Report
Share
Download to read offline
Recommended
Mads Mikkelsen - danefæområdet - status og udvikling

Mads Mikkelsen - danefæområdet - status og udviklingAssociation of Danish Museums / Organisationen Danske Museer
Forhistorisk arkæologiFood Safety Webcast: Allergen Management

In this hour-long webcast we explored best practices that contribute to creating a foodservice environment that’s responsive to allergens and helps meet consumers evolving dietary needs without compromising on quality or service. Members of the foodservice community came with their questions and our panelists did their best to provide practical answers based on their years of experience.
Secure Linear Transformation Based Cryptosystem using Dynamic Byte Substitution

Many classical cryptosystems are developed based on simple substitution. Hybrid cryptosystem using byte substitution and variable length sub key groups is a simple nonlinear algorithm but the cryptanalyst can find the length of each sub key group because the byte substitution is static and if the modulo prime number is small then byte substitution is limited to first few rows of S-box. In this paper an attempt is made to introduce the nonlinearity to the linear transformation based cryptosystem using dynamic byte substitution over GF (28). The secret value is added to the index value to shift the substitution to a new secret location dynamically. This adds extra security in addition to non-linearity, confusion and diffusion. The performance evaluation of the method is also studied and presented.
Recommended
Mads Mikkelsen - danefæområdet - status og udvikling

Mads Mikkelsen - danefæområdet - status og udviklingAssociation of Danish Museums / Organisationen Danske Museer
Forhistorisk arkæologiFood Safety Webcast: Allergen Management

In this hour-long webcast we explored best practices that contribute to creating a foodservice environment that’s responsive to allergens and helps meet consumers evolving dietary needs without compromising on quality or service. Members of the foodservice community came with their questions and our panelists did their best to provide practical answers based on their years of experience.
Secure Linear Transformation Based Cryptosystem using Dynamic Byte Substitution

Many classical cryptosystems are developed based on simple substitution. Hybrid cryptosystem using byte substitution and variable length sub key groups is a simple nonlinear algorithm but the cryptanalyst can find the length of each sub key group because the byte substitution is static and if the modulo prime number is small then byte substitution is limited to first few rows of S-box. In this paper an attempt is made to introduce the nonlinearity to the linear transformation based cryptosystem using dynamic byte substitution over GF (28). The secret value is added to the index value to shift the substitution to a new secret location dynamically. This adds extra security in addition to non-linearity, confusion and diffusion. The performance evaluation of the method is also studied and presented.
Lotte Sparrevohn - en rituel palisade fra bronzealder

Lotte Sparrevohn - en rituel palisade fra bronzealderAssociation of Danish Museums / Organisationen Danske Museer
Forhistorisk arkæologiCustomer Finder Marketing - Marketing for Veterinarians PowerPoint

Marketing for VeterinariansPowerPoint
Custom Decals

Best Sign Company A sign promotion has bloom to become one of the best Edmonton's sign and decal experts. Coroplast signs,vehicle wraps, specialty graphics & etc.
Identificacin de riesgos y seguridad industrial.

Identificacion de riesgos y seguridad industrial, esto con el fin de dar a conocer los tipos de riesgos que se deben tener en cuenta al momento de trabajar en una empres o multinacional, conociendo tambien los parametros de seguridad para el bienestar fisico e integro del trabajador
More Related Content
Viewers also liked
Lotte Sparrevohn - en rituel palisade fra bronzealder

Lotte Sparrevohn - en rituel palisade fra bronzealderAssociation of Danish Museums / Organisationen Danske Museer
Forhistorisk arkæologiCustomer Finder Marketing - Marketing for Veterinarians PowerPoint

Marketing for VeterinariansPowerPoint
Custom Decals

Best Sign Company A sign promotion has bloom to become one of the best Edmonton's sign and decal experts. Coroplast signs,vehicle wraps, specialty graphics & etc.
Identificacin de riesgos y seguridad industrial.

Identificacion de riesgos y seguridad industrial, esto con el fin de dar a conocer los tipos de riesgos que se deben tener en cuenta al momento de trabajar en una empres o multinacional, conociendo tambien los parametros de seguridad para el bienestar fisico e integro del trabajador
Viewers also liked (17)
Lotte Sparrevohn - en rituel palisade fra bronzealder

Lotte Sparrevohn - en rituel palisade fra bronzealder
Customer Finder Marketing - Marketing for Veterinarians PowerPoint

Customer Finder Marketing - Marketing for Veterinarians PowerPoint
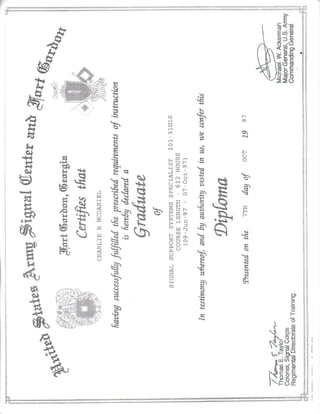
Certificate of graduation from Hilton reservations & Customer Care

Certificate of graduation from Hilton reservations & Customer Care