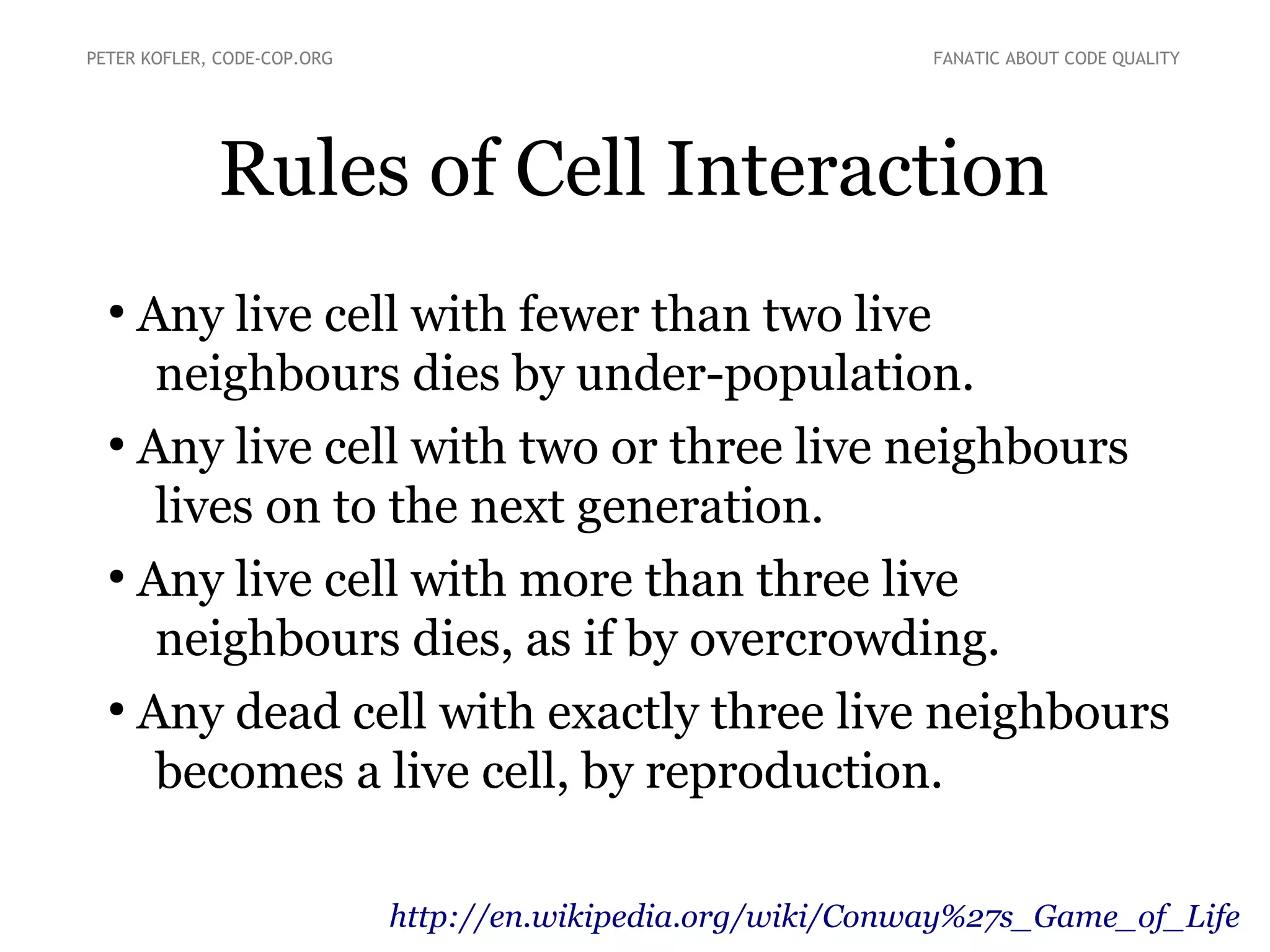
The document describes a Global Day of Code Retreat event in Vienna in December 2013 hosted by Peter Kofler. The one-day event focuses on improving code quality through collaborative coding exercises and principles of test-driven development. Attendees will participate in sessions practicing pairing programming, refactoring existing code, and discussing techniques for writing high-quality code. The goal is for participants to learn through doing rather than focusing on completing the exercises.