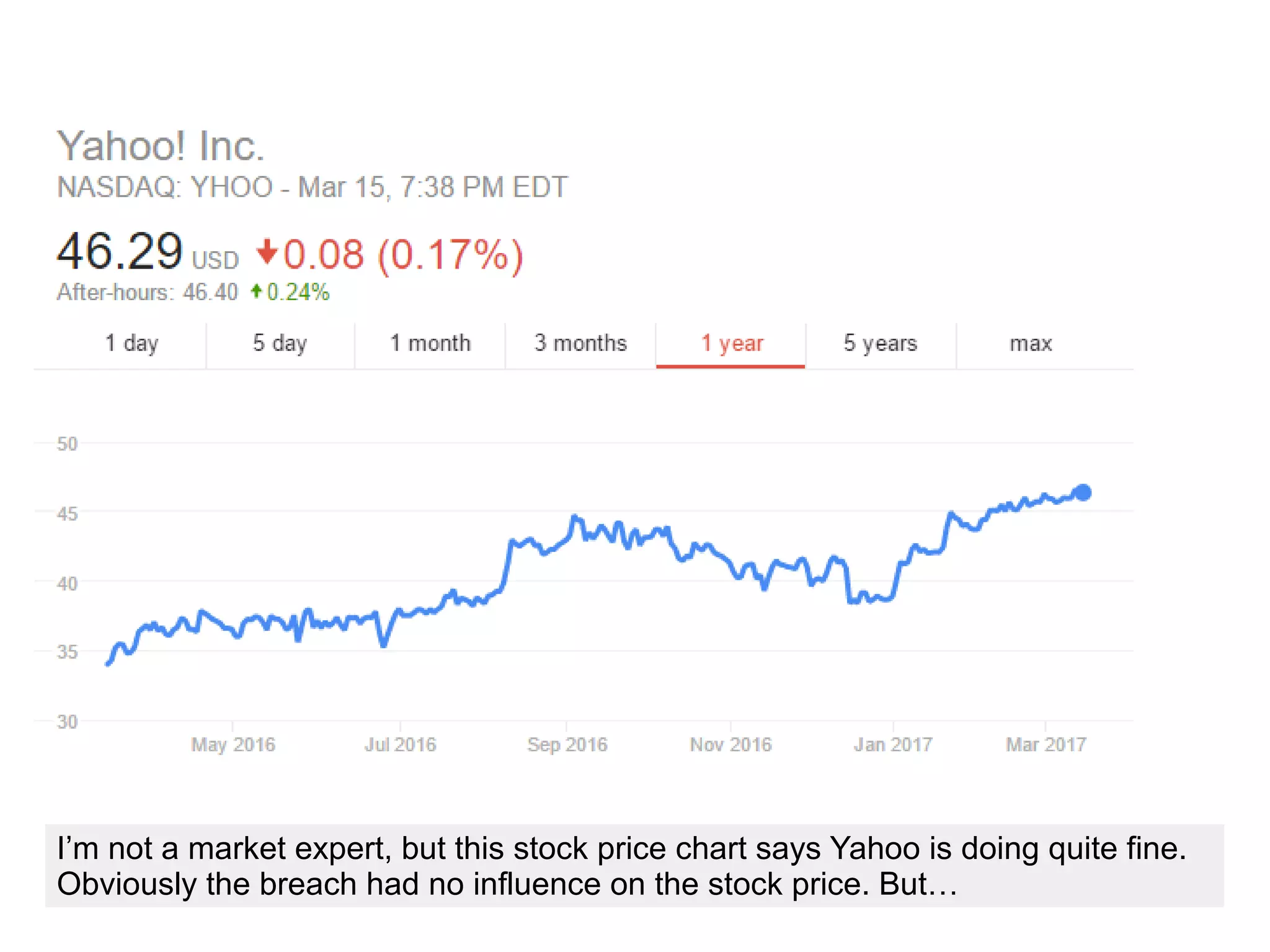
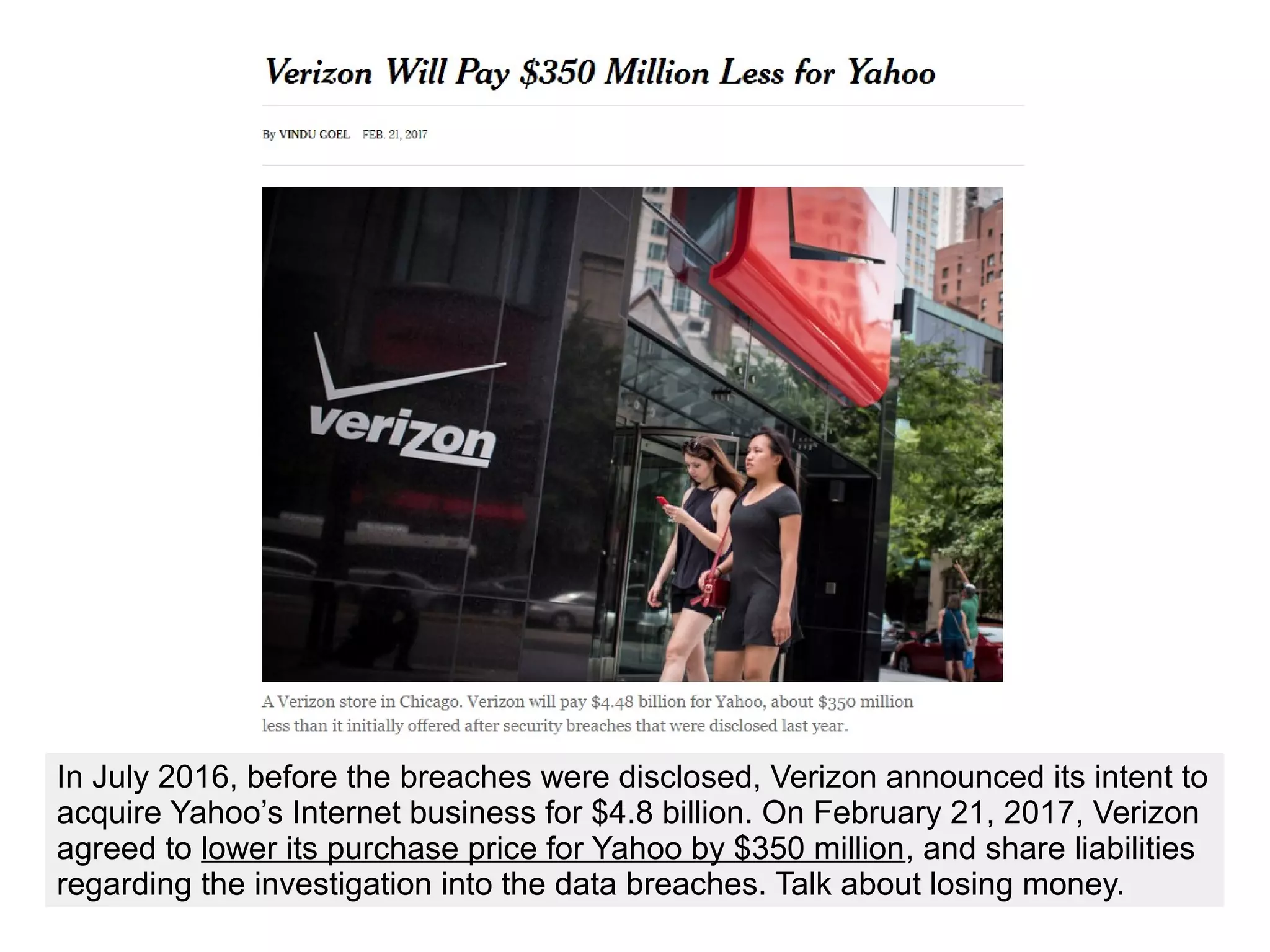
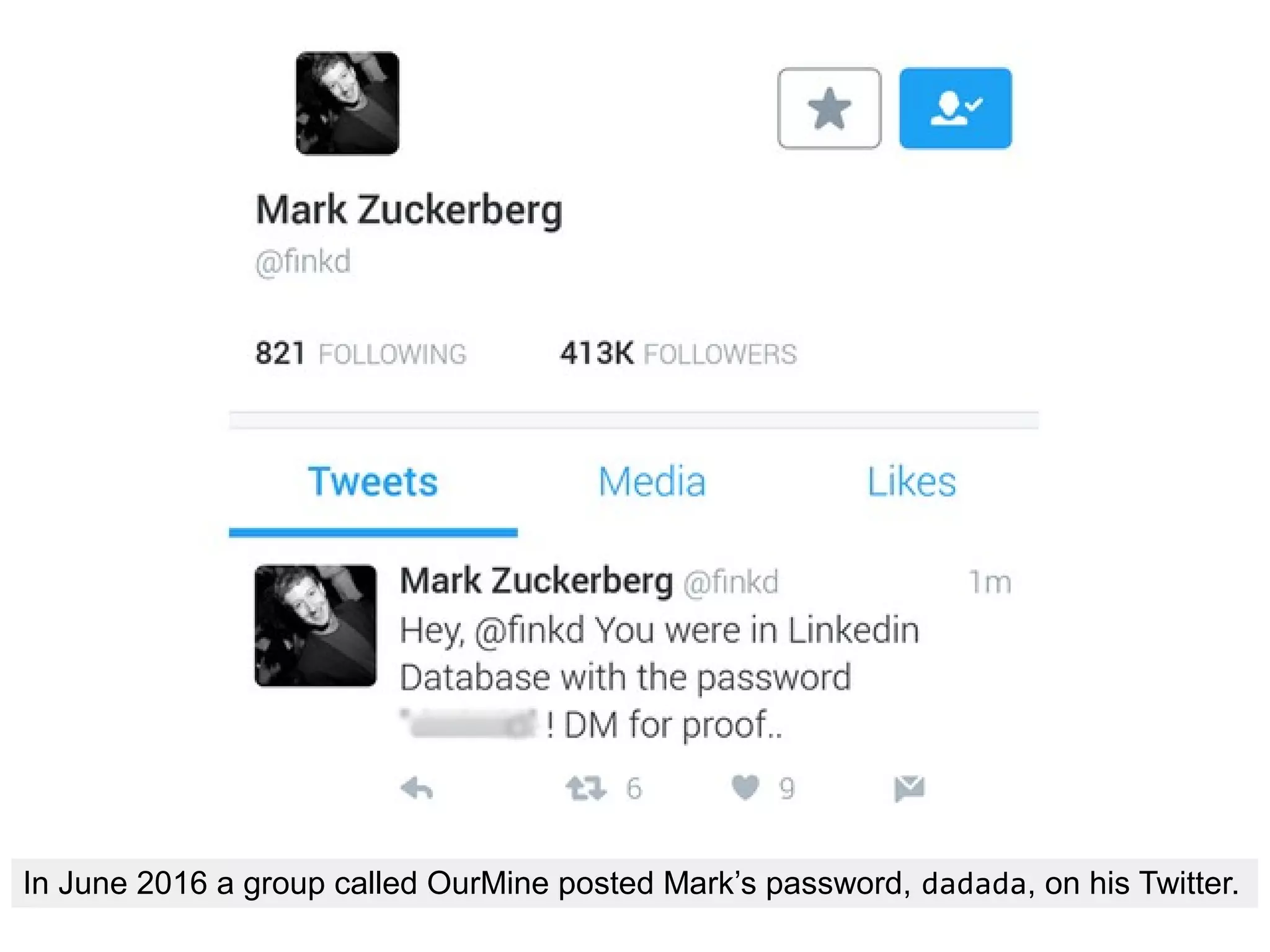
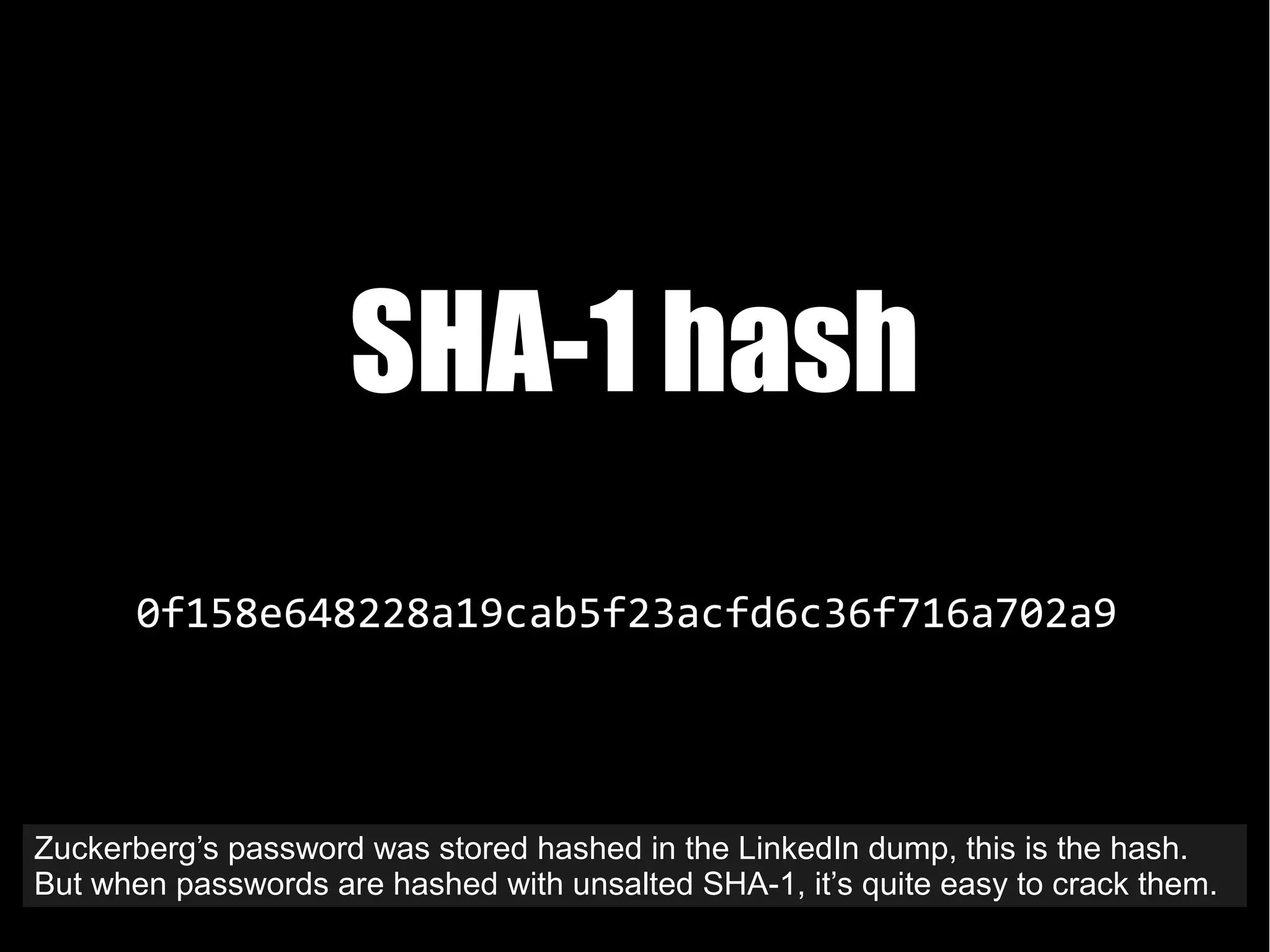
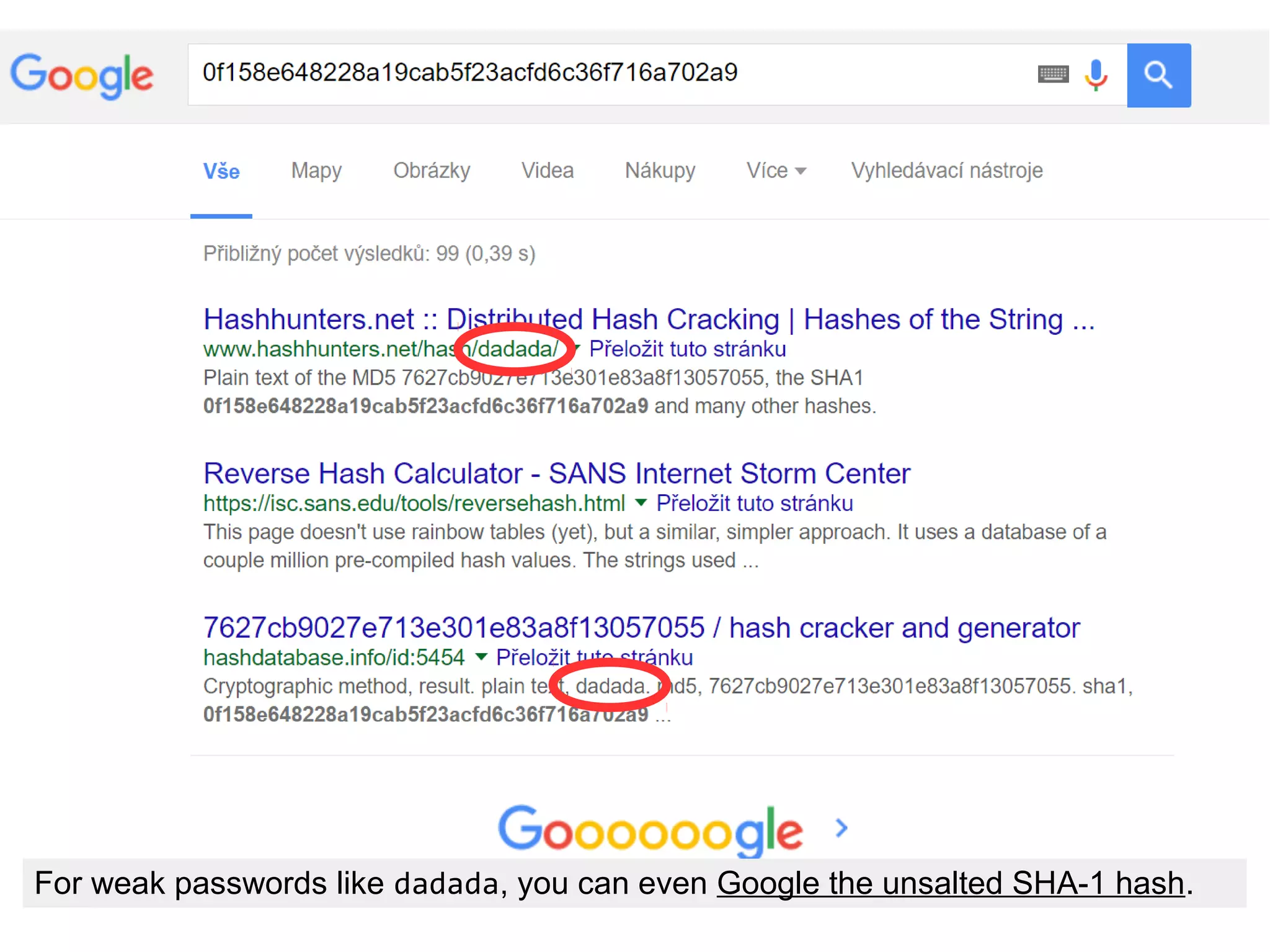
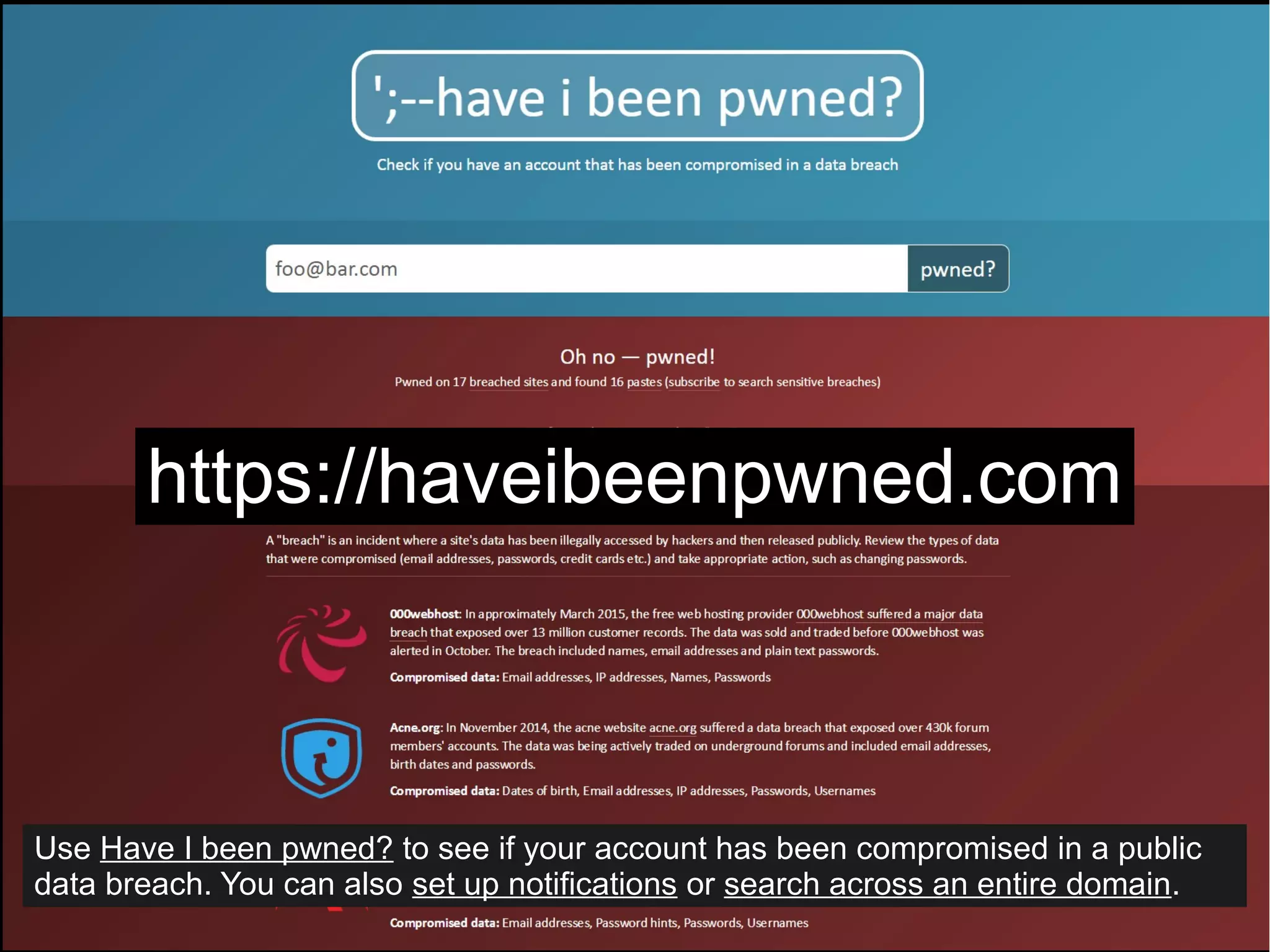
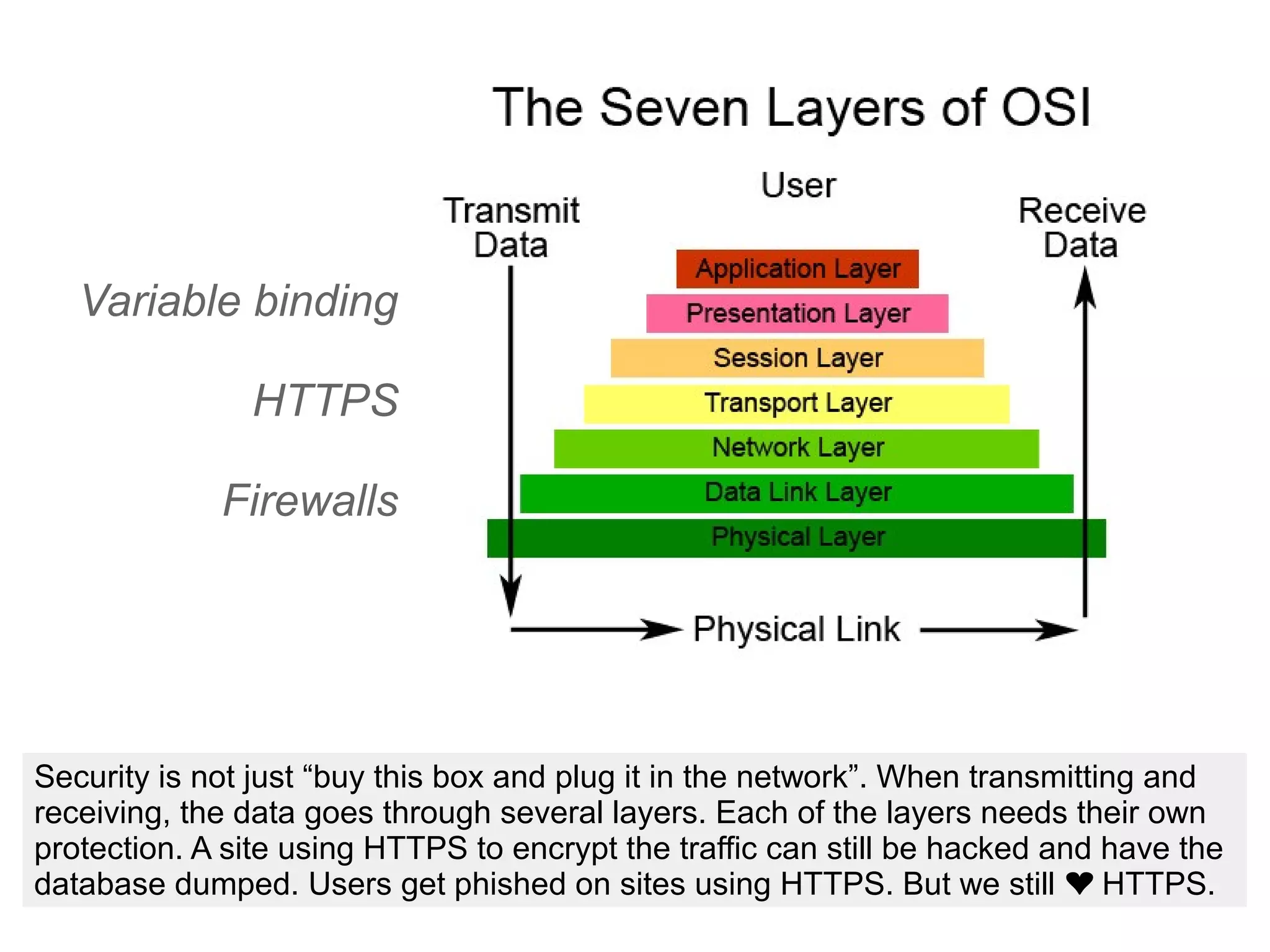
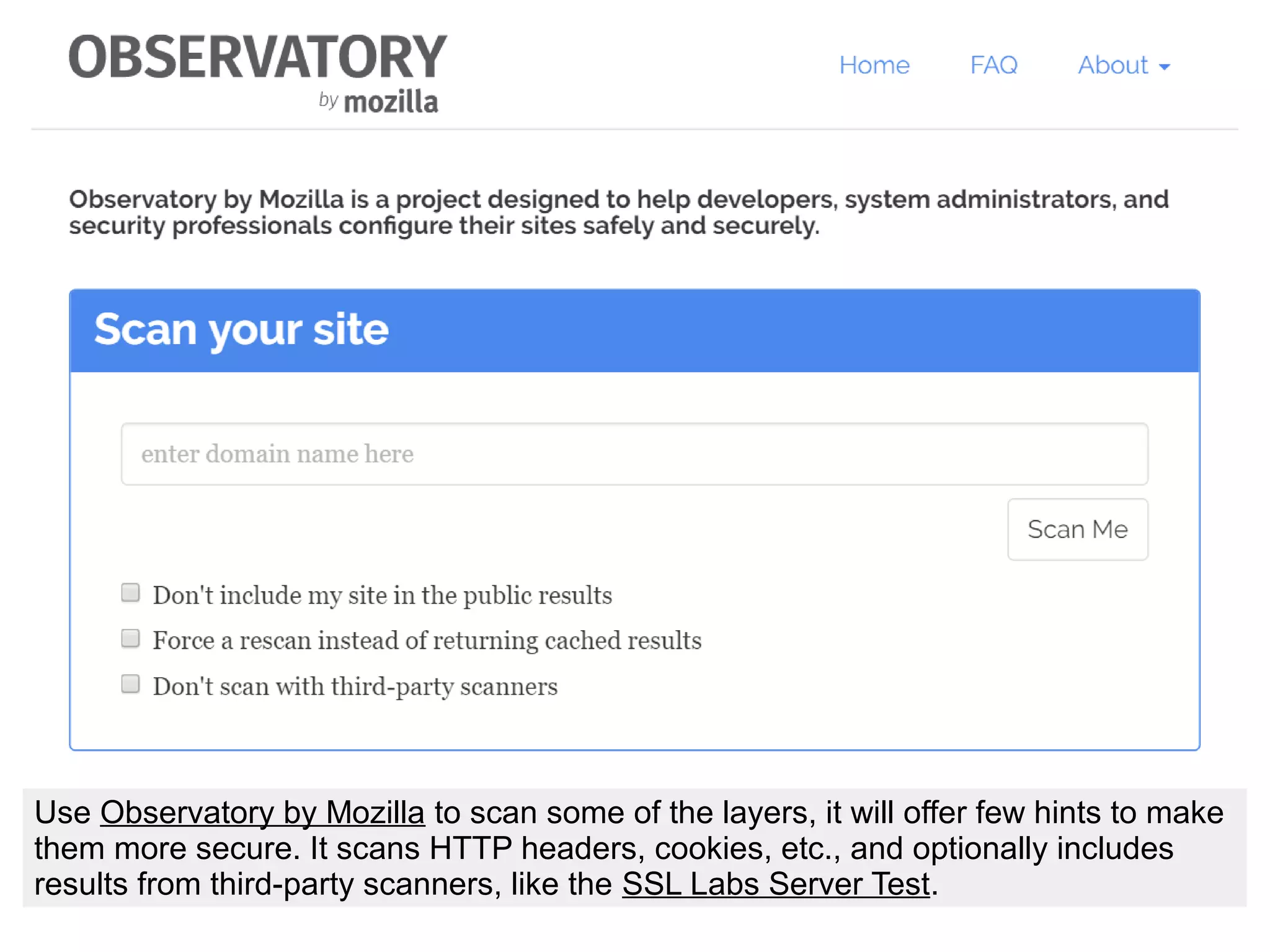
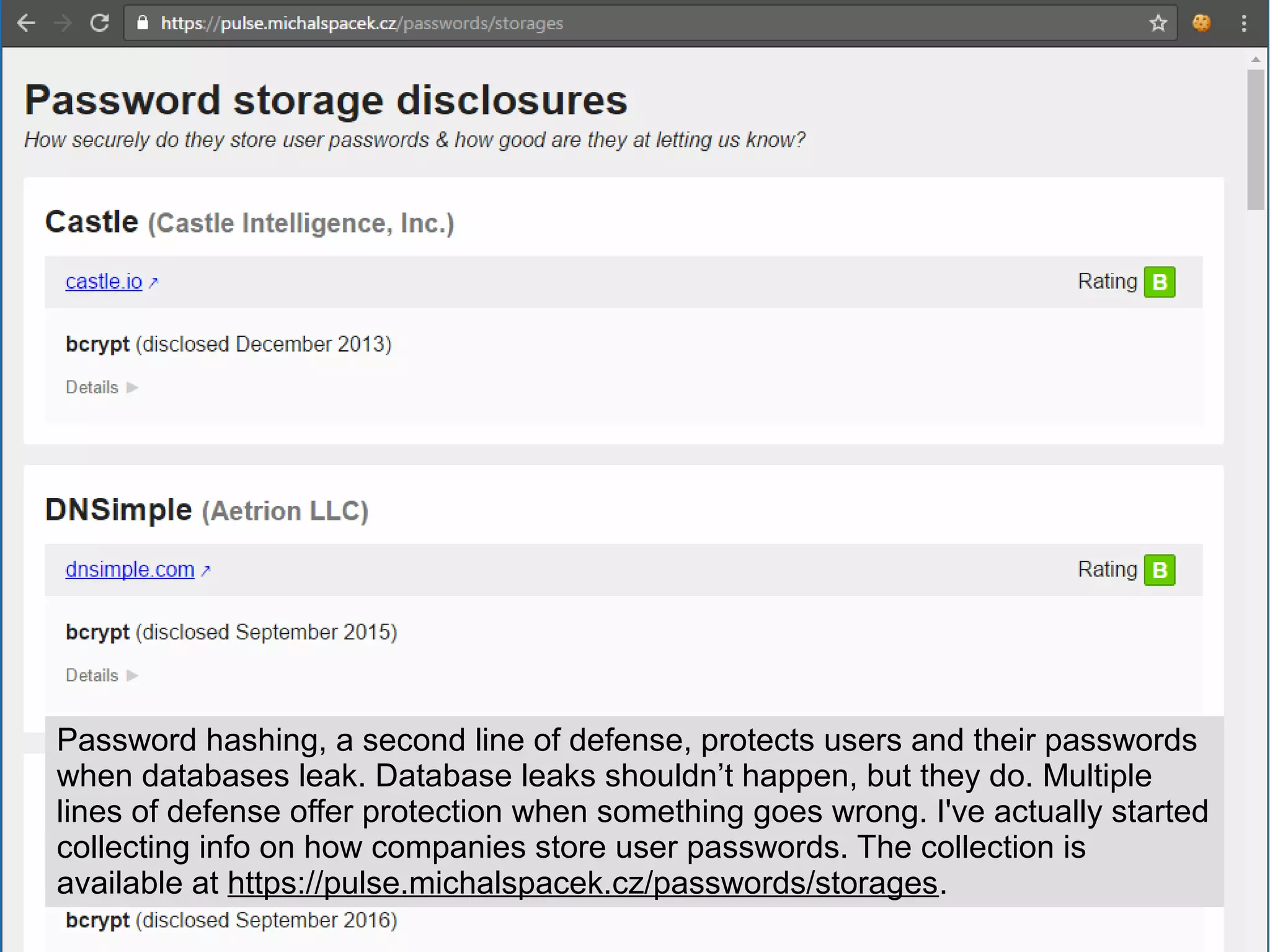
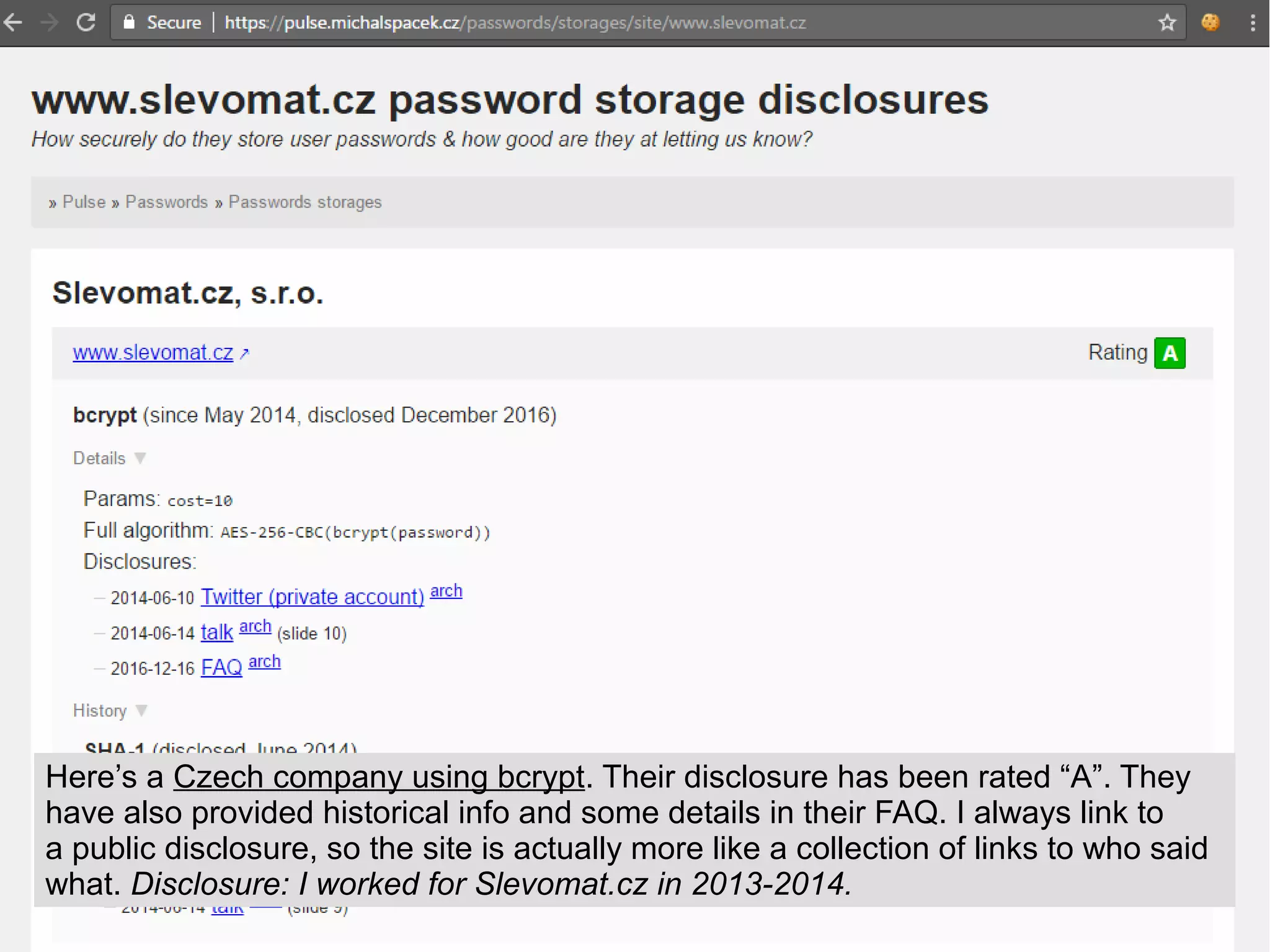
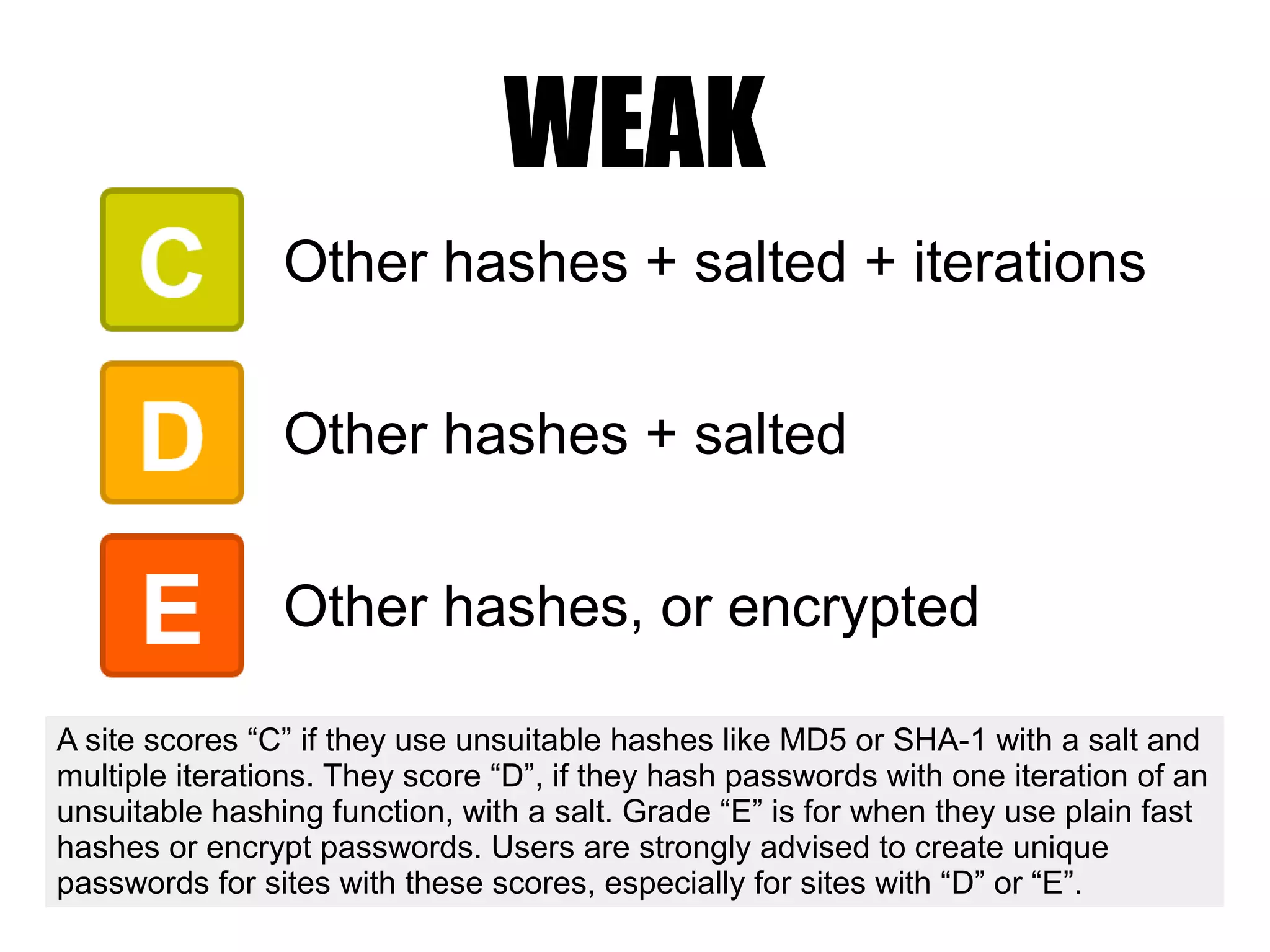
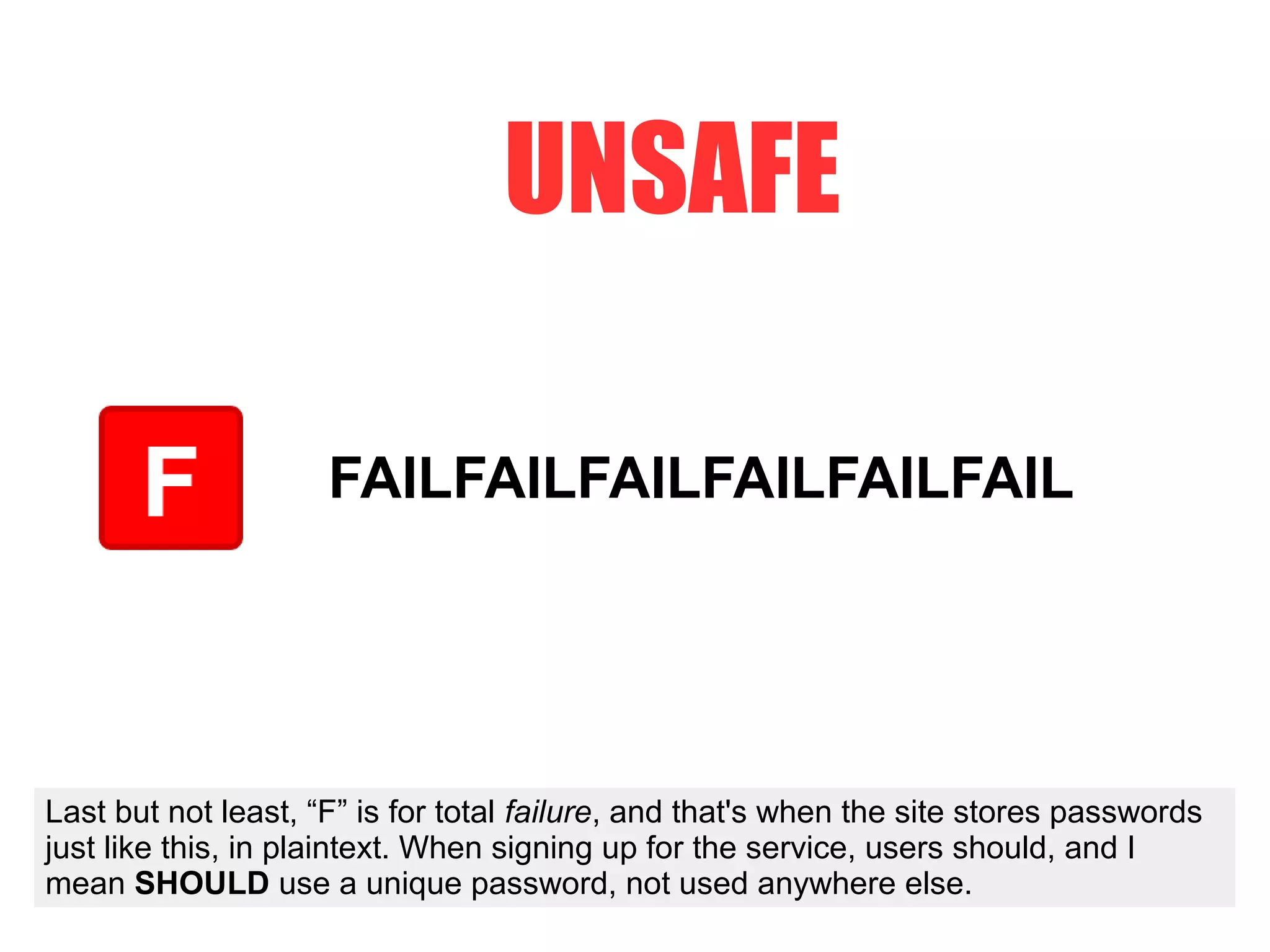
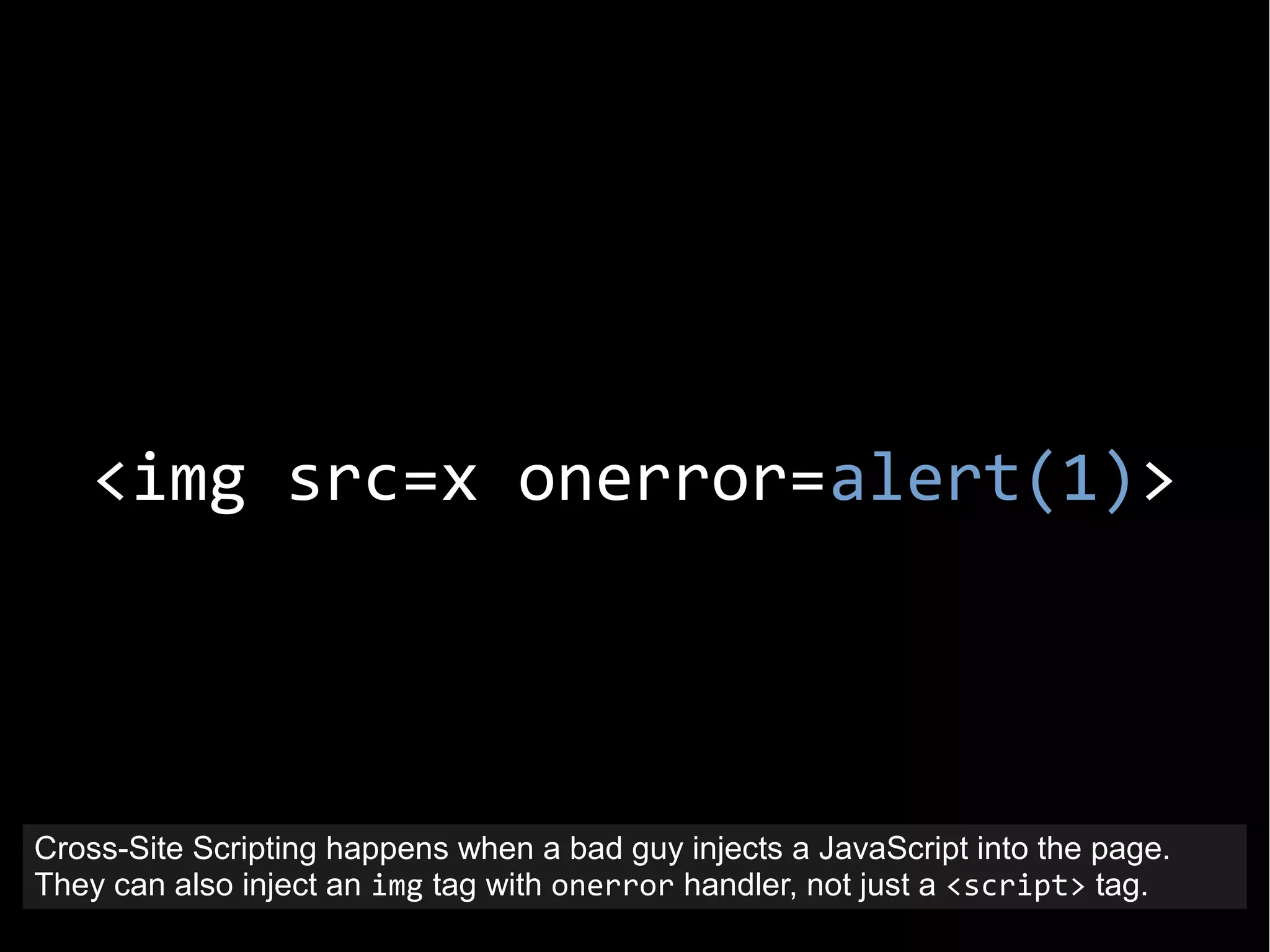
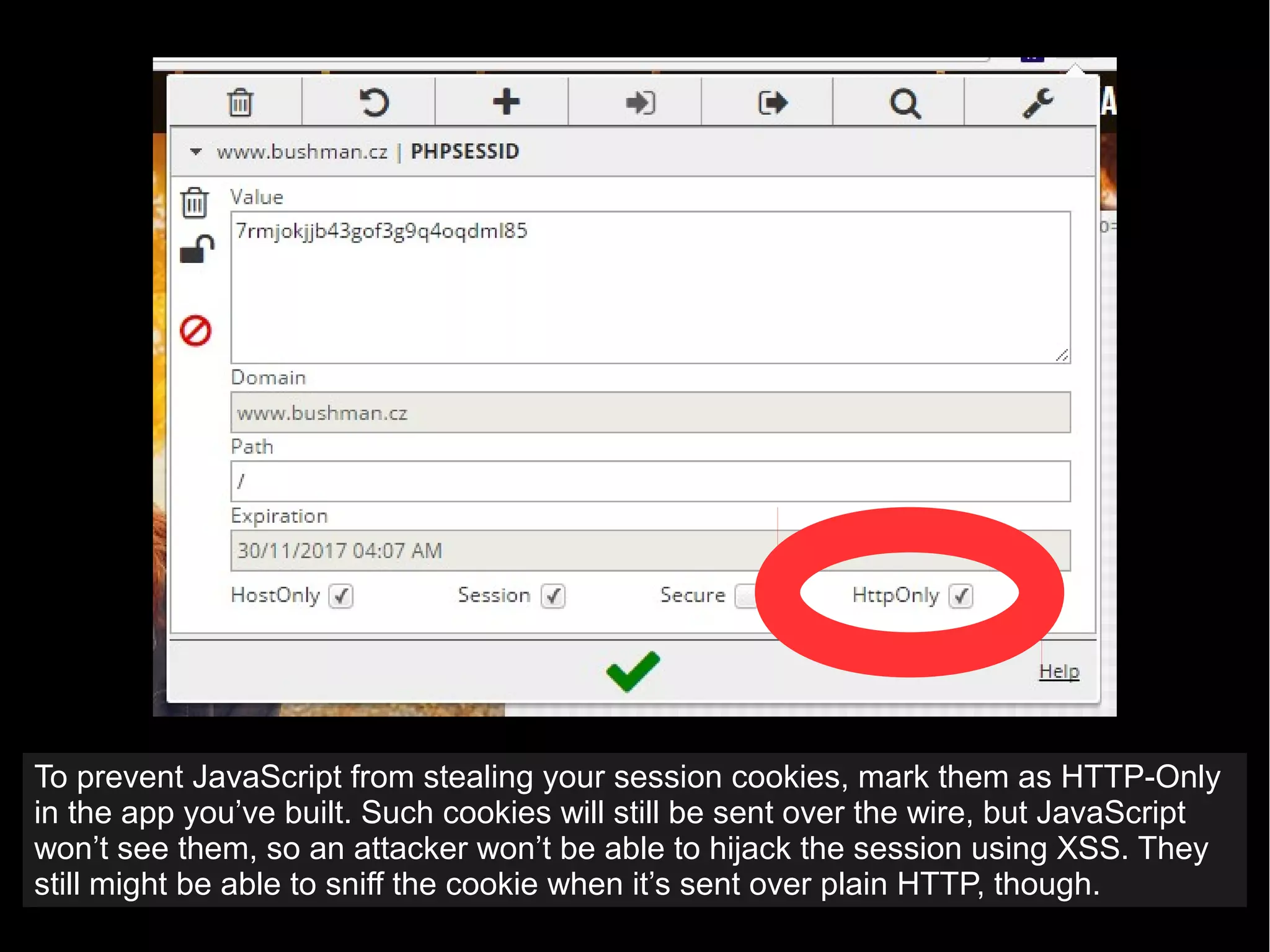
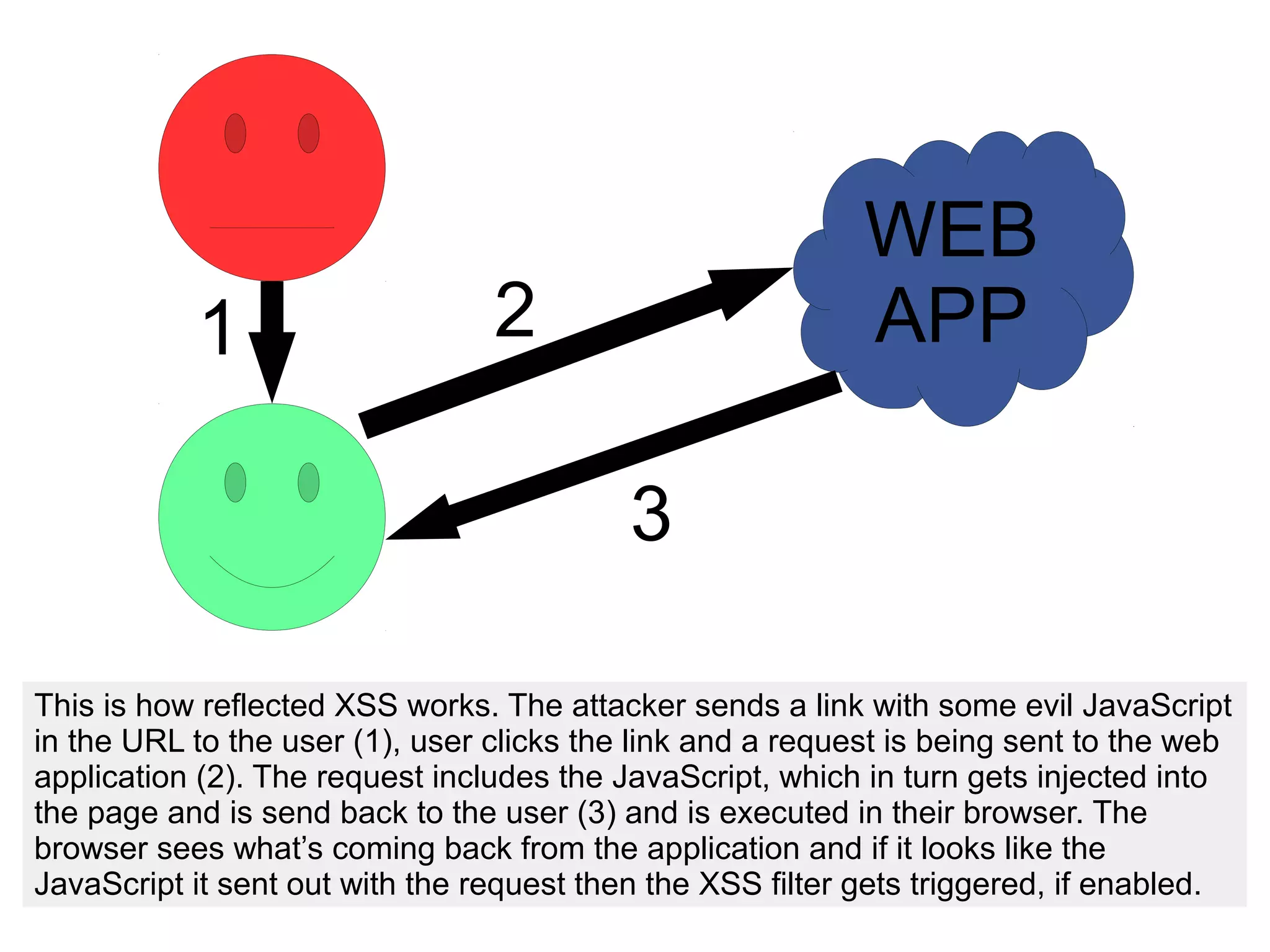
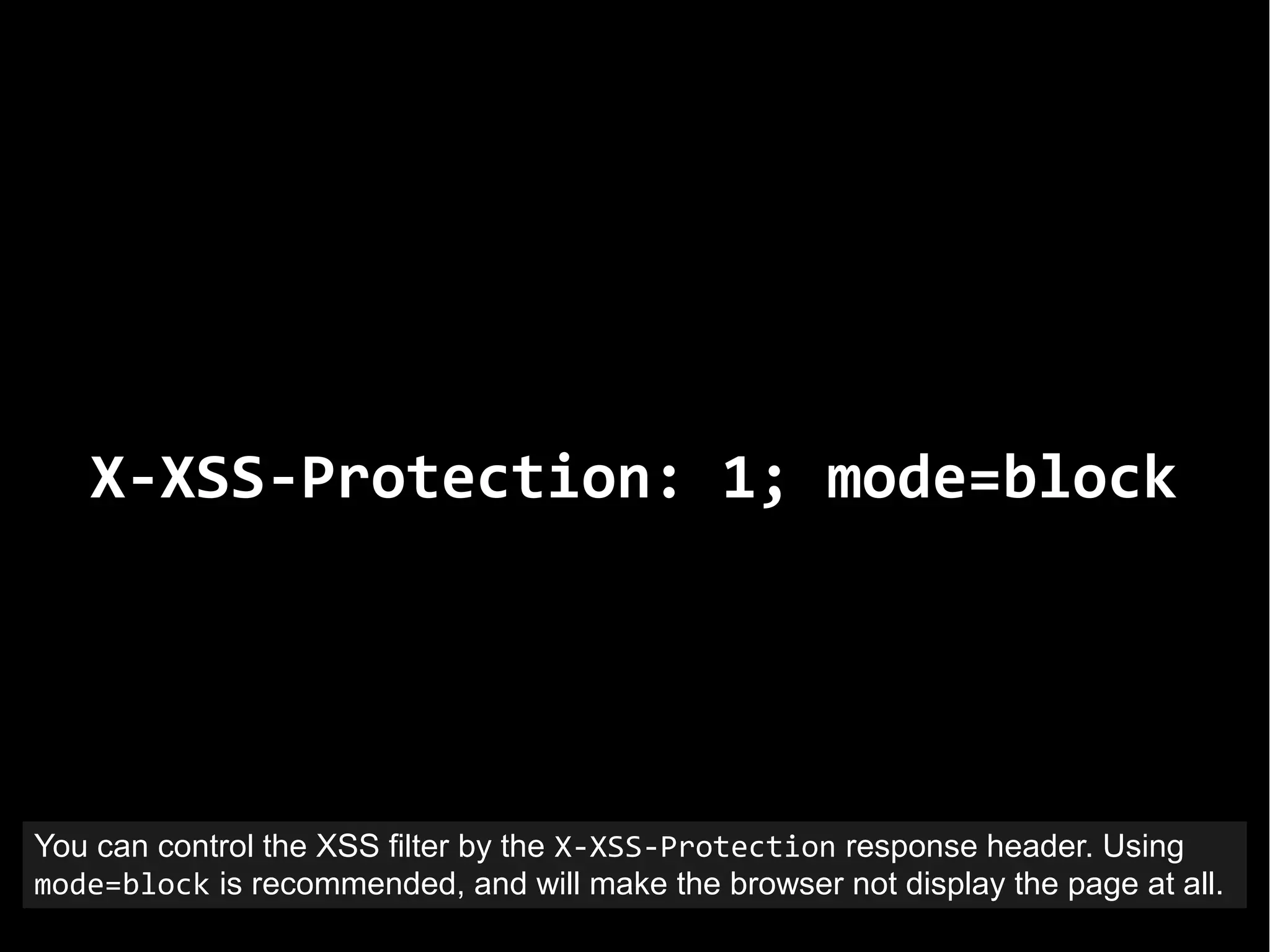
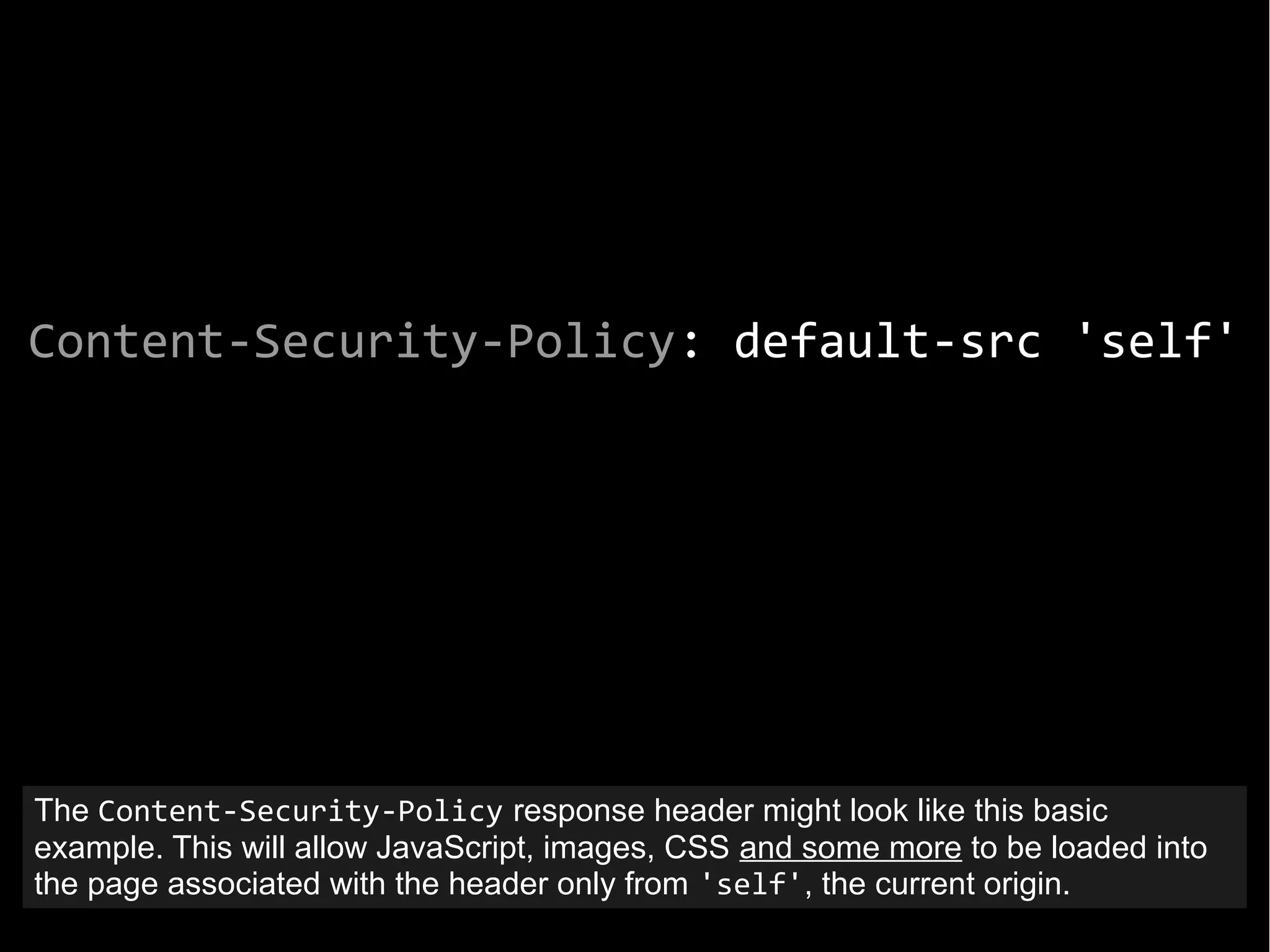
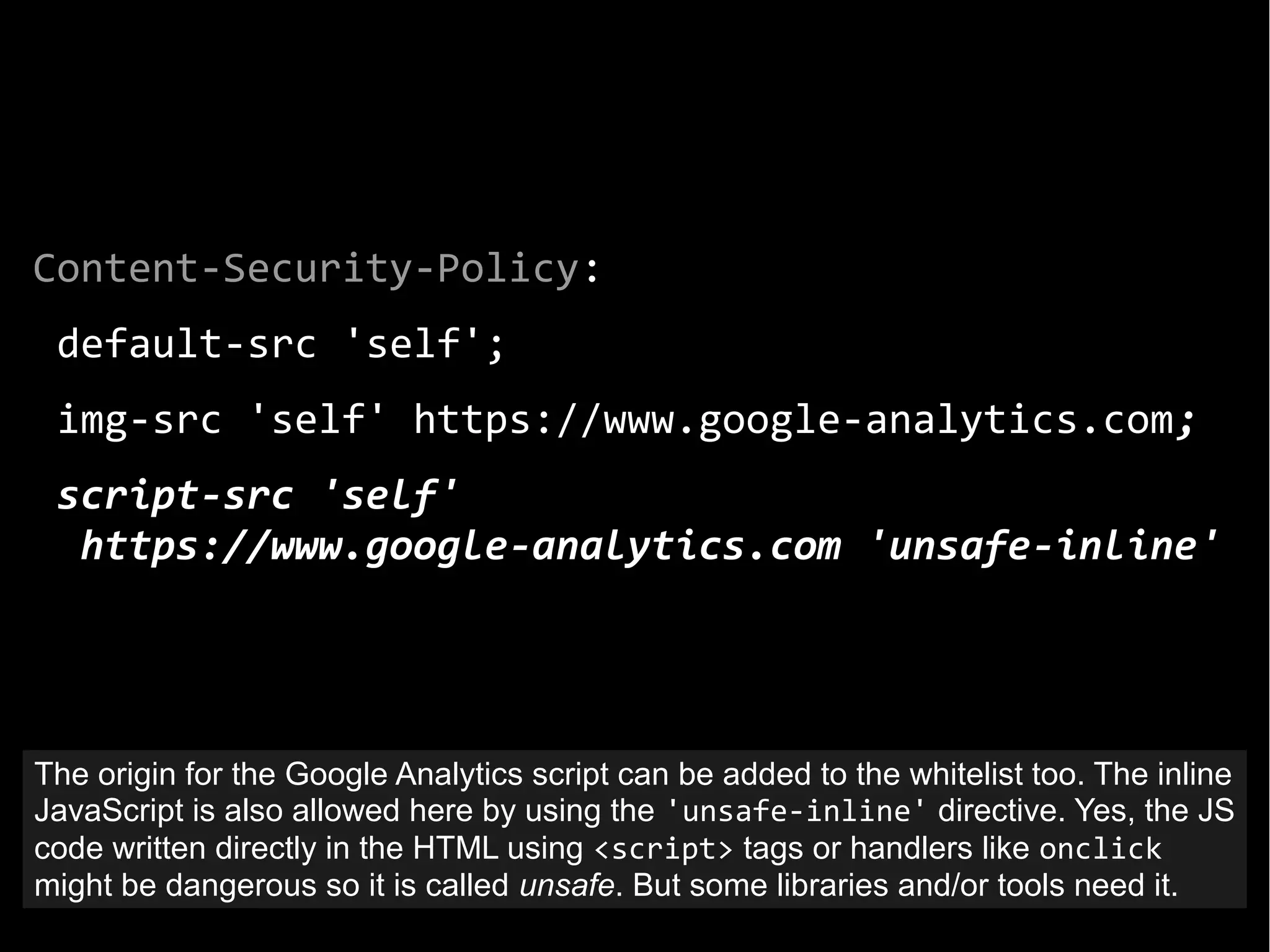
The document discusses the importance of quality of life in web application security and the implementation of multiple lines of defense against cyber threats. It provides examples of major data breaches and the consequences of poor security practices, emphasizing the need for strong password management and various defense mechanisms, such as cross-site scripting protections. Recommendations include using unique passwords, employing secure hashing techniques, and utilizing advanced security features like content security policy to mitigate vulnerabilities.