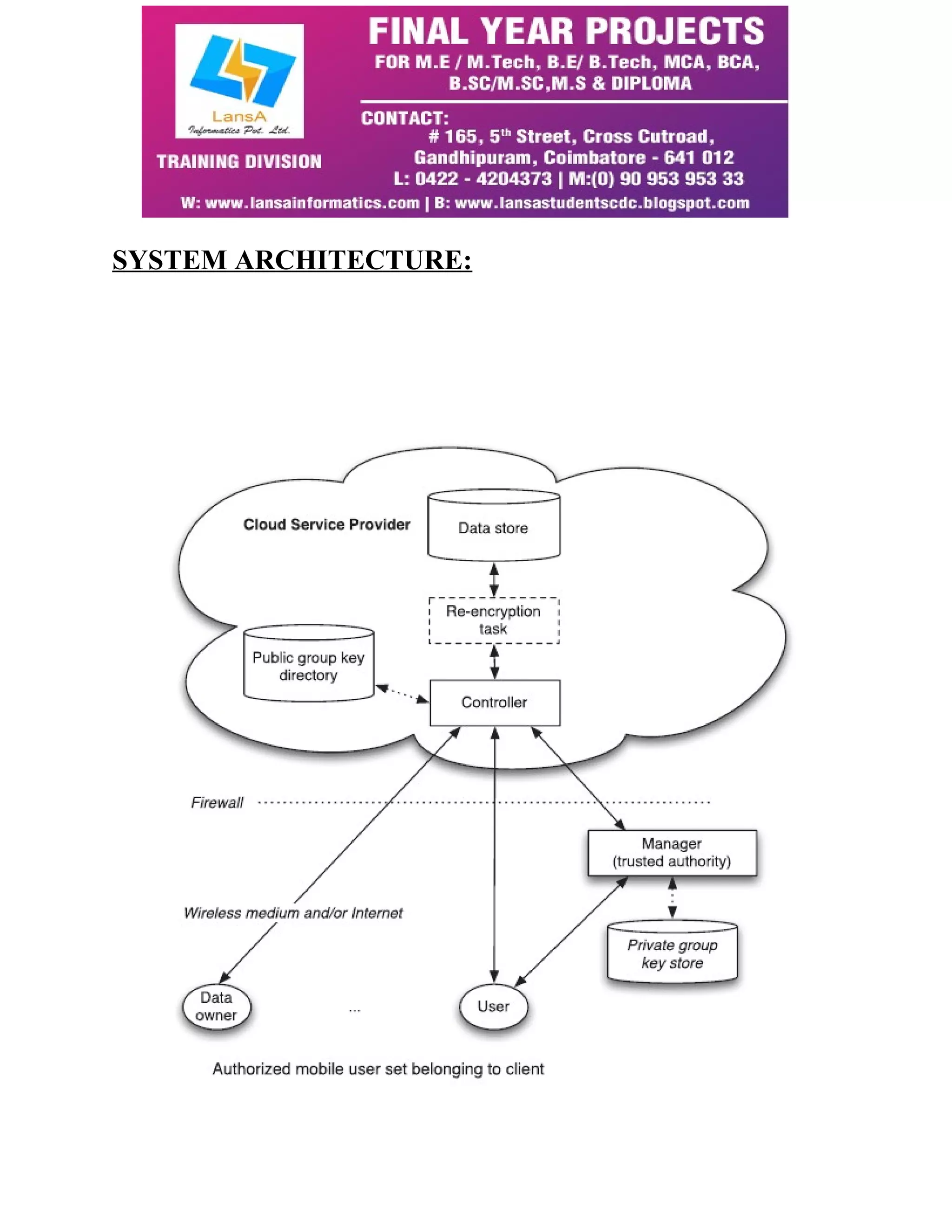
The document discusses a proposed protocol for secure data storage in the cloud, focusing on a hybrid attribute-based encryption and re-encryption system designed for mobile applications. It addresses security concerns by allowing only authorized users to access data based on specified attributes, shifting computational burdens to the cloud provider. This system enhances efficiency, reduces data traffic, and offers better key management, making it suitable for sensitive information while being accessible from resource-constrained mobile devices.