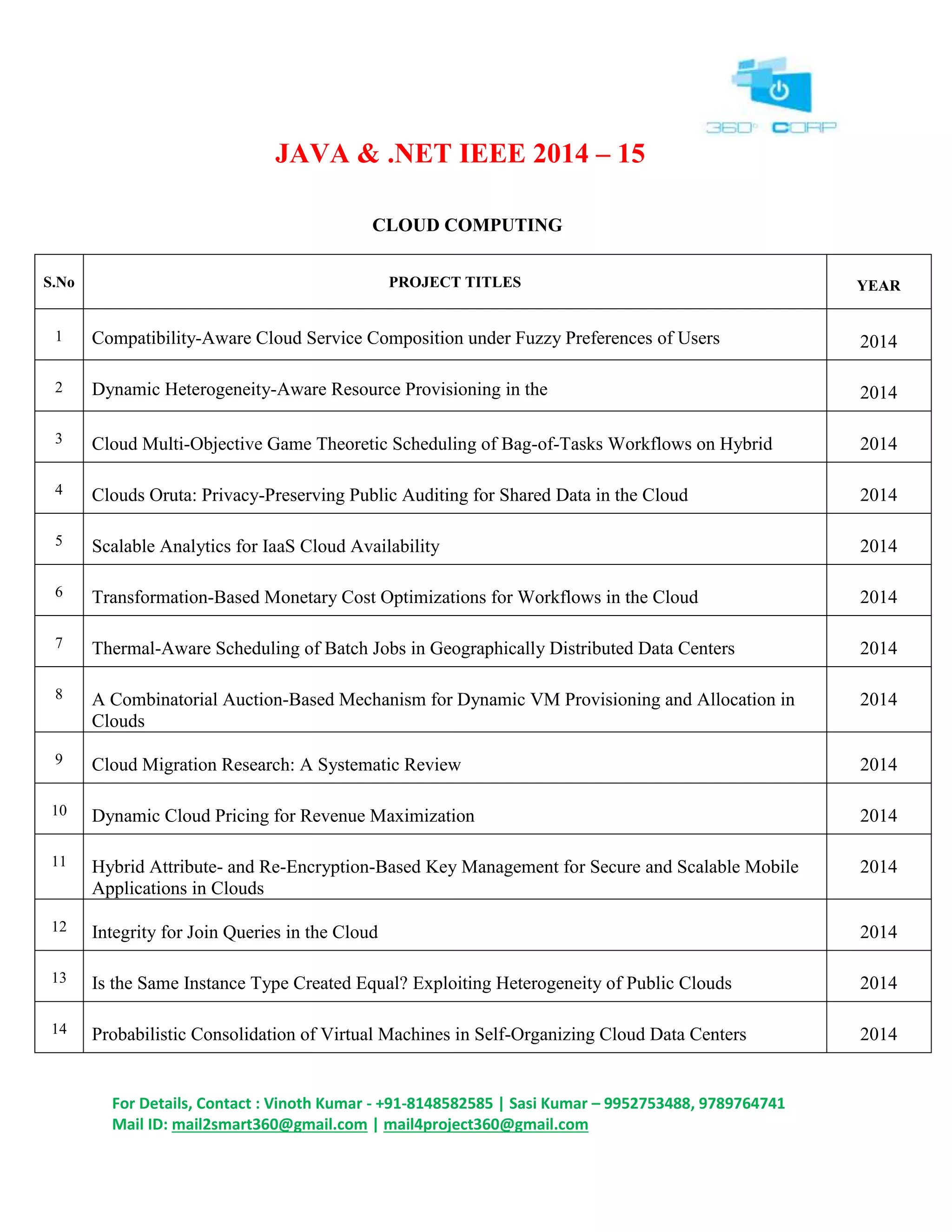
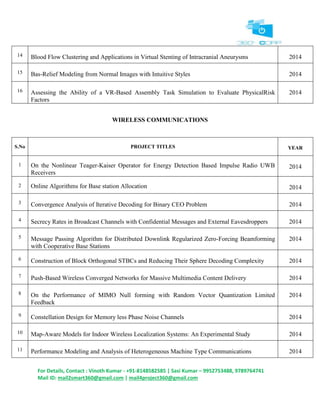
This document contains details of projects in various domains like cloud computing, data mining, network security, networking, parallel and distributed systems and service computing from the years 2014-2015. It lists the project titles and year of completion. It also provides contact details for project details. The document contains over 200 projects spanning 16 domains of research from IEEE 2014-15.