DIGIPASS for web powered by Intel
•
0 likes•233 views
DIGIPASS for web powered by Intel - 201110 v3b
Report
Share
Report
Share
Download to read offline
Recommended
Alliance universit ybabballb fee-structure

The document outlines the fee structure for the B.A. LL.B. (Hons.) and B.B.A. LL.B. (Hons.) programs at Alliance University for the years 2015-2020. It provides the tuition fees, payment due dates, and total payable amounts for Indian nationals, NRIs/SAARC nationals, and other foreign nationals. Additionally, it lists the hostel fees for on-campus accommodation including security deposits and meal plan costs for triple, double, and single occupancy rooms. All fees are subject to change and payment should be made via demand draft in the specified currency and in favor of Alliance University.
Increasing your mobile banking business

With the potential to create everything from new revenue opportunities, to increased customer acquisition to cost savings, mobile is changing the landscape of banking as we know it. The rollout of foundational mobile services is already yielding tremendous success, and by increasing security while keeping a keen eye on user experience, leading banks and financial services providers can offer more advanced mobile services, which will play a key role in their growth strategies.
By broadening mobile banking offerings, financial institutions will be positioned to increase mobile transactions, shift transactions away from higher-cost channels, and retain and attract more customers.
To be successful with mobile, VASCO understands that banks need to pay close attention to the security of mobile applications and consumers, without creating challenges for the user experience.
MYDIGIPASS.COM leaflet

VASCO's MYDIGIPASS.COM service allows websites to easily integrate strong two-factor authentication to securely authenticate users and protect content. The service provides a customizable secure launch pad that highlights the website's content and builds its brand community. It also simplifies access for users by eliminating separate passwords. MYDIGIPASS.COM is suitable for any website that offers password-protected online content and provides banking-level security through VASCO's proven authentication technologies.
We Authenticate the World

VASCO is a leading provider of authentication solutions and services specializing in internet security. It offers a range of backend platforms and end-user authentication devices to secure online transactions for applications such as banking, enterprise systems, and other online applications. Some of its key products include the VACMAN platform, IDENTIKEY authentication servers, and DIGIPASS authentication devices. VASCO serves over 100 countries and helps customers secure many different applications and online transactions.
Secure Online Banking

VASCO is a leading provider of strong authentication and e-signature solutions, specializing in internet security. They help customers in over 100 countries securely deploy authentication solutions. Their full-option approach ensures all authentication technologies work on their single VACMAN platform, including over 50 DIGIPASS end-user devices. They offer banking-level security for a variety of industries and applications. Their strategy is to expand their financial sector solutions to other markets while enhancing their security products and services.
Secure your Business

VASCO is a leading supplier of strong authentication and e-signature solutions specializing in internet security. They help customers around the globe deploy strong authentication solutions for securing access to networks, applications, and online transactions. VASCO offers a full range of authentication technologies including hardware and software-based authentication devices, as well as electronic and digital signature solutions. Their solutions can be used to secure a variety of business applications across many industries.
Identikey

VASCO is a leading global provider of strong authentication and e-signature solutions. It offers the IDENTIKEY Authentication Server and other products for securing internet transactions. VASCO has offices worldwide and serves customers in over 100 countries, especially in financial services, enterprise security, e-commerce, and e-government. It provides authentication, consulting, training, and support services to help customers implement authentication solutions.
How to successfully implement a secure mobile strategy

VASCO provides several mobile authentication solutions to help organizations successfully implement a secure mobile strategy. These solutions include DIGIPASS for Mobile, Virtual DIGIPASS, DIGIPASS Nano, DIGIPASS powered by Intel ITP, and DIGIPASS SDK. They allow for two-factor authentication on mobile devices for secure access to corporate networks and applications from any location. Case studies demonstrate how National Bank of Fujairah, Rotterdam University, Qatargas, Randstad Germany, and HSBC Bank Brazil have successfully implemented VASCO's mobile authentication solutions.
Recommended
Alliance universit ybabballb fee-structure

The document outlines the fee structure for the B.A. LL.B. (Hons.) and B.B.A. LL.B. (Hons.) programs at Alliance University for the years 2015-2020. It provides the tuition fees, payment due dates, and total payable amounts for Indian nationals, NRIs/SAARC nationals, and other foreign nationals. Additionally, it lists the hostel fees for on-campus accommodation including security deposits and meal plan costs for triple, double, and single occupancy rooms. All fees are subject to change and payment should be made via demand draft in the specified currency and in favor of Alliance University.
Increasing your mobile banking business

With the potential to create everything from new revenue opportunities, to increased customer acquisition to cost savings, mobile is changing the landscape of banking as we know it. The rollout of foundational mobile services is already yielding tremendous success, and by increasing security while keeping a keen eye on user experience, leading banks and financial services providers can offer more advanced mobile services, which will play a key role in their growth strategies.
By broadening mobile banking offerings, financial institutions will be positioned to increase mobile transactions, shift transactions away from higher-cost channels, and retain and attract more customers.
To be successful with mobile, VASCO understands that banks need to pay close attention to the security of mobile applications and consumers, without creating challenges for the user experience.
MYDIGIPASS.COM leaflet

VASCO's MYDIGIPASS.COM service allows websites to easily integrate strong two-factor authentication to securely authenticate users and protect content. The service provides a customizable secure launch pad that highlights the website's content and builds its brand community. It also simplifies access for users by eliminating separate passwords. MYDIGIPASS.COM is suitable for any website that offers password-protected online content and provides banking-level security through VASCO's proven authentication technologies.
We Authenticate the World

VASCO is a leading provider of authentication solutions and services specializing in internet security. It offers a range of backend platforms and end-user authentication devices to secure online transactions for applications such as banking, enterprise systems, and other online applications. Some of its key products include the VACMAN platform, IDENTIKEY authentication servers, and DIGIPASS authentication devices. VASCO serves over 100 countries and helps customers secure many different applications and online transactions.
Secure Online Banking

VASCO is a leading provider of strong authentication and e-signature solutions, specializing in internet security. They help customers in over 100 countries securely deploy authentication solutions. Their full-option approach ensures all authentication technologies work on their single VACMAN platform, including over 50 DIGIPASS end-user devices. They offer banking-level security for a variety of industries and applications. Their strategy is to expand their financial sector solutions to other markets while enhancing their security products and services.
Secure your Business

VASCO is a leading supplier of strong authentication and e-signature solutions specializing in internet security. They help customers around the globe deploy strong authentication solutions for securing access to networks, applications, and online transactions. VASCO offers a full range of authentication technologies including hardware and software-based authentication devices, as well as electronic and digital signature solutions. Their solutions can be used to secure a variety of business applications across many industries.
Identikey

VASCO is a leading global provider of strong authentication and e-signature solutions. It offers the IDENTIKEY Authentication Server and other products for securing internet transactions. VASCO has offices worldwide and serves customers in over 100 countries, especially in financial services, enterprise security, e-commerce, and e-government. It provides authentication, consulting, training, and support services to help customers implement authentication solutions.
How to successfully implement a secure mobile strategy

VASCO provides several mobile authentication solutions to help organizations successfully implement a secure mobile strategy. These solutions include DIGIPASS for Mobile, Virtual DIGIPASS, DIGIPASS Nano, DIGIPASS powered by Intel ITP, and DIGIPASS SDK. They allow for two-factor authentication on mobile devices for secure access to corporate networks and applications from any location. Case studies demonstrate how National Bank of Fujairah, Rotterdam University, Qatargas, Randstad Germany, and HSBC Bank Brazil have successfully implemented VASCO's mobile authentication solutions.
aXsGuard Gatekeeper

This document provides information on the aXsGUARD Gatekeeper, a security appliance from VASCO that offers a complete solution for secure remote network access. It has four software bundles - Basic, Standard, Enterprise, and Enterprise Backup - that can run on five hardware models and provide features like firewall, VPN, authentication, and content scanning. The document outlines the included features for each software bundle and hardware specifications. It also describes the content scanning options for mail and web traffic and provides examples of how the aXsGUARD Gatekeeper can be used in different solutions.
DIGIPASS for Apps

DIGIPASS for APPS is a framework that provides a comprehensive set of features to securely protect web and mobile applications. It offers secure authentication, data protection, and lifecycle management capabilities. These include multi-factor authentication, secure storage, device binding, provisioning and reactivation to help secure applications across platforms and layers.
MYDIGIPASS.COM

The document discusses password security and introduces MYDIGIPASS.COM as an app that aims to provide a more secure and convenient way to manage multiple passwords and digital identities. It notes that password theft increased dramatically in 2012. MYDIGIPASS.COM would allow users to log into websites using a single password while providing two-factor authentication. The document outlines benefits for both application owners and users, positioning MYDIGIPASS.COM as a solution to the challenges of digital identity management across multiple devices and applications.
Password fatigation

The document discusses identity and access management solutions using VASCO's IDENTIKEY Federation Server, including single sign-on capabilities, reducing costs of managing user identities and authentication across multiple applications and systems, and securing access for internal employee and external business partners. It provides an overview of key features and benefits of the IDENTIKEY Federation Server for centralized user authentication, identity federation, and single sign-on across various applications.
Infosec1november

The document discusses secure identity challenges and how VASCO Data Security helps solve them. It describes the growing issues of digital identity across multiple devices and apps, and consumers reusing the same passwords. VASCO provides strong authentication solutions like DIGIPASS tokens to securely and conveniently authenticate users on any device. The presentation outlines VASCO's philosophy of balancing security, ease of use and cost-effectiveness and provides examples of how their solutions enable online applications and transactions from any location.
Infosec31october

Yes, DIGIPASS authentication can enable online applications by addressing both application owner and user concerns:
- For application owners, DIGIPASS provides a secure authentication method that can help build user communities and drive conversion/traffic.
- For users, DIGIPASS authentication is very easy to use from any internet-connected device, allowing access from "my lazy chair." Some DIGIPASS models like the GO and Nano are as simple as entering a code to log in, avoiding complex passwords.
By balancing strong security with ease of use, DIGIPASS authentication can help unlock the potential of online applications and services for both those providing and using the applications. The right DIGIPASS solution can be an enabler, removing
Fueling AI with Great Data with Airbyte Webinar

This talk will focus on how to collect data from a variety of sources, leveraging this data for RAG and other GenAI use cases, and finally charting your course to productionalization.
GNSS spoofing via SDR (Criptored Talks 2024)

In the realm of cybersecurity, offensive security practices act as a critical shield. By simulating real-world attacks in a controlled environment, these techniques expose vulnerabilities before malicious actors can exploit them. This proactive approach allows manufacturers to identify and fix weaknesses, significantly enhancing system security.
This presentation delves into the development of a system designed to mimic Galileo's Open Service signal using software-defined radio (SDR) technology. We'll begin with a foundational overview of both Global Navigation Satellite Systems (GNSS) and the intricacies of digital signal processing.
The presentation culminates in a live demonstration. We'll showcase the manipulation of Galileo's Open Service pilot signal, simulating an attack on various software and hardware systems. This practical demonstration serves to highlight the potential consequences of unaddressed vulnerabilities, emphasizing the importance of offensive security practices in safeguarding critical infrastructure.
Dandelion Hashtable: beyond billion requests per second on a commodity server

This slide deck presents DLHT, a concurrent in-memory hashtable. Despite efforts to optimize hashtables, that go as far as sacrificing core functionality, state-of-the-art designs still incur multiple memory accesses per request and block request processing in three cases. First, most hashtables block while waiting for data to be retrieved from memory. Second, open-addressing designs, which represent the current state-of-the-art, either cannot free index slots on deletes or must block all requests to do so. Third, index resizes block every request until all objects are copied to the new index. Defying folklore wisdom, DLHT forgoes open-addressing and adopts a fully-featured and memory-aware closed-addressing design based on bounded cache-line-chaining. This design offers lock-free index operations and deletes that free slots instantly, (2) completes most requests with a single memory access, (3) utilizes software prefetching to hide memory latencies, and (4) employs a novel non-blocking and parallel resizing. In a commodity server and a memory-resident workload, DLHT surpasses 1.6B requests per second and provides 3.5x (12x) the throughput of the state-of-the-art closed-addressing (open-addressing) resizable hashtable on Gets (Deletes).
Principle of conventional tomography-Bibash Shahi ppt..pptx

before the computed tomography, it had been widely used.
Columbus Data & Analytics Wednesdays - June 2024

Columbus Data & Analytics Wednesdays, June 2024 with Maria Copot 20
Mutation Testing for Task-Oriented Chatbots

Conversational agents, or chatbots, are increasingly used to access all sorts of services using natural language. While open-domain chatbots - like ChatGPT - can converse on any topic, task-oriented chatbots - the focus of this paper - are designed for specific tasks, like booking a flight, obtaining customer support, or setting an appointment. Like any other software, task-oriented chatbots need to be properly tested, usually by defining and executing test scenarios (i.e., sequences of user-chatbot interactions). However, there is currently a lack of methods to quantify the completeness and strength of such test scenarios, which can lead to low-quality tests, and hence to buggy chatbots.
To fill this gap, we propose adapting mutation testing (MuT) for task-oriented chatbots. To this end, we introduce a set of mutation operators that emulate faults in chatbot designs, an architecture that enables MuT on chatbots built using heterogeneous technologies, and a practical realisation as an Eclipse plugin. Moreover, we evaluate the applicability, effectiveness and efficiency of our approach on open-source chatbots, with promising results.
How to Interpret Trends in the Kalyan Rajdhani Mix Chart.pdf

A Mix Chart displays historical data of numbers in a graphical or tabular form. The Kalyan Rajdhani Mix Chart specifically shows the results of a sequence of numbers over different periods.
Northern Engraving | Nameplate Manufacturing Process - 2024

Manufacturing custom quality metal nameplates and badges involves several standard operations. Processes include sheet prep, lithography, screening, coating, punch press and inspection. All decoration is completed in the flat sheet with adhesive and tooling operations following. The possibilities for creating unique durable nameplates are endless. How will you create your brand identity? We can help!
zkStudyClub - LatticeFold: A Lattice-based Folding Scheme and its Application...

Folding is a recent technique for building efficient recursive SNARKs. Several elegant folding protocols have been proposed, such as Nova, Supernova, Hypernova, Protostar, and others. However, all of them rely on an additively homomorphic commitment scheme based on discrete log, and are therefore not post-quantum secure. In this work we present LatticeFold, the first lattice-based folding protocol based on the Module SIS problem. This folding protocol naturally leads to an efficient recursive lattice-based SNARK and an efficient PCD scheme. LatticeFold supports folding low-degree relations, such as R1CS, as well as high-degree relations, such as CCS. The key challenge is to construct a secure folding protocol that works with the Ajtai commitment scheme. The difficulty, is ensuring that extracted witnesses are low norm through many rounds of folding. We present a novel technique using the sumcheck protocol to ensure that extracted witnesses are always low norm no matter how many rounds of folding are used. Our evaluation of the final proof system suggests that it is as performant as Hypernova, while providing post-quantum security.
Paper Link: https://eprint.iacr.org/2024/257
5th LF Energy Power Grid Model Meet-up Slides

5th Power Grid Model Meet-up
It is with great pleasure that we extend to you an invitation to the 5th Power Grid Model Meet-up, scheduled for 6th June 2024. This event will adopt a hybrid format, allowing participants to join us either through an online Mircosoft Teams session or in person at TU/e located at Den Dolech 2, Eindhoven, Netherlands. The meet-up will be hosted by Eindhoven University of Technology (TU/e), a research university specializing in engineering science & technology.
Power Grid Model
The global energy transition is placing new and unprecedented demands on Distribution System Operators (DSOs). Alongside upgrades to grid capacity, processes such as digitization, capacity optimization, and congestion management are becoming vital for delivering reliable services.
Power Grid Model is an open source project from Linux Foundation Energy and provides a calculation engine that is increasingly essential for DSOs. It offers a standards-based foundation enabling real-time power systems analysis, simulations of electrical power grids, and sophisticated what-if analysis. In addition, it enables in-depth studies and analysis of the electrical power grid’s behavior and performance. This comprehensive model incorporates essential factors such as power generation capacity, electrical losses, voltage levels, power flows, and system stability.
Power Grid Model is currently being applied in a wide variety of use cases, including grid planning, expansion, reliability, and congestion studies. It can also help in analyzing the impact of renewable energy integration, assessing the effects of disturbances or faults, and developing strategies for grid control and optimization.
What to expect
For the upcoming meetup we are organizing, we have an exciting lineup of activities planned:
-Insightful presentations covering two practical applications of the Power Grid Model.
-An update on the latest advancements in Power Grid -Model technology during the first and second quarters of 2024.
-An interactive brainstorming session to discuss and propose new feature requests.
-An opportunity to connect with fellow Power Grid Model enthusiasts and users.
Skybuffer SAM4U tool for SAP license adoption

Manage and optimize your license adoption and consumption with SAM4U, an SAP free customer software asset management tool.
SAM4U, an SAP complimentary software asset management tool for customers, delivers a detailed and well-structured overview of license inventory and usage with a user-friendly interface. We offer a hosted, cost-effective, and performance-optimized SAM4U setup in the Skybuffer Cloud environment. You retain ownership of the system and data, while we manage the ABAP 7.58 infrastructure, ensuring fixed Total Cost of Ownership (TCO) and exceptional services through the SAP Fiori interface.
Leveraging the Graph for Clinical Trials and Standards

Katja Glaß
OpenStudyBuilder Community Manager - Katja Glaß Consulting
Marius Conjeaud
Principal Consultant - Neo4j
Energy Efficient Video Encoding for Cloud and Edge Computing Instances

Energy Efficient Video Encoding for Cloud and Edge Computing Instances
Taking AI to the Next Level in Manufacturing.pdf

Read Taking AI to the Next Level in Manufacturing to gain insights on AI adoption in the manufacturing industry, such as:
1. How quickly AI is being implemented in manufacturing.
2. Which barriers stand in the way of AI adoption.
3. How data quality and governance form the backbone of AI.
4. Organizational processes and structures that may inhibit effective AI adoption.
6. Ideas and approaches to help build your organization's AI strategy.
Crafting Excellence: A Comprehensive Guide to iOS Mobile App Development Serv...

Crafting Excellence: A Comprehensive Guide to iOS Mobile App Development Serv...Pitangent Analytics & Technology Solutions Pvt. Ltd
Discover top-tier mobile app development services, offering innovative solutions for iOS and Android. Enhance your business with custom, user-friendly mobile applications.More Related Content
More from VASCO Data Security
aXsGuard Gatekeeper

This document provides information on the aXsGUARD Gatekeeper, a security appliance from VASCO that offers a complete solution for secure remote network access. It has four software bundles - Basic, Standard, Enterprise, and Enterprise Backup - that can run on five hardware models and provide features like firewall, VPN, authentication, and content scanning. The document outlines the included features for each software bundle and hardware specifications. It also describes the content scanning options for mail and web traffic and provides examples of how the aXsGUARD Gatekeeper can be used in different solutions.
DIGIPASS for Apps

DIGIPASS for APPS is a framework that provides a comprehensive set of features to securely protect web and mobile applications. It offers secure authentication, data protection, and lifecycle management capabilities. These include multi-factor authentication, secure storage, device binding, provisioning and reactivation to help secure applications across platforms and layers.
MYDIGIPASS.COM

The document discusses password security and introduces MYDIGIPASS.COM as an app that aims to provide a more secure and convenient way to manage multiple passwords and digital identities. It notes that password theft increased dramatically in 2012. MYDIGIPASS.COM would allow users to log into websites using a single password while providing two-factor authentication. The document outlines benefits for both application owners and users, positioning MYDIGIPASS.COM as a solution to the challenges of digital identity management across multiple devices and applications.
Password fatigation

The document discusses identity and access management solutions using VASCO's IDENTIKEY Federation Server, including single sign-on capabilities, reducing costs of managing user identities and authentication across multiple applications and systems, and securing access for internal employee and external business partners. It provides an overview of key features and benefits of the IDENTIKEY Federation Server for centralized user authentication, identity federation, and single sign-on across various applications.
Infosec1november

The document discusses secure identity challenges and how VASCO Data Security helps solve them. It describes the growing issues of digital identity across multiple devices and apps, and consumers reusing the same passwords. VASCO provides strong authentication solutions like DIGIPASS tokens to securely and conveniently authenticate users on any device. The presentation outlines VASCO's philosophy of balancing security, ease of use and cost-effectiveness and provides examples of how their solutions enable online applications and transactions from any location.
Infosec31october

Yes, DIGIPASS authentication can enable online applications by addressing both application owner and user concerns:
- For application owners, DIGIPASS provides a secure authentication method that can help build user communities and drive conversion/traffic.
- For users, DIGIPASS authentication is very easy to use from any internet-connected device, allowing access from "my lazy chair." Some DIGIPASS models like the GO and Nano are as simple as entering a code to log in, avoiding complex passwords.
By balancing strong security with ease of use, DIGIPASS authentication can help unlock the potential of online applications and services for both those providing and using the applications. The right DIGIPASS solution can be an enabler, removing
More from VASCO Data Security (6)
Recently uploaded
Fueling AI with Great Data with Airbyte Webinar

This talk will focus on how to collect data from a variety of sources, leveraging this data for RAG and other GenAI use cases, and finally charting your course to productionalization.
GNSS spoofing via SDR (Criptored Talks 2024)

In the realm of cybersecurity, offensive security practices act as a critical shield. By simulating real-world attacks in a controlled environment, these techniques expose vulnerabilities before malicious actors can exploit them. This proactive approach allows manufacturers to identify and fix weaknesses, significantly enhancing system security.
This presentation delves into the development of a system designed to mimic Galileo's Open Service signal using software-defined radio (SDR) technology. We'll begin with a foundational overview of both Global Navigation Satellite Systems (GNSS) and the intricacies of digital signal processing.
The presentation culminates in a live demonstration. We'll showcase the manipulation of Galileo's Open Service pilot signal, simulating an attack on various software and hardware systems. This practical demonstration serves to highlight the potential consequences of unaddressed vulnerabilities, emphasizing the importance of offensive security practices in safeguarding critical infrastructure.
Dandelion Hashtable: beyond billion requests per second on a commodity server

This slide deck presents DLHT, a concurrent in-memory hashtable. Despite efforts to optimize hashtables, that go as far as sacrificing core functionality, state-of-the-art designs still incur multiple memory accesses per request and block request processing in three cases. First, most hashtables block while waiting for data to be retrieved from memory. Second, open-addressing designs, which represent the current state-of-the-art, either cannot free index slots on deletes or must block all requests to do so. Third, index resizes block every request until all objects are copied to the new index. Defying folklore wisdom, DLHT forgoes open-addressing and adopts a fully-featured and memory-aware closed-addressing design based on bounded cache-line-chaining. This design offers lock-free index operations and deletes that free slots instantly, (2) completes most requests with a single memory access, (3) utilizes software prefetching to hide memory latencies, and (4) employs a novel non-blocking and parallel resizing. In a commodity server and a memory-resident workload, DLHT surpasses 1.6B requests per second and provides 3.5x (12x) the throughput of the state-of-the-art closed-addressing (open-addressing) resizable hashtable on Gets (Deletes).
Principle of conventional tomography-Bibash Shahi ppt..pptx

before the computed tomography, it had been widely used.
Columbus Data & Analytics Wednesdays - June 2024

Columbus Data & Analytics Wednesdays, June 2024 with Maria Copot 20
Mutation Testing for Task-Oriented Chatbots

Conversational agents, or chatbots, are increasingly used to access all sorts of services using natural language. While open-domain chatbots - like ChatGPT - can converse on any topic, task-oriented chatbots - the focus of this paper - are designed for specific tasks, like booking a flight, obtaining customer support, or setting an appointment. Like any other software, task-oriented chatbots need to be properly tested, usually by defining and executing test scenarios (i.e., sequences of user-chatbot interactions). However, there is currently a lack of methods to quantify the completeness and strength of such test scenarios, which can lead to low-quality tests, and hence to buggy chatbots.
To fill this gap, we propose adapting mutation testing (MuT) for task-oriented chatbots. To this end, we introduce a set of mutation operators that emulate faults in chatbot designs, an architecture that enables MuT on chatbots built using heterogeneous technologies, and a practical realisation as an Eclipse plugin. Moreover, we evaluate the applicability, effectiveness and efficiency of our approach on open-source chatbots, with promising results.
How to Interpret Trends in the Kalyan Rajdhani Mix Chart.pdf

A Mix Chart displays historical data of numbers in a graphical or tabular form. The Kalyan Rajdhani Mix Chart specifically shows the results of a sequence of numbers over different periods.
Northern Engraving | Nameplate Manufacturing Process - 2024

Manufacturing custom quality metal nameplates and badges involves several standard operations. Processes include sheet prep, lithography, screening, coating, punch press and inspection. All decoration is completed in the flat sheet with adhesive and tooling operations following. The possibilities for creating unique durable nameplates are endless. How will you create your brand identity? We can help!
zkStudyClub - LatticeFold: A Lattice-based Folding Scheme and its Application...

Folding is a recent technique for building efficient recursive SNARKs. Several elegant folding protocols have been proposed, such as Nova, Supernova, Hypernova, Protostar, and others. However, all of them rely on an additively homomorphic commitment scheme based on discrete log, and are therefore not post-quantum secure. In this work we present LatticeFold, the first lattice-based folding protocol based on the Module SIS problem. This folding protocol naturally leads to an efficient recursive lattice-based SNARK and an efficient PCD scheme. LatticeFold supports folding low-degree relations, such as R1CS, as well as high-degree relations, such as CCS. The key challenge is to construct a secure folding protocol that works with the Ajtai commitment scheme. The difficulty, is ensuring that extracted witnesses are low norm through many rounds of folding. We present a novel technique using the sumcheck protocol to ensure that extracted witnesses are always low norm no matter how many rounds of folding are used. Our evaluation of the final proof system suggests that it is as performant as Hypernova, while providing post-quantum security.
Paper Link: https://eprint.iacr.org/2024/257
5th LF Energy Power Grid Model Meet-up Slides

5th Power Grid Model Meet-up
It is with great pleasure that we extend to you an invitation to the 5th Power Grid Model Meet-up, scheduled for 6th June 2024. This event will adopt a hybrid format, allowing participants to join us either through an online Mircosoft Teams session or in person at TU/e located at Den Dolech 2, Eindhoven, Netherlands. The meet-up will be hosted by Eindhoven University of Technology (TU/e), a research university specializing in engineering science & technology.
Power Grid Model
The global energy transition is placing new and unprecedented demands on Distribution System Operators (DSOs). Alongside upgrades to grid capacity, processes such as digitization, capacity optimization, and congestion management are becoming vital for delivering reliable services.
Power Grid Model is an open source project from Linux Foundation Energy and provides a calculation engine that is increasingly essential for DSOs. It offers a standards-based foundation enabling real-time power systems analysis, simulations of electrical power grids, and sophisticated what-if analysis. In addition, it enables in-depth studies and analysis of the electrical power grid’s behavior and performance. This comprehensive model incorporates essential factors such as power generation capacity, electrical losses, voltage levels, power flows, and system stability.
Power Grid Model is currently being applied in a wide variety of use cases, including grid planning, expansion, reliability, and congestion studies. It can also help in analyzing the impact of renewable energy integration, assessing the effects of disturbances or faults, and developing strategies for grid control and optimization.
What to expect
For the upcoming meetup we are organizing, we have an exciting lineup of activities planned:
-Insightful presentations covering two practical applications of the Power Grid Model.
-An update on the latest advancements in Power Grid -Model technology during the first and second quarters of 2024.
-An interactive brainstorming session to discuss and propose new feature requests.
-An opportunity to connect with fellow Power Grid Model enthusiasts and users.
Skybuffer SAM4U tool for SAP license adoption

Manage and optimize your license adoption and consumption with SAM4U, an SAP free customer software asset management tool.
SAM4U, an SAP complimentary software asset management tool for customers, delivers a detailed and well-structured overview of license inventory and usage with a user-friendly interface. We offer a hosted, cost-effective, and performance-optimized SAM4U setup in the Skybuffer Cloud environment. You retain ownership of the system and data, while we manage the ABAP 7.58 infrastructure, ensuring fixed Total Cost of Ownership (TCO) and exceptional services through the SAP Fiori interface.
Leveraging the Graph for Clinical Trials and Standards

Katja Glaß
OpenStudyBuilder Community Manager - Katja Glaß Consulting
Marius Conjeaud
Principal Consultant - Neo4j
Energy Efficient Video Encoding for Cloud and Edge Computing Instances

Energy Efficient Video Encoding for Cloud and Edge Computing Instances
Taking AI to the Next Level in Manufacturing.pdf

Read Taking AI to the Next Level in Manufacturing to gain insights on AI adoption in the manufacturing industry, such as:
1. How quickly AI is being implemented in manufacturing.
2. Which barriers stand in the way of AI adoption.
3. How data quality and governance form the backbone of AI.
4. Organizational processes and structures that may inhibit effective AI adoption.
6. Ideas and approaches to help build your organization's AI strategy.
Crafting Excellence: A Comprehensive Guide to iOS Mobile App Development Serv...

Crafting Excellence: A Comprehensive Guide to iOS Mobile App Development Serv...Pitangent Analytics & Technology Solutions Pvt. Ltd
Discover top-tier mobile app development services, offering innovative solutions for iOS and Android. Enhance your business with custom, user-friendly mobile applications.Apps Break Data

How information systems are built or acquired puts information, which is what they should be about, in a secondary place. Our language adapted accordingly, and we no longer talk about information systems but applications. Applications evolved in a way to break data into diverse fragments, tightly coupled with applications and expensive to integrate. The result is technical debt, which is re-paid by taking even bigger "loans", resulting in an ever-increasing technical debt. Software engineering and procurement practices work in sync with market forces to maintain this trend. This talk demonstrates how natural this situation is. The question is: can something be done to reverse the trend?
Main news related to the CCS TSI 2023 (2023/1695)

An English 🇬🇧 translation of a presentation to the speech I gave about the main changes brought by CCS TSI 2023 at the biggest Czech conference on Communications and signalling systems on Railways, which was held in Clarion Hotel Olomouc from 7th to 9th November 2023 (konferenceszt.cz). Attended by around 500 participants and 200 on-line followers.
The original Czech 🇨🇿 version of the presentation can be found here: https://www.slideshare.net/slideshow/hlavni-novinky-souvisejici-s-ccs-tsi-2023-2023-1695/269688092 .
The videorecording (in Czech) from the presentation is available here: https://youtu.be/WzjJWm4IyPk?si=SImb06tuXGb30BEH .
Choosing The Best AWS Service For Your Website + API.pptx

Have you ever been confused by the myriad of choices offered by AWS for hosting a website or an API?
Lambda, Elastic Beanstalk, Lightsail, Amplify, S3 (and more!) can each host websites + APIs. But which one should we choose?
Which one is cheapest? Which one is fastest? Which one will scale to meet our needs?
Join me in this session as we dive into each AWS hosting service to determine which one is best for your scenario and explain why!
Your One-Stop Shop for Python Success: Top 10 US Python Development Providers

Simplify your search for a reliable Python development partner! This list presents the top 10 trusted US providers offering comprehensive Python development services, ensuring your project's success from conception to completion.
Recently uploaded (20)
Dandelion Hashtable: beyond billion requests per second on a commodity server

Dandelion Hashtable: beyond billion requests per second on a commodity server
Principle of conventional tomography-Bibash Shahi ppt..pptx

Principle of conventional tomography-Bibash Shahi ppt..pptx
Nordic Marketo Engage User Group_June 13_ 2024.pptx

Nordic Marketo Engage User Group_June 13_ 2024.pptx
How to Interpret Trends in the Kalyan Rajdhani Mix Chart.pdf

How to Interpret Trends in the Kalyan Rajdhani Mix Chart.pdf
Northern Engraving | Nameplate Manufacturing Process - 2024

Northern Engraving | Nameplate Manufacturing Process - 2024
zkStudyClub - LatticeFold: A Lattice-based Folding Scheme and its Application...

zkStudyClub - LatticeFold: A Lattice-based Folding Scheme and its Application...
Leveraging the Graph for Clinical Trials and Standards

Leveraging the Graph for Clinical Trials and Standards
Energy Efficient Video Encoding for Cloud and Edge Computing Instances

Energy Efficient Video Encoding for Cloud and Edge Computing Instances
Crafting Excellence: A Comprehensive Guide to iOS Mobile App Development Serv...

Crafting Excellence: A Comprehensive Guide to iOS Mobile App Development Serv...
Choosing The Best AWS Service For Your Website + API.pptx

Choosing The Best AWS Service For Your Website + API.pptx
Your One-Stop Shop for Python Success: Top 10 US Python Development Providers

Your One-Stop Shop for Python Success: Top 10 US Python Development Providers
DIGIPASS for web powered by Intel
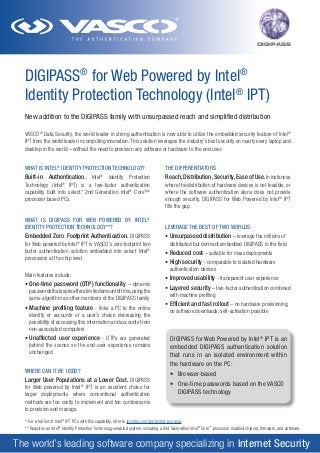
- 1. DIGIPASS DIGIPASS® for Web Powered by Intel® Identity Protection Technology (Intel® IPT) New addition to the DIGIPASS family with unsurpassed reach and simplified distribution VASCO® Data Security, the world leader in strong authentication is now able to utilize the embedded security feature of Intel® IPT from the world leader in computing innovation. This solution leverages the industry’s best security on nearly every laptop and desktop in the world – without the need to provision any software or hardware to the end-user. WHAT IS INTEL® IDENTITY PROTECTION TECHNOLOGY? THE DIFFERENTIATORS Built-in Authentication. Intel Reach, Distribution, Security, Ease of Use. In instances where the distribution of hardware devices is not feasible, or where the software authentication alone does not provide enough security, DIGIPASS for Web Powered by Intel® IPT fills the gap. Identity Protection Technology (Intel® IPT) is a two-factor authentication capability built into select* 2nd Generation Intel® Core™ processor based PCs. ® WHAT IS DIGIPASS FOR WEB POWERED BY INTEL® IDENTITY PROTECTION TECHNOLOGY**? Embedded Zero Footprint Authentication. DIGIPASS for Web powered by Intel IPT is VASCO’s zero footprint two factor authentication solution embedded into select Intel® processors at the chip level. ® Main features include: • One-time password (OTP) functionality – dynamic passwords that expire after a limited amount of time, using the same algorithm as other members of the DIGIPASS family • Machine profiling feature - links a PC to the online identity or accounts of a user’s choice decreasing the possibility of accessing this information and accounts from non-associated computers LEVERAGE THE BEST OF TWO WORLDS • Unsurpassed distribution – leverage the millions of distributed but dormant embedded DIGIPASS in the field • Reduced cost – suitable for mass deployments • High security - comparable to isolated hardware authentication devices • Improved usability - transparent user experience • Layered security – two-factor authentication combined with machine profiling • Efficient and fast rollout – no hardware provisioning, no software downloads, self-activation possible • Unaffected user experience - OTPs are generated behind the scenes so the end-user experience remains unchanged DIGIPASS for Web Powered by Intel ® IPT is an embedded DIGIPASS authentication solution that runs in an isolated environment within the hardware on the PC: WHERE CAN IT BE USED? • Browser-based Larger User Populations at a Lower Cost. DIGIPASS for Web powered by Intel® IPT is an excellent choice for larger deployments where conventional authentication methods are too costly to implement and too cumbersome to provision and manage. • One-time passwords based on the VASCO DIGIPASS technology * For a full list of Intel® IPT PCs with this capability, refer to ipt.intel.com/protected-pcs.aspx ** Requires an Intel® Identity Protection Technology-enabled system, including a 2nd Generation Intel® Core™ processor enabled chipset, firmware, and software. The world’s leading software company specializing in Internet Security
- 2. www.vasco.com DIGIPASS HOW IT WORKS Transparent end-user experience • The login process is as simple as using a static password yet with added two-factor authentication security via a Java applet of two-factor authentication via a Java applet Standard back-end installation • Much like with any other DIGIPASS family member, VASCO’s authentication platform VACMAN Controller or authentication software suite IDENTIKEY, handle the verification of the submitted one-time passwords on the back-end • Cloud-based authentication solution supported by VASCO’s DIGIPASS as a Service (DPS) platform is also possible Automated deployment and provisioning • The user can register his system via a web page without software installations or the need for human assistance • The DIGIPASS applet profiles the user’s system. The user chooses a password to use with his DIGIPASS Powered by Intel® Identity Protection Technology (Intel® IPT) login Intuitive use • After registration, the login page prompts the user for his username and “pre-registered” password • The DIGIPASS applet does the rest, generating a one-time password that is tied to that user on his particular machine(s) DIGIPASS for Web Powered by Intel® IPT Usage Models Online banking, e-brokerage, financial applications Social networking Online gaming e-Commerce Online subscriptions to magazines, databases Online and PoP email Insurance and health management SaaS applications Custom applications Consumer SMB Enterprise About VASCO VASCO designs, develops, markets and supports patented DIGIPASS®, DIGIPASS PLUS, VACMAN®, IDENTIKEY® and aXsGUARD® authentication products for the financial world, remote access, e-business and e-commerce. With tens of millions of products sold, VASCO has established itself as the world leader in Strong User Authentication for e-Banking and Enterprise Security for blue-chip corporations and governments worldwide. www.vasco.com I N T E R N AT I O N A L H Q ZURICH (Europe) phone: +41 43 555 3500 email: info_europe@vasco.com C O R P O R AT E H Q CHICAGO (North America) phone: +1 630 932 88 44 info-usa@vasco.com BRUSSELS (EUROPE) phone: +32.2.609.97.00 email: info-europe@vasco.com BOSTON (NORTH AMERICA) phone: +1.508.281.66.70 email: info-usa@vasco.com S Y D N E Y ( PA C I F I C ) phone: +61.2.8061.3700 email: info-australia@vasco.com SINGAPORE (ASIA) phone: +65.6323.0906 email: info-asia@vasco.com VACMAN ®, IDENTIKEY ®, aXs GUARD ®, and DIGIPASS ® are registered trademarks of Vasco Data Security. All trademarks or trade names are the property of their respective owners. VASCO reserves the right to make changes to specifications at any time and without notice. The information furnished by VASCO in this document is believed to be accurate and reliable. However, VASCO may not be held liable for its use, nor for infringement of patents or other rights of third parties resulting from its use. © 2011 VASCO. All rights reserved. LE101110 - v3b No system can provide absolute security under all conditions. Requires an Intel® IPT enabled system, including a 2nd generation Intel® Core™ processor, enabled chipset, firmware, and software. Available only on participating websites. Consult your system manufacturer. Intel® assumes no liability for lost or stolen data and/or systems or any resulting damages. For more information, visit ipt.intel.com www.vasco.com www.vasco.com
