Report
Share
Download to read offline
Recommended
Трећаци се приптемају за Нушићев вашар 2014.

Презентација која сведочи о напорима трећака, њихових родитеља и наставника да понуда Нушићевог вашара буде што богатија и у духу овогодишње теме "Нушић и српсканародна традиција".
Recommended
Трећаци се приптемају за Нушићев вашар 2014.

Презентација која сведочи о напорима трећака, њихових родитеља и наставника да понуда Нушићевог вашара буде што богатија и у духу овогодишње теме "Нушић и српсканародна традиција".
Mapa conceptual grupo 1

El ministro de salud de Chile, Jaime Mañalich, indicó que los resultados del censo de 2012 obligarán a modificar las metas sanitarias del país. Las patologías más prevalentes en Chile incluyen diabetes, hipertensión arterial y trastornos de la coagulación. El documento proporciona rangos de glucosa en sangre, presión arterial y niveles de INR para el manejo de estas condiciones.
Growth Hacking Masterclass: How to acquire users when you have zero marketing...

The document discusses various tactics for acquiring users with zero marketing budget, including becoming active on social media, optimizing website speed, blogging as a thought leader, using infographics, sharing on forums, A/B testing headlines and calls to action, building an engaged community, leveraging curiosity and contests, retargeting existing visitors, and using affiliates. It also outlines Neil Patel's three levels of the customer funnel - getting visitors, activating members, and retaining users - and provides examples of how to progress customers through each level.
AXELOS

Ashish Jain has achieved an ITIL® Foundation Certificate in IT Service Management effective from June 27, 2014 with certificate number 5086868.20289931. The certificate was issued by AXELOS and remains their property.
E017153342

This document discusses and compares three main data mining algorithms: association, classification, and clustering. Association rule learning is used to discover interesting relationships between variables in large databases. Classification involves predicting a target based on given data and finding relationships between predictor and target variables. Clustering groups a set of data into meaningful subclasses called clusters where objects within a cluster are more similar to each other than objects in other clusters. The document then discusses specific algorithms for each technique, including Apriori, FP-Growth, Naive Bayes, k-Nearest Neighbors (k-NN), and DBSCAN. It provides an overview of each algorithm and compares their approaches.
M017218088

This document proposes a new dual threshold median filter called Dual Threshold Median Filter (DTMF) for removing random valued impulse noise from digital images while preserving edges. The algorithm has two main stages: noise detection and noise removal. In the detection stage, the maximum and minimum pixel values in a 3x3 window are used to classify the central pixel as noisy or noise-free. Noisy pixels are then replaced in the removal stage using median filtering. The proposed filter is tested on standard images like Lena and Mandrill corrupted with 3-99% random valued impulse noise. Results show it achieves better peak signal-to-noise ratios and lower mean squared errors than previous methods, especially at high noise densities, indicating it effectively
H017215057

This document proposes a data usage monitoring and limiting system for shared wireless networks using only built-in Windows features. The system uses batch scripts and the Windows Task Scheduler to monitor individual data usage against user-set limits, blocking network access when limits are exceeded until the user modifies the limit. The system displays usage information through a command line interface, scheduling monitoring monthly by default. It was tested successfully on Windows 7 and aims to expand functionality for multiple profiles, platforms, and improved security while reducing human interaction.
E017242431

The document discusses the intensification of privacy invasion in cyberspace due to the widespread adoption of social media and mobile computing. It explores the different levels at which cyberspace users are exposed to privacy invasion, including personal information, communication activities, location data, and behavioral and biological data being collected without consent. While cyberspace enables new opportunities, advances in technology are also raising new threats to privacy, integrity, and trust. As interactions cut across borders without existing relationships of trust, protecting individual privacy in cyberspace is challenging and requires addressing social, legal and technical issues.
Presentacion

Este poema conmemora a alguien que falleció repentinamente y dejó un gran vacío en sus seres queridos. Describe que aunque la muerte es inesperada, la persona ahora descansa en paz en el cielo rodeada de ángeles, esperando reunirse con sus seres queridos nuevamente algún día. Recuerda con cariño a esta persona y asegura que siempre estará en sus corazones.
H017225058

This document proposes a Secure QoS-Oriented Distributed routing protocol (SQOD) for hybrid wireless networks. SQOD contains two parts: 1) A QoS-Oriented Distributed Routing Protocol (QOD) that reduces transmission delay and increases throughput through distributed resource scheduling. 2) An Enhanced Adaptive ACKnowledgment (EAACK) intrusion detection system that protects against attacks through a three-part ACK scheme involving standard ACKs, secure ACKs, and misbehavior reports with authentication. The document analyzes problems in existing routing protocols like false misbehavior reports, limited transmission power, and receiver collisions. It then describes the network and service models and provides details of the QOD and EAACK schemes
Clipping cnc 30062016 versão de impressão

Chuvas e frio prejudicam lavouras de café no sul de Minas Gerais e região de Mogiana em São Paulo, acelerando a maturação dos frutos e aumentando a queda e fermentação dos mesmos. Isso pode reduzir a qualidade e quantidade da safra. Exportação mundial de café cai 6,8% em maio ante o mesmo mês do ano passado. Colheita do arábica avança no Brasil, mas liquidez segue baixa, enquanto preço do conilon pode chegar a R$400 devido à pouca of
L017158389

The document describes a hybrid computational intelligence method for clustering sense-tagged Nepali documents. The method uses a combination of self-organizing map (SOM), particle swarm optimization (PSO), and k-means clustering. Documents are first represented as vectors using senses from WordNet rather than bag-of-words to address polysemy and synonymy issues. A hybrid SOM+PSO+k-means algorithm is then applied, where SOM is used to generate prototype vectors, PSO finds initial centroids, and k-means performs the final clustering of the prototypes into groups. The method is tested on sense-tagged Nepali text documents.
H017524854

The document summarizes a 1-level discrete wavelet transform (DWT) image watermarking algorithm for embedding watermarks into RGB cover images. The algorithm applies 1-level DWT to decompose the RGB cover image and watermark into frequency subbands. It then inserts the watermark into the low-frequency approximation subband of the cover image using alpha blending. The watermarked image achieves good quality with high peak signal-to-noise ratio. The extracted watermark matches the original with a normalized correlation value close to 1, showing the algorithm efficiently detects the watermark. The algorithm is imperceptible and robust against various attacks like noise and filtering.
Ocho utensilios infaltables para repostería

Si quieres crear los mejores pasteles de chocolate, tortas de cumpleaños o macarrones dulces, hay algunos utensilios importantes que debes tener y que mejorarán en gran medida el resultado de tus recetas.
More Related Content
Viewers also liked
Mapa conceptual grupo 1

El ministro de salud de Chile, Jaime Mañalich, indicó que los resultados del censo de 2012 obligarán a modificar las metas sanitarias del país. Las patologías más prevalentes en Chile incluyen diabetes, hipertensión arterial y trastornos de la coagulación. El documento proporciona rangos de glucosa en sangre, presión arterial y niveles de INR para el manejo de estas condiciones.
Growth Hacking Masterclass: How to acquire users when you have zero marketing...

The document discusses various tactics for acquiring users with zero marketing budget, including becoming active on social media, optimizing website speed, blogging as a thought leader, using infographics, sharing on forums, A/B testing headlines and calls to action, building an engaged community, leveraging curiosity and contests, retargeting existing visitors, and using affiliates. It also outlines Neil Patel's three levels of the customer funnel - getting visitors, activating members, and retaining users - and provides examples of how to progress customers through each level.
AXELOS

Ashish Jain has achieved an ITIL® Foundation Certificate in IT Service Management effective from June 27, 2014 with certificate number 5086868.20289931. The certificate was issued by AXELOS and remains their property.
E017153342

This document discusses and compares three main data mining algorithms: association, classification, and clustering. Association rule learning is used to discover interesting relationships between variables in large databases. Classification involves predicting a target based on given data and finding relationships between predictor and target variables. Clustering groups a set of data into meaningful subclasses called clusters where objects within a cluster are more similar to each other than objects in other clusters. The document then discusses specific algorithms for each technique, including Apriori, FP-Growth, Naive Bayes, k-Nearest Neighbors (k-NN), and DBSCAN. It provides an overview of each algorithm and compares their approaches.
M017218088

This document proposes a new dual threshold median filter called Dual Threshold Median Filter (DTMF) for removing random valued impulse noise from digital images while preserving edges. The algorithm has two main stages: noise detection and noise removal. In the detection stage, the maximum and minimum pixel values in a 3x3 window are used to classify the central pixel as noisy or noise-free. Noisy pixels are then replaced in the removal stage using median filtering. The proposed filter is tested on standard images like Lena and Mandrill corrupted with 3-99% random valued impulse noise. Results show it achieves better peak signal-to-noise ratios and lower mean squared errors than previous methods, especially at high noise densities, indicating it effectively
H017215057

This document proposes a data usage monitoring and limiting system for shared wireless networks using only built-in Windows features. The system uses batch scripts and the Windows Task Scheduler to monitor individual data usage against user-set limits, blocking network access when limits are exceeded until the user modifies the limit. The system displays usage information through a command line interface, scheduling monitoring monthly by default. It was tested successfully on Windows 7 and aims to expand functionality for multiple profiles, platforms, and improved security while reducing human interaction.
E017242431

The document discusses the intensification of privacy invasion in cyberspace due to the widespread adoption of social media and mobile computing. It explores the different levels at which cyberspace users are exposed to privacy invasion, including personal information, communication activities, location data, and behavioral and biological data being collected without consent. While cyberspace enables new opportunities, advances in technology are also raising new threats to privacy, integrity, and trust. As interactions cut across borders without existing relationships of trust, protecting individual privacy in cyberspace is challenging and requires addressing social, legal and technical issues.
Presentacion

Este poema conmemora a alguien que falleció repentinamente y dejó un gran vacío en sus seres queridos. Describe que aunque la muerte es inesperada, la persona ahora descansa en paz en el cielo rodeada de ángeles, esperando reunirse con sus seres queridos nuevamente algún día. Recuerda con cariño a esta persona y asegura que siempre estará en sus corazones.
H017225058

This document proposes a Secure QoS-Oriented Distributed routing protocol (SQOD) for hybrid wireless networks. SQOD contains two parts: 1) A QoS-Oriented Distributed Routing Protocol (QOD) that reduces transmission delay and increases throughput through distributed resource scheduling. 2) An Enhanced Adaptive ACKnowledgment (EAACK) intrusion detection system that protects against attacks through a three-part ACK scheme involving standard ACKs, secure ACKs, and misbehavior reports with authentication. The document analyzes problems in existing routing protocols like false misbehavior reports, limited transmission power, and receiver collisions. It then describes the network and service models and provides details of the QOD and EAACK schemes
Clipping cnc 30062016 versão de impressão

Chuvas e frio prejudicam lavouras de café no sul de Minas Gerais e região de Mogiana em São Paulo, acelerando a maturação dos frutos e aumentando a queda e fermentação dos mesmos. Isso pode reduzir a qualidade e quantidade da safra. Exportação mundial de café cai 6,8% em maio ante o mesmo mês do ano passado. Colheita do arábica avança no Brasil, mas liquidez segue baixa, enquanto preço do conilon pode chegar a R$400 devido à pouca of
L017158389

The document describes a hybrid computational intelligence method for clustering sense-tagged Nepali documents. The method uses a combination of self-organizing map (SOM), particle swarm optimization (PSO), and k-means clustering. Documents are first represented as vectors using senses from WordNet rather than bag-of-words to address polysemy and synonymy issues. A hybrid SOM+PSO+k-means algorithm is then applied, where SOM is used to generate prototype vectors, PSO finds initial centroids, and k-means performs the final clustering of the prototypes into groups. The method is tested on sense-tagged Nepali text documents.
H017524854

The document summarizes a 1-level discrete wavelet transform (DWT) image watermarking algorithm for embedding watermarks into RGB cover images. The algorithm applies 1-level DWT to decompose the RGB cover image and watermark into frequency subbands. It then inserts the watermark into the low-frequency approximation subband of the cover image using alpha blending. The watermarked image achieves good quality with high peak signal-to-noise ratio. The extracted watermark matches the original with a normalized correlation value close to 1, showing the algorithm efficiently detects the watermark. The algorithm is imperceptible and robust against various attacks like noise and filtering.
Ocho utensilios infaltables para repostería

Si quieres crear los mejores pasteles de chocolate, tortas de cumpleaños o macarrones dulces, hay algunos utensilios importantes que debes tener y que mejorarán en gran medida el resultado de tus recetas.
Viewers also liked (15)
Growth Hacking Masterclass: How to acquire users when you have zero marketing...

Growth Hacking Masterclass: How to acquire users when you have zero marketing...
More from ivana969
More from ivana969 (9)
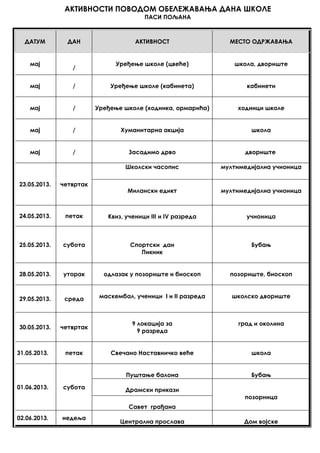
Dan škole p.poljana
- 1. АКТИВНОСТИ ПОВОДОМ ОБЕЛЕЖАВАЊА ДАНА ШКОЛЕ ПАСИ ПОЉАНА ДАТУМ ДАН АКТИВНОСТ МЕСТО ОДРЖАВАЊА мај / Уређење школе (цвеће) школа, двориште мај / Уређење школе (кабинета) кабинети мај / Уређење школе (ходника, ормарића) ходници школе мај / Хуманитарна акција школа мај / Засадимо дрво двориште 23.05.2013. четвртак Школски часопис мултимедијална учионица Милански едикт мултимедијална учионица 24.05.2013. петак Квиз, ученици III и IV разреда учионица 25.05.2013. субота Спортски дан Пикник Бубањ 28.05.2013. уторак одлазак у позориште и биоскоп позориште, биоскоп 29.05.2013. среда маскембал, ученици I и II разреда школско двориште 30.05.2013. четвртак 9 локација за 9 разреда град и околина 31.05.2013. петак Свечано Наставничко веће школа 01.06.2013. субота Пуштање балона Бубањ Драмски прикази позорница Савет грађана 02.06.2013. недеља Централна прослава Дом војске