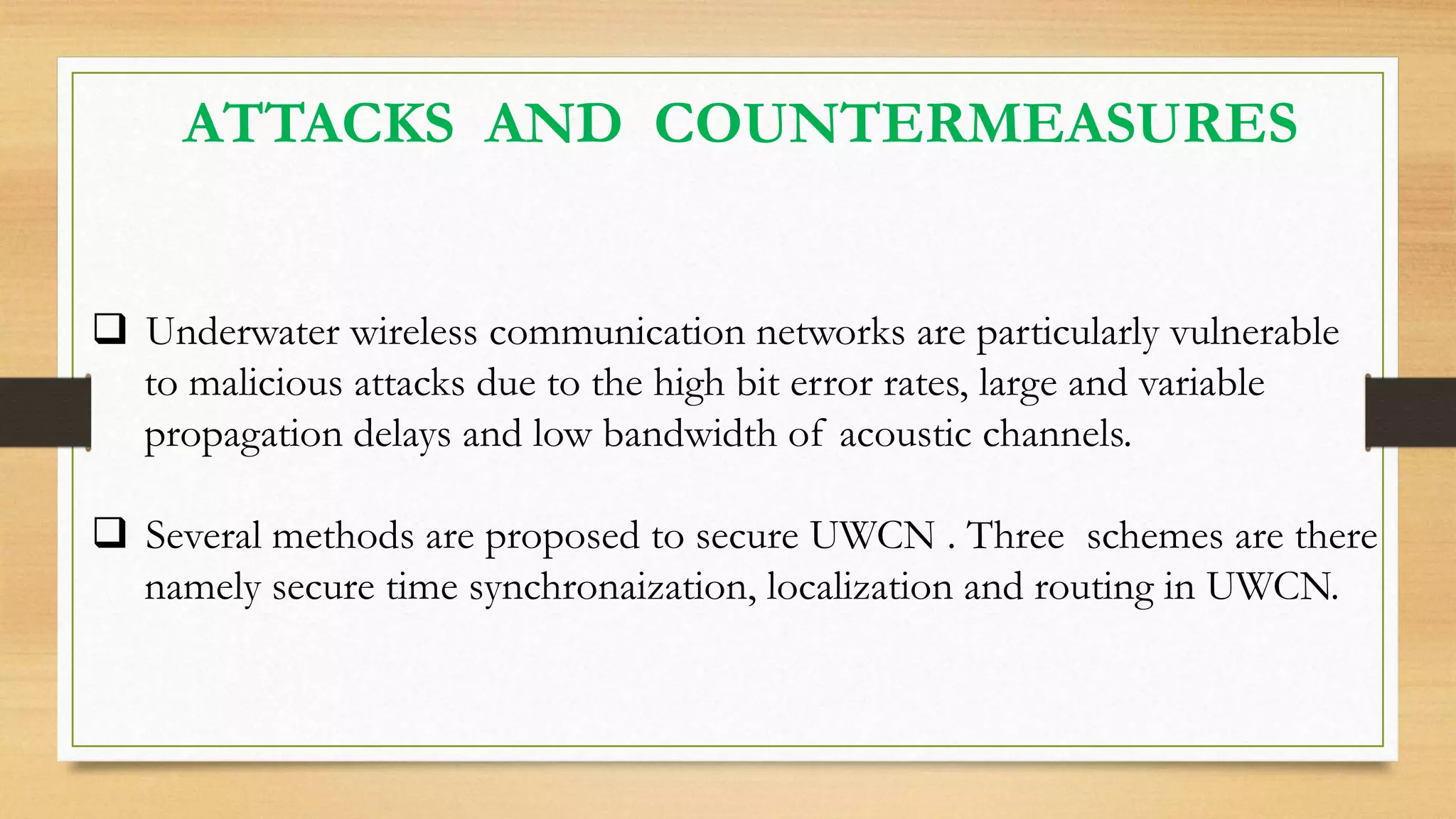
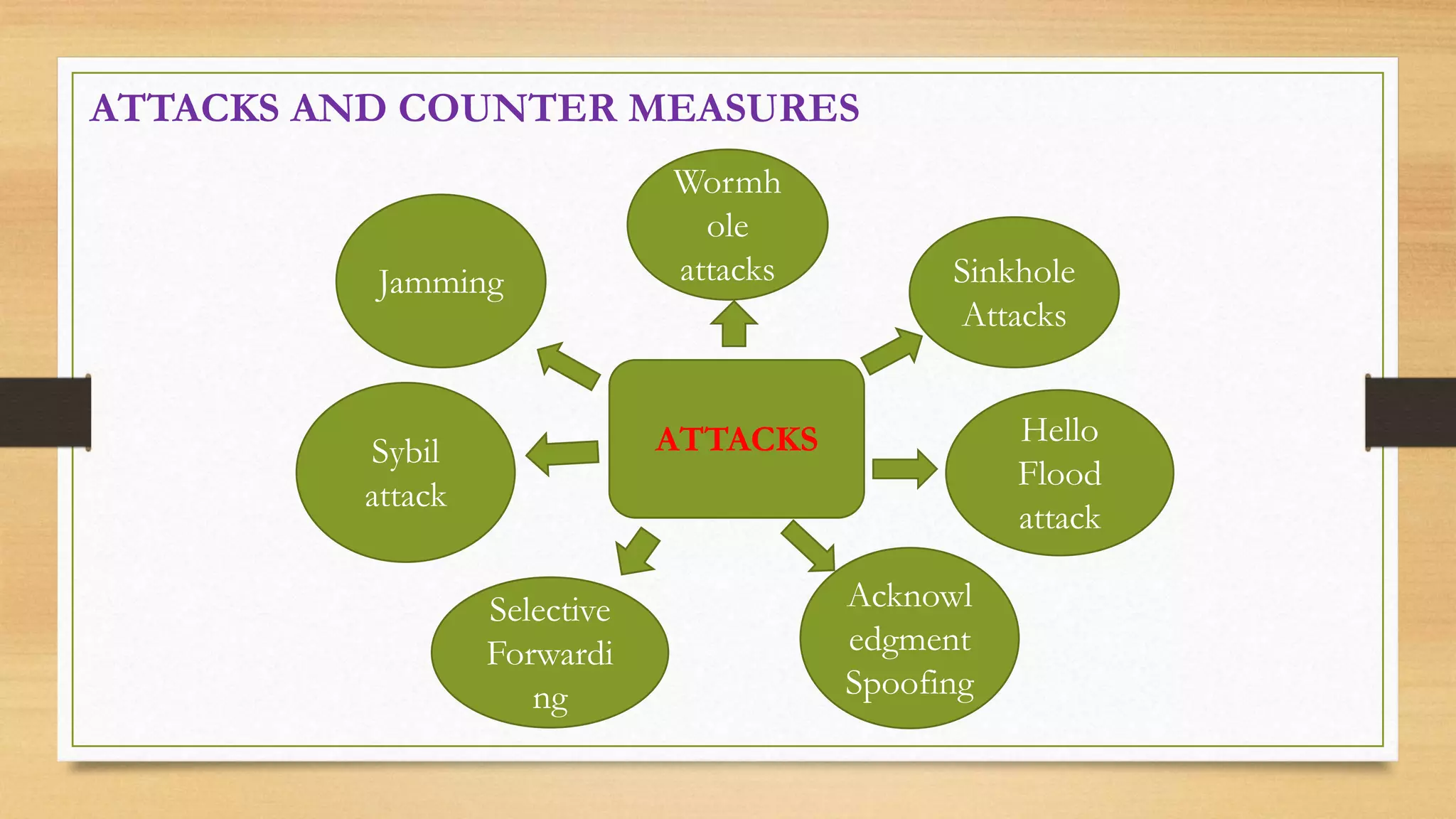
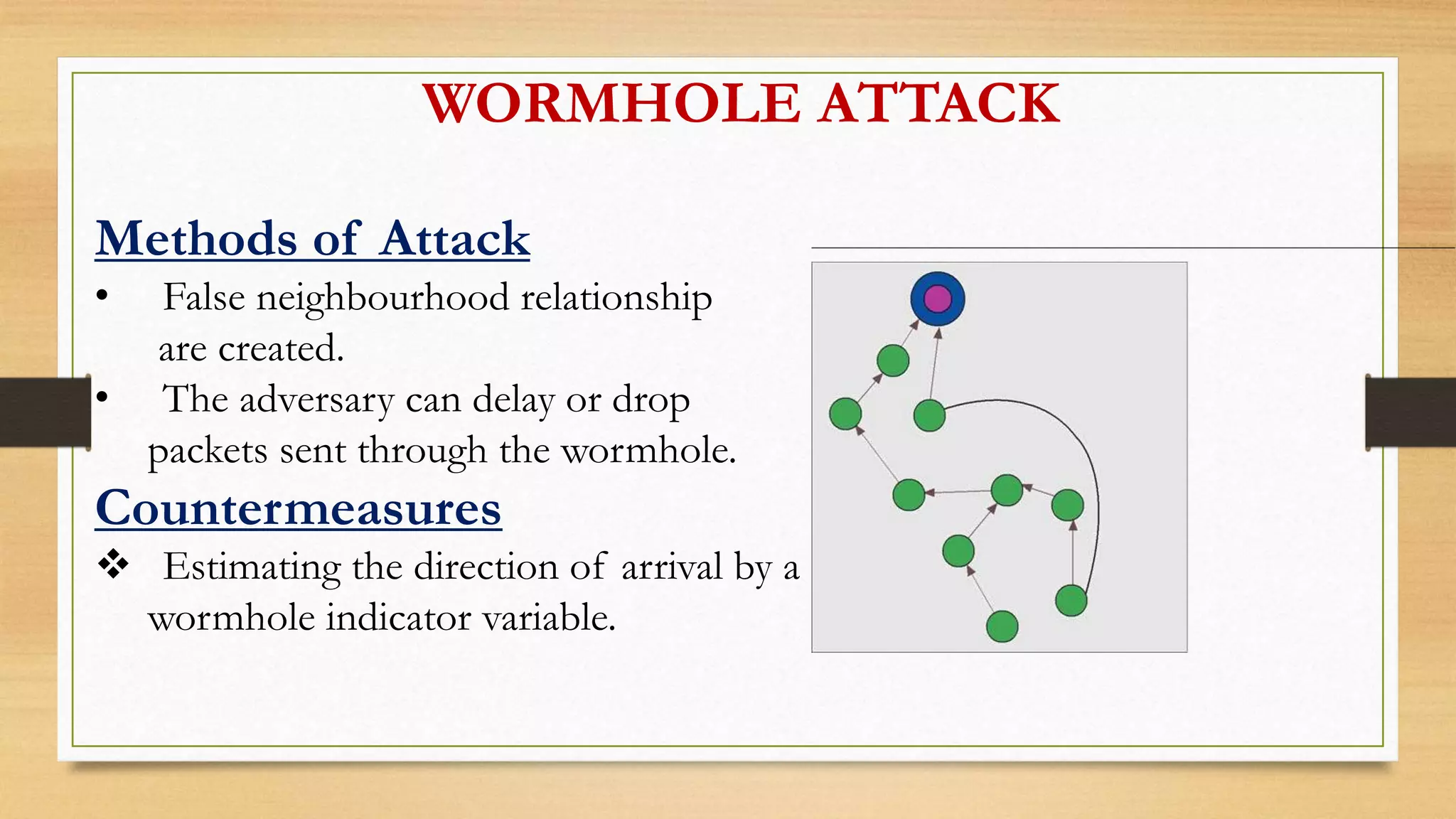
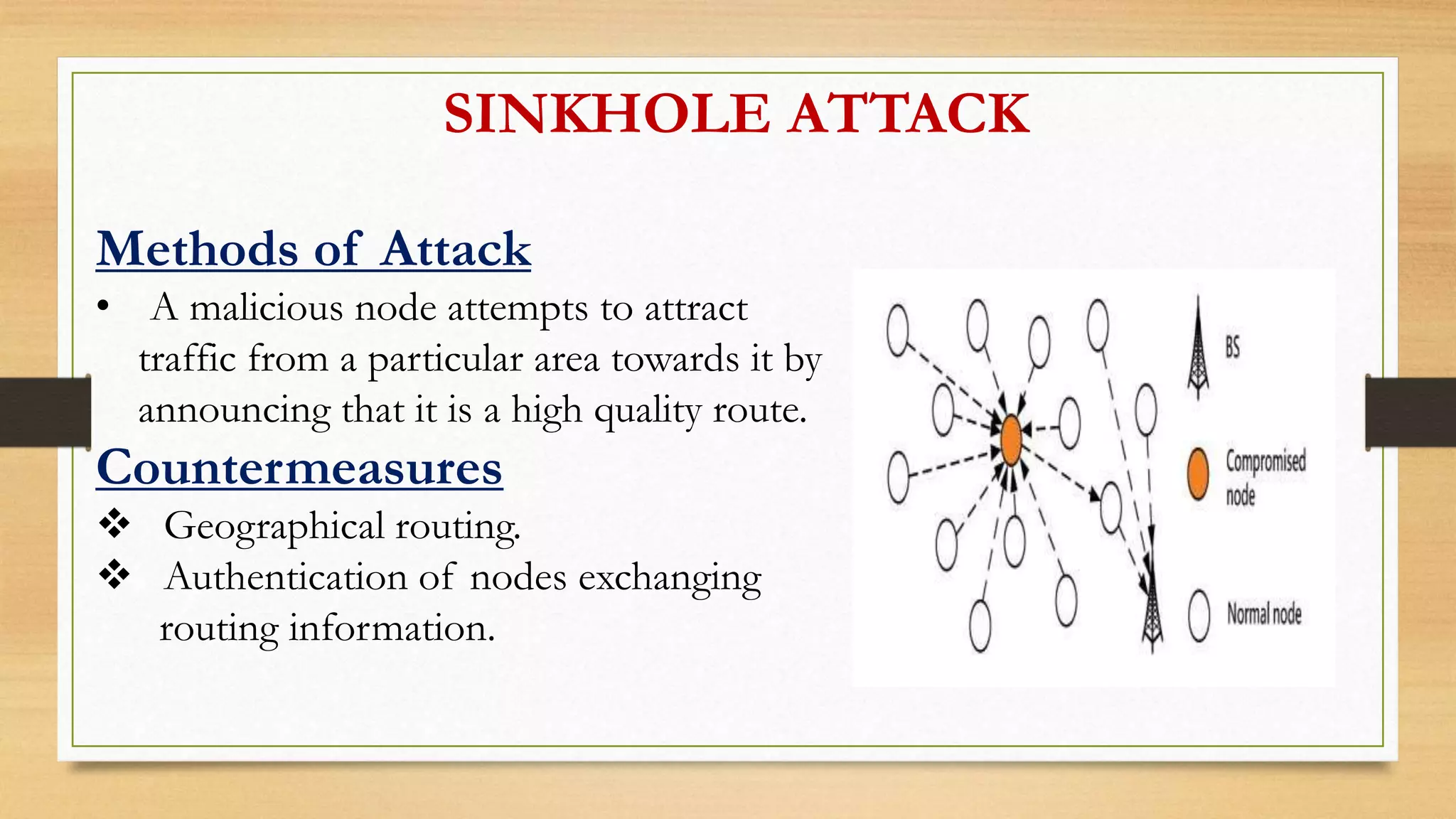
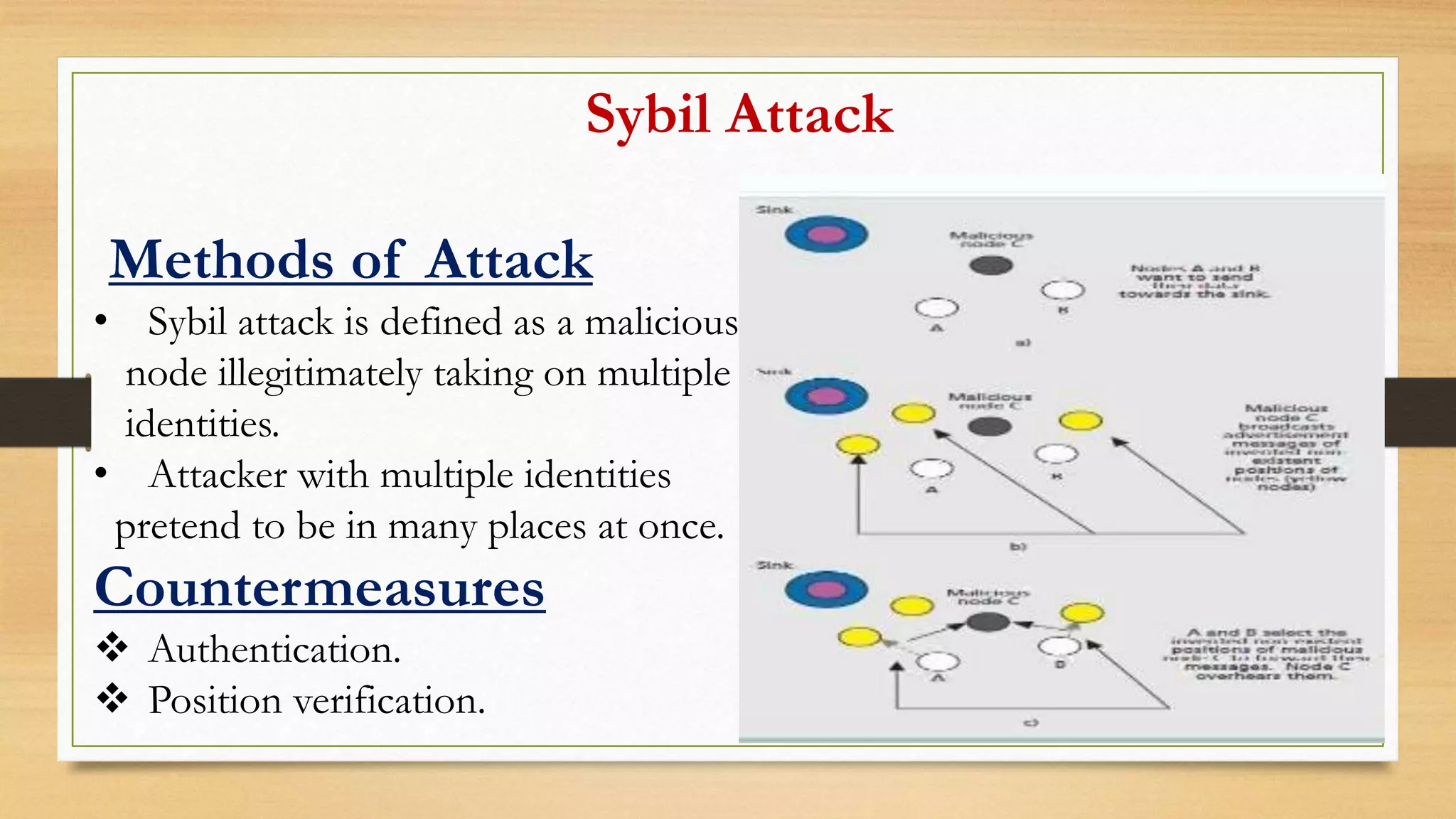
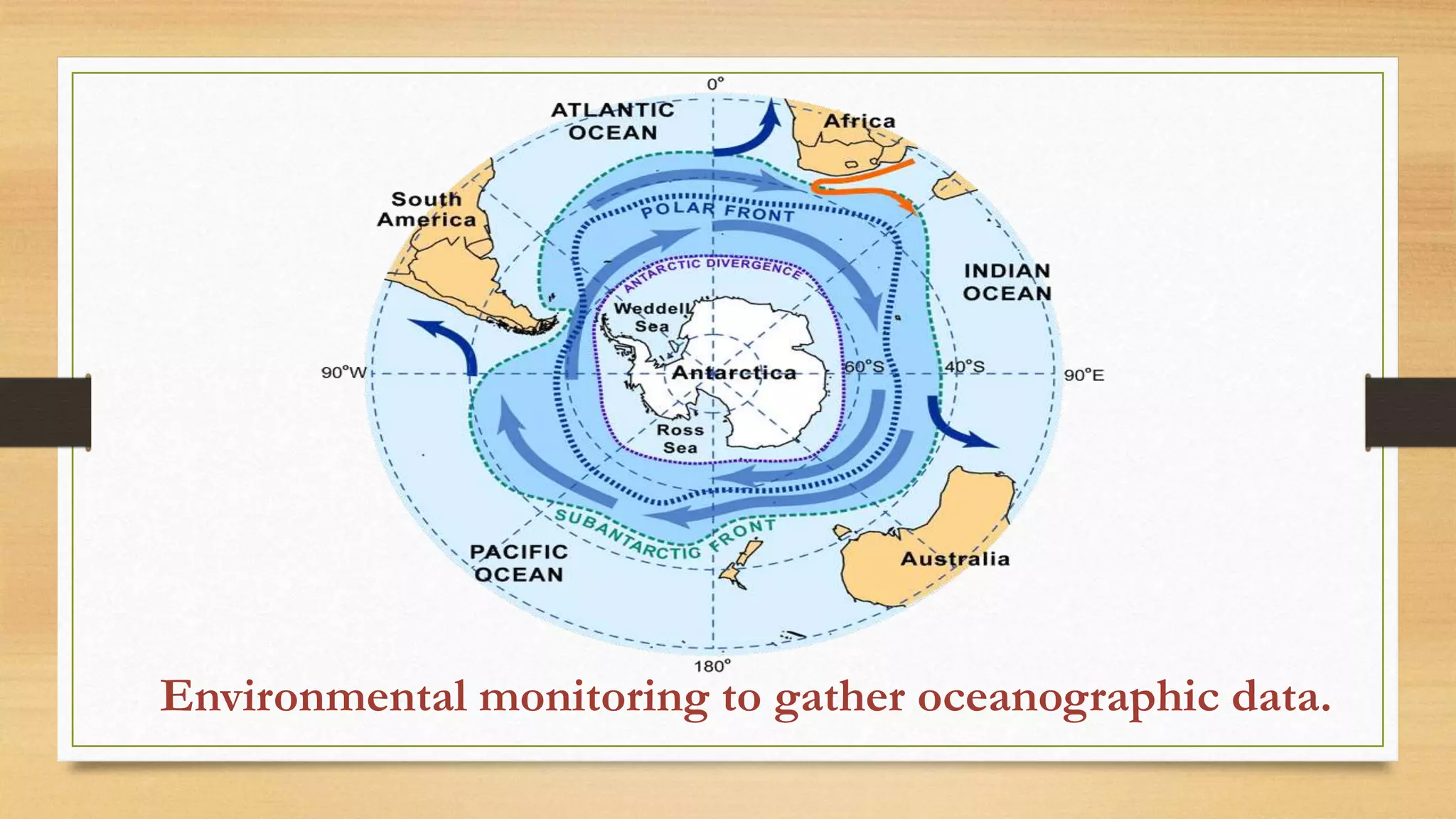
This document outlines security challenges and mechanisms for underwater wireless communication networks (UWCNs). UWCNs use acoustic links for sensors and autonomous underwater vehicles due to radio frequency absorption by water. The document discusses common attacks on UWCNs like jamming, wormholes, and selective forwarding. It proposes secure time synchronization, localization, and routing to authenticate nodes and secure the network. Potential applications of UWCNs include environmental monitoring, search and rescue missions, and marine archaeology. Key challenges are limited battery power, bandwidth, and high error rates in underwater acoustic channels.