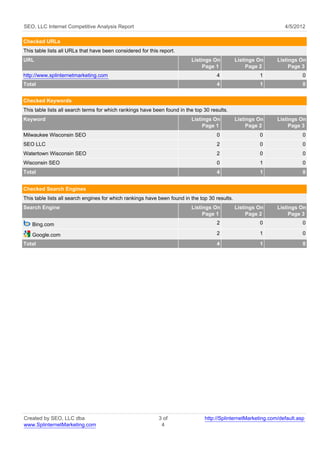
This document is an SEO competitive analysis report from SEO, LLC dated April 5, 2012. It analyzes the search engine rankings for 4 keywords and 1 URL on Google and Bing. The analysis found 1 listing in the #1 position, 2 in the top 5 positions, 4 in the top 10 positions, and 5 in the top 20 positions. It provides details on the rankings found for the analyzed keywords and URLs on each search engine.