Academic
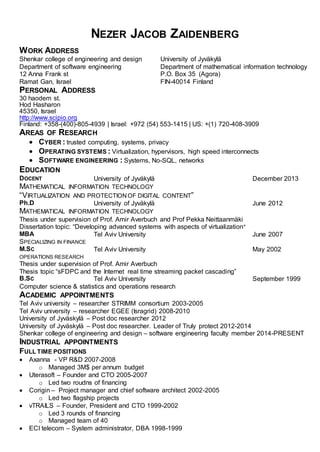
- 1. NEZER JACOB ZAIDENBERG WORK ADDRESS Shenkar college of engineering and design Department of software engineering 12 Anna Frank st Ramat Gan, Israel University of Jyväkylä Department of mathematical information technology P.O. Box 35 (Agora) FIN-40014 Finland PERSONAL ADDRESS 30 haodem st. Hod Hasharon 45350, Israel http://www.scipio.org Finland: +358-(400)-805-4939 | Israel: +972 (54) 553-1415 | US: +(1) 720-408-3909 AREAS OF RESEARCH CYBER : trusted computing, systems, privacy OPERATING SYSTEMS : Virtualization, hypervisors, high speed interconnects SOFTWARE ENGINEERING : Systems, No-SQL, networks EDUCATION DOCENT University of Jyväkylä December 2013 MATHEMATICAL INFORMATION TECHNOLOGY “VIRTUALIZATION AND PROTECTIONOF DIGITAL CONTENT” Ph.D University of Jyväkylä June 2012 MATHEMATICAL INFORMATION TECHNOLOGY Thesis under supervision of Prof. Amir Averbuch and Prof Pekka Neittaanmäki Dissertation topic: “Developing advanced systems with aspects of virtualization” MBA Tel Aviv University June 2007 SPECIALIZING IN FINANCE M.SC Tel Aviv University May 2002 OPERATIONS RESEARCH Thesis under supervision of Prof. Amir Averbuch Thesis topic “sFDPC and the Internet real time streaming packet cascading” B.SC Tel Aviv University September 1999 Computer science & statistics and operations research ACADEMIC APPOINTMENTS Tel Aviv university – researcher STRIMM consortium 2003-2005 Tel Aviv university – researcher EGEE (Isragrid) 2008-2010 University of Jyväskylä – Post doc researcher 2012 University of Jyväskylä – Post doc researcher. Leader of Truly protect 2012-2014 Shenkar college of engineering and design – software engineering faculty member 2014-PRESENT INDUSTRIAL APPOINTMENTS FULL TIME POSITIONS Axanna - VP R&D 2007-2008 o Managed 3M$ per annum budget Uterasoft – Founder and CTO 2005-2007 o Led two roudns of financing Corigin – Project manager and chief software architect 2002-2005 o Led two flagship projects vTRAILS – Founder, President and CTO 1999-2002 o Led 3 rounds of financing o Managed team of 40 ECI telecom – System administrator, DBA 1998-1999
- 2. CONSULTANT Videocells (Herzelia, Israel); redesigned and led the company through product and infrastructure transformations Friendly Technologies (Ramat Gan, Israel) Faced product design and performance challenges. Infowrap/Blusky (Israel/Italy) Supervised technology transfer to Italian buyer. Expay-Global (Israel/Bulgaria) Solution infrastructure and R&D focus, security, PCI authorization. NDS/Cisco (Jerusalem, Israel); provided training on Mac architecture internals; generated repeated business for the implementation of three products. Designed PS3 port of PC-Show product. SintecMedia (Jerusalem, Israel); Technology advisor for the CTO; Software architecture for STB. Data mining. Kardan VC (Tel Aviv, Israel); headed technology due-diligence for investment. EDF Energy (Plymouth, UK); UK’s #1 utility provider. Transfer from mainframe to open systems. MCE-systems User space driver development Diligent/IBM Fibrechannel driver development under linux Perion Mac (OSX) internals Finjan Windows to Solaris porting Axxana research on brocade switches RESEARCH GRANTS AND PERSONAL AWARDS 1. 2003-5 STRIMM consurtium grant for peer-2-peer streaming (based on masters thesis) w/ Prof Amir Averbuch (TAU) 2. 20012-14 TEKES TUTLI grant for TRULY-PROTECT 1.25M€ 3. Ellen and arrturi Nyyssosen foundation grant (18,600€) 4. TrulyProtect business plan won technology award CCSU 2013 PROFESSIONAL SOCIETIES AND ACTIVITIES IEEE (SINCE 2011) a. PROCTOR AND “COACH” OF SCHOOL TEAM FOR IEEEXTREME 2014 COMPETITION SCS (SINCE 2011) FINNISH MATHEMATICAL SOCIETY – SINCE 2012 ACADEMIC COURSES SECURE SYSTEM DESIGN (M.SC LEVEL) – JYU 2013-14 OPERATING SYSTEM SECURITY 1 (DOMAINS MANAGEMENT- M.SC LEVEL) - JYU 2013-2014 OPERATING SYSTEM SECURITY 2 (TRUSTED COMPUTING - M.SC LEVEL) – JYU 2011-12, 2013-2014 – 2 TIMES (ONCE AS “TRUSTED COMPUTING”) MASTER DEGREE - CYBER WORKSHOP (M.SC LEVEL) – MTA 2014-2015 BACHELOR DEGREE - LINUX WORKSHOP MTA 2010-2011, 2009-2010 TAU 2009-2010 – TOTAL 3 TIMES MASTER SEMINAR (M.SC LEVEL) – JYU 2013-2014 FIBRECHANNEL (M.SC LEVEL) – JYU 2011-2012 DATABASES – SHNKAR 2012-2013 SECURE PROGRAMMING – SHENKAR 2014-2015 CYBER SEMINAR - SHENKAR 2014-2015 CYBER SYSTEMS - SHENKAR 2014-2015 SYSTEM PROGRAMMING UNIX MTA (2012-2013, 2013-2014, 2014-2015) SHENKAR (2013-2014, 2014- 2015) TOTAL 6 TIMES SECURE PROGRAMMING - SEMINAR HAKIBUTZIM (2009-2010) ADVANCED TOPICS IN OPERATING SYSTEMS (M.SC / B.SC) TAU (2009-2010, 2010-2011) MTA (2009- 2010, 2010-2011, 2011-2012, 2012-2013, 2013-2014) TOTAL 7 TIMES REAL TIME OPERATING SYSTEMS – RUPPIN (2009-2010) OPERATING SYSTEMS – MTA (2009-2010, 2010-2011) TAU (2009-2010, 2010-2011) RUPPIN (2009- 2010), SEMINAR HAKIBUTZIM (2009-2010) – TOTAL 10 TIMES CALCULUS 1 – MTA (2008-2009) COMPUTER ORGANIZATION AND ASSEMBLER (OPEN UNIVERSITY 1998-1999)
- 3. INDUSTRIAL COURSES INTRODUCTION TO MAC/MAC PROGRAMMING – NDS - 30 HOURS 2009 UNIX SYSTEM PROGRAMMING – NDS - 30 HOURS -2009 MAC INTERNALS – NDS - 192 HOURS - 2009
- 4. GRADUATE STUDENTS SUPERVISION AND CO-SUPERVISION DOCTORAL STUDENTS Present Limor Gavish @ University of jyväskylä Michael Kiperberg @ University of jyväskylä (to graduate 2015) Amit Resh @ University of jyväskylä Amir Hussain Rajnama @ University of jyväskylä Tiina Kovanen @ University of jyväskylä MASTER STUDENTS Present Eviatar Khen @ Tel Aviv University (w/ Prof. Amir Averbuch) Alexei Sragovitch @ Tel Aviv Jaffa-academic college (w/ Dr. Carmi Merimovitch) Asaf Algawi @ Tel Aviv Jaffa-academic college (w/ Dr. Carmi Merimovitch) Evyatar Tamir @ Tel Aviv Jaffa-academic college (w/ Dr. Carmi Merimovitch) Avihu Efrat @ University of jyväskylä Tomer Shani @ University of jyväskylä David Bauminger @ University of jyväskylä M.Sc students thesis under my supervision / co supervision Past Limor Gavish – Thesis submitted @ Tel Aviv university (2012 w/ Prof. Amir Averbuch) Thesis: http://www.scipio.org/students/LimorGavish/book.pdf Michael Kiperberg – Thesis submitted @ Tel Aviv University (2012, Cum laude w/ Prof. Amir Averbuch) Thesis: http://www.cs.tau.ac.il/thesis/thesis/Kiperberg.Michael-MSc.thesis.pdf Tomer Margalit – Thesis submitted @ Tel Aviv University (2013 w/ Prof. Amir Averbuch) Thesis: http://www.scipio.org/students/TomerMargalit/amirror3.pdf Tamir Erez – Thesis submitted @ Tel Aviv Jaffa-academic collage (2013 w/ Dr. Carmi Merimovich) Thesis: http://www.scipio.org/students/TamirErez/G2GMsc.pdf Amit Resh @ University of jyväskylä (2013) Asaf David @ Tel Aviv Jaffa-academic college (2014 w/ Dr. Carmi Merimovich) Yuval Meir @ Tel Aviv University (2014 w/ Prof. Amir Averbuch) PUBLICATIONS
- 5. 5 most important publications 1. "Truly Protect: An Efficient VM-Based Software Protection” 2. “An Efficient VM-Based Software Protection” 3. “A low bitrate approach to replication of block devices and virtual machines” 4. “LgDb 2.0: A code coverage and profiler architecture for the Linux kernel” 5. Business plan:Truly protect - winner of CCSU 2013 technology award Book chapters 1. Trusted computing. to appear at CYBER SECURITY ANALYTICS Vol. 3 Cybersecurity technologies (w/ Pekka Neittaanmäki) 2. Game console hacks to appear at CYBER SECURITY ANALYTICS Vol. 3 Cybersecurity technologies 3. Timing and side channel attacks to appear at CYBER SECURITY ANALYTICS Vol. 3 Cybersecurity technologies (w/ Amit Resh) 4. Trusted computing Projects at JYU to appear at CYBER SECURITY ANALYTICS Vol. 3 Cybersecurity technologies (TrulyProtect w/ Michael Kiperberg, Amit Resh, Pekka Neittaanmäki. TrulyTrusted w/ Tiina Kovanen, Evyatar Tamir and Pekka Neittaanmäki) Journal papers Trusted computing publication 1. Averbuch A., Kiperberg M., Zaidenberg N. "Truly Protect : An Efficient VM-Based Software Protection” IEEE System journal September 2013 http://ieeexplore.ieee.org/xpl/articleDetails.jsp?arnumber=6553406 2. M Kiperberg M. and Zaidenberg N. “Efficient Remote Authentication” to appear in Journal of information warfare October 2013 Peer-2-peer streaming 1. Averbuch, A., Roditi, Y., & Zaidenberg, N. (2013). PPPC — peer-2-peer streaming and algorithm for creating spanning trees for peer-2-peer networks. In S. Repin, T. Tiihonen, & T. Tuovinen (Eds.), Numerical Methods for Differential Equations, Optimization, and Technological Problems. Dedicated to Professor P. Neittaanmäki on His 60th Birthday (pp. 363-377). Computational Methods in Applied Sciences (27). Berlin: Springer. doi:10.1007/978-94-007-5288-7_20 Trusted computing publication 1. A. Averbuch, M. Kiperberg, N. Zaidenberg (2011) "An Efficient VM-Based Software Protection” IEEE NSS 2011 http://www.cs.tau.ac.il/~kiperber/truly.pdf 2. A. Resh & N. Zaidenberg (2013) "Can keys be hidden inside the CPU on modern Windows host” ECIW 2013 pages 231-235 3. N. Zaidenberg & A. David (2013) Truly protect video delivery ECIW 2013 pages 405-407 4. M. Kiperberg & N. Zaidenberg (2013) "Efficient Remote Authentication" ECIW 2013 pages 144-148 5. E. Tamir, N. Zaidenberg & P Neittaanmäki (2014) “TrulyTrusted Operating System Environment” to appear ICCSM 2014 6. A. Algawi, P. Neittaanmaki, N. Zaidenberg & T Parisinos (2014) “In kernel implementation of RSA routines” to appear ICCSM 2014 7. A. David & N. Zaidenberg (2014) “Maintaining streaming video DRM” to appear ICCSM 2014 Operating systems improvements
- 6. 1. Averbuch A., T. Margalit, N. Zaidenberg N. & Khen E. (2011) "A low bitrate approach to replication of block devices and virtual machines" IEEE NAS 2011 "http://www.computer.org/csdl/proceedings/nas/2011/4509/00/4509a180-abs.html" 2. Khen E., Zaidenberg N. & Averbuch A. (2011) Using virtualization for online kernel profiling, code coverage and instrumentation SPECTS 2011 http://ieeexplore.ieee.org/xpls/abs_all.jsp?arnumber=5984854&tag=1 3. Khen E., Zaidenberg N., Averbuch A. & Fermocovich E. (2013) "LgDb 2.0: A code coverage and profiler architecture for the Linux kernel" SPECTS 13 4. Erez T. & Zaidenberg N. (2013) "Grid2Go – A web based internet of things grid computing engine requiring only a browser. ICI 2013 Systems 1. Averbuch, A., Roditi, Y., & Zaidenberg, N. (2011). An algorithm for creating a spanning graph for peer-2-peer internet broadcast. In S. Repin, T. Tiihonen, & T. Tuovinen (Eds.), Proceedings of CAO2011: ECCOMAS Thematic Conference on Computational Analysis and Optimization : University of Jyväskylä, June 9-11, 2011 (pp. 73-76). Reports of the Department of Mathematical Information Technology. Series A, Collections (1/2011). [Jyväskylä]: University of Jyväskylä 2. Zaidenberg N. (2014) HoneyGuard - Opensource VSaaS system Mathematical genetics (population dynamics) and modeling 1. Zaidenberg N. & Eshel I. (2012) “Zaidenberg’s learning model for the evolution of altruistically cooperation” ECCOMAS 2012 (4826) Other Publications Ph.D dissertation : “Developing advanced systems with aspects of virtualization” Zaidenberg N. University of Jyvaskyla June 2012 M.Sc thesis : “sFDPC and the Internet real time streaming packet cascading” Zaidenberg N. Tel Aviv University September 2011 “Truly-Protect: Business plan” K. Choi, I. Legmpelos, T. Palosnick, M. Polo-Guardia, D. Zaidenberg and N. Zaidenberg. Winner of CCSU 2013 Technology award. Posters 1. "Asynchronous replication solution for Unix, replicating storage and QEMU and Lguest VMs". Amir Averbuch, Eviatar Khen, Tomer Margalit and Nezer Zaidenberg SYSTOR 2011 2. "LgDb" Amir Averbuch, Eviatar Khen and Nezer Zaidenberg SYSTOR 2011 3. Truly-Protect: An efficient VM-Based copy protection. Amir Averbuch, Michael Kiperberg and Nezer Zaidenerg SYSTOR 2012 http://pjd-1.ccs.neu.edu/~pjd/systor12/posters/systor12-poster4.pdf 4. A method for hiding decryption keys in copy protected software Amit Resh and Nezer Zaidenberg SYSTOR 2013 5. Grid2Go: A Web Based Internet of Things GRID Computing Engine. Tamir Erez and Nezer Zaidneberg SYSTOR 2013 6. TrulyProtect 2.0 and attacks on TrulyProtect 1.0 Amit Resh, Nezer Zaidenberg, Limor Gavish, Michael Kiperberg and Eviatar Khen ECIW 2013 http://academic- conferences.org/eciw/eciw2013/eciw13-proceedings.htm Patents in the field of trusted computing 1. "Virtual Machine Software Protection" N.Zaidenberg and M. Kiperberg 2. "SYSTEM AND METHODS FOR CPU CACHE PINNING OF A COMPUTING DEVICE" N.
- 7. Zaidenberg M. Kiperberg and A. Resh 3. “Remote Authentication Application” N Zaidenberg M. Kiperberg and A. Resh Contributions to Linux Kernel 1. In kernel RSA implementation 2. Minor contributions to several components including lguest parallel port driver etc.