This document provides an introduction to Linux, including:
- What Linux is and where it came from, as an open source operating system created by Linus Torvalds in 1991.
- How to get Linux through downloading a distribution like Red Hat and the packages it includes.
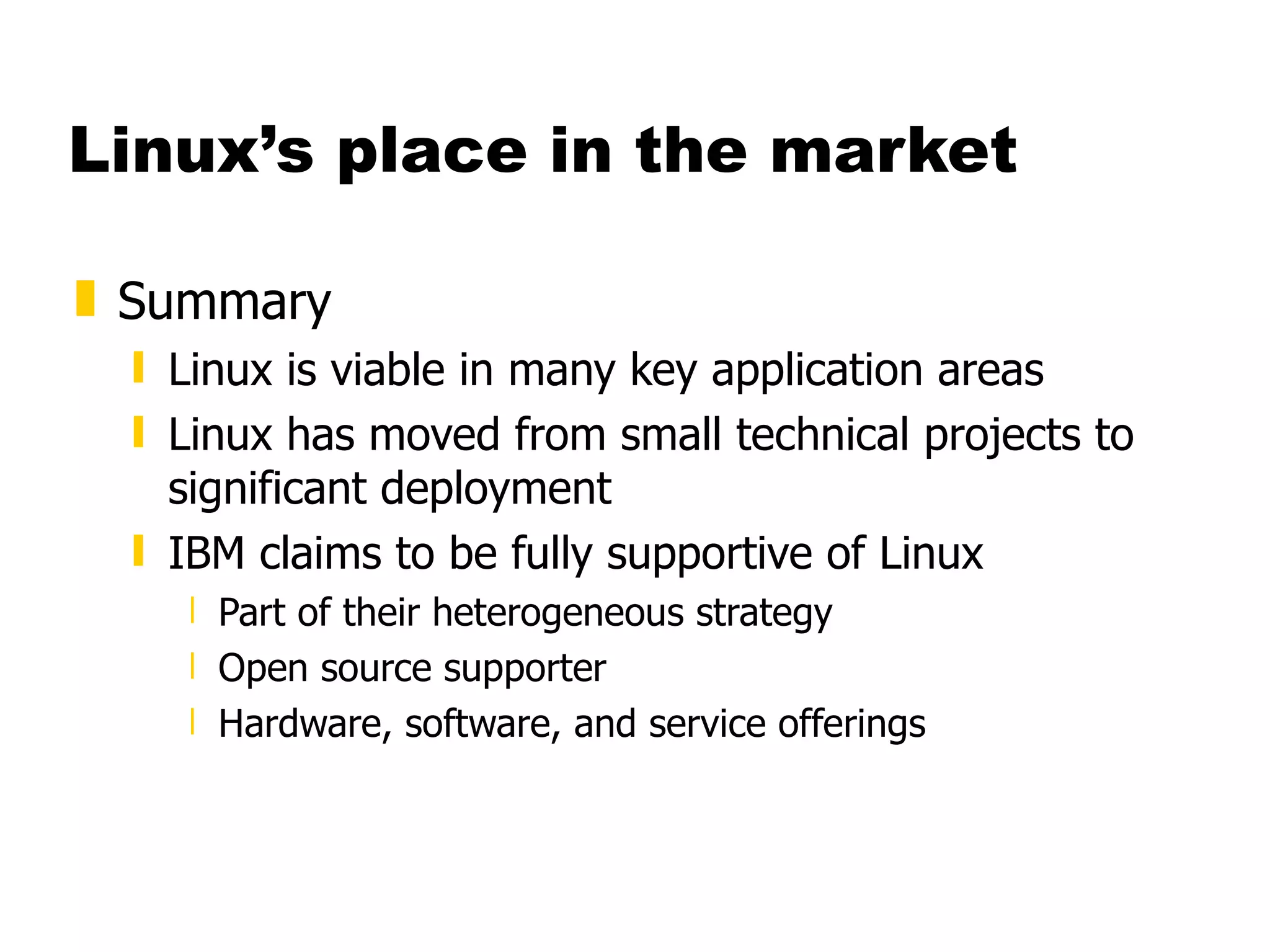
- Why Linux has become significant due to its growing popularity, ability to run on multiple hardware platforms, and being free.
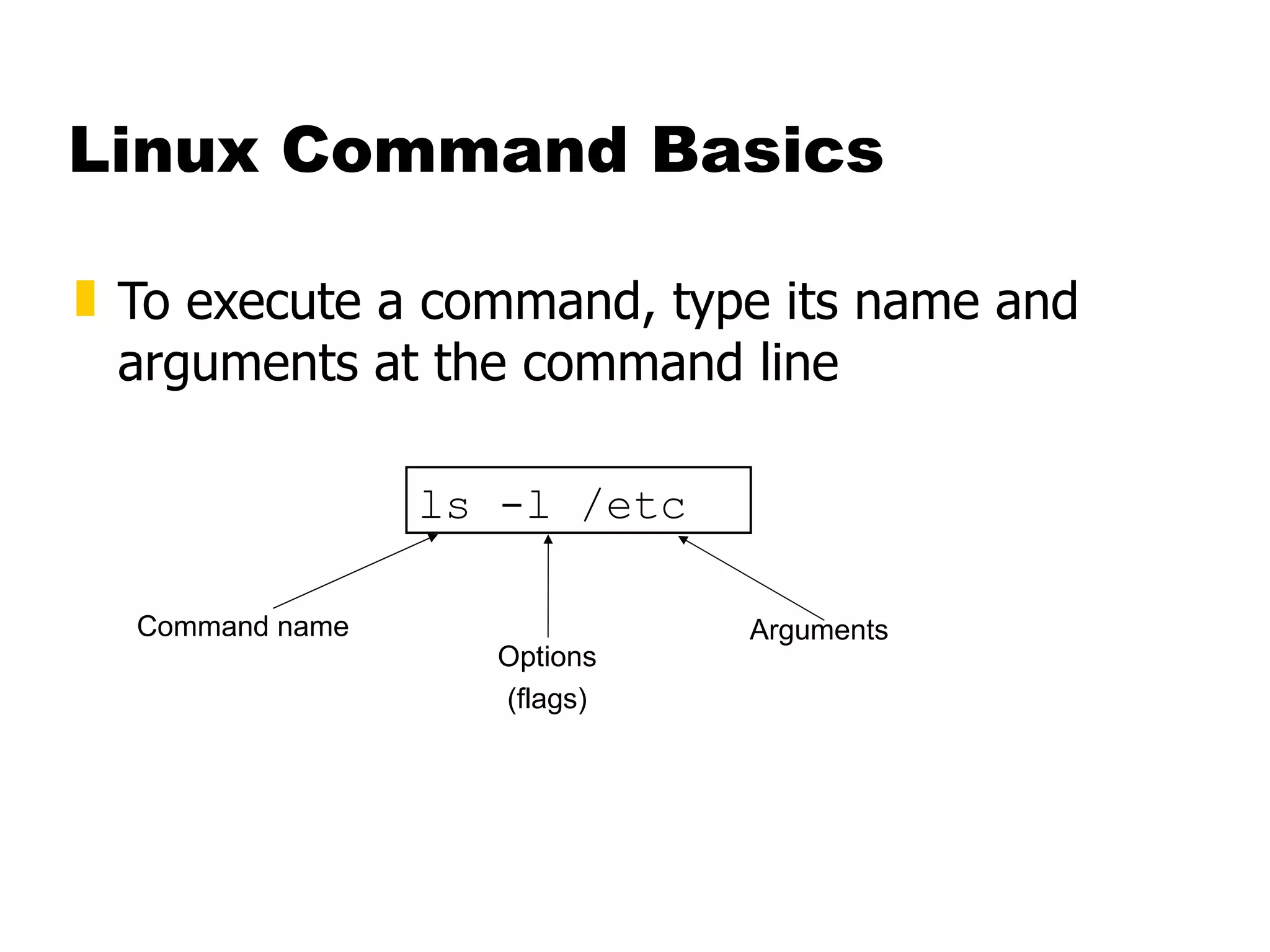
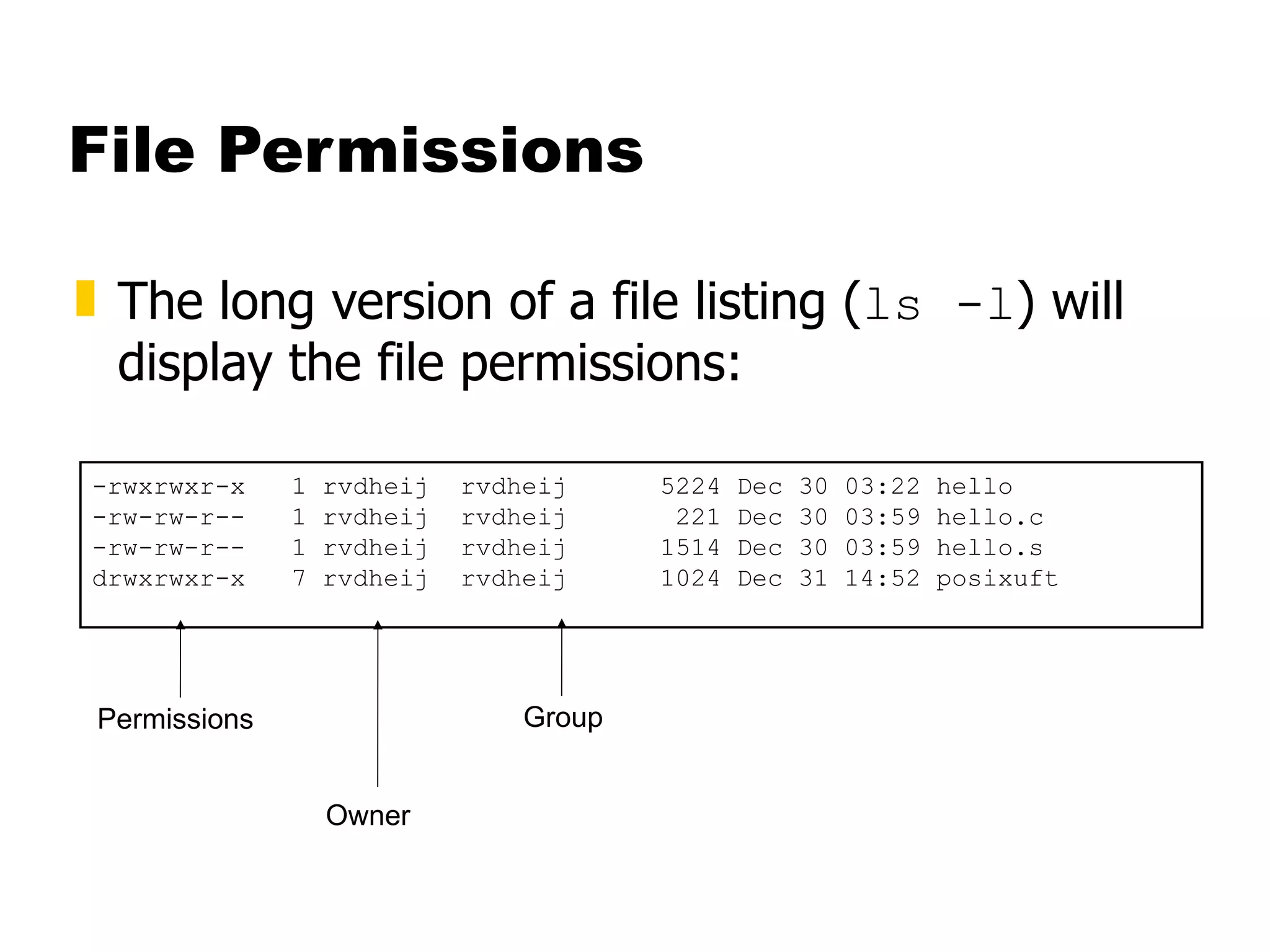
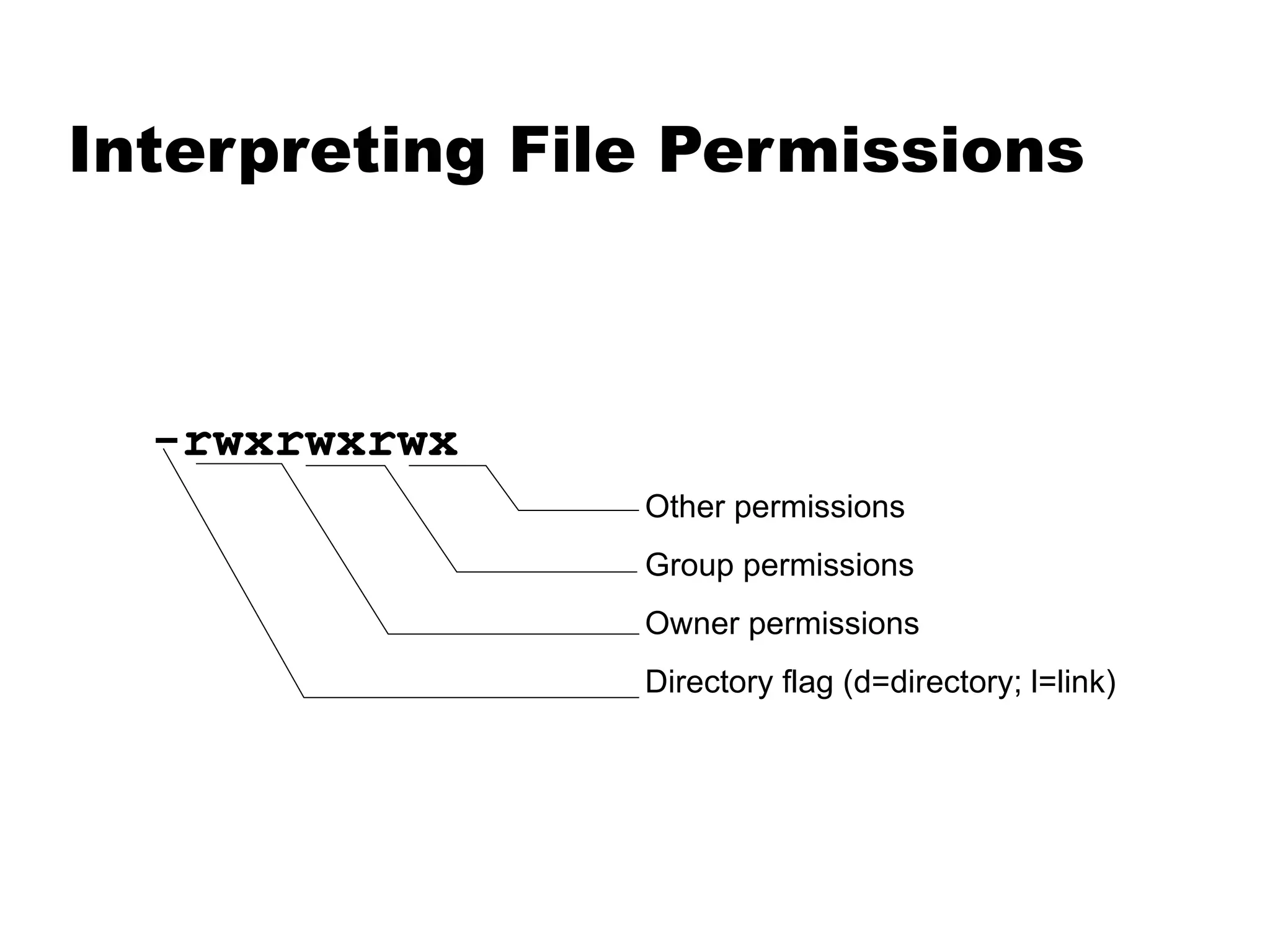
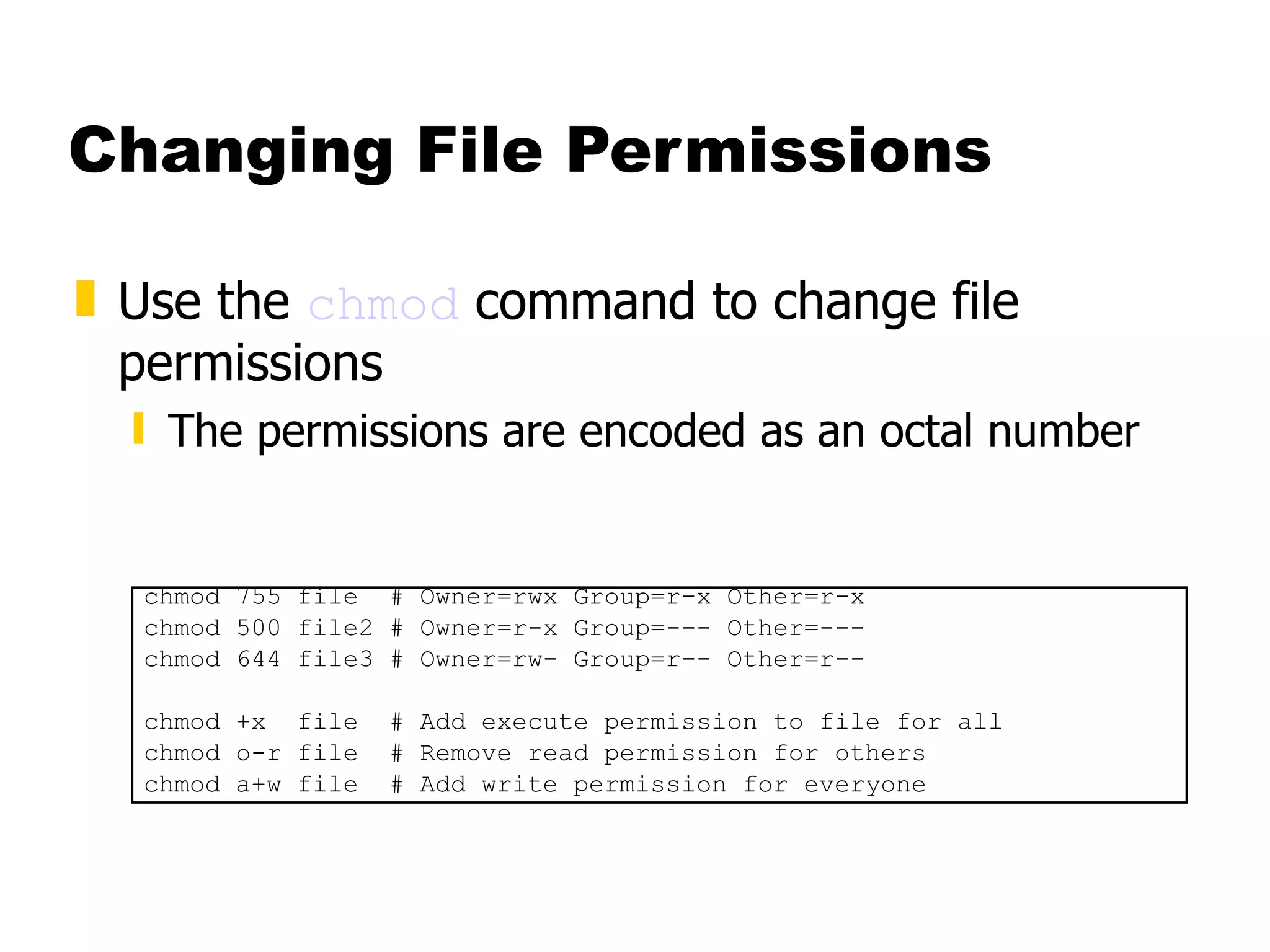
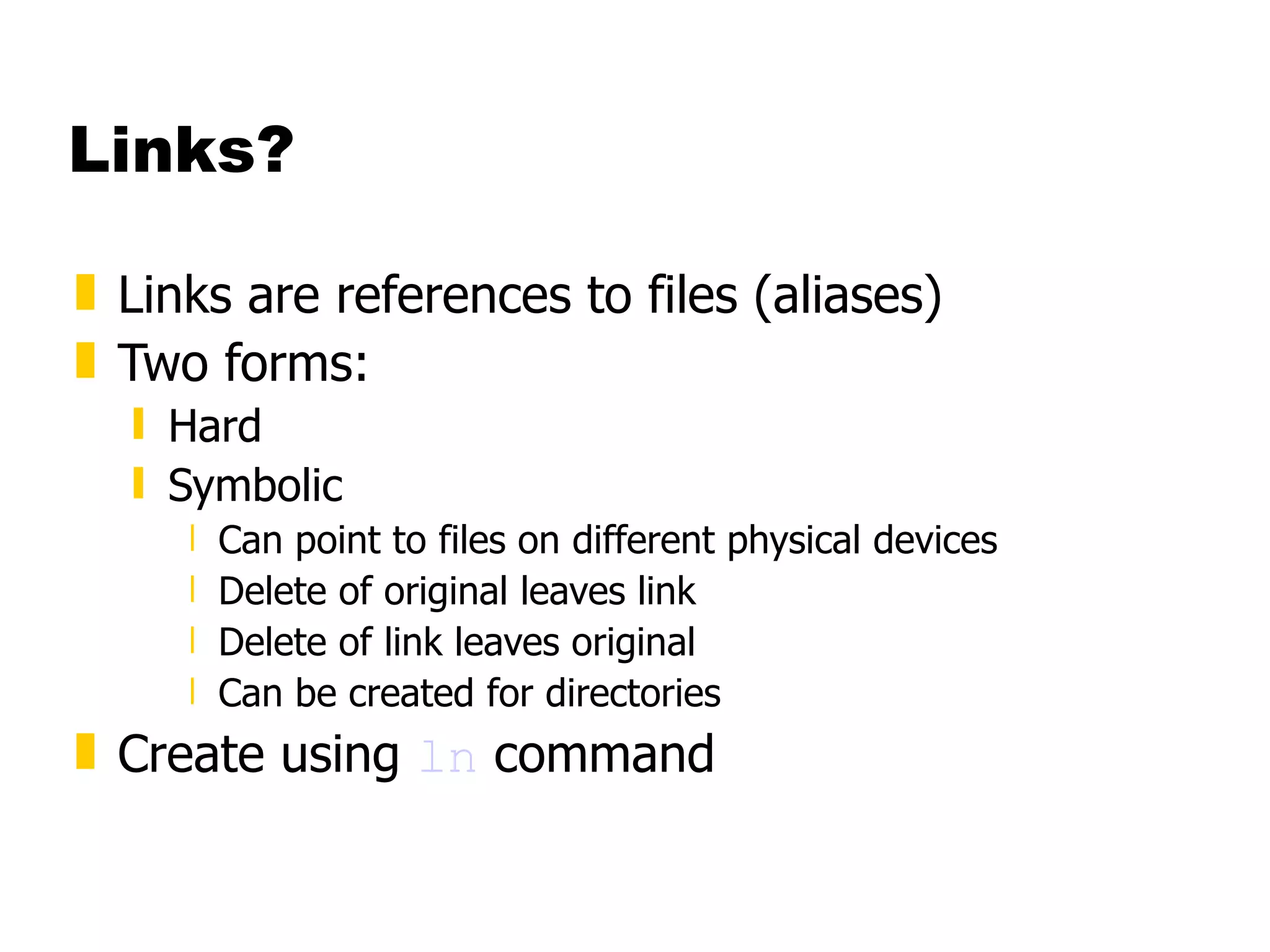
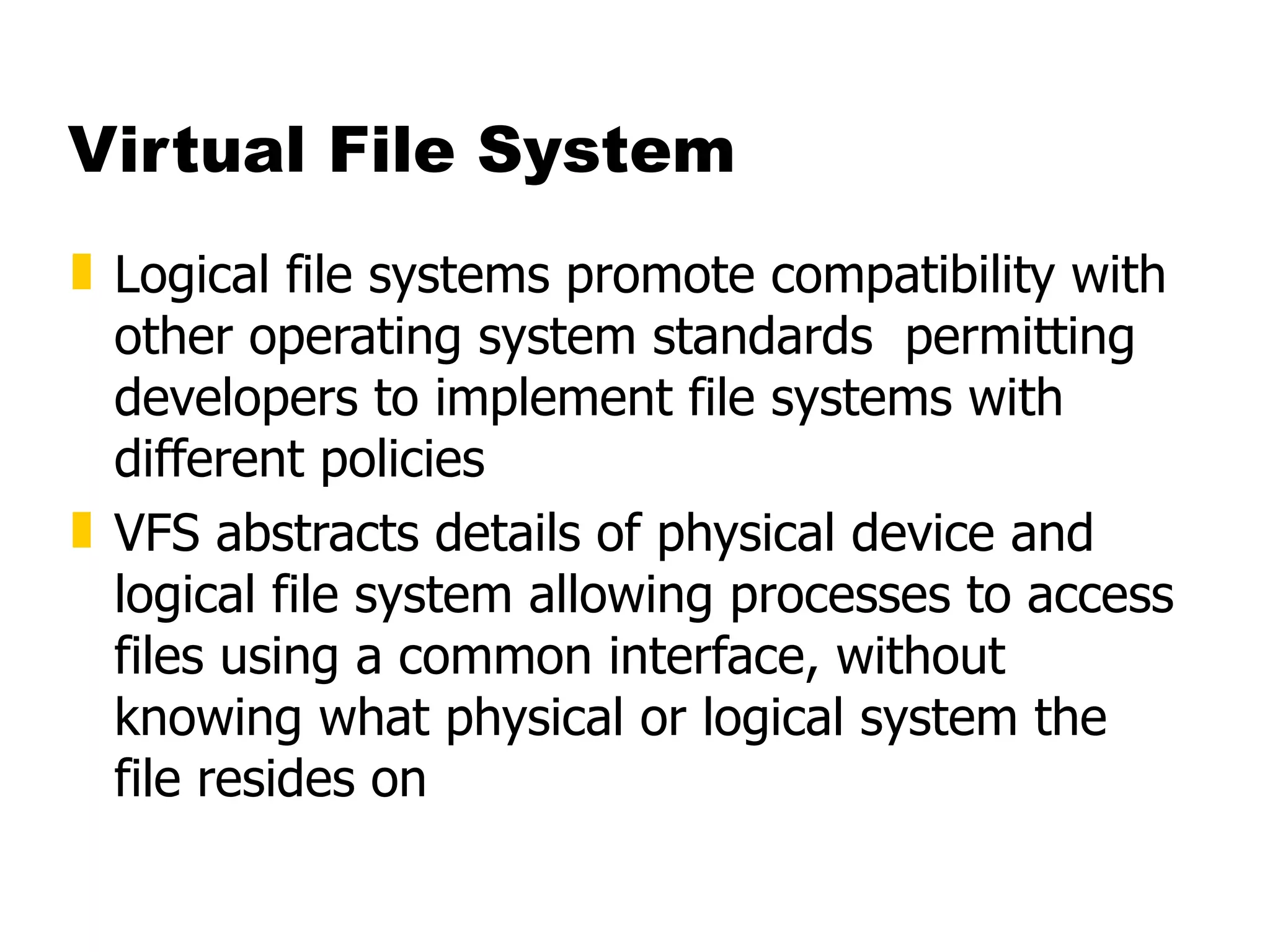
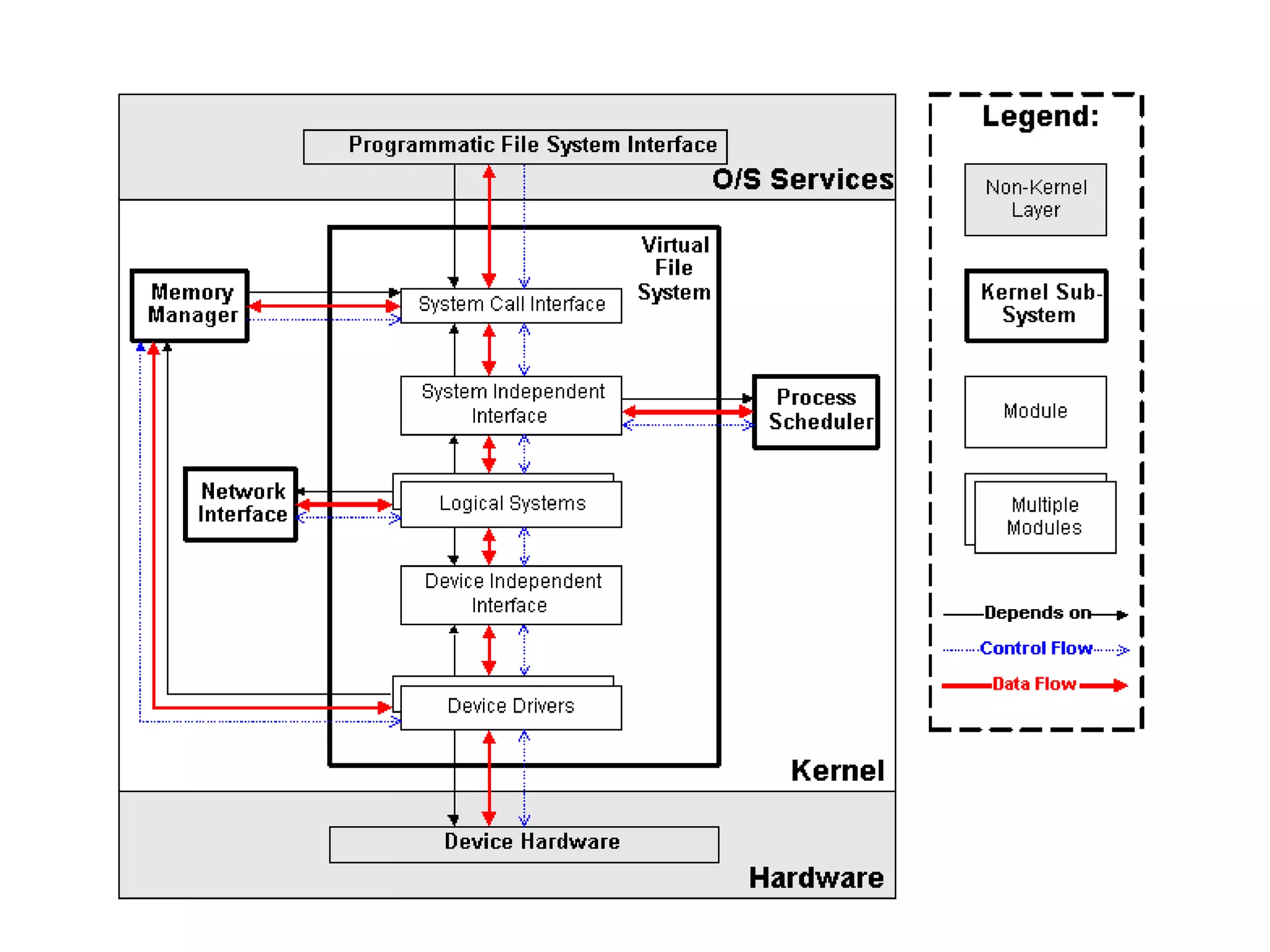
- An overview of Linux commands and utilities for file management, processes, users and permissions.

![Logging In Before you can use it you must login by specifying your account and password: Linux 2.2.13 (penguinvm.princeton.edu) (ttyp1) penguinvm login: neale Password: Last login: Tue Jan 4 10:13:13 from linuxtcp.princeton.edu [neale@penguinvm neale]$](https://image.slidesharecdn.com/linux-100530234528-phpapp02/75/Linux-10-2048.jpg)
![Creating a new user Use the useradd command Use the passwd command to set password Try it… logon as r oot [root@penguinvm]# useradd scully [root@penguinvm]# passwd scully Changing password for user scully New UNIX password: Retype new UNIX password: passwd: all authentication tokens updated successfully [root@penguinvm]#](https://image.slidesharecdn.com/linux-100530234528-phpapp02/75/Linux-12-2048.jpg)
![Using the new user Now logoff using the exit command login as the new user Linux 2.2.13 (penguinvm.princeton.edu) (ttyp2) penguinvm login: scully Password: [scully@penguinvm scully]$](https://image.slidesharecdn.com/linux-100530234528-phpapp02/75/Linux-17-2048.jpg)
![More Commands kill - sends a signal to a process or process group You can only kill your own processes unless you are root UID PID PPID C STIME TTY TIME CMD root 6715 6692 2 14:34 ttyp0 00:00:00 sleep 10h root 6716 6692 0 14:34 ttyp0 00:00:00 ps -ef [root@penguinvm log]# kill 6715 [1]+ Terminated sleep 10h](https://image.slidesharecdn.com/linux-100530234528-phpapp02/75/Linux-38-2048.jpg)
![Processes Daemons Background processes for system administration are referred to as “daemons” These processes are usually started during the boot process The processes are not assigned any terminals UID PID PPID C STIME TTY TIME CMD root 5 1 0 1999 ? 00:00:14 [kswapd] bin 254 1 0 1999 ? 00:00:00 [portmap] root 307 1 0 1999 ? 00:00:23 syslogd -m 0 root 350 1 0 1999 ? 00:00:34 httpd](https://image.slidesharecdn.com/linux-100530234528-phpapp02/75/Linux-72-2048.jpg)
![Processes [root@penguinvm log]# sleep 10h & [1] 6718 [root@penguinvm log]# ps -ef UID PID PPID C STIME TTY TIME CMD root 6718 6692 0 14:49 ttyp0 00:00:00 sleep 10h & causes process to be run in “background” Job Number Process ID (ID) Parent Process ID](https://image.slidesharecdn.com/linux-100530234528-phpapp02/75/Linux-73-2048.jpg)