things have opened up a new space for innovation opportunities. By analyzing these new applications in detail, we not only find that they have many new requirements (in comparison with traditional software), but that many of these new requirements are common to many of them. Hence, development costs can be reduced by the introduction of new and appropriate software tools aimed specifically at this scenario.
2016 05-18-it-census-2015-edition-main-results

The document summarizes the results of the 2015 IT Sector Census. Some key findings include:
- 945 companies from 30 countries participated, with 555 responses analyzed
- Most responses came from Latin America (87.6%), followed by Europe (7.4%) and Africa (5%)
- Brazil had the most participants (55.1%) followed by Argentina (8.5%) and other Latin American countries
- The census database with over 188,000 individual answers from 2013-2015 is available for further in-depth analysis by associations, universities, and governments to better understand IT sector trends.
2016 02-26-resumo-resultados-censo-ti-2013-2015

O documento apresenta os principais resultados do Censo do Setor de TI de 2013 a 2015, cobrindo a participação por país, idade e porte das empresas, crescimento, capital humano e aspectos financeiros. De 2013 a 2015, a participação brasileira caiu levemente de 63,4% para 55,1%, enquanto a participação de outros países sul-americanos aumentou. A maioria das empresas brasileiras tem até 25 anos e faturamento anual inferior a R$20 milhões.
Mediação AE 2016 

Este documento descreve uma equipe multidisciplinar de mediação de conflitos no Brasil. A equipe ajuda famílias e usuários de álcool e drogas a resolverem disputas por meio de um processo de diálogo facilitado com o objetivo de modificar relacionamentos de forma positiva. O documento também discute os benefícios da mediação e conceitos como comportamentos positivos e negativos, visão sistêmica e responsabilidade das partes no processo.
2008-11-28-jornalismo-2.0-quem-le-o-que-itu-sp

Esta palestra fez parte do evento Jornalismo 2.0, realizado em 28 de novembro de 2008 (maiores informações sobre o evento você encontra em www.jornalismo20.com.br) e apresenta resultado de pesquisa de mercado desenvolvida para o evento, sobre hábitos de leitura.
2015-05-19-mbi-la-economia-de-las-apis

Este documento discute la economía de las APIs y cómo las empresas pueden exponer sus recursos de información a través de APIs para crear nuevas oportunidades de negocio. Define la economía de las APIs como el intercambio comercial de recursos de información facilitado al exponer los recursos centrales de una entidad a un ecosistema de desarrolladores a través de una interfaz de aplicación basada en Internet. Proporciona ejemplos de cómo las empresas pueden usar las APIs para vender datos individuales, permitir que los sistemas se conviertan en pl
2014-12 Pesquisa sobre ERP, CRM e BI no Interior Paulista

Veja aqui os resultados de ampla pesquisa conduzida pela MBI ao longo de quase todo o ano de 2014, entrevistando mais de 400 empresas localizadas no Interior do Estado de São Paulo, em relação ao uso atual e futuro de sistemas de ERP, CRM e BI.
2014 06-11-roberto-mayer-resultados-censo-ti-2013

Este documento apresenta os resultados do segundo Censo do Setor de TI realizado pela Assespro em 2013, que contou com a participação de 850 empresas de 17 países. Os principais temas abordados foram vendas, exportações, recursos humanos e inovação. Os resultados mostraram que o Brasil respondeu por 63,4% das empresas participantes e que a maioria investe em capacitação e certificação de seus profissionais.
The Microsoft 365 Migration Tutorial For Beginner.pptx

This presentation will help you understand the power of Microsoft 365. However, we have mentioned every productivity app included in Office 365. Additionally, we have suggested the migration situation related to Office 365 and how we can help you.
You can also read: https://www.systoolsgroup.com/updates/office-365-tenant-to-tenant-migration-step-by-step-complete-guide/
GNSS spoofing via SDR (Criptored Talks 2024)

In the realm of cybersecurity, offensive security practices act as a critical shield. By simulating real-world attacks in a controlled environment, these techniques expose vulnerabilities before malicious actors can exploit them. This proactive approach allows manufacturers to identify and fix weaknesses, significantly enhancing system security.
This presentation delves into the development of a system designed to mimic Galileo's Open Service signal using software-defined radio (SDR) technology. We'll begin with a foundational overview of both Global Navigation Satellite Systems (GNSS) and the intricacies of digital signal processing.
The presentation culminates in a live demonstration. We'll showcase the manipulation of Galileo's Open Service pilot signal, simulating an attack on various software and hardware systems. This practical demonstration serves to highlight the potential consequences of unaddressed vulnerabilities, emphasizing the importance of offensive security practices in safeguarding critical infrastructure.
More Related Content
More from Roberto C. Mayer
WCIT 2016 Manu Bhardwaj

The document outlines the goals and accomplishments of the Global Connect initiative, a US-led effort to accelerate international connectivity and make internet access fundamental to development efforts. It discusses two events in April - a working group with 160 experts and a high-level event with government and industry leaders - that focused on prioritizing connectivity, announcing over $20 billion in financial commitments, and agreeing to increase lending. The goals of Global Connect are to help institutions prioritize digital access lending, get countries to prioritize connectivity policies, and ensure expertise is available for capacity building. Next steps include an October stakeholders event and country-specific outreach efforts.
WCIT 2016 Manu Bhardwaj 2 

The Global Connect Initiative aims to bring an additional 1.5 billion people online by 2020 to support achieving UN Sustainable Development Goals. It encourages governments to prioritize internet connectivity in national development strategies, international organizations to finance internet infrastructure projects, and cross-sector working groups to accelerate progress and build capacity for faster digital inclusion. Despite growth, 60% of the global population remains offline due to challenges such as lack of funds, technical expertise, and political instability in some developing countries.
WCIT 2016 Julio Cesar Ribeiro

O documento discute diversas áreas tecnológicas como biotecnologia, nanotecnologia, saúde, cosméticos, energia, agricultura e segurança. Aponta que a inovação em TIC será fundamental para viabilizar o crescimento dessas tecnologias nos próximos anos.
WCIT 2016 Jan Ming Ho

1) Taiwan is working to build government-wide cybersecurity situation awareness through a defense-in-depth approach with cooperation between public and private sectors.
2) A hierarchical cybersecurity organization has been established in Taiwan with national, domain, and enterprise levels to enable early warning and continuous monitoring.
3) Taiwan has established taskforces and working groups to coordinate cybersecurity efforts across different government agencies and critical infrastructure sectors and promote information sharing.
WCIT 2016 George Newstrom

This document discusses opportunities for global IT companies in government contracting. It provides data on projected growth in global and US government IT spending. It also outlines some of the barriers foreign companies face in the US federal market, such as competition, ownership restrictions, and regulations. However, the document notes that foreign-owned companies can succeed through strategies like mergers/acquisitions, joint ventures, partnerships, and teaming arrangements.
WCIT 2016 Dr. William P. Magee Jr

This document discusses Operation Smile, a non-profit organization that provides cleft lip and palate surgery to patients around the world. It notes that Operation Smile has over 300 employees worldwide, 13,000 medical volunteers in over 60 countries, and has treated hundreds of thousands of patients through over 180 medical missions this year alone. The document also describes some of Operation Smile's work in areas like electronic medical records, volunteer management, genetics research, and using technology like 3D printing and voice/facial recognition to advance their efforts.
WCIT 2016 Dr. Ming Ji Wu

The document summarizes Taiwan's efforts to develop smart cities through integrating multiple technological solutions. It discusses issues facing modern cities like public safety, traffic, and education resources. Taiwan is using technologies like surveillance systems, smart lighting, electric vehicle sharing, and online education platforms to address these issues. Examples provided include a 170,000 camera surveillance network, smart lighting that also provides charging stations, and a program allowing small rural schools to share educational resources virtually. The goal is to improve quality of life through efficient, sustainable, and innovative smart city initiatives.
WCIT 2016 Amy Aussieker

Envision Charlotte is a public-private partnership in Charlotte, North Carolina that brings together the city, county, universities, businesses, and utilities to make Charlotte a global model for a smart city. Through innovative smart city projects, the partnership aims to increase economic competitiveness, environmental sustainability, and measurable community benefits. It was announced as part of the White House's Smart City Initiative and has held workshops to develop smart city projects since 2016.
WCIT 2016 Aline Sordilli

1. O documento discute como os estereótipos de gênero são introduzidos desde a infância e se perpetuam ao longo da vida, influenciando as percepções e oportunidades de homens e mulheres.
2. Mulheres tendem a atribuir seu sucesso a fatores externos como sorte e ajuda de outros, enquanto homens o atribuem a habilidades internas. Isso influencia a autoconfiança e ambições de cada gênero.
3. É necessário empoderar as mulheres e ensiná-las a neg
2016 it-census-2015-edition-main-results

The document summarizes the results of the 2015 IT Sector Census, which surveyed companies from 30 countries. Some key findings include:
- Most participating companies were small-to-medium enterprises, especially in Latin America and Europe. African companies tended to be the youngest.
- Top IT activities differed by region, with custom software development most common in Europe and application products in Africa.
- Financial services, governments, and telecom were among the most common client verticals across regions.
- Partnerships were most frequently with Microsoft, Oracle, and IBM.
- Sources of capital were mostly partners' own, while recurring revenues over 50% were most common for Latin American companies.
2016-08-31 Comorbidades e a Dependência Química

O documento fornece informações sobre Daniel Cordeiro, um psiquiatra especialista em dependência química. Ele descreve sua formação acadêmica, incluindo graduação, residência, especializações e mestrado. Também lista seus empregos anteriores em hospitais e centros de tratamento de dependência química.
Cloud iot novos requisitos software

O documento discute como a Internet das Coisas e a computação em nuvem estão criando novos requisitos de software. Muitos dispositivos agora se conectam à Internet e compartilham dados, exigindo software que pode lidar com transações globais, segurança, privacidade e atualizações de versão em larga escala. Além disso, os desenvolvedores precisam criar aplicativos que funcionam em vários ambientes culturais e permitem microtransações e auditoria.
Cloud iot-new-software-requirements

Cloud Computing and the Internet of Things have opened up a new space for innovation opportunities. By analyzing these new applications in detail, we not only find that they have many new requirements (in comparison with traditional software), but that many of these new requirements are common to many of them. Hence, development costs can be reduced by the introduction of new and appropriate software tools aimed specifically at this scenario.
2016 05-18-it-census-2015-edition-main-results

The document summarizes the results of the 2015 IT Sector Census. Some key findings include:
- 945 companies from 30 countries participated, with 555 responses analyzed
- Most responses came from Latin America (87.6%), followed by Europe (7.4%) and Africa (5%)
- Brazil had the most participants (55.1%) followed by Argentina (8.5%) and other Latin American countries
- The census database with over 188,000 individual answers from 2013-2015 is available for further in-depth analysis by associations, universities, and governments to better understand IT sector trends.
2016 02-26-resumo-resultados-censo-ti-2013-2015

O documento apresenta os principais resultados do Censo do Setor de TI de 2013 a 2015, cobrindo a participação por país, idade e porte das empresas, crescimento, capital humano e aspectos financeiros. De 2013 a 2015, a participação brasileira caiu levemente de 63,4% para 55,1%, enquanto a participação de outros países sul-americanos aumentou. A maioria das empresas brasileiras tem até 25 anos e faturamento anual inferior a R$20 milhões.
Mediação AE 2016 

Este documento descreve uma equipe multidisciplinar de mediação de conflitos no Brasil. A equipe ajuda famílias e usuários de álcool e drogas a resolverem disputas por meio de um processo de diálogo facilitado com o objetivo de modificar relacionamentos de forma positiva. O documento também discute os benefícios da mediação e conceitos como comportamentos positivos e negativos, visão sistêmica e responsabilidade das partes no processo.
2008-11-28-jornalismo-2.0-quem-le-o-que-itu-sp

Esta palestra fez parte do evento Jornalismo 2.0, realizado em 28 de novembro de 2008 (maiores informações sobre o evento você encontra em www.jornalismo20.com.br) e apresenta resultado de pesquisa de mercado desenvolvida para o evento, sobre hábitos de leitura.
2015-05-19-mbi-la-economia-de-las-apis

Este documento discute la economía de las APIs y cómo las empresas pueden exponer sus recursos de información a través de APIs para crear nuevas oportunidades de negocio. Define la economía de las APIs como el intercambio comercial de recursos de información facilitado al exponer los recursos centrales de una entidad a un ecosistema de desarrolladores a través de una interfaz de aplicación basada en Internet. Proporciona ejemplos de cómo las empresas pueden usar las APIs para vender datos individuales, permitir que los sistemas se conviertan en pl
2014-12 Pesquisa sobre ERP, CRM e BI no Interior Paulista

Veja aqui os resultados de ampla pesquisa conduzida pela MBI ao longo de quase todo o ano de 2014, entrevistando mais de 400 empresas localizadas no Interior do Estado de São Paulo, em relação ao uso atual e futuro de sistemas de ERP, CRM e BI.
2014 06-11-roberto-mayer-resultados-censo-ti-2013

Este documento apresenta os resultados do segundo Censo do Setor de TI realizado pela Assespro em 2013, que contou com a participação de 850 empresas de 17 países. Os principais temas abordados foram vendas, exportações, recursos humanos e inovação. Os resultados mostraram que o Brasil respondeu por 63,4% das empresas participantes e que a maioria investe em capacitação e certificação de seus profissionais.
More from Roberto C. Mayer (20)
2014-12 Pesquisa sobre ERP, CRM e BI no Interior Paulista

2014-12 Pesquisa sobre ERP, CRM e BI no Interior Paulista
Recently uploaded
The Microsoft 365 Migration Tutorial For Beginner.pptx

This presentation will help you understand the power of Microsoft 365. However, we have mentioned every productivity app included in Office 365. Additionally, we have suggested the migration situation related to Office 365 and how we can help you.
You can also read: https://www.systoolsgroup.com/updates/office-365-tenant-to-tenant-migration-step-by-step-complete-guide/
GNSS spoofing via SDR (Criptored Talks 2024)

In the realm of cybersecurity, offensive security practices act as a critical shield. By simulating real-world attacks in a controlled environment, these techniques expose vulnerabilities before malicious actors can exploit them. This proactive approach allows manufacturers to identify and fix weaknesses, significantly enhancing system security.
This presentation delves into the development of a system designed to mimic Galileo's Open Service signal using software-defined radio (SDR) technology. We'll begin with a foundational overview of both Global Navigation Satellite Systems (GNSS) and the intricacies of digital signal processing.
The presentation culminates in a live demonstration. We'll showcase the manipulation of Galileo's Open Service pilot signal, simulating an attack on various software and hardware systems. This practical demonstration serves to highlight the potential consequences of unaddressed vulnerabilities, emphasizing the importance of offensive security practices in safeguarding critical infrastructure.
Generating privacy-protected synthetic data using Secludy and Milvus

During this demo, the founders of Secludy will demonstrate how their system utilizes Milvus to store and manipulate embeddings for generating privacy-protected synthetic data. Their approach not only maintains the confidentiality of the original data but also enhances the utility and scalability of LLMs under privacy constraints. Attendees, including machine learning engineers, data scientists, and data managers, will witness first-hand how Secludy's integration with Milvus empowers organizations to harness the power of LLMs securely and efficiently.
5th LF Energy Power Grid Model Meet-up Slides

5th Power Grid Model Meet-up
It is with great pleasure that we extend to you an invitation to the 5th Power Grid Model Meet-up, scheduled for 6th June 2024. This event will adopt a hybrid format, allowing participants to join us either through an online Mircosoft Teams session or in person at TU/e located at Den Dolech 2, Eindhoven, Netherlands. The meet-up will be hosted by Eindhoven University of Technology (TU/e), a research university specializing in engineering science & technology.
Power Grid Model
The global energy transition is placing new and unprecedented demands on Distribution System Operators (DSOs). Alongside upgrades to grid capacity, processes such as digitization, capacity optimization, and congestion management are becoming vital for delivering reliable services.
Power Grid Model is an open source project from Linux Foundation Energy and provides a calculation engine that is increasingly essential for DSOs. It offers a standards-based foundation enabling real-time power systems analysis, simulations of electrical power grids, and sophisticated what-if analysis. In addition, it enables in-depth studies and analysis of the electrical power grid’s behavior and performance. This comprehensive model incorporates essential factors such as power generation capacity, electrical losses, voltage levels, power flows, and system stability.
Power Grid Model is currently being applied in a wide variety of use cases, including grid planning, expansion, reliability, and congestion studies. It can also help in analyzing the impact of renewable energy integration, assessing the effects of disturbances or faults, and developing strategies for grid control and optimization.
What to expect
For the upcoming meetup we are organizing, we have an exciting lineup of activities planned:
-Insightful presentations covering two practical applications of the Power Grid Model.
-An update on the latest advancements in Power Grid -Model technology during the first and second quarters of 2024.
-An interactive brainstorming session to discuss and propose new feature requests.
-An opportunity to connect with fellow Power Grid Model enthusiasts and users.
Mutation Testing for Task-Oriented Chatbots

Conversational agents, or chatbots, are increasingly used to access all sorts of services using natural language. While open-domain chatbots - like ChatGPT - can converse on any topic, task-oriented chatbots - the focus of this paper - are designed for specific tasks, like booking a flight, obtaining customer support, or setting an appointment. Like any other software, task-oriented chatbots need to be properly tested, usually by defining and executing test scenarios (i.e., sequences of user-chatbot interactions). However, there is currently a lack of methods to quantify the completeness and strength of such test scenarios, which can lead to low-quality tests, and hence to buggy chatbots.
To fill this gap, we propose adapting mutation testing (MuT) for task-oriented chatbots. To this end, we introduce a set of mutation operators that emulate faults in chatbot designs, an architecture that enables MuT on chatbots built using heterogeneous technologies, and a practical realisation as an Eclipse plugin. Moreover, we evaluate the applicability, effectiveness and efficiency of our approach on open-source chatbots, with promising results.
Main news related to the CCS TSI 2023 (2023/1695)

An English 🇬🇧 translation of a presentation to the speech I gave about the main changes brought by CCS TSI 2023 at the biggest Czech conference on Communications and signalling systems on Railways, which was held in Clarion Hotel Olomouc from 7th to 9th November 2023 (konferenceszt.cz). Attended by around 500 participants and 200 on-line followers.
The original Czech 🇨🇿 version of the presentation can be found here: https://www.slideshare.net/slideshow/hlavni-novinky-souvisejici-s-ccs-tsi-2023-2023-1695/269688092 .
The videorecording (in Czech) from the presentation is available here: https://youtu.be/WzjJWm4IyPk?si=SImb06tuXGb30BEH .
Freshworks Rethinks NoSQL for Rapid Scaling & Cost-Efficiency

Freshworks creates AI-boosted business software that helps employees work more efficiently and effectively. Managing data across multiple RDBMS and NoSQL databases was already a challenge at their current scale. To prepare for 10X growth, they knew it was time to rethink their database strategy. Learn how they architected a solution that would simplify scaling while keeping costs under control.
GraphRAG for LifeSciences Hands-On with the Clinical Knowledge Graph

Tomaz Bratanic
Graph ML and GenAI Expert - Neo4j
Connector Corner: Seamlessly power UiPath Apps, GenAI with prebuilt connectors

Join us to learn how UiPath Apps can directly and easily interact with prebuilt connectors via Integration Service--including Salesforce, ServiceNow, Open GenAI, and more.
The best part is you can achieve this without building a custom workflow! Say goodbye to the hassle of using separate automations to call APIs. By seamlessly integrating within App Studio, you can now easily streamline your workflow, while gaining direct access to our Connector Catalog of popular applications.
We’ll discuss and demo the benefits of UiPath Apps and connectors including:
Creating a compelling user experience for any software, without the limitations of APIs.
Accelerating the app creation process, saving time and effort
Enjoying high-performance CRUD (create, read, update, delete) operations, for
seamless data management.
Speakers:
Russell Alfeche, Technology Leader, RPA at qBotic and UiPath MVP
Charlie Greenberg, host
zkStudyClub - LatticeFold: A Lattice-based Folding Scheme and its Application...

Folding is a recent technique for building efficient recursive SNARKs. Several elegant folding protocols have been proposed, such as Nova, Supernova, Hypernova, Protostar, and others. However, all of them rely on an additively homomorphic commitment scheme based on discrete log, and are therefore not post-quantum secure. In this work we present LatticeFold, the first lattice-based folding protocol based on the Module SIS problem. This folding protocol naturally leads to an efficient recursive lattice-based SNARK and an efficient PCD scheme. LatticeFold supports folding low-degree relations, such as R1CS, as well as high-degree relations, such as CCS. The key challenge is to construct a secure folding protocol that works with the Ajtai commitment scheme. The difficulty, is ensuring that extracted witnesses are low norm through many rounds of folding. We present a novel technique using the sumcheck protocol to ensure that extracted witnesses are always low norm no matter how many rounds of folding are used. Our evaluation of the final proof system suggests that it is as performant as Hypernova, while providing post-quantum security.
Paper Link: https://eprint.iacr.org/2024/257
"Choosing proper type of scaling", Olena Syrota

Imagine an IoT processing system that is already quite mature and production-ready and for which client coverage is growing and scaling and performance aspects are life and death questions. The system has Redis, MongoDB, and stream processing based on ksqldb. In this talk, firstly, we will analyze scaling approaches and then select the proper ones for our system.
Crafting Excellence: A Comprehensive Guide to iOS Mobile App Development Serv...

Crafting Excellence: A Comprehensive Guide to iOS Mobile App Development Serv...Pitangent Analytics & Technology Solutions Pvt. Ltd
Discover top-tier mobile app development services, offering innovative solutions for iOS and Android. Enhance your business with custom, user-friendly mobile applications.AppSec PNW: Android and iOS Application Security with MobSF

Mobile Security Framework - MobSF is a free and open source automated mobile application security testing environment designed to help security engineers, researchers, developers, and penetration testers to identify security vulnerabilities, malicious behaviours and privacy concerns in mobile applications using static and dynamic analysis. It supports all the popular mobile application binaries and source code formats built for Android and iOS devices. In addition to automated security assessment, it also offers an interactive testing environment to build and execute scenario based test/fuzz cases against the application.
This talk covers:
Using MobSF for static analysis of mobile applications.
Interactive dynamic security assessment of Android and iOS applications.
Solving Mobile app CTF challenges.
Reverse engineering and runtime analysis of Mobile malware.
How to shift left and integrate MobSF/mobsfscan SAST and DAST in your build pipeline.
Your One-Stop Shop for Python Success: Top 10 US Python Development Providers

Simplify your search for a reliable Python development partner! This list presents the top 10 trusted US providers offering comprehensive Python development services, ensuring your project's success from conception to completion.
"Frontline Battles with DDoS: Best practices and Lessons Learned", Igor Ivaniuk

At this talk we will discuss DDoS protection tools and best practices, discuss network architectures and what AWS has to offer. Also, we will look into one of the largest DDoS attacks on Ukrainian infrastructure that happened in February 2022. We'll see, what techniques helped to keep the web resources available for Ukrainians and how AWS improved DDoS protection for all customers based on Ukraine experience
Fueling AI with Great Data with Airbyte Webinar

This talk will focus on how to collect data from a variety of sources, leveraging this data for RAG and other GenAI use cases, and finally charting your course to productionalization.
JavaLand 2024: Application Development Green Masterplan

My presentation slides I used at JavaLand 2024
Digital Banking in the Cloud: How Citizens Bank Unlocked Their Mainframe

Inconsistent user experience and siloed data, high costs, and changing customer expectations – Citizens Bank was experiencing these challenges while it was attempting to deliver a superior digital banking experience for its clients. Its core banking applications run on the mainframe and Citizens was using legacy utilities to get the critical mainframe data to feed customer-facing channels, like call centers, web, and mobile. Ultimately, this led to higher operating costs (MIPS), delayed response times, and longer time to market.
Ever-changing customer expectations demand more modern digital experiences, and the bank needed to find a solution that could provide real-time data to its customer channels with low latency and operating costs. Join this session to learn how Citizens is leveraging Precisely to replicate mainframe data to its customer channels and deliver on their “modern digital bank” experiences.
June Patch Tuesday

Ivanti’s Patch Tuesday breakdown goes beyond patching your applications and brings you the intelligence and guidance needed to prioritize where to focus your attention first. Catch early analysis on our Ivanti blog, then join industry expert Chris Goettl for the Patch Tuesday Webinar Event. There we’ll do a deep dive into each of the bulletins and give guidance on the risks associated with the newly-identified vulnerabilities.
Recently uploaded (20)
The Microsoft 365 Migration Tutorial For Beginner.pptx

The Microsoft 365 Migration Tutorial For Beginner.pptx
Generating privacy-protected synthetic data using Secludy and Milvus

Generating privacy-protected synthetic data using Secludy and Milvus
Freshworks Rethinks NoSQL for Rapid Scaling & Cost-Efficiency

Freshworks Rethinks NoSQL for Rapid Scaling & Cost-Efficiency
GraphRAG for LifeSciences Hands-On with the Clinical Knowledge Graph

GraphRAG for LifeSciences Hands-On with the Clinical Knowledge Graph
Connector Corner: Seamlessly power UiPath Apps, GenAI with prebuilt connectors

Connector Corner: Seamlessly power UiPath Apps, GenAI with prebuilt connectors
zkStudyClub - LatticeFold: A Lattice-based Folding Scheme and its Application...

zkStudyClub - LatticeFold: A Lattice-based Folding Scheme and its Application...
Crafting Excellence: A Comprehensive Guide to iOS Mobile App Development Serv...

Crafting Excellence: A Comprehensive Guide to iOS Mobile App Development Serv...
AppSec PNW: Android and iOS Application Security with MobSF

AppSec PNW: Android and iOS Application Security with MobSF
Your One-Stop Shop for Python Success: Top 10 US Python Development Providers

Your One-Stop Shop for Python Success: Top 10 US Python Development Providers
"Frontline Battles with DDoS: Best practices and Lessons Learned", Igor Ivaniuk

"Frontline Battles with DDoS: Best practices and Lessons Learned", Igor Ivaniuk
JavaLand 2024: Application Development Green Masterplan

JavaLand 2024: Application Development Green Masterplan
Digital Banking in the Cloud: How Citizens Bank Unlocked Their Mainframe

Digital Banking in the Cloud: How Citizens Bank Unlocked Their Mainframe
