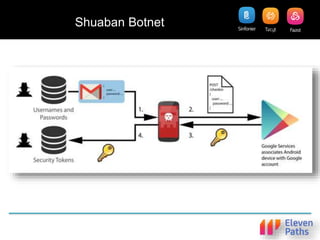
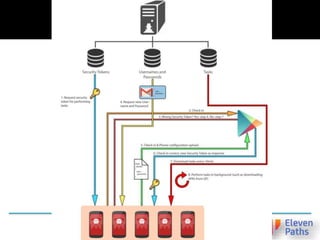
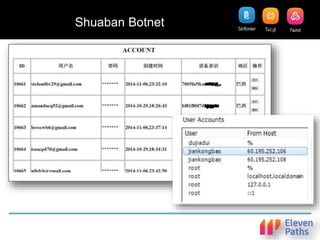
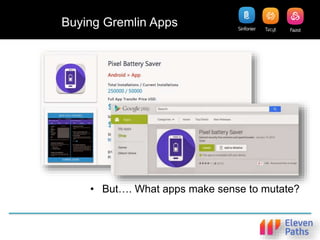
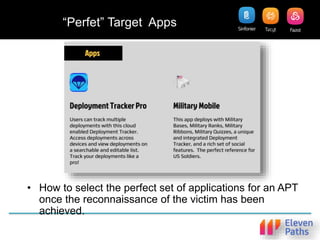
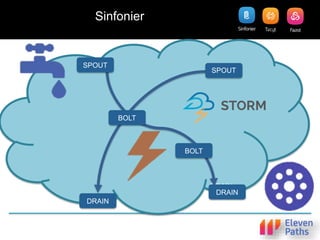
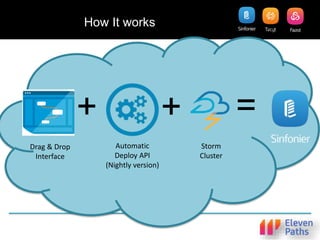
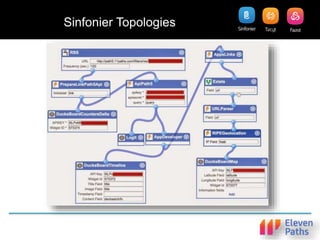
The document discusses the challenges of cybercrime in Android apps, particularly on platforms like Google Play, and presents OSINT (Open Source Intelligence) as a method to analyze and mitigate these threats. It emphasizes the importance of correlating data to detect anomalies rather than solely focusing on detection, and introduces the Tacyt platform for real-time processing and analysis of app data. The document concludes that while cybercrime in apps is significant, tools like Tacyt and Sinfonier can aid in discovering anomalies and integrating various data sources for enhanced security measures.