Image-to-Code Converter 31July2023.pptx
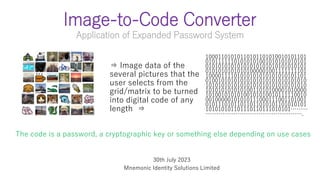
- 1. Image-to-Code Converter Application of Expanded Password System 10001101010110101101010010101101 01011111101010101001010101010101 01010101010101010101010101010101 01010101010101000001001111111101 10000111101010101010101010101101 01001010101010101010101010101010 10101010101010101010101010101010 10101010101010011010100001010000 10100101010100101010010111110010 00100000101010111000111001101001 01011101011011011010101101010101 101010101101110110111010101……… ……………………………………………. ⇒ Image data of the several pictures that the user selects from the grid/matrix to be turned into digital code of any length ⇒ The code is a password, a cryptographic key or something else depending on use cases 30th July 2023 Mnemonic Identity Solutions Limited
- 2. Processing of Image Data Image data of a picture that the user picks up will be hashed by the likes of Sha256 Sha-hashed data of the selected several pictures will be put together and hashed by the likes of Argon2id The Argon2id-hashed data will be outputted as the code to be used as a password, a crypto key, a master-password or something else depending on use cases. With unique salts added, a number of derivative codes can be automatically generated from the first code in a single process * The 2023 version
- 3. On-the-fly Regeneration The code thus generated will be eliminated when the program is shut down. It no longer exists anywhere in the universe. When the code is required next, the user will only need to select the same pictures - The same code will be regenerated. Leak-proof – Should a hacker break into the program, they would not find any secret data they may want other than login credential invincibly hashed by Shar256 and Argon2id. *2023 version
- 4. Entropy What ‘several images among dozens’ has to cope with is not the automated brute force attacks on the server, but visual-manual attacks on the display. A million trials, say, 20 bits, would be no more than a joke against automated brute force attacks. However, it makes a pretty tall wall against visual-manual attacks, particularly when the positions of images are randomly changed. On the other hand, the entropy of the code that faces brute force attacks can easily be 160bits, 320 bits or even megabits, gigabits, terabits by linking thumbnail images to massive unique dataset. The burden on the user will still be the same - locating several pictures.
- 5. Applications of Converter (A)Password generation for device/app login (B) Master-password generation for password manager (B’) Master-password generation for crypto-key manager (C) Crypto-key generation for data encryption software
- 6. Mnemonic Guard Software of password generation for Windows login A 32-digit password generated by our Converter will be handed to the login interface under Windows’ account management system – There is a single-user version and a multi-user version. There should be no problem to get it incorporated into Active Directory. A derivative of the multi-user version is used by Japanese Army for the personnel responsible for encrypted data exchange on field communications vehicles since 2013.
- 7. Mnemonic Gateways Software of master-password generation for password manager with no password vault When logged-in to the software by picking up the registered images, a unique secret credential will be generated/re- generated from the image data on the fly. Then, select the account requiring a password from the account list and the software will enable us to send out the user ID and the unique password generated/re-generated from the abovesaid secret credential to the login page of the target account.
- 8. Cryptomnemo Software of crypto-key generation for a combined data encryption software When logged-in to the software by picking up the registered images, a cryptographic key will be generated/re-generated from the image data on the fly. Then, specify the files or folders that require encryption or decryption – The specified data will be encrypted or decrypted. When the program is shut down, the crypto-key will be eliminated. Next time the program is started and the registered images selected, the same crypto key will be regenerated on the fly. Combination with QRC’s eAES will be the optimal for security-sensitive areas.
- 9. Thanks for your time
