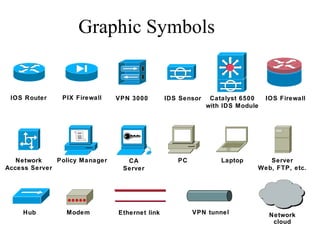
Cisco symboler
•Download as PPT, PDF•
1 like•335 views
This diagram shows a network architecture with various security devices protecting resources. It includes routers, firewalls, VPNs, intrusion detection sensors, switches, and other network devices connected through ethernet links and VPN tunnels. The devices are managing access to resources like servers, PCs, laptops and web/FTP applications.
Report
Share
Report
Share
Recommended
Layer 7: Cloud Security For The Public Sector

Presentation by Layer 7 Public Sector CTO Adam Vincent on Cloud risks, threats and security for the public sector.
Bridging the Enterprise and the Cloud from Layer 7

Layer 7 Technologies CTO Presentation from 2010 Gartner AADI on Cloud Integration and Single Sign-on Using Cloud Gateways / Brokers.
Physical Security & IT

Competing and converging network and building access control technologies are redefining rule-based network security processes. HID and RSA are competing standards for controlling access to buildings and networks, while biometrics, pin numbers and passwords are converging to create the standard for validating a person�s identity. Learn about the physical and logical security convergence impact to IT departments.
Physical Security & IT

Competing and converging network and building access control technologies are redefining rule-based network security processes. HID and RSA are competing standards for controlling access to buildings and networks, while biometrics, pin numbers and passwords are converging to create the standard for validating a persons identity. Security professionals define the impact of the convergence of physical and logical security on IT departments.
Block Armour securing critical IoT infrastructure and 5g networks

Smart, connected devices are already an integral part of our lives, in business and at home. And, with the rollout of 5G, this is expected to scale multi-fold. IoT and 5G will open up previously closed systems to remote access & control, and existing security solutions are simply unable to keep pace, scale up and address the security challenges facing this new always-on, fast-evolving interconnected world.
The IoT Armour solution by BlockArmour is explicitly designed to secure connected devices, integrated IoT systems, and associated 5G communication networks. The solution is powered by Software Defined Perimeter (SDP) architecture & Blockchain technology. SDP architecture renders core systems and IoT gateways invisible to attackers; while customized agents along with private Blockchain technology deliver a new breed of digital identity and access control for all connected devices.
Protect your guest wifi - NOW

Cisco Umbrella is the easiest and fastest cloud security platform for provisioning secure and compliant guest Wi-Fi. Our
solution’s simplicity and performance is the reason Fortune 50 retailers, top universities, and some of the largest hospitals in
the US trust Umbrella to protect their Wi-Fi.
Recommended
Layer 7: Cloud Security For The Public Sector

Presentation by Layer 7 Public Sector CTO Adam Vincent on Cloud risks, threats and security for the public sector.
Bridging the Enterprise and the Cloud from Layer 7

Layer 7 Technologies CTO Presentation from 2010 Gartner AADI on Cloud Integration and Single Sign-on Using Cloud Gateways / Brokers.
Physical Security & IT

Competing and converging network and building access control technologies are redefining rule-based network security processes. HID and RSA are competing standards for controlling access to buildings and networks, while biometrics, pin numbers and passwords are converging to create the standard for validating a person�s identity. Learn about the physical and logical security convergence impact to IT departments.
Physical Security & IT

Competing and converging network and building access control technologies are redefining rule-based network security processes. HID and RSA are competing standards for controlling access to buildings and networks, while biometrics, pin numbers and passwords are converging to create the standard for validating a persons identity. Security professionals define the impact of the convergence of physical and logical security on IT departments.
Block Armour securing critical IoT infrastructure and 5g networks

Smart, connected devices are already an integral part of our lives, in business and at home. And, with the rollout of 5G, this is expected to scale multi-fold. IoT and 5G will open up previously closed systems to remote access & control, and existing security solutions are simply unable to keep pace, scale up and address the security challenges facing this new always-on, fast-evolving interconnected world.
The IoT Armour solution by BlockArmour is explicitly designed to secure connected devices, integrated IoT systems, and associated 5G communication networks. The solution is powered by Software Defined Perimeter (SDP) architecture & Blockchain technology. SDP architecture renders core systems and IoT gateways invisible to attackers; while customized agents along with private Blockchain technology deliver a new breed of digital identity and access control for all connected devices.
Protect your guest wifi - NOW

Cisco Umbrella is the easiest and fastest cloud security platform for provisioning secure and compliant guest Wi-Fi. Our
solution’s simplicity and performance is the reason Fortune 50 retailers, top universities, and some of the largest hospitals in
the US trust Umbrella to protect their Wi-Fi.
More Related Content
More from roberthpedersen
More from roberthpedersen (8)
Cisco symboler
- 1. Graphic Symbols IOS Router PIX Firewall VPN 3000 IDS Sensor Catalyst 6500 with IDS Module IOS Firewall Network Access Server Policy Manager CA Server PC Laptop Server Web, FTP, etc. Modem Ethernet link VPN tunnelHub Network cloud