Trkr
•Download as TXT, PDF•
0 likes•181 views
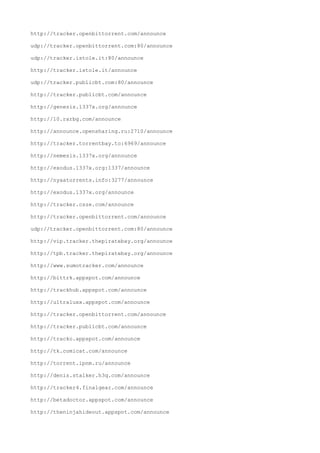
The document contains a list of 50 URLs for BitTorrent trackers. The URLs are for announcing torrents to various public trackers across the internet in order to help people find and download the torrent files.
Report
Share
Report
Share
Recommended
[Nuxeo World 2013] MARKETPLACE PACKAGES - THIBAUD ARGUILLERE![[Nuxeo World 2013] MARKETPLACE PACKAGES - THIBAUD ARGUILLERE](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[Nuxeo World 2013] MARKETPLACE PACKAGES - THIBAUD ARGUILLERE](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
The document discusses Nuxeo Marketplace Packages, which provide a structured way to package and deploy plugins and configurations. Marketplace Packages contain all necessary files within a single zip file and include rules and metadata. They can be installed, uninstalled, and upgraded via the Nuxeo Admin Center or nuxeoctl command line tool. The document provides links for more information on creating, distributing, and using Marketplace Packages.
Rastreadores 2015

This document contains a list of over 200 magnet links and torrent tracker URLs. The trackers listed are used to locate peer computers that are sharing specific torrent files across various public bittorrent swarms. Many of the trackers listed relate to popular public torrent sites like The Pirate Bay and public swarms for TV shows and movies.
Starting python

This document discusses Python, including installing multiple Python versions on CentOS, creating virtual environments (venv) for different projects, using pip to install packages, and basic concepts like modules, packages, and running Python files. It provides instructions for cloning a Python build script from GitHub, shows commands for installing Python 3.5.2 and listing available Python versions, and demonstrates creating and activating a venv.
Fuzzy Feelings for Fuzzy Matching

Lightning talk given at the Inaugural VimIndy meetup. See how FZF can make your life easier by providing an incredibly fast fuzzy matching interface.
Java 9 – The Ultimate Feature List

All new features, expected features and speculations regarding the upcoming Java 9 release: the Jigsaw project, performance improvements and long awaited APIs:
www.takipiblog.com/java-9-the-ultimate-feature-list/
USHMM CD-0204

CD for scholarly and remembrance of the Holocaust
IFUD of Human Rights / Freistaat Bayern München
1995
Vundle: Managing Vim Plugins With Sanity

This are the slides for a lightning talk (5 minute talk) I gave at work in Corvil on January 23 2014.
Vundle is a plugin that allows for a very convenient way to install, remove and keep plugins up to date.
The talk covered a bit of history of how Vundle came to be, and finally presented Vundle itself.
Public Key Cryptography

The document discusses ensuring privacy in electronic communications through the use of public key cryptography. It explains how public key cryptography works using private and public keys to encrypt messages. Keyservers are used to store and distribute public keys so that parties can encrypt messages for intended recipients without needing to share secrets beforehand. Digital signatures are also discussed as a way to verify the identity of the key holder through signing with their private key.
Recommended
[Nuxeo World 2013] MARKETPLACE PACKAGES - THIBAUD ARGUILLERE![[Nuxeo World 2013] MARKETPLACE PACKAGES - THIBAUD ARGUILLERE](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[Nuxeo World 2013] MARKETPLACE PACKAGES - THIBAUD ARGUILLERE](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
The document discusses Nuxeo Marketplace Packages, which provide a structured way to package and deploy plugins and configurations. Marketplace Packages contain all necessary files within a single zip file and include rules and metadata. They can be installed, uninstalled, and upgraded via the Nuxeo Admin Center or nuxeoctl command line tool. The document provides links for more information on creating, distributing, and using Marketplace Packages.
Rastreadores 2015

This document contains a list of over 200 magnet links and torrent tracker URLs. The trackers listed are used to locate peer computers that are sharing specific torrent files across various public bittorrent swarms. Many of the trackers listed relate to popular public torrent sites like The Pirate Bay and public swarms for TV shows and movies.
Starting python

This document discusses Python, including installing multiple Python versions on CentOS, creating virtual environments (venv) for different projects, using pip to install packages, and basic concepts like modules, packages, and running Python files. It provides instructions for cloning a Python build script from GitHub, shows commands for installing Python 3.5.2 and listing available Python versions, and demonstrates creating and activating a venv.
Fuzzy Feelings for Fuzzy Matching

Lightning talk given at the Inaugural VimIndy meetup. See how FZF can make your life easier by providing an incredibly fast fuzzy matching interface.
Java 9 – The Ultimate Feature List

All new features, expected features and speculations regarding the upcoming Java 9 release: the Jigsaw project, performance improvements and long awaited APIs:
www.takipiblog.com/java-9-the-ultimate-feature-list/
USHMM CD-0204

CD for scholarly and remembrance of the Holocaust
IFUD of Human Rights / Freistaat Bayern München
1995
Vundle: Managing Vim Plugins With Sanity

This are the slides for a lightning talk (5 minute talk) I gave at work in Corvil on January 23 2014.
Vundle is a plugin that allows for a very convenient way to install, remove and keep plugins up to date.
The talk covered a bit of history of how Vundle came to be, and finally presented Vundle itself.
Public Key Cryptography

The document discusses ensuring privacy in electronic communications through the use of public key cryptography. It explains how public key cryptography works using private and public keys to encrypt messages. Keyservers are used to store and distribute public keys so that parties can encrypt messages for intended recipients without needing to share secrets beforehand. Digital signatures are also discussed as a way to verify the identity of the key holder through signing with their private key.
9月

The document contains a list of over 100 magnet links and torrent tracker URLs. The trackers listed are used to locate peer computers that are currently sharing specific torrent files, in order to facilitate file sharing via the BitTorrent protocol.
Tracker

The document contains a list of URLs for BitTorrent trackers and torrent sites. There are over 100 URLs listed, including http and udp trackers from sites like The Pirate Bay, TorrentLeech, TorrentDownloads and more. The trackers cover a wide range of port numbers and IP addresses for distributing torrent metadata.
Tracket

This document contains a list of over 30 BitTorrent tracker URLs. BitTorrent trackers are servers that help facilitate peer-to-peer file sharing on the BitTorrent network by maintaining records of which peers are participating in sharing particular files. The list includes trackers from various domains that help users find peers to download torrent files from.
Rastreadores utorrent

The document contains a list of over 100 URLs for torrent trackers and sites. The URLs provide locations for finding torrent metadata for file sharing and peer-to-peer downloading across many domains and categories of content.
儲かるドキュメント

Sphinx is a documentation generator that can create HTML and other formats from reStructuredText markup and Python docstrings. It supports features like automatic cross-referencing, built-in search, and the ability to extend and customize the templates. Documentation built with Sphinx can be hosted on sites like ReadTheDocs for easy web hosting of project documentation.
Torrents site

The document lists several torrent websites for downloading movies and books through torrent files. For movies, the top recommendations include The Pirate Bay, KickassTorrents, Torrentz2, Torrentfunk, RARBG, EZTV, and Torlock. For books, the top torrent sites mentioned are Zooqle, 1337x, Manybooks, Books-Share, and FreebooksSpot. The document provides both regular URLs and deep web links for some of the most popular torrent indexing websites.
Dark web أخطر مواقع الانترنت الخفي وأشهرها بين الهاكرز

أخطر مواقع الانترنت الخفي وأشهرها بين الهاكرز
#Dark_web
أخطر مواقع الانترنت المظلم التي يحبها الهاكرز
تكلمنا عن الويب المظلم في عدة مقالات عبر مدونة الاحتراف الجزائري ولكن سنتكلم اليوم عن مواقع توجد عبر الويب المظلم يحبها الهكرز وهي الرقم واحد بالنسبة له ، هي مواقع سرية للغاية تباع فيها أدوية طبية ممنوعة و مخدرات و أسلحة...إلخ ، و فيها يجد الهاكرز راحته وضالته .
في هذه التدوينة سوف أقدم لكم أخطر مواقع الانترنت المظلم التي يحبها الهاكرز ، لتعرف ما نوعية هذه المواقع ولتتقرب منها أكثر ، طبعا لا يمكن الشراء منهم لان ابسط شيئ ستشتريه سيكون سعره حوالي 10 بيتكوين وهذا المبلغ لن تجده عند معظم الاشخاص .
List of micro blog websites

This document contains a list of website URLs and their associated popularity ranking scores (pr) based on a scale of 1 to 7. The most popular sites are http://blip.pl and http://identi.ca which both have a pr of 7. Several other sites receive scores between 5 and 3. The majority of sites listed receive a pr of 2 or below, with many sites only receiving a score of 1.
الجانب المظلم في التاريخ المسيحي

The document contains 30 repetitions of the URL http://kotob.no-ip.org/. The URL is repeated multiple times throughout but there is no other text or context provided.
Web3 + scams = It's a match

The document discusses various scams and vulnerabilities related to cryptocurrency and web3 technologies. It begins by introducing Zoltan Balazs and his work researching vulnerabilities. It then describes several types of scams, including rug pulls, giveaway scams, advance fee fraud, and hardware wallet scams. Best practices are suggested, such as being wary of unsolicited messages, verifying sources of apps/dapps, and using strong passwords and hardware wallets to protect funds. The overall message is that web3 and cryptocurrency technologies have enabled numerous scams that have impacted many users.
Last.fm API workshop - Stockholm

Last.fm provides a public API that allows developers to access information about music and social features on Last.fm. The API includes over 100 methods to retrieve data on artists, albums, tracks, tags, users and more. It outputs data in XML or JSON formats and supports authentication for private data. Common methods include artist.getImages, album.getTags, and track.search. Developers need an API key to access the API.
Cybersecurity Asia 2021 Conference: Learning from Honeypots

APNIC Senior Security Specialist Adli Wahid presents on the APNIC Honeynet Project at the Cybersecurity Asia 2021 Conference, held online from 11 to 12 October 2021.
互联网精神

The document discusses the history and development of the Internet from the 1970s to the present. It describes some of the key events and individuals that contributed to the creation of the Internet, including the development of TCP/IP, the creation of ARPANET, the introduction of email, the invention of the World Wide Web, and the growth of popular websites and use of the Internet around the world. The document provides context around the technological advances and standards that allowed the Internet to evolve from a small network to a global communication system.
Profile Creation Sites.docx

We are making next-Gen easy to adapt and creating your network easy to operate. Therefore, you can quickly configure, troubleshoot, and secure your network while minimizing errors. Reach us for more information about our plugin services.
Internet Librarian International #ili2016 Phil's Faves

A copy of the presentation that I gave at ILI 2016 listing the things that I've found in the last year which may be of interest to people.
Http1

The document contains a list of over 200 social bookmarking and link sharing websites along with the number of votes or bookmarks each site has received. The most popular sites include Reddit, Digg, Slashdot, Delicious, Newsvine and Diigo which have received between 7-8 votes. Many other sites on the list have received between 1-6 votes, indicating varying levels of popularity and usage for sharing and discovering web links online.
Data Vault #flushyourmeds

This document lists various archives, backups, files, and links related to literary nonsense, open source software, freedom of speech, and fringe material. It was created by Scott A. Barry and contains URLs, file links, and references to flushing medications, anti-Zionism, and anti-psychiatry topics. The document serves as a data vault for this type of material.
Creating "Secure" PHP applications, Part 2, Server Hardening

The document provides guidance on server hardening techniques. It discusses using netstat to view listening services on a server and using update-rc.d or chkconfig to disable unnecessary services from starting at boot. It also recommends enabling access control lists (ACLs) in file system mounts, using SELinux or AppArmor to enforce mandatory access controls, and setting reasonable PHP memory limits to prevent potential denial of service attacks. The document stresses the importance of only allowing approved applications to execute and knowing the resource limits of the server to avoid potential outages.
Top 100 web2.0

This document contains a list of over 80 website URLs. It includes a variety of social media sites, blogging platforms, online communities and forums. Some of the sites listed are more commonly known such as WordPress, Xing and LiveJournal, while others on the list may be less familiar. The document provides a wide sampling of websites across different categories and usage types.
Robots

This document contains a robots.txt file with directives to disallow crawling of the entire site ("/") by over 200 bot user agents to prevent unwanted indexing and scraping of website content. The file should be uploaded to the root folder to block these bots from accessing the site.
More Related Content
Similar to Trkr
9月

The document contains a list of over 100 magnet links and torrent tracker URLs. The trackers listed are used to locate peer computers that are currently sharing specific torrent files, in order to facilitate file sharing via the BitTorrent protocol.
Tracker

The document contains a list of URLs for BitTorrent trackers and torrent sites. There are over 100 URLs listed, including http and udp trackers from sites like The Pirate Bay, TorrentLeech, TorrentDownloads and more. The trackers cover a wide range of port numbers and IP addresses for distributing torrent metadata.
Tracket

This document contains a list of over 30 BitTorrent tracker URLs. BitTorrent trackers are servers that help facilitate peer-to-peer file sharing on the BitTorrent network by maintaining records of which peers are participating in sharing particular files. The list includes trackers from various domains that help users find peers to download torrent files from.
Rastreadores utorrent

The document contains a list of over 100 URLs for torrent trackers and sites. The URLs provide locations for finding torrent metadata for file sharing and peer-to-peer downloading across many domains and categories of content.
儲かるドキュメント

Sphinx is a documentation generator that can create HTML and other formats from reStructuredText markup and Python docstrings. It supports features like automatic cross-referencing, built-in search, and the ability to extend and customize the templates. Documentation built with Sphinx can be hosted on sites like ReadTheDocs for easy web hosting of project documentation.
Torrents site

The document lists several torrent websites for downloading movies and books through torrent files. For movies, the top recommendations include The Pirate Bay, KickassTorrents, Torrentz2, Torrentfunk, RARBG, EZTV, and Torlock. For books, the top torrent sites mentioned are Zooqle, 1337x, Manybooks, Books-Share, and FreebooksSpot. The document provides both regular URLs and deep web links for some of the most popular torrent indexing websites.
Dark web أخطر مواقع الانترنت الخفي وأشهرها بين الهاكرز

أخطر مواقع الانترنت الخفي وأشهرها بين الهاكرز
#Dark_web
أخطر مواقع الانترنت المظلم التي يحبها الهاكرز
تكلمنا عن الويب المظلم في عدة مقالات عبر مدونة الاحتراف الجزائري ولكن سنتكلم اليوم عن مواقع توجد عبر الويب المظلم يحبها الهكرز وهي الرقم واحد بالنسبة له ، هي مواقع سرية للغاية تباع فيها أدوية طبية ممنوعة و مخدرات و أسلحة...إلخ ، و فيها يجد الهاكرز راحته وضالته .
في هذه التدوينة سوف أقدم لكم أخطر مواقع الانترنت المظلم التي يحبها الهاكرز ، لتعرف ما نوعية هذه المواقع ولتتقرب منها أكثر ، طبعا لا يمكن الشراء منهم لان ابسط شيئ ستشتريه سيكون سعره حوالي 10 بيتكوين وهذا المبلغ لن تجده عند معظم الاشخاص .
List of micro blog websites

This document contains a list of website URLs and their associated popularity ranking scores (pr) based on a scale of 1 to 7. The most popular sites are http://blip.pl and http://identi.ca which both have a pr of 7. Several other sites receive scores between 5 and 3. The majority of sites listed receive a pr of 2 or below, with many sites only receiving a score of 1.
الجانب المظلم في التاريخ المسيحي

The document contains 30 repetitions of the URL http://kotob.no-ip.org/. The URL is repeated multiple times throughout but there is no other text or context provided.
Web3 + scams = It's a match

The document discusses various scams and vulnerabilities related to cryptocurrency and web3 technologies. It begins by introducing Zoltan Balazs and his work researching vulnerabilities. It then describes several types of scams, including rug pulls, giveaway scams, advance fee fraud, and hardware wallet scams. Best practices are suggested, such as being wary of unsolicited messages, verifying sources of apps/dapps, and using strong passwords and hardware wallets to protect funds. The overall message is that web3 and cryptocurrency technologies have enabled numerous scams that have impacted many users.
Last.fm API workshop - Stockholm

Last.fm provides a public API that allows developers to access information about music and social features on Last.fm. The API includes over 100 methods to retrieve data on artists, albums, tracks, tags, users and more. It outputs data in XML or JSON formats and supports authentication for private data. Common methods include artist.getImages, album.getTags, and track.search. Developers need an API key to access the API.
Cybersecurity Asia 2021 Conference: Learning from Honeypots

APNIC Senior Security Specialist Adli Wahid presents on the APNIC Honeynet Project at the Cybersecurity Asia 2021 Conference, held online from 11 to 12 October 2021.
互联网精神

The document discusses the history and development of the Internet from the 1970s to the present. It describes some of the key events and individuals that contributed to the creation of the Internet, including the development of TCP/IP, the creation of ARPANET, the introduction of email, the invention of the World Wide Web, and the growth of popular websites and use of the Internet around the world. The document provides context around the technological advances and standards that allowed the Internet to evolve from a small network to a global communication system.
Profile Creation Sites.docx

We are making next-Gen easy to adapt and creating your network easy to operate. Therefore, you can quickly configure, troubleshoot, and secure your network while minimizing errors. Reach us for more information about our plugin services.
Internet Librarian International #ili2016 Phil's Faves

A copy of the presentation that I gave at ILI 2016 listing the things that I've found in the last year which may be of interest to people.
Http1

The document contains a list of over 200 social bookmarking and link sharing websites along with the number of votes or bookmarks each site has received. The most popular sites include Reddit, Digg, Slashdot, Delicious, Newsvine and Diigo which have received between 7-8 votes. Many other sites on the list have received between 1-6 votes, indicating varying levels of popularity and usage for sharing and discovering web links online.
Data Vault #flushyourmeds

This document lists various archives, backups, files, and links related to literary nonsense, open source software, freedom of speech, and fringe material. It was created by Scott A. Barry and contains URLs, file links, and references to flushing medications, anti-Zionism, and anti-psychiatry topics. The document serves as a data vault for this type of material.
Creating "Secure" PHP applications, Part 2, Server Hardening

The document provides guidance on server hardening techniques. It discusses using netstat to view listening services on a server and using update-rc.d or chkconfig to disable unnecessary services from starting at boot. It also recommends enabling access control lists (ACLs) in file system mounts, using SELinux or AppArmor to enforce mandatory access controls, and setting reasonable PHP memory limits to prevent potential denial of service attacks. The document stresses the importance of only allowing approved applications to execute and knowing the resource limits of the server to avoid potential outages.
Top 100 web2.0

This document contains a list of over 80 website URLs. It includes a variety of social media sites, blogging platforms, online communities and forums. Some of the sites listed are more commonly known such as WordPress, Xing and LiveJournal, while others on the list may be less familiar. The document provides a wide sampling of websites across different categories and usage types.
Robots

This document contains a robots.txt file with directives to disallow crawling of the entire site ("/") by over 200 bot user agents to prevent unwanted indexing and scraping of website content. The file should be uploaded to the root folder to block these bots from accessing the site.
Similar to Trkr (20)
Dark web أخطر مواقع الانترنت الخفي وأشهرها بين الهاكرز

Dark web أخطر مواقع الانترنت الخفي وأشهرها بين الهاكرز
Cybersecurity Asia 2021 Conference: Learning from Honeypots

Cybersecurity Asia 2021 Conference: Learning from Honeypots
Internet Librarian International #ili2016 Phil's Faves

Internet Librarian International #ili2016 Phil's Faves
Creating "Secure" PHP applications, Part 2, Server Hardening

Creating "Secure" PHP applications, Part 2, Server Hardening
