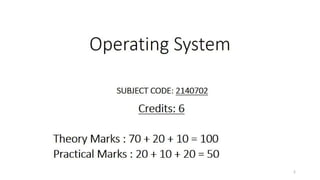
OS Unit 1 - Introduction to Operating System
•
1 like•73 views
Definition Generations of Operating systems Types of Operating Systems OS Service System Calls OS structure Layered Monolithic Operating Systems Micro-kernel Operating Systems Concept of Virtual Machine
Report
Share
Report
Share
Download to read offline
Recommended
WD - Unit - 7 - Advanced Concepts

Asynchronous Web requests using AJAX, Creating REST API using PHP
jQuery: Working with jQuery, Using plugins in jQuery and Creating Image slider, Generating charts from data using 3rd Party Libs
WD - Unit - 4 - PHP Basics

Introduction to Server side programming , PHP variables, decision and looping with examples, PHP and HTML, Arrays, Functions, Browser control and detection, String, Form processing, File uploads, Dates and timezone, Working with Regular Expressions, Exception Handling, Working with JSON data, Object Oriented Programming with PHP
WD - Unit - 3 - Java Script

Javascript Syntax, Types of Javascript, variables, arrays, functions, conditions, loops, Pop up boxes, Javascript objects and DOM, Javascript inbuilt functions, Javascript validations, Regular expressions, Event handling with Javascript, Callbacks in Javascript, Function as arguments in Javascript, Object concepts in Javascript
WD - Unit - 6 - Database Connectivity using PHP

Basic commands for database connection and query execution with CURD examples, Object oriented database access using PHP
WD - Unit - 5 - Session and State Management using PHP

Need of session management, Various techniques for state and session management like: Hidden Fields, Query String, Cookie and Session
WD - Unit - 2 - HTML & CSS

HTML page structure, formatting tags in HTML, tables, links, images, meta tags, frames, html form tags, media, APIs, HTML5 tags in relation to validations and SEO.
CSS: Need for CSS, Basic syntax and structure, Backgrounds, Colors and properties, Manipulating texts, Fonts, borders and boxes, Margins, Padding Lists, CSS2, CSS3, Animations, Tool-Tips, Style images, Variables, Flex Box, Media Queries, Wildcard Selectors (*, ^ and $) in CSS, Working with Gradients, Pseudo Class, Pseudo elements, basic of frameworks like Bootstrap, Responsive web design and Media Query, CSS variables
WD - Unit - 1 - Introduction

Basics of WWW, HTTP protocol methods and headers, HTTP Request and Response, Architecture of web browser, Web server installation and configuration, Web security, CORS, Understanding SEO
OSV - Unit - 8 - Unix/Linux Operating System

Development Of Unix/Linux, Role & Function Of Kernel, System Calls, Elementary Linux command & Shell Programming, Directory Structure, System Administration
Case study: Linux, Windows Operating System
Recommended
WD - Unit - 7 - Advanced Concepts

Asynchronous Web requests using AJAX, Creating REST API using PHP
jQuery: Working with jQuery, Using plugins in jQuery and Creating Image slider, Generating charts from data using 3rd Party Libs
WD - Unit - 4 - PHP Basics

Introduction to Server side programming , PHP variables, decision and looping with examples, PHP and HTML, Arrays, Functions, Browser control and detection, String, Form processing, File uploads, Dates and timezone, Working with Regular Expressions, Exception Handling, Working with JSON data, Object Oriented Programming with PHP
WD - Unit - 3 - Java Script

Javascript Syntax, Types of Javascript, variables, arrays, functions, conditions, loops, Pop up boxes, Javascript objects and DOM, Javascript inbuilt functions, Javascript validations, Regular expressions, Event handling with Javascript, Callbacks in Javascript, Function as arguments in Javascript, Object concepts in Javascript
WD - Unit - 6 - Database Connectivity using PHP

Basic commands for database connection and query execution with CURD examples, Object oriented database access using PHP
WD - Unit - 5 - Session and State Management using PHP

Need of session management, Various techniques for state and session management like: Hidden Fields, Query String, Cookie and Session
WD - Unit - 2 - HTML & CSS

HTML page structure, formatting tags in HTML, tables, links, images, meta tags, frames, html form tags, media, APIs, HTML5 tags in relation to validations and SEO.
CSS: Need for CSS, Basic syntax and structure, Backgrounds, Colors and properties, Manipulating texts, Fonts, borders and boxes, Margins, Padding Lists, CSS2, CSS3, Animations, Tool-Tips, Style images, Variables, Flex Box, Media Queries, Wildcard Selectors (*, ^ and $) in CSS, Working with Gradients, Pseudo Class, Pseudo elements, basic of frameworks like Bootstrap, Responsive web design and Media Query, CSS variables
WD - Unit - 1 - Introduction

Basics of WWW, HTTP protocol methods and headers, HTTP Request and Response, Architecture of web browser, Web server installation and configuration, Web security, CORS, Understanding SEO
OSV - Unit - 8 - Unix/Linux Operating System

Development Of Unix/Linux, Role & Function Of Kernel, System Calls, Elementary Linux command & Shell Programming, Directory Structure, System Administration
Case study: Linux, Windows Operating System
OSV - Unit - 10 - Approaches to Virtualization

Processor Issue, Memory Management, I/O Management, VMware ESXi, Microsoft Hyper-V and Xen Variants, Java VM, Linux VServer Virtual Machine Architecture, Android Virtual Machine.
OSV - Unit - 9 - Virtualization Concepts

Virtual machines; supporting multiple operating systems simultaneously on a single hardware platform; running one operating system on top of another. True or pure virtualization.
OSV - Unit - 7 - I/O Management & Disk scheduling

I/O Devices, Organization of I/O functions, Operating System Design issues, I/O
Buffering, Disk Scheduling (FCFS, SCAN, C-SCAN, SSTF), RAID, Disk
Cache
OSV - Unit - 6 - Memory Management

Memory Management requirements, Memory partitioning: Fixed and Variable Partitioning, Memory Allocation: Allocation Strategies (First Fit, Best Fit, and Worst Fit), Swapping, Paging and Fragmentation. Demand Paging, Security Issues.
Virtual Memory: Concepts, VM management, Page Replacement Policies (FIFO, LRU, Optimal, Other Strategies), Thrashing.
CNS - Unit - 10 - Web Security Threats and Approaches

Web Security threats and approaches, SSL architecture and protocol, Transport layer security, HTTPS and SSH
OSV - Unit - 5 - Deadlock

Principles of Deadlock, Starvation, Deadlock Prevention, Deadlock Avoidance, Deadlock Detection, System calls.
OSV - Unit - 4 - Inter Process Communication

Inter Process Communication:
Race Conditions, Critical Section, Mutual Exclusion, Hardware Solution, Strict Alternation, Peterson’s Solution, The Producer Consumer Problem, Semaphores, Event Counters, Monitors, Message Passing, Classical IPC Problems: Reader’s & Writer Problem, Dinning Philosopher Problem etc., Scheduling, Scheduling Algorithms.
OSV - Unit - 3 - Concurrency

Concurrency: Principles of Concurrency, Mutual Exclusion: S/W approaches, H/W Support, Semaphores, Pipes, Message Passing, Signals, and Monitors.
OSV - Unit - 2 - Process and Threads Management

Process and Threads Management: Process Concept, Process states, Process control, Threads, Uni-processor Scheduling: Types of scheduling: Preemptive, Non preemptive, Scheduling algorithms: FCFS, SJF, RR, Priority, Thread Scheduling, Real Time Scheduling. System calls like ps, fork, join, exec family, wait.
CNS - Unit - 8 - Key Management and Distribution

Key management and distribution, symmetric key distribution using symmetric and asymmetric encryptions, distribution of public keys, X.509 certificates, Public key infrastructure
CNS - Unit - 7 - Digital Signature

Digital Signature, its properties, requirements and security, various digital signature schemes (Elgamal and Schnorr), NIST digital Signature algorithm
CNS - Unit - 6 - Message Authentication Code

Message Authentication Codes, its requirements and security, MACs based on Hash Functions, Macs based on Block Ciphers
CNS - Unit - 5 - Cryptographic Hash Functions

Cryptographic Hash Functions, their applications, Simple hash functions, its requirements and security, Hash functions based on Cipher Block Chaining, Secure Hash Algorithm (SHA)
CNS - Unit - 4 - Public Key Cryptosystem 

Public Key Cryptosystems with Applications, Requirements and
Cryptanalysis, RSA algorithm, its computational aspects and security, Diffie-Hillman Key Exchange algorithm, Man-in-Middle attack
CNS - Unit - 3 - Block Cipher Mode

Multiple encryption and triple DES, Electronic Code Book, Cipher Block Chaining Mode, Cipher Feedback mode, Output Feedback mode, Counter mode
OSV - Unit - 1 - Introduction

Computer system overview, Architecture, Goals & Structures of
O.S, Basic functions, Interaction of O.S. & hardware architecture, System calls,
Batch, multiprogramming. Multitasking, time sharing, parallel, distributed & realtime
O.S.
CNS - Unit - 2 - Stream Ciphers and Block Ciphers

Stream ciphers and block ciphers, Block Cipher structure, Data Encryption standard (DES) with example, strength of DES, Design principles of block cipher, AES with structure, its transformation functions, key expansion, example and implementation
CNS - Unit - 1 - Introduction

Security services, security services, security mechanisms
Finite fields – group, ring, fields, modular arithmetic, The Euclidean algorithm.Symmetric Cipher Model, Cryptography, Cryptanalysis and Attacks; Substitution and Transposition techniques
DC - Unit - 6 - Mathematical Preliminaries for Lossy Coding

Distortion criteria – The Human Visual System, Auditory Perception Models – Probability Models, Linear System Models, Physical Models Scalar Quantization: The Quantization Problem Uniform Quantizer Adaptive Quantization – Forward Adaptive , Backward Adaptive Non uniform Quantization – pdf optimized Quantization, Companded Quantization Entropy Coded Quantization – Entropy coding of Lloyd – Max Quantizer Outputs Vector Quantization : Advantages of Vector Quantization over Scalar Quantization The Linde-Buzo-Gray Algorithm Tree structured Vector Quantization Structured Vector Quantization
The Benefits and Techniques of Trenchless Pipe Repair.pdf

Explore the innovative world of trenchless pipe repair with our comprehensive guide, "The Benefits and Techniques of Trenchless Pipe Repair." This document delves into the modern methods of repairing underground pipes without the need for extensive excavation, highlighting the numerous advantages and the latest techniques used in the industry.
Learn about the cost savings, reduced environmental impact, and minimal disruption associated with trenchless technology. Discover detailed explanations of popular techniques such as pipe bursting, cured-in-place pipe (CIPP) lining, and directional drilling. Understand how these methods can be applied to various types of infrastructure, from residential plumbing to large-scale municipal systems.
Ideal for homeowners, contractors, engineers, and anyone interested in modern plumbing solutions, this guide provides valuable insights into why trenchless pipe repair is becoming the preferred choice for pipe rehabilitation. Stay informed about the latest advancements and best practices in the field.
Student information management system project report ii.pdf

Our project explains about the student management. This project mainly explains the various actions related to student details. This project shows some ease in adding, editing and deleting the student details. It also provides a less time consuming process for viewing, adding, editing and deleting the marks of the students.
More Related Content
More from Gyanmanjari Institute Of Technology
OSV - Unit - 10 - Approaches to Virtualization

Processor Issue, Memory Management, I/O Management, VMware ESXi, Microsoft Hyper-V and Xen Variants, Java VM, Linux VServer Virtual Machine Architecture, Android Virtual Machine.
OSV - Unit - 9 - Virtualization Concepts

Virtual machines; supporting multiple operating systems simultaneously on a single hardware platform; running one operating system on top of another. True or pure virtualization.
OSV - Unit - 7 - I/O Management & Disk scheduling

I/O Devices, Organization of I/O functions, Operating System Design issues, I/O
Buffering, Disk Scheduling (FCFS, SCAN, C-SCAN, SSTF), RAID, Disk
Cache
OSV - Unit - 6 - Memory Management

Memory Management requirements, Memory partitioning: Fixed and Variable Partitioning, Memory Allocation: Allocation Strategies (First Fit, Best Fit, and Worst Fit), Swapping, Paging and Fragmentation. Demand Paging, Security Issues.
Virtual Memory: Concepts, VM management, Page Replacement Policies (FIFO, LRU, Optimal, Other Strategies), Thrashing.
CNS - Unit - 10 - Web Security Threats and Approaches

Web Security threats and approaches, SSL architecture and protocol, Transport layer security, HTTPS and SSH
OSV - Unit - 5 - Deadlock

Principles of Deadlock, Starvation, Deadlock Prevention, Deadlock Avoidance, Deadlock Detection, System calls.
OSV - Unit - 4 - Inter Process Communication

Inter Process Communication:
Race Conditions, Critical Section, Mutual Exclusion, Hardware Solution, Strict Alternation, Peterson’s Solution, The Producer Consumer Problem, Semaphores, Event Counters, Monitors, Message Passing, Classical IPC Problems: Reader’s & Writer Problem, Dinning Philosopher Problem etc., Scheduling, Scheduling Algorithms.
OSV - Unit - 3 - Concurrency

Concurrency: Principles of Concurrency, Mutual Exclusion: S/W approaches, H/W Support, Semaphores, Pipes, Message Passing, Signals, and Monitors.
OSV - Unit - 2 - Process and Threads Management

Process and Threads Management: Process Concept, Process states, Process control, Threads, Uni-processor Scheduling: Types of scheduling: Preemptive, Non preemptive, Scheduling algorithms: FCFS, SJF, RR, Priority, Thread Scheduling, Real Time Scheduling. System calls like ps, fork, join, exec family, wait.
CNS - Unit - 8 - Key Management and Distribution

Key management and distribution, symmetric key distribution using symmetric and asymmetric encryptions, distribution of public keys, X.509 certificates, Public key infrastructure
CNS - Unit - 7 - Digital Signature

Digital Signature, its properties, requirements and security, various digital signature schemes (Elgamal and Schnorr), NIST digital Signature algorithm
CNS - Unit - 6 - Message Authentication Code

Message Authentication Codes, its requirements and security, MACs based on Hash Functions, Macs based on Block Ciphers
CNS - Unit - 5 - Cryptographic Hash Functions

Cryptographic Hash Functions, their applications, Simple hash functions, its requirements and security, Hash functions based on Cipher Block Chaining, Secure Hash Algorithm (SHA)
CNS - Unit - 4 - Public Key Cryptosystem 

Public Key Cryptosystems with Applications, Requirements and
Cryptanalysis, RSA algorithm, its computational aspects and security, Diffie-Hillman Key Exchange algorithm, Man-in-Middle attack
CNS - Unit - 3 - Block Cipher Mode

Multiple encryption and triple DES, Electronic Code Book, Cipher Block Chaining Mode, Cipher Feedback mode, Output Feedback mode, Counter mode
OSV - Unit - 1 - Introduction

Computer system overview, Architecture, Goals & Structures of
O.S, Basic functions, Interaction of O.S. & hardware architecture, System calls,
Batch, multiprogramming. Multitasking, time sharing, parallel, distributed & realtime
O.S.
CNS - Unit - 2 - Stream Ciphers and Block Ciphers

Stream ciphers and block ciphers, Block Cipher structure, Data Encryption standard (DES) with example, strength of DES, Design principles of block cipher, AES with structure, its transformation functions, key expansion, example and implementation
CNS - Unit - 1 - Introduction

Security services, security services, security mechanisms
Finite fields – group, ring, fields, modular arithmetic, The Euclidean algorithm.Symmetric Cipher Model, Cryptography, Cryptanalysis and Attacks; Substitution and Transposition techniques
DC - Unit - 6 - Mathematical Preliminaries for Lossy Coding

Distortion criteria – The Human Visual System, Auditory Perception Models – Probability Models, Linear System Models, Physical Models Scalar Quantization: The Quantization Problem Uniform Quantizer Adaptive Quantization – Forward Adaptive , Backward Adaptive Non uniform Quantization – pdf optimized Quantization, Companded Quantization Entropy Coded Quantization – Entropy coding of Lloyd – Max Quantizer Outputs Vector Quantization : Advantages of Vector Quantization over Scalar Quantization The Linde-Buzo-Gray Algorithm Tree structured Vector Quantization Structured Vector Quantization
More from Gyanmanjari Institute Of Technology (20)
CNS - Unit - 10 - Web Security Threats and Approaches

CNS - Unit - 10 - Web Security Threats and Approaches
DC - Unit - 6 - Mathematical Preliminaries for Lossy Coding

DC - Unit - 6 - Mathematical Preliminaries for Lossy Coding
Recently uploaded
The Benefits and Techniques of Trenchless Pipe Repair.pdf

Explore the innovative world of trenchless pipe repair with our comprehensive guide, "The Benefits and Techniques of Trenchless Pipe Repair." This document delves into the modern methods of repairing underground pipes without the need for extensive excavation, highlighting the numerous advantages and the latest techniques used in the industry.
Learn about the cost savings, reduced environmental impact, and minimal disruption associated with trenchless technology. Discover detailed explanations of popular techniques such as pipe bursting, cured-in-place pipe (CIPP) lining, and directional drilling. Understand how these methods can be applied to various types of infrastructure, from residential plumbing to large-scale municipal systems.
Ideal for homeowners, contractors, engineers, and anyone interested in modern plumbing solutions, this guide provides valuable insights into why trenchless pipe repair is becoming the preferred choice for pipe rehabilitation. Stay informed about the latest advancements and best practices in the field.
Student information management system project report ii.pdf

Our project explains about the student management. This project mainly explains the various actions related to student details. This project shows some ease in adding, editing and deleting the student details. It also provides a less time consuming process for viewing, adding, editing and deleting the marks of the students.
Gen AI Study Jams _ For the GDSC Leads in India.pdf

Gen AI Study Jams _ For the GDSC Leads in India.pdf
Hierarchical Digital Twin of a Naval Power System

A hierarchical digital twin of a Naval DC power system has been developed and experimentally verified. Similar to other state-of-the-art digital twins, this technology creates a digital replica of the physical system executed in real-time or faster, which can modify hardware controls. However, its advantage stems from distributing computational efforts by utilizing a hierarchical structure composed of lower-level digital twin blocks and a higher-level system digital twin. Each digital twin block is associated with a physical subsystem of the hardware and communicates with a singular system digital twin, which creates a system-level response. By extracting information from each level of the hierarchy, power system controls of the hardware were reconfigured autonomously. This hierarchical digital twin development offers several advantages over other digital twins, particularly in the field of naval power systems. The hierarchical structure allows for greater computational efficiency and scalability while the ability to autonomously reconfigure hardware controls offers increased flexibility and responsiveness. The hierarchical decomposition and models utilized were well aligned with the physical twin, as indicated by the maximum deviations between the developed digital twin hierarchy and the hardware.
AKS UNIVERSITY Satna Final Year Project By OM Hardaha.pdf

AKS UNIVERSITY Satna Final Year Project By OM Hardaha.
Thank me later.
samsarthak31@gmail.com
Standard Reomte Control Interface - Neometrix

About
Indigenized remote control interface card suitable for MAFI system CCR equipment. Compatible for IDM8000 CCR. Backplane mounted serial and TCP/Ethernet communication module for CCR remote access. IDM 8000 CCR remote control on serial and TCP protocol.
• Remote control: Parallel or serial interface.
• Compatible with MAFI CCR system.
• Compatible with IDM8000 CCR.
• Compatible with Backplane mount serial communication.
• Compatible with commercial and Defence aviation CCR system.
• Remote control system for accessing CCR and allied system over serial or TCP.
• Indigenized local Support/presence in India.
• Easy in configuration using DIP switches.
Technical Specifications
Indigenized remote control interface card suitable for MAFI system CCR equipment. Compatible for IDM8000 CCR. Backplane mounted serial and TCP/Ethernet communication module for CCR remote access. IDM 8000 CCR remote control on serial and TCP protocol.
Key Features
Indigenized remote control interface card suitable for MAFI system CCR equipment. Compatible for IDM8000 CCR. Backplane mounted serial and TCP/Ethernet communication module for CCR remote access. IDM 8000 CCR remote control on serial and TCP protocol.
• Remote control: Parallel or serial interface
• Compatible with MAFI CCR system
• Copatiable with IDM8000 CCR
• Compatible with Backplane mount serial communication.
• Compatible with commercial and Defence aviation CCR system.
• Remote control system for accessing CCR and allied system over serial or TCP.
• Indigenized local Support/presence in India.
Application
• Remote control: Parallel or serial interface.
• Compatible with MAFI CCR system.
• Compatible with IDM8000 CCR.
• Compatible with Backplane mount serial communication.
• Compatible with commercial and Defence aviation CCR system.
• Remote control system for accessing CCR and allied system over serial or TCP.
• Indigenized local Support/presence in India.
• Easy in configuration using DIP switches.
一比一原版(SFU毕业证)西蒙菲莎大学毕业证成绩单如何办理

SFU毕业证原版定制【微信:176555708】【西蒙菲莎大学毕业证成绩单-学位证】【微信:176555708】(留信学历认证永久存档查询)采用学校原版纸张、特殊工艺完全按照原版一比一制作(包括:隐形水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠,文字图案浮雕,激光镭射,紫外荧光,温感,复印防伪)行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备,十五年致力于帮助留学生解决难题,业务范围有加拿大、英国、澳洲、韩国、美国、新加坡,新西兰等学历材料,包您满意。
◆◆◆◆◆ — — — — — — — — 【留学教育】留学归国服务中心 — — — — — -◆◆◆◆◆
【主营项目】
一.毕业证【微信:176555708】成绩单、使馆认证、教育部认证、雅思托福成绩单、学生卡等!
二.真实使馆公证(即留学回国人员证明,不成功不收费)
三.真实教育部学历学位认证(教育部存档!教育部留服网站永久可查)
四.办理各国各大学文凭(一对一专业服务,可全程监控跟踪进度)
如果您处于以下几种情况:
◇在校期间,因各种原因未能顺利毕业……拿不到官方毕业证【微信:176555708】
◇面对父母的压力,希望尽快拿到;
◇不清楚认证流程以及材料该如何准备;
◇回国时间很长,忘记办理;
◇回国马上就要找工作,办给用人单位看;
◇企事业单位必须要求办理的
◇需要报考公务员、购买免税车、落转户口
◇申请留学生创业基金
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分→ 【关于价格问题(保证一手价格)
我们所定的价格是非常合理的,而且我们现在做得单子大多数都是代理和回头客户介绍的所以一般现在有新的单子 我给客户的都是第一手的代理价格,因为我想坦诚对待大家 不想跟大家在价格方面浪费时间
对于老客户或者被老客户介绍过来的朋友,我们都会适当给一些优惠。
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
选择实体注册公司办理,更放心,更安全!我们的承诺:可来公司面谈,可签订合同,会陪同客户一起到教育部认证窗口递交认证材料,客户在教育部官方认证查询网站查询到认证通过结果后付款,不成功不收费!
学历顾问:微信:176555708
一比一原版(IIT毕业证)伊利诺伊理工大学毕业证成绩单专业办理

IIT毕业证原版定制【微信:176555708】【伊利诺伊理工大学毕业证成绩单-学位证】【微信:176555708】(留信学历认证永久存档查询)采用学校原版纸张、特殊工艺完全按照原版一比一制作(包括:隐形水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠,文字图案浮雕,激光镭射,紫外荧光,温感,复印防伪)行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备,十五年致力于帮助留学生解决难题,业务范围有加拿大、英国、澳洲、韩国、美国、新加坡,新西兰等学历材料,包您满意。
◆◆◆◆◆ — — — — — — — — 【留学教育】留学归国服务中心 — — — — — -◆◆◆◆◆
【主营项目】
一.毕业证【微信:176555708】成绩单、使馆认证、教育部认证、雅思托福成绩单、学生卡等!
二.真实使馆公证(即留学回国人员证明,不成功不收费)
三.真实教育部学历学位认证(教育部存档!教育部留服网站永久可查)
四.办理各国各大学文凭(一对一专业服务,可全程监控跟踪进度)
如果您处于以下几种情况:
◇在校期间,因各种原因未能顺利毕业……拿不到官方毕业证【微信:176555708】
◇面对父母的压力,希望尽快拿到;
◇不清楚认证流程以及材料该如何准备;
◇回国时间很长,忘记办理;
◇回国马上就要找工作,办给用人单位看;
◇企事业单位必须要求办理的
◇需要报考公务员、购买免税车、落转户口
◇申请留学生创业基金
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分→ 【关于价格问题(保证一手价格)
我们所定的价格是非常合理的,而且我们现在做得单子大多数都是代理和回头客户介绍的所以一般现在有新的单子 我给客户的都是第一手的代理价格,因为我想坦诚对待大家 不想跟大家在价格方面浪费时间
对于老客户或者被老客户介绍过来的朋友,我们都会适当给一些优惠。
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
选择实体注册公司办理,更放心,更安全!我们的承诺:可来公司面谈,可签订合同,会陪同客户一起到教育部认证窗口递交认证材料,客户在教育部官方认证查询网站查询到认证通过结果后付款,不成功不收费!
学历顾问:微信:176555708
一比一原版(UofT毕业证)多伦多大学毕业证成绩单如何办理

UofT毕业证原版定制【微信:176555708】【多伦多大学毕业证成绩单-学位证】【微信:176555708】(留信学历认证永久存档查询)采用学校原版纸张、特殊工艺完全按照原版一比一制作(包括:隐形水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠,文字图案浮雕,激光镭射,紫外荧光,温感,复印防伪)行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备,十五年致力于帮助留学生解决难题,业务范围有加拿大、英国、澳洲、韩国、美国、新加坡,新西兰等学历材料,包您满意。
◆◆◆◆◆ — — — — — — — — 【留学教育】留学归国服务中心 — — — — — -◆◆◆◆◆
【主营项目】
一.毕业证【微信:176555708】成绩单、使馆认证、教育部认证、雅思托福成绩单、学生卡等!
二.真实使馆公证(即留学回国人员证明,不成功不收费)
三.真实教育部学历学位认证(教育部存档!教育部留服网站永久可查)
四.办理各国各大学文凭(一对一专业服务,可全程监控跟踪进度)
如果您处于以下几种情况:
◇在校期间,因各种原因未能顺利毕业……拿不到官方毕业证【微信:176555708】
◇面对父母的压力,希望尽快拿到;
◇不清楚认证流程以及材料该如何准备;
◇回国时间很长,忘记办理;
◇回国马上就要找工作,办给用人单位看;
◇企事业单位必须要求办理的
◇需要报考公务员、购买免税车、落转户口
◇申请留学生创业基金
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分→ 【关于价格问题(保证一手价格)
我们所定的价格是非常合理的,而且我们现在做得单子大多数都是代理和回头客户介绍的所以一般现在有新的单子 我给客户的都是第一手的代理价格,因为我想坦诚对待大家 不想跟大家在价格方面浪费时间
对于老客户或者被老客户介绍过来的朋友,我们都会适当给一些优惠。
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
选择实体注册公司办理,更放心,更安全!我们的承诺:可来公司面谈,可签订合同,会陪同客户一起到教育部认证窗口递交认证材料,客户在教育部官方认证查询网站查询到认证通过结果后付款,不成功不收费!
学历顾问:微信:176555708
Investor-Presentation-Q1FY2024 investor presentation document.pptx

this is the investor presemtaiton document for qurrter 1 2024
Runway Orientation Based on the Wind Rose Diagram.pptx

Runway Orientation Based on the Wind Rose Diagram
RAT: Retrieval Augmented Thoughts Elicit Context-Aware Reasoning in Long-Hori...

RAT: Retrieval Augmented Thoughts Elicit Context-Aware Reasoning in Long-Horizon Generation
Governing Equations for Fundamental Aerodynamics_Anderson2010.pdf

Governing Equations for Fundamental Aerodynamics
Top 10 Oil and Gas Projects in Saudi Arabia 2024.pdf

Saudi Arabia stands as a titan in the global energy landscape, renowned for its abundant oil and gas resources. It's the largest exporter of petroleum and holds some of the world's most significant reserves. Let's delve into the top 10 oil and gas projects shaping Saudi Arabia's energy future in 2024.
Recently uploaded (20)
The Benefits and Techniques of Trenchless Pipe Repair.pdf

The Benefits and Techniques of Trenchless Pipe Repair.pdf
Student information management system project report ii.pdf

Student information management system project report ii.pdf
Gen AI Study Jams _ For the GDSC Leads in India.pdf

Gen AI Study Jams _ For the GDSC Leads in India.pdf
AKS UNIVERSITY Satna Final Year Project By OM Hardaha.pdf

AKS UNIVERSITY Satna Final Year Project By OM Hardaha.pdf
Investor-Presentation-Q1FY2024 investor presentation document.pptx

Investor-Presentation-Q1FY2024 investor presentation document.pptx
Runway Orientation Based on the Wind Rose Diagram.pptx

Runway Orientation Based on the Wind Rose Diagram.pptx
RAT: Retrieval Augmented Thoughts Elicit Context-Aware Reasoning in Long-Hori...

RAT: Retrieval Augmented Thoughts Elicit Context-Aware Reasoning in Long-Hori...
Governing Equations for Fundamental Aerodynamics_Anderson2010.pdf

Governing Equations for Fundamental Aerodynamics_Anderson2010.pdf
Top 10 Oil and Gas Projects in Saudi Arabia 2024.pdf

Top 10 Oil and Gas Projects in Saudi Arabia 2024.pdf
ML for identifying fraud using open blockchain data.pptx

ML for identifying fraud using open blockchain data.pptx
