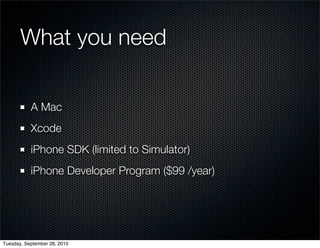
This document provides an overview of iPhone development for .NET developers. It discusses the tools needed like Xcode and the iOS SDK. It introduces Objective-C concepts like classes, methods, memory management using retain/release. It also covers view controllers, the model-view-controller pattern, and the iOS application lifecycle. The goal is to help .NET developers get started with iPhone development.
![Objective-C Primer
Calling methods
[someObject someMethod];
Tuesday, September 28, 2010](https://image.slidesharecdn.com/iphone-for-net-developers-100928184819-phpapp01/85/iPhone-for-NET-Developers-5-320.jpg)
![Objective-C Primer
Calling methods
[someObject someMethod];
[someObject someMethodWithInput:5];
Tuesday, September 28, 2010](https://image.slidesharecdn.com/iphone-for-net-developers-100928184819-phpapp01/85/iPhone-for-NET-Developers-6-320.jpg)
![Objective-C Primer
Calling methods
[someObject someMethod];
[someObject someMethodWithInput:5];
[dictionary setObject:obj
forKey:key];
Tuesday, September 28, 2010](https://image.slidesharecdn.com/iphone-for-net-developers-100928184819-phpapp01/85/iPhone-for-NET-Developers-7-320.jpg)
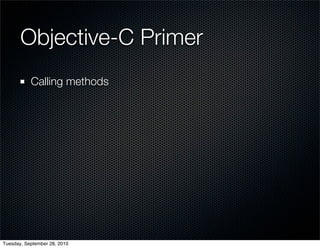
![Objective-C Primer
Nesting method calls
[NSString stringWithFormat:
[prefs format]];
Tuesday, September 28, 2010](https://image.slidesharecdn.com/iphone-for-net-developers-100928184819-phpapp01/85/iPhone-for-NET-Developers-9-320.jpg)
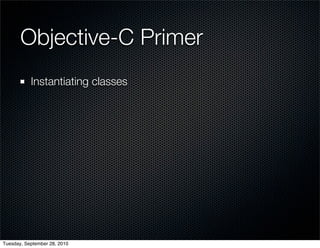
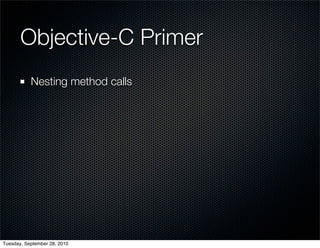
![Objective-C Primer
Instantiating classes
UIView *view = [[UIView alloc] init];
Tuesday, September 28, 2010](https://image.slidesharecdn.com/iphone-for-net-developers-100928184819-phpapp01/85/iPhone-for-NET-Developers-11-320.jpg)
![Objective-C Primer
Instantiating classes
UIView *view = [[UIView alloc] init];
NSDate *date = [NSDate date];
Tuesday, September 28, 2010](https://image.slidesharecdn.com/iphone-for-net-developers-100928184819-phpapp01/85/iPhone-for-NET-Developers-12-320.jpg)

![Memory Management
Retain / Release Dance
1
Foo *foo = [[Foo alloc] init];
Tuesday, September 28, 2010](https://image.slidesharecdn.com/iphone-for-net-developers-100928184819-phpapp01/85/iPhone-for-NET-Developers-25-320.jpg)
![Memory Management
Retain / Release Dance
1
Foo *foo = [[Foo alloc] init];
2
[foo retain];
Tuesday, September 28, 2010](https://image.slidesharecdn.com/iphone-for-net-developers-100928184819-phpapp01/85/iPhone-for-NET-Developers-26-320.jpg)
![Memory Management
Retain / Release Dance
1
Foo *foo = [[Foo alloc] init];
2
[foo retain];
1
[foo release];
Tuesday, September 28, 2010](https://image.slidesharecdn.com/iphone-for-net-developers-100928184819-phpapp01/85/iPhone-for-NET-Developers-27-320.jpg)
![Memory Management
Retain / Release Dance
1
Foo *foo = [[Foo alloc] init];
2
[foo retain];
1
[foo release];
[foo release]; 0
Tuesday, September 28, 2010](https://image.slidesharecdn.com/iphone-for-net-developers-100928184819-phpapp01/85/iPhone-for-NET-Developers-28-320.jpg)
![Memory Management
Retain / Release Dance
1
Foo *foo = [[Foo alloc] init];
2
[foo retain];
1
[foo release];
[foo release]; foo is deallocated 0
Tuesday, September 28, 2010](https://image.slidesharecdn.com/iphone-for-net-developers-100928184819-phpapp01/85/iPhone-for-NET-Developers-29-320.jpg)

![Getters / Setters
[foo setBar:@"baz"];
Tuesday, September 28, 2010](https://image.slidesharecdn.com/iphone-for-net-developers-100928184819-phpapp01/85/iPhone-for-NET-Developers-31-320.jpg)
![Getters / Setters
[foo setBar:@"baz"];
[foo bar]; //returns @"baz"
Tuesday, September 28, 2010](https://image.slidesharecdn.com/iphone-for-net-developers-100928184819-phpapp01/85/iPhone-for-NET-Developers-32-320.jpg)
![Getters / Setters
[foo setBar:@"baz"];
[foo bar]; //returns @"baz"
foo.bar = @"gruul";
Tuesday, September 28, 2010](https://image.slidesharecdn.com/iphone-for-net-developers-100928184819-phpapp01/85/iPhone-for-NET-Developers-33-320.jpg)
![Getters / Setters
[foo setBar:@"baz"];
[foo bar]; //returns @"baz"
foo.bar = @"gruul";
foo.bar //returns @"gruul"
Tuesday, September 28, 2010](https://image.slidesharecdn.com/iphone-for-net-developers-100928184819-phpapp01/85/iPhone-for-NET-Developers-34-320.jpg)

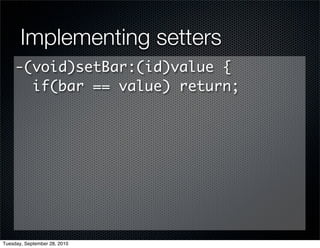
![Implementing setters
-(void)setBar:(id)value {
if(bar == value) return;
if(bar != nil) {
[bar release];
Tuesday, September 28, 2010](https://image.slidesharecdn.com/iphone-for-net-developers-100928184819-phpapp01/85/iPhone-for-NET-Developers-39-320.jpg)
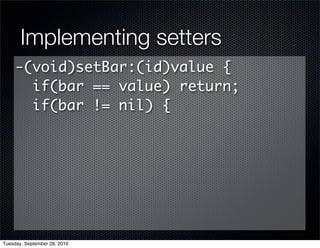
![Implementing setters
-(void)setBar:(id)value {
if(bar == value) return;
if(bar != nil) {
[bar release];
bar = nil;
Tuesday, September 28, 2010](https://image.slidesharecdn.com/iphone-for-net-developers-100928184819-phpapp01/85/iPhone-for-NET-Developers-40-320.jpg)
![Implementing setters
-(void)setBar:(id)value {
if(bar == value) return;
if(bar != nil) {
[bar release];
bar = nil;
}
Tuesday, September 28, 2010](https://image.slidesharecdn.com/iphone-for-net-developers-100928184819-phpapp01/85/iPhone-for-NET-Developers-41-320.jpg)
![Implementing setters
-(void)setBar:(id)value {
if(bar == value) return;
if(bar != nil) {
[bar release];
bar = nil;
}
if(value != nil)
Tuesday, September 28, 2010](https://image.slidesharecdn.com/iphone-for-net-developers-100928184819-phpapp01/85/iPhone-for-NET-Developers-42-320.jpg)
![Implementing setters
-(void)setBar:(id)value {
if(bar == value) return;
if(bar != nil) {
[bar release];
bar = nil;
}
if(value != nil)
bar = [value retain];
Tuesday, September 28, 2010](https://image.slidesharecdn.com/iphone-for-net-developers-100928184819-phpapp01/85/iPhone-for-NET-Developers-43-320.jpg)
![Implementing setters
-(void)setBar:(id)value {
if(bar == value) return;
if(bar != nil) {
[bar release];
bar = nil;
}
if(value != nil)
bar = [value retain];
}
Tuesday, September 28, 2010](https://image.slidesharecdn.com/iphone-for-net-developers-100928184819-phpapp01/85/iPhone-for-NET-Developers-44-320.jpg)
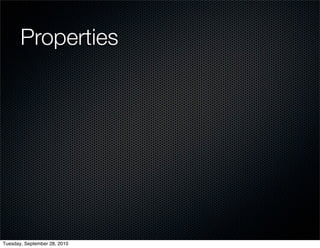
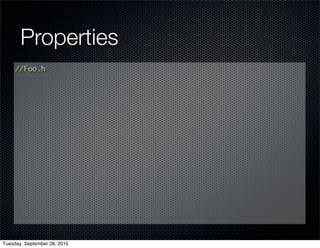
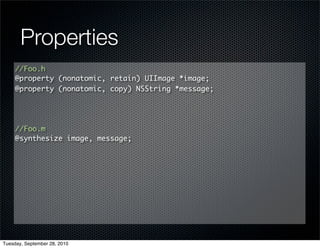
![Properties
//Foo.h
@property (nonatomic, retain) UIImage *image;
@property (nonatomic, copy) NSString *message;
//Foo.m
@synthesize image, message;
-(void)dealloc {
[image release];
Tuesday, September 28, 2010](https://image.slidesharecdn.com/iphone-for-net-developers-100928184819-phpapp01/85/iPhone-for-NET-Developers-53-320.jpg)
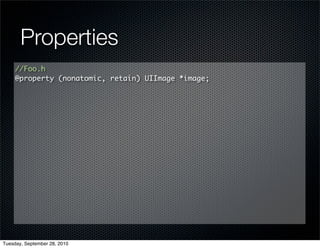
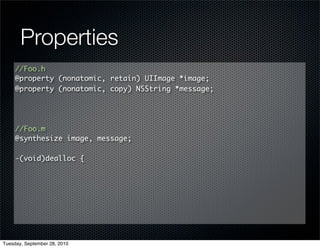
![Properties
//Foo.h
@property (nonatomic, retain) UIImage *image;
@property (nonatomic, copy) NSString *message;
//Foo.m
@synthesize image, message;
-(void)dealloc {
[image release];
[message release];
Tuesday, September 28, 2010](https://image.slidesharecdn.com/iphone-for-net-developers-100928184819-phpapp01/85/iPhone-for-NET-Developers-54-320.jpg)
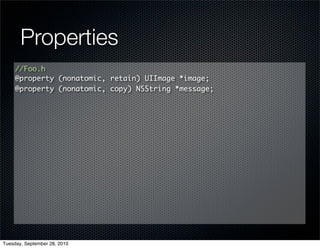
![Properties
//Foo.h
@property (nonatomic, retain) UIImage *image;
@property (nonatomic, copy) NSString *message;
//Foo.m
@synthesize image, message;
-(void)dealloc {
[image release];
[message release];
[super dealloc];
Tuesday, September 28, 2010](https://image.slidesharecdn.com/iphone-for-net-developers-100928184819-phpapp01/85/iPhone-for-NET-Developers-55-320.jpg)
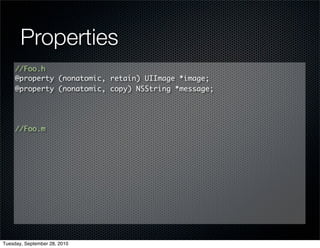
![Properties
//Foo.h
@property (nonatomic, retain) UIImage *image;
@property (nonatomic, copy) NSString *message;
//Foo.m
@synthesize image, message;
-(void)dealloc {
[image release];
[message release];
[super dealloc];
}
Tuesday, September 28, 2010](https://image.slidesharecdn.com/iphone-for-net-developers-100928184819-phpapp01/85/iPhone-for-NET-Developers-56-320.jpg)