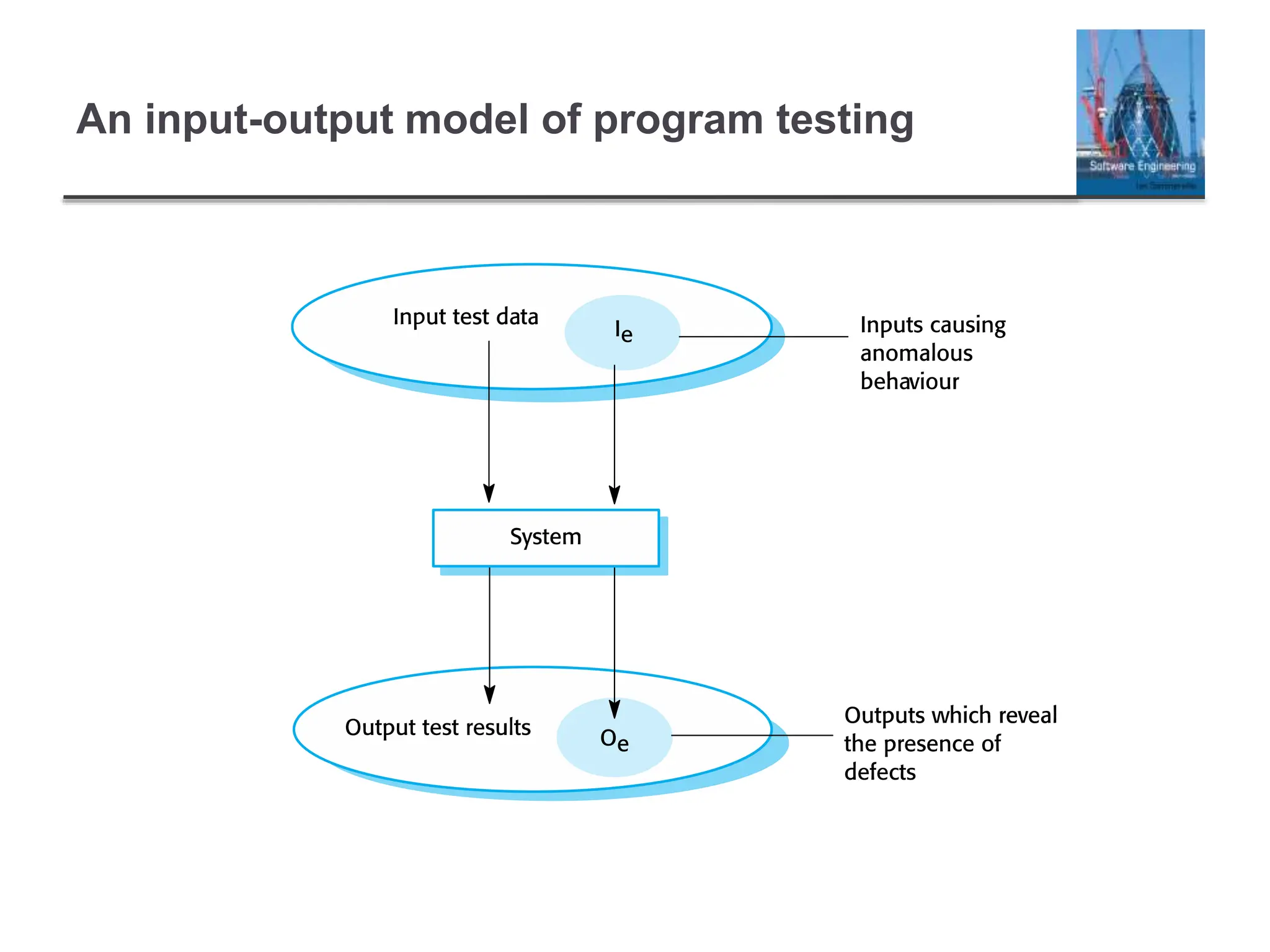
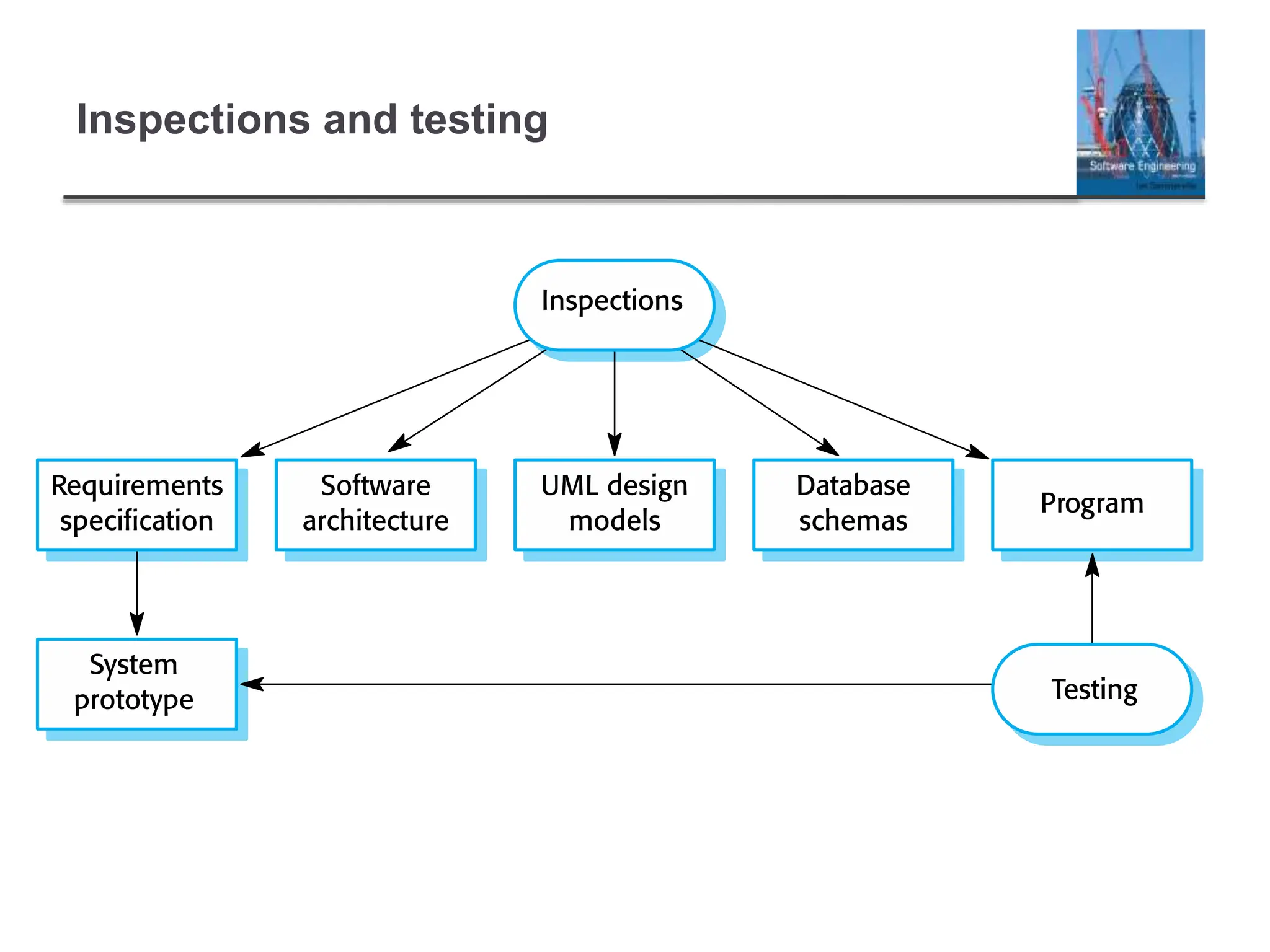
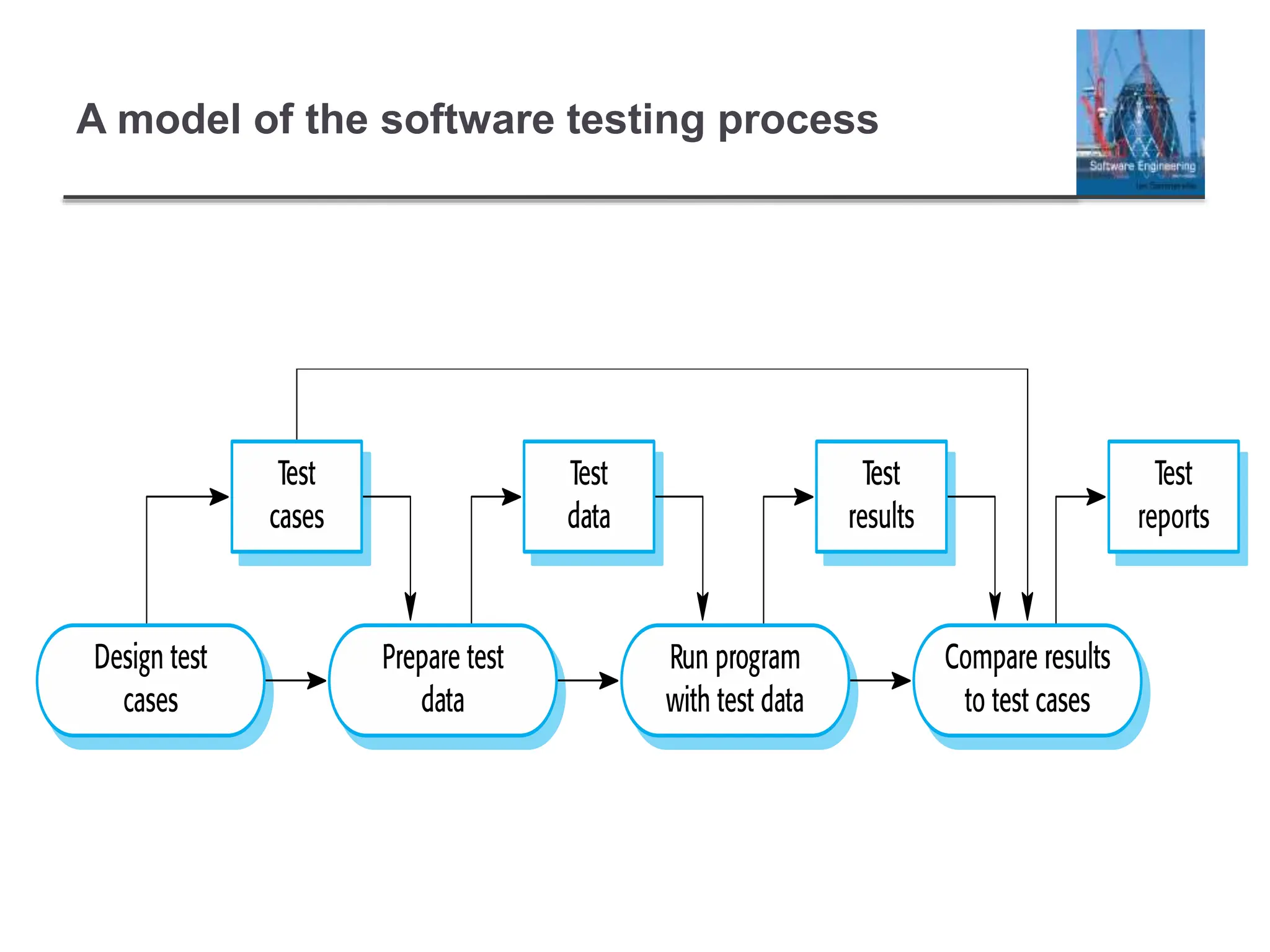
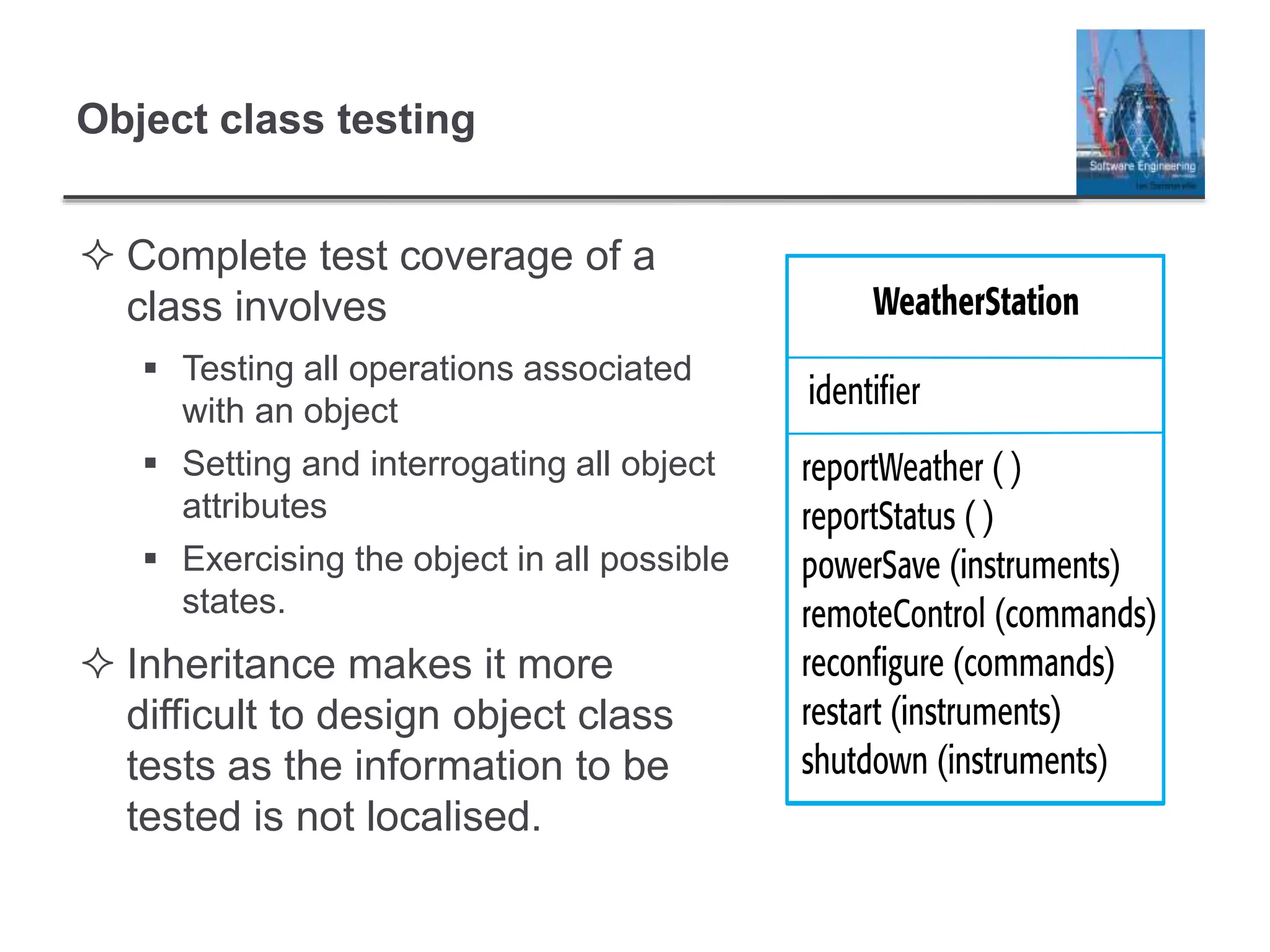
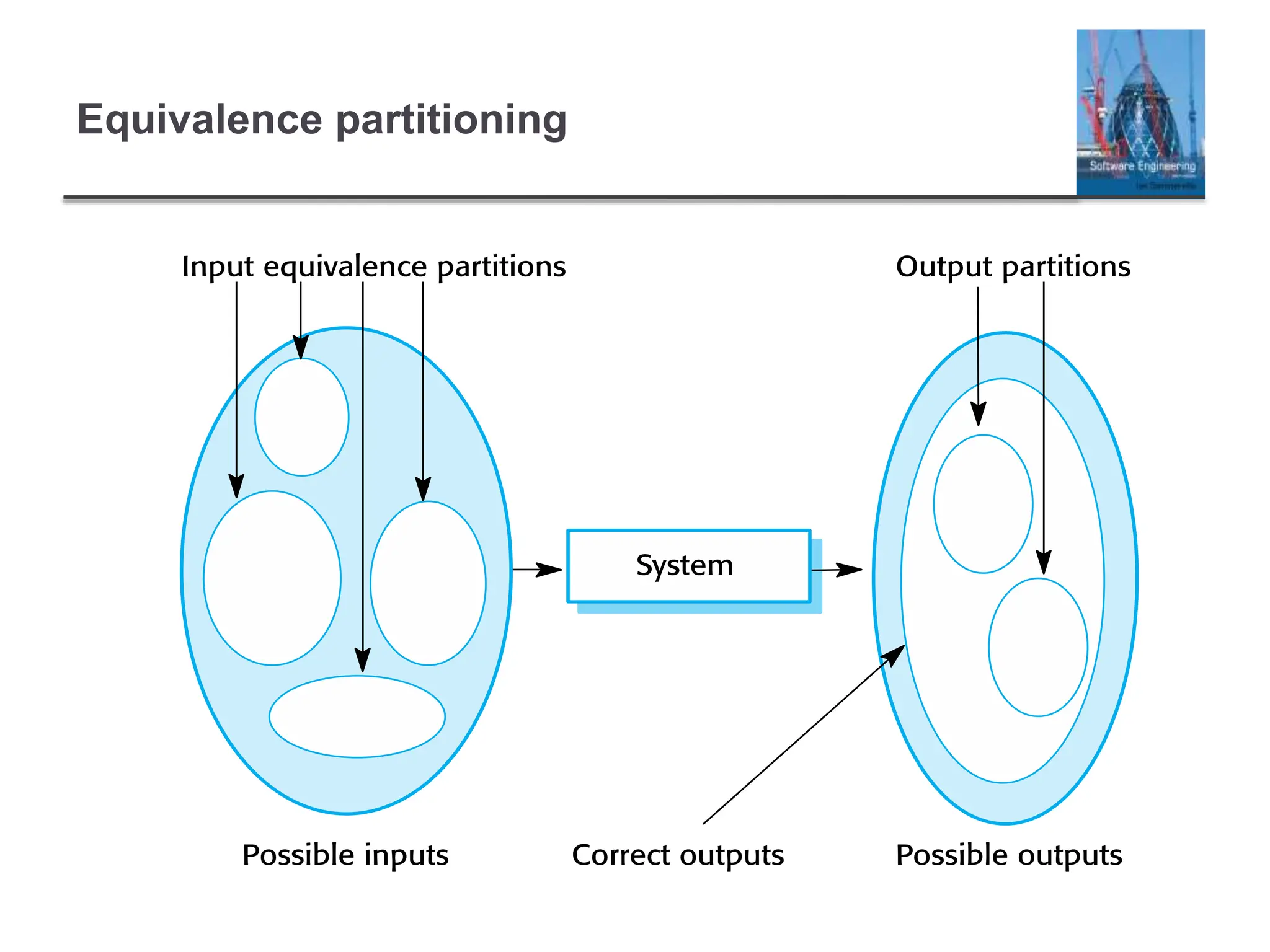
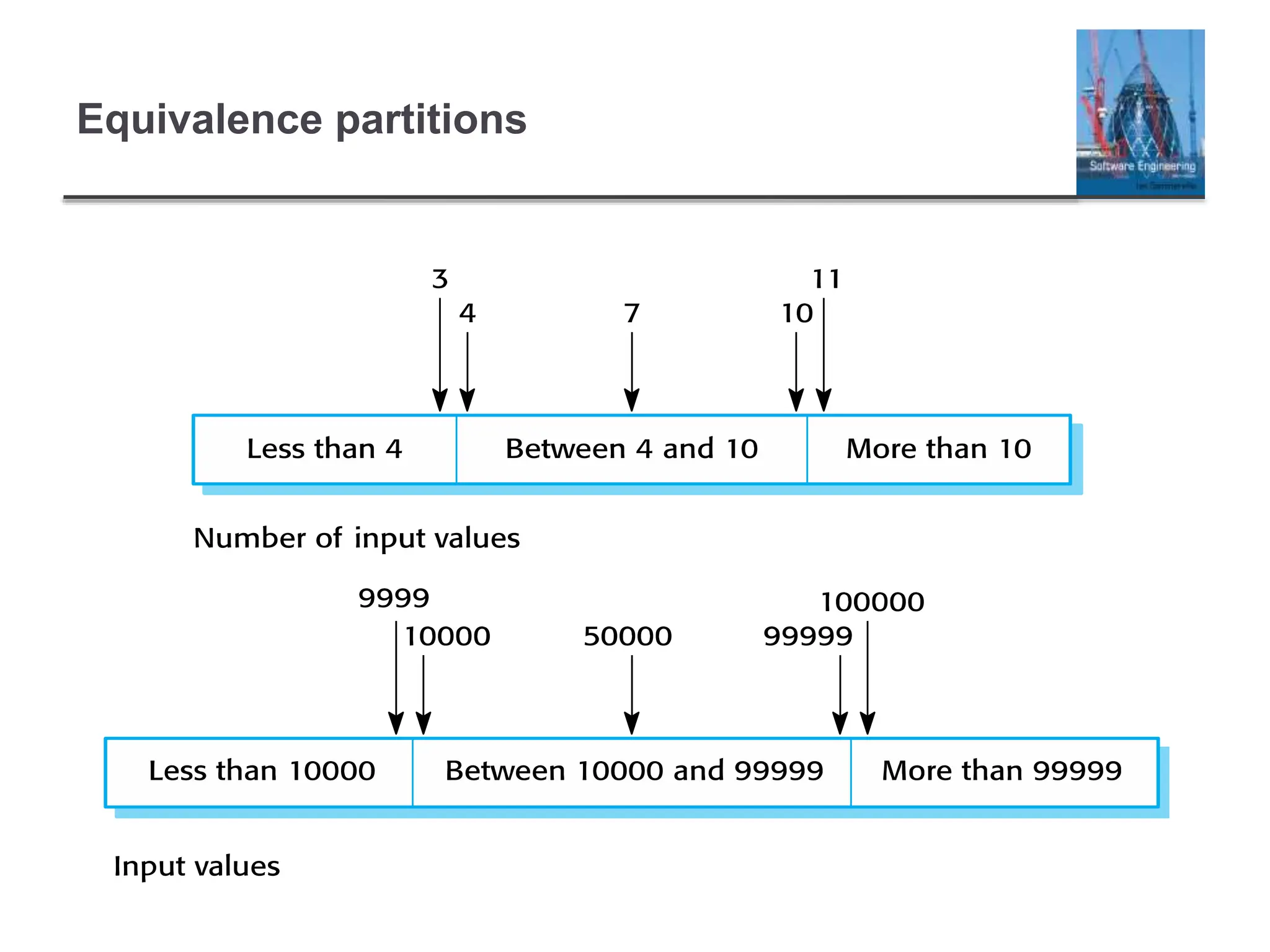
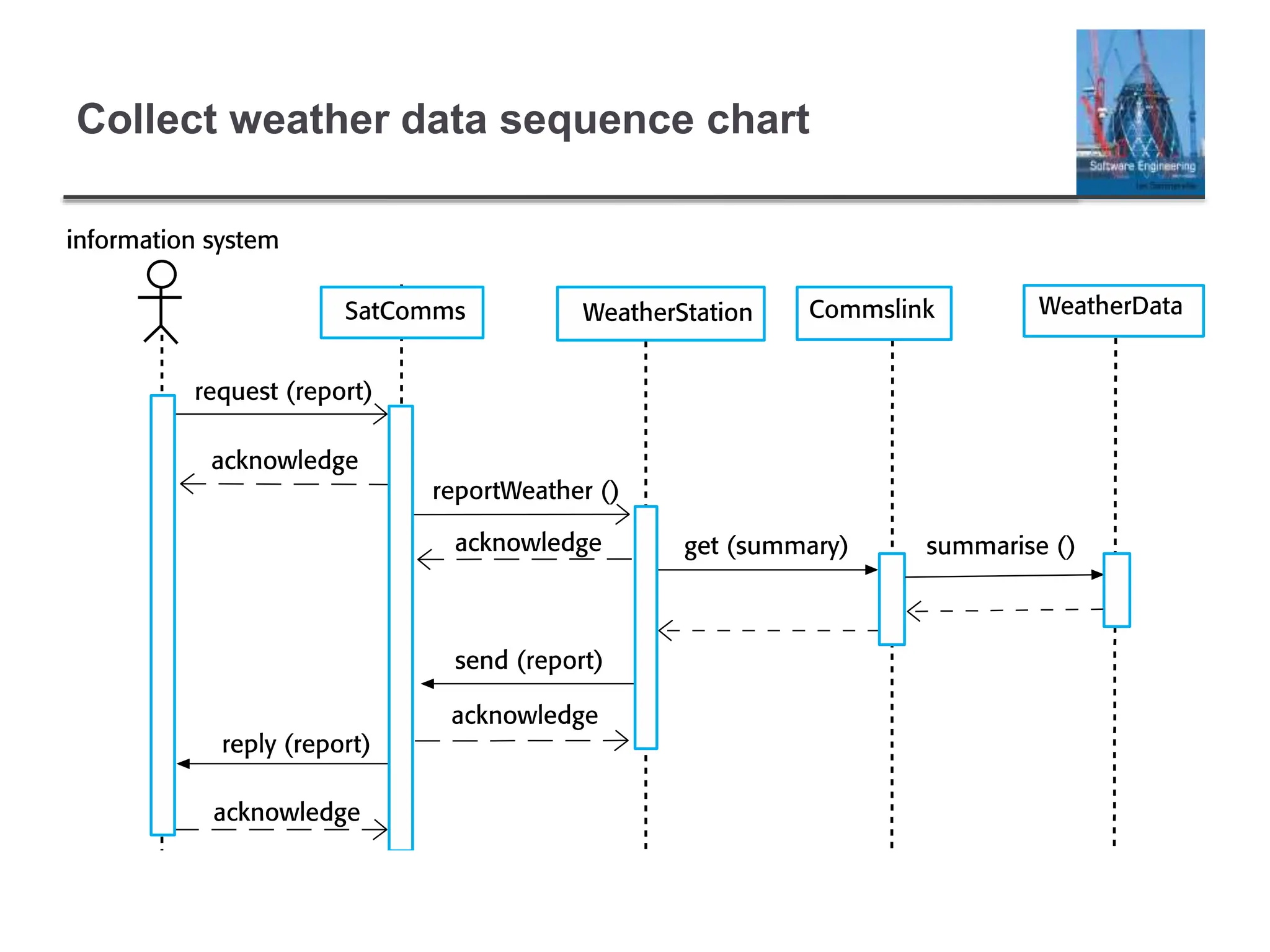
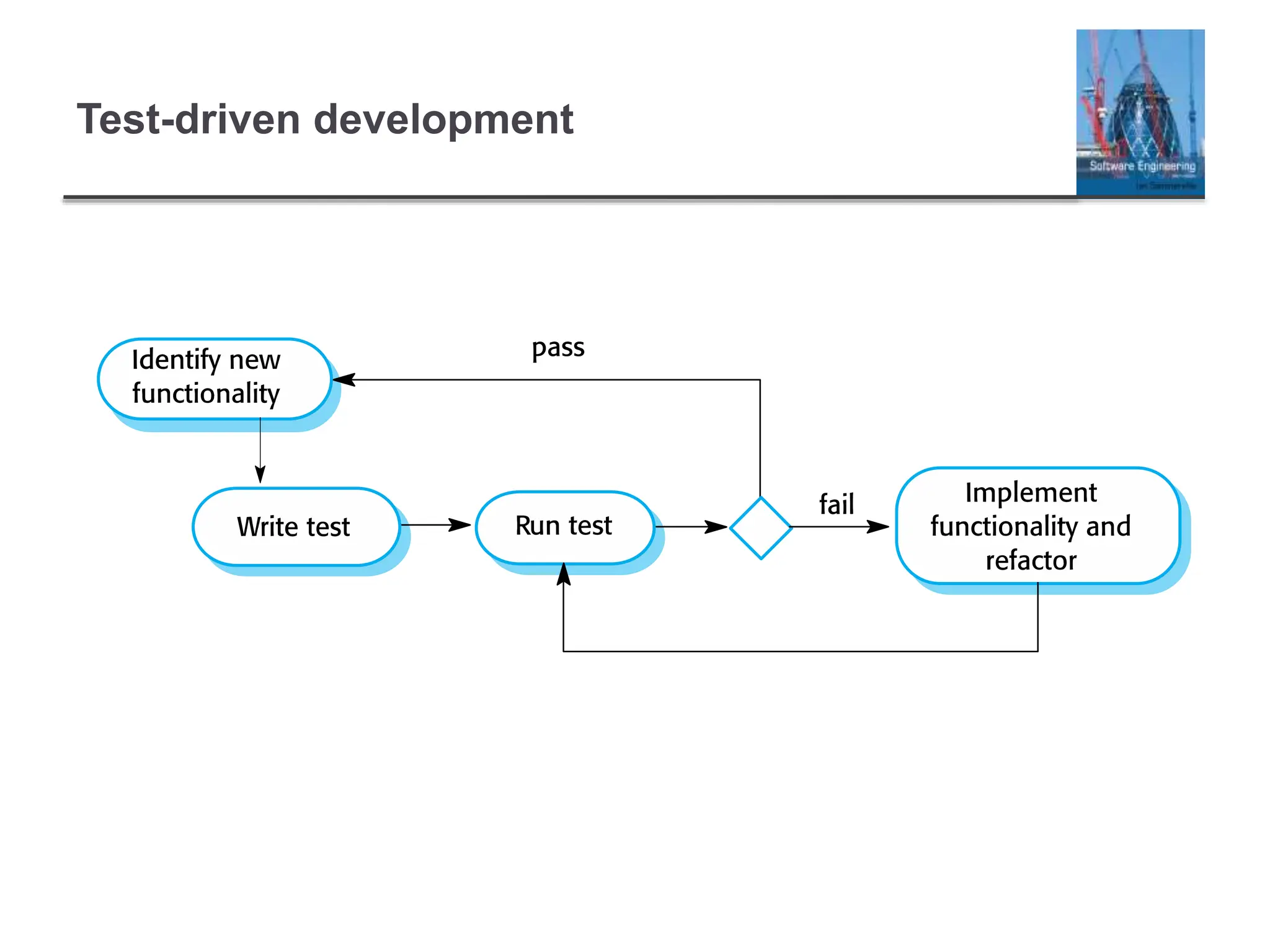
This document summarizes key topics related to software testing, including different types of testing (development, release, user), testing goals (validation, defect detection), and testing techniques (unit testing, integration testing, requirements-based testing). It describes the testing process from writing test cases to executing them and comparing results to expected outputs. Test-driven development is introduced as an approach where tests are written before code to validate functionality in small increments. The document emphasizes that testing can find bugs but not guarantee their absence, and that a variety of techniques including inspections are needed to establish software quality and reliability.