Report
Share
Recommended
La reina de la nit i joan miró

Una sencilla presentación de algunas obras de Miró, relacionadas con música de La Reina de la Noche de la ópera de Mozart, La Flauta Mágica.
Recommended
La reina de la nit i joan miró

Una sencilla presentación de algunas obras de Miró, relacionadas con música de La Reina de la Noche de la ópera de Mozart, La Flauta Mágica.
Lights off love on...

This document promotes an unhealthy pursuit of perfection through extreme weight loss and control over eating, suggesting that readers can achieve their dreams of being perfect by keeping calm, stopping eating, and enjoying the process. It acknowledges that this lifestyle will never be enough but claims that the feeling of being skinny is better than any food.
china

The document summarizes a trip to China, including a 24-hour flight, staying in a hotel with a pool on the 3rd floor, visiting an Olympic village and stadium where the author ran 400 meters, learning about silk at the Silk Market, seeing temples used to worship Buddha that emperors would vacation at, and seeing parts of the Great Wall that were destroyed.
How amazon works

Amazon employs various technologies to securely process online orders and payments. Its massive data warehouse contains over 15 terabytes of customer data and handles millions of daily operations for both Amazon's direct sales and sales through third-party sellers. In addition to selling goods directly from its own warehouses, Amazon allows other large retailers to use its platform for online sales fulfillment. Through marketing partnerships, product recommendations, and community websites, Amazon aims to be the most customer-centric online retailer.
Week12

Encryption works by using keys to scramble data before transmitting it, then using the same key to unscramble it upon receipt. There are two main types: symmetric key encryption which uses the same key by both parties, and public key encryption which uses different keys but relates them through hashing. Public key encryption addressed weaknesses in symmetric key encryption by allowing secure communication without pre-sharing a key. Hashing algorithms are used to generate hash values from data in public key encryption in a way that makes deriving the original data nearly impossible without the hash value.
More Related Content
Viewers also liked
Lights off love on...

This document promotes an unhealthy pursuit of perfection through extreme weight loss and control over eating, suggesting that readers can achieve their dreams of being perfect by keeping calm, stopping eating, and enjoying the process. It acknowledges that this lifestyle will never be enough but claims that the feeling of being skinny is better than any food.
china

The document summarizes a trip to China, including a 24-hour flight, staying in a hotel with a pool on the 3rd floor, visiting an Olympic village and stadium where the author ran 400 meters, learning about silk at the Silk Market, seeing temples used to worship Buddha that emperors would vacation at, and seeing parts of the Great Wall that were destroyed.
How amazon works

Amazon employs various technologies to securely process online orders and payments. Its massive data warehouse contains over 15 terabytes of customer data and handles millions of daily operations for both Amazon's direct sales and sales through third-party sellers. In addition to selling goods directly from its own warehouses, Amazon allows other large retailers to use its platform for online sales fulfillment. Through marketing partnerships, product recommendations, and community websites, Amazon aims to be the most customer-centric online retailer.
Week12

Encryption works by using keys to scramble data before transmitting it, then using the same key to unscramble it upon receipt. There are two main types: symmetric key encryption which uses the same key by both parties, and public key encryption which uses different keys but relates them through hashing. Public key encryption addressed weaknesses in symmetric key encryption by allowing secure communication without pre-sharing a key. Hashing algorithms are used to generate hash values from data in public key encryption in a way that makes deriving the original data nearly impossible without the hash value.
Viewers also liked (8)
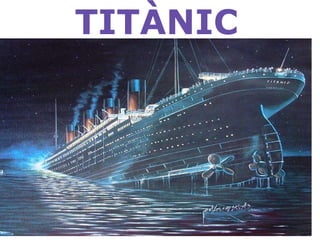
Titanic
- 1. TITÀNIC
- 2. VÍCTOR Titànic tracta sobre un vaixell que se'n va cap a estats units i es on hi havia gent molt rica. I a mig camí es xoca contra un iceberg
- 3. VÍCTOR I així es com va quedar després de que es xocar.
- 4. IONA Leonardo DiCaprio, protagonista de la pel·lícula Titànic. Nescut l'11 de noviembre de 1974, a Los Àngeles, California.
- 5. IONA Kate Winslet, protagonista de la pel·lícula Titànic. Necuda el 5 d'octubre de 1975, Englaterra.
- 6. NAHUM El titanic era un vaixell molt luxós.
- 7. NAHUM Però només contaven amb luxe, no amb els riscos que comporten aquelles aigües congelades.
- 8. AINA Va provocar la destrucció i enfonsament del vaixell i la mort de més de 1.515 persones
- 9. AINA La pel·lícula va guanyar onze oscars