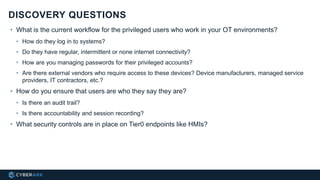
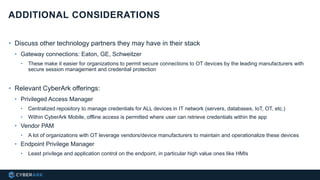
This document provides an overview of an OT solution from CyberArk. It begins by defining operational technology (OT) and explaining that OT systems like PLCs, HMIs and SCADA software are increasingly connected and targeted by attackers due to weak security. It then outlines CyberArk's solution to secure OT environments, including using its Privileged Access Manager to discover and manage privileged accounts, its remote access and mobile capabilities for offline access, and Endpoint Privilege Manager for application control on endpoints. The document concludes by suggesting sales questions about the customer's current OT security practices and credentials management.