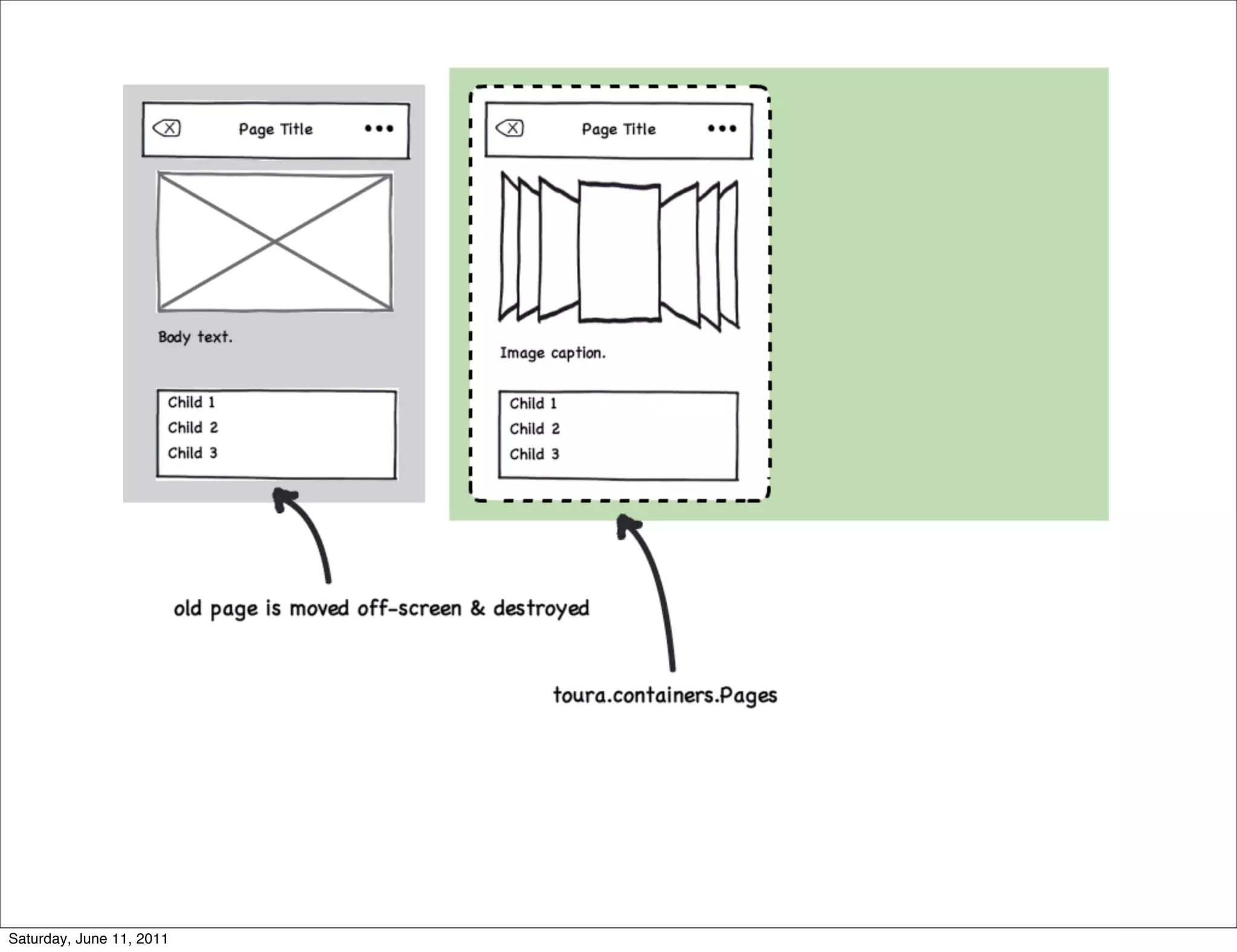
- Software rewrites are tempting but often more difficult than initially expected. It's better to write code that can coexist with existing software as an optional add-on.
- When using new systems or technologies, plan to build a "throwaway" version first since the best planning won't get it right the first time.
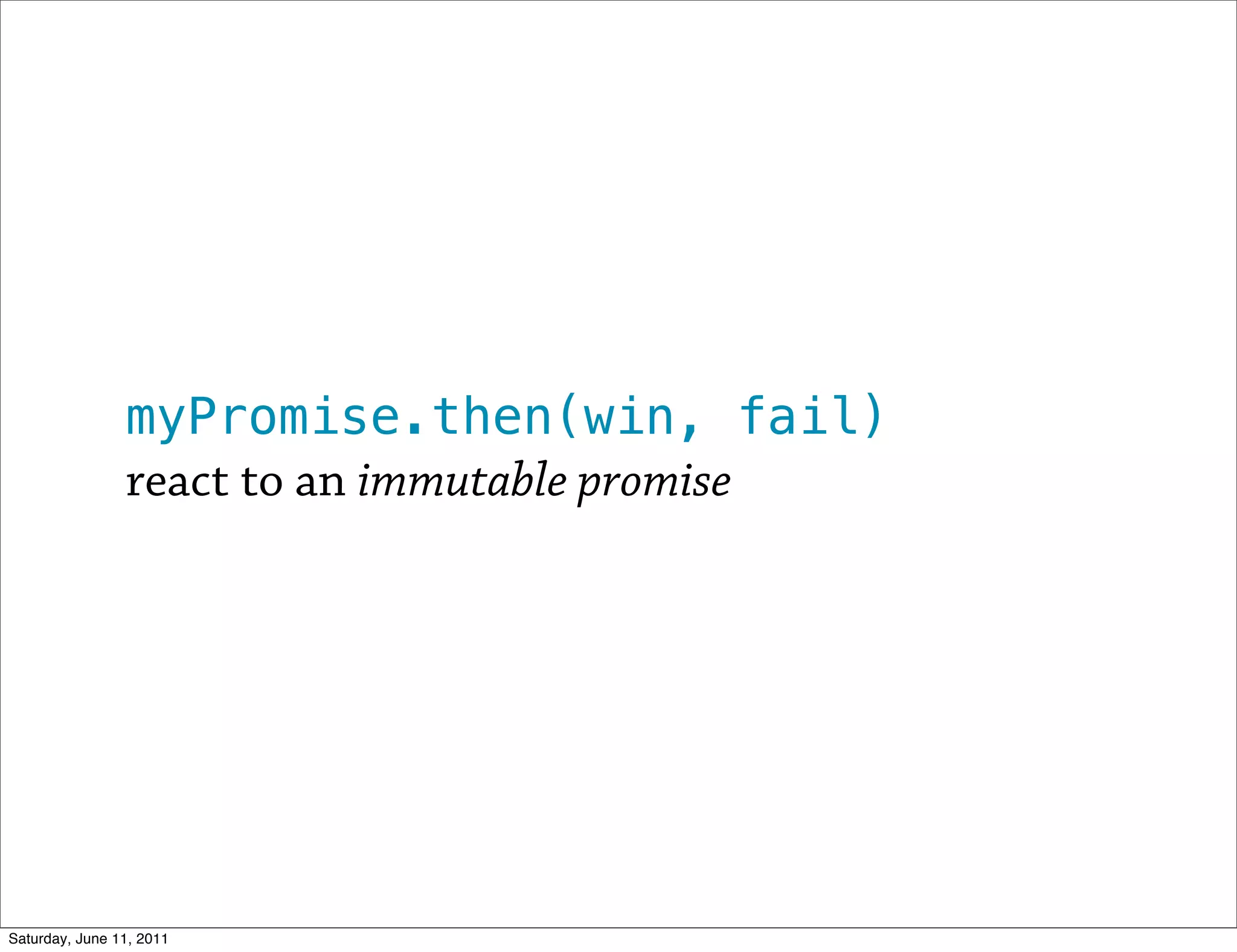
- For early-stage products, don't sink too much time and money into implementation until proving market viability. Build minimal throwaway proof-of-concept versions instead.
- Code is generally harder to read than write, so old code often seems like a "mess" even if it's not.
![Until you are able to prove that you have a
viable market ... you shouldn’t be sinking a lot
of time and money into implementation.
Assuming you are [competent], you should be
able to ... take on quite a bit of technical
debt to build throwaway proof-of-concept
versions of your product.
Obie Fernandez
Saturday, June 11, 2011](https://image.slidesharecdn.com/lessons-from-a-rewrite-110611144158-phpapp01/75/Lessons-from-a-Rewrite-4-2048.jpg)
![}
}],
"parent": {
"_reference": "node-365"
},
"page_controller": "Audios1",
"id": "node-369",
"sharing_text": null,
"sharing_url": null,
"images": [{
"caption": {
"_reference": "text-asset-60"
},
"image": {
"_reference": "image-174"
}
}, {
"caption": {
"_reference": "text-asset-61"
},
"image": {
"_reference": "image-182"
Saturday, June 11, 2011
}](https://image.slidesharecdn.com/lessons-from-a-rewrite-110611144158-phpapp01/75/Lessons-from-a-Rewrite-15-2048.jpg)


![this.placements = [
[
'VideoCaption',
{ node : this.node },
'videoCaption'
],
[
'VideoList',
{ node : this.node },
'videoList'
],
[
'VideoPlayer',
{ node : this.node },
'videoPlayer'
]
];
Saturday, June 11, 2011](https://image.slidesharecdn.com/lessons-from-a-rewrite-110611144158-phpapp01/75/Lessons-from-a-Rewrite-25-2048.jpg)

![videoPlayer.set('mediaId', mediaId);
_setMediaIdAttr : function(mediaId) {
var media = this.media = this.mediasCache[mediaId];
if (this.useHtml5Player && !this.player) {
this._queuedMedia = media;
return;
}
this._queuedMedia = null;
if (this.player) {
this.player.src = media.url;
}
},
Saturday, June 11, 2011](https://image.slidesharecdn.com/lessons-from-a-rewrite-110611144158-phpapp01/75/Lessons-from-a-Rewrite-27-2048.jpg)

![/* {{^android}} */
var mediaPath = "www/media/" + toura.pages.currentId +
"/";
/* {{/android}} */
/* {{#android}} */
var mediaPath = [Toura.getTouraPath(),
toura.pages.currentId].join("/");
/* {{/android}} */
var imagesList = [], dimensionsList = [], namesList =
[], thumbsList = [];
var pos = -1, count = 0;
/* {{#android}} */
var pos = 0, count = 0;
/* {{/android}} */
Saturday, June 11, 2011](https://image.slidesharecdn.com/lessons-from-a-rewrite-110611144158-phpapp01/75/Lessons-from-a-Rewrite-33-2048.jpg)

![{
route : //node/(.*)/,
handler : function(params, route) {
var splat = params.splat[0].split('/'),
nodeId = splat[0],
pageState = {
assetType : splat[1],
assetId : splat[2],
assetSubId : splat[3]
};
return nodeRoute(route, nodeId, pageState);
}
},
{
route : //search/?(.*)/,
handler : function(params) {
var page = toura.app.UI.getCurrentPage(),
term = params.splat && params.splat[0].split('/')[0];
if (!page || !page.type || page.type !== 'search') {
Saturday, June 11, 2011](https://image.slidesharecdn.com/lessons-from-a-rewrite-110611144158-phpapp01/75/Lessons-from-a-Rewrite-47-2048.jpg)
![dojo.require('dojo.Stateful');
dojo.declare('toura.app.UI', [ dojo.Stateful ], {
// ...
});
Saturday, June 11, 2011](https://image.slidesharecdn.com/lessons-from-a-rewrite-110611144158-phpapp01/75/Lessons-from-a-Rewrite-49-2048.jpg)
![expect(c.queryInput).toBeDefined();
expect(c.i18n_placeholderText).toBeTruthy();
});
});
it("should provide an API for setting the search term", function() {
c = C();
c.set('searchTerm', term);
expect(c.queryInput.value).toBe(term);
});
it("should announce searches when the form is submitted with a term", function() {
var submitHandler;
toura.app.UI.hasTouch = false;
c = C();
c.set('searchTerm', term);
spyOn(c, 'search');
submitHandler = getEventHandlers(c, 'submit', c.searchForm)[0];
submitHandler(fakeEventObj);
expect(c.search).toHaveBeenCalledWith(term);
});
it("should not announce searches if the form is submitted with no term", function() {
var submitHandler;
toura.app.UI.hasTouch = false;
c = C();
c.set('searchTerm', '');
spyOn(c, 'search');
Saturday, June 11, 2011 submitHandler = getEventHandlers(c, 'submit', c.searchForm)[0];](https://image.slidesharecdn.com/lessons-from-a-rewrite-110611144158-phpapp01/75/Lessons-from-a-Rewrite-53-2048.jpg)