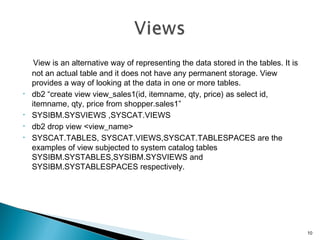
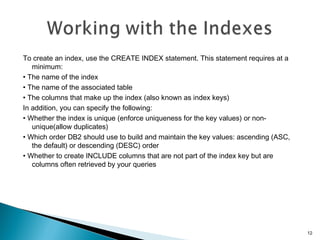
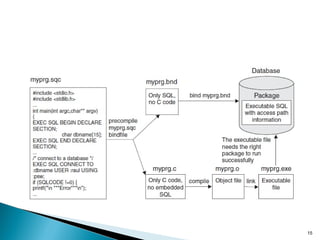
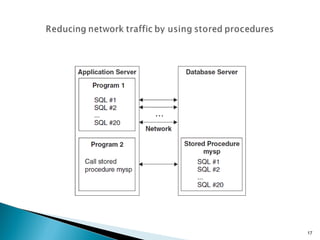
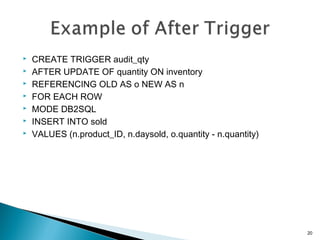
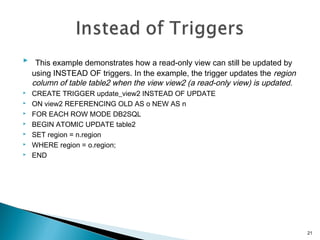
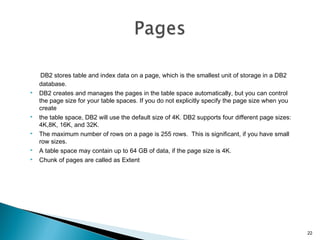
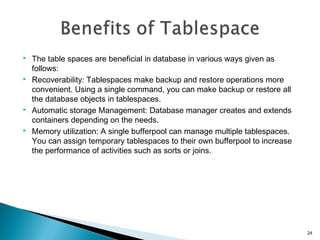
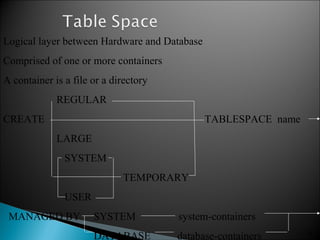
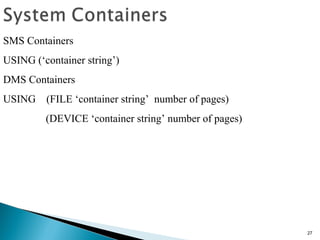
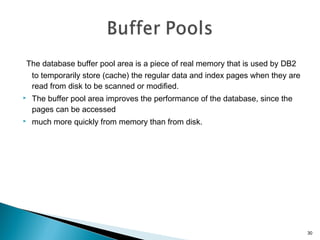
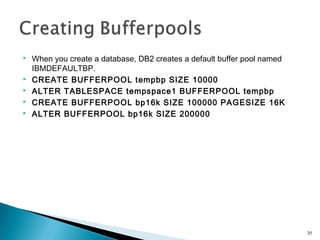
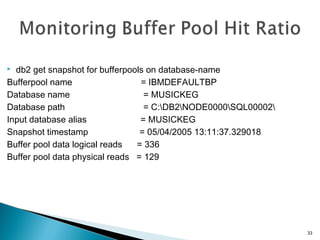
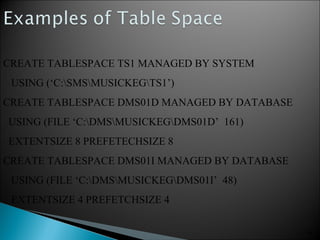
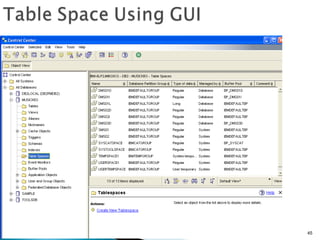
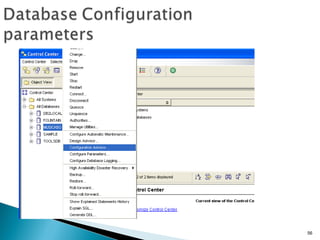
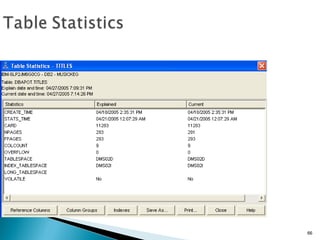
This document provides an overview of various database administration concepts in DB2 including tables, views, indexes, procedures, triggers, tablespaces, and buffer pools. It discusses how tables are used to store column and row data, and how system catalog tables track metadata. It also describes views, indexes, procedures, triggers, how they are used and created. The document outlines how tablespaces are used to logically group database objects and storage, and how buffer pools cache data pages in memory to improve performance.