LG_App_Parent_Receipt
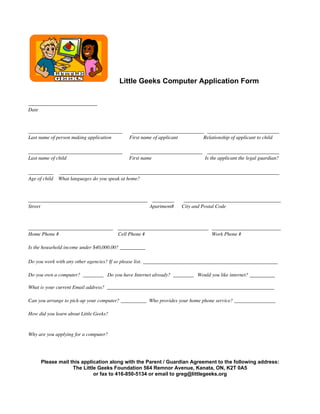
- 1. Little Geeks Computer Application Form ______________________ Date ______________________________ _______________________ _______________________ Last name of person making application First name of applicant Relationship of applicant to child ______________________________ _______________________ _______________________ Last name of child First name Is the applicant the legal guardian? ________ ______________________________________________________________________ Age of child What languages do you speak at home? ______________________________________ _______ _______________________________ Street Apartment# City and Postal Code ___________________________ _____________________________ ______________________ Home Phone # Cell Phone # Work Phone # Is the household income under $40,000.00? __________ Do you work with any other agencies? If so please list. ___________________________________________ Do you own a computer? ________ Do you have Internet already? ________ Would you like internet? ________ What is your current Email address? _________________________________________________________________ Can you arrange to pick-up your computer? __________ Who provides your home phone service? ________________ How did you learn about Little Geeks? Why are you applying for a computer? Please mail this application along with the Parent / Guardian Agreement to the following address: The Little Geeks Foundation 564 Remnor Avenue, Kanata, ON, K2T 0A5 or fax to 416-850-5134 or email to greg@littlegeeks.org
- 2. The Little Geeks Parent / Guardian Agreement I, _____________________________________________________, parent or legal guardian of (please print) ____________________________________________________________, agree to participate, (please print) along with the recipient in an internet awareness course prior to receiving a computer from the Little Geeks Foundation. I agree that this computer will be used exclusively for the benefit of my child’s education and that I am responsible for the supervision of both computer and Internet usage. The provided computer comes pre-loaded with an operating system and the Microsoft Office suite of tools. The recipient may also be provided with a free internet connection provided by Little Geeks subject to availability. The computer is intended primarily as an educational tool in support of school studies. The parent or legal guardian acknowledges that the downloading and installation of any software obtained via the Internet will render the service terms of this contract null and void. This fact should be shared with the child. For example, the installation of peer-to-peer file sharing software is unacceptable. It’s unacceptable because file-sharing software is a primary source of computer viruses. Little Geeks agrees to repair for a period of 1-year original software or hardware related problems. All Little Geeks computers leave the shop in good working order, virus-free and operating at an acceptable speed. Little Geeks may reclaim computers should there be an abuse of privledges. The parent or guardian understands that it is impossible for the Little Geeks Foundation to restrict access to all controversial materials, and as a consequence neither the Little Geeks Foundation nor any of is representatives nor agents can be held responsible for materials acquired while surfing the web. Should there be any problems with the machine, then the Little Geeks Foundation will try to make repairs remotely, meaning either by phone or by Internet. Any information accessed in this process by the Little Geeks Foundation will be treated in the strictest confidence except in situations that warrant contacting guardians, parents or the police. The Little Geeks Foundation hopes you enjoy your new computer and we look forward to hearing of your progress. _________________________________________ ________________________________ Parent / Guardian Date Revised March 1, 2009
- 3. Computer Receipt By accepting delivery of this computer system, I fully acknowledge and agree to the following terms and conditions: • This is a previously use, fully functional computer, refurbished by the Little Geeks Foundation and it’s partners. • The system includes a computer, monitor, keyboard and mouse. • Computers are distributed in a non-preferential and fair manner and all users receive a similar type computer. • These computers have been equiped with anti-virus and anti-spyware software that may require updating from time to time. • Our systems have a one-year hardware warranty. These computers should only be serviced by the Little Geeks Foundation. • THE SOFTWARE ON THESE COMPUTERS SHOULD NOT BE ALTERED, UNINSTALLED OR MODIFIED IN ANY WAY. DOING SO WILL VOID ANY REPAIR OBLIGATIONS BY LITTLE GEEKS. • The Little Geeks Foundation reserves the right to reclaim a user’s computer. Date: Jan. Feb. March April May June July August Sept. Oct. Nov. Dec. 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 2010 Parent / Legal Guardian name: ______________________________ (Please print) Parent / Legal Guardian Signature: __________________________ (Please sign) Revised March 16, 2009