Adversary Path Analysis 1.pptx
•
1 like•117 views
Adversary Path Analysis 1
Report
Share
Report
Share
Recommended
Recommended
Call Girls In Saket Delhi 9953056974 (Low Price) Escort Service Saket Delhi

Call Girls In Saket Delhi 9953056974 (Low Price) Escort Service Saket Delhi9953056974 Low Rate Call Girls In Saket, Delhi NCR
More Related Content
Similar to Adversary Path Analysis 1.pptx
Similar to Adversary Path Analysis 1.pptx (20)
The Security Vulnerability Assessment Process & Best Practices

The Security Vulnerability Assessment Process & Best Practices
Protecting the Portals - Strengthening Data Security.pdf

Protecting the Portals - Strengthening Data Security.pdf
Preparing for future attacks. Solution Brief: Implementing the right securit...

Preparing for future attacks. Solution Brief: Implementing the right securit...
Safety training: Risk Assessment & Job Safety Analysis

Safety training: Risk Assessment & Job Safety Analysis
Recently uploaded
Call Girls In Saket Delhi 9953056974 (Low Price) Escort Service Saket Delhi

Call Girls In Saket Delhi 9953056974 (Low Price) Escort Service Saket Delhi9953056974 Low Rate Call Girls In Saket, Delhi NCR
Recently uploaded (20)
Call Girls In Saket Delhi 9953056974 (Low Price) Escort Service Saket Delhi

Call Girls In Saket Delhi 9953056974 (Low Price) Escort Service Saket Delhi
Best VIP Call Girl Noida Sector 48 Call Me: 8700611579

Best VIP Call Girl Noida Sector 48 Call Me: 8700611579
Call Girls In {Laxmi Nagar Delhi} 9667938988 Indian Russian High Profile Girl...

Call Girls In {Laxmi Nagar Delhi} 9667938988 Indian Russian High Profile Girl...
Digha ❤CALL GIRL 89101*77447 ❤CALL GIRLS IN Digha ESCORT SERVICE❤CALL GIRL

Digha ❤CALL GIRL 89101*77447 ❤CALL GIRLS IN Digha ESCORT SERVICE❤CALL GIRL
Call Girls In {{Green Park Delhi}}9667938988 Indian Russian High Profile Esco...

Call Girls In {{Green Park Delhi}}9667938988 Indian Russian High Profile Esco...
Best VIP Call Girls Noida Sector 23 Call Me: 8700611579

Best VIP Call Girls Noida Sector 23 Call Me: 8700611579
Call Girls In {Laxmi Nagar Delhi} 9667938988 Indian Russian High Profile Girl...

Call Girls In {Laxmi Nagar Delhi} 9667938988 Indian Russian High Profile Girl...
Low Rate Russian Call Girls In Lajpat Nagar ➡️ 7836950116 Call Girls Service ...

Low Rate Russian Call Girls In Lajpat Nagar ➡️ 7836950116 Call Girls Service ...
Best VIP Call Girls Noida Sector 24 Call Me: 8700611579

Best VIP Call Girls Noida Sector 24 Call Me: 8700611579
Malda ❤CALL GIRL 89101*77447 ❤CALL GIRLS IN Malda ESCORT SERVICE❤CALL GIRL

Malda ❤CALL GIRL 89101*77447 ❤CALL GIRLS IN Malda ESCORT SERVICE❤CALL GIRL
Hot Vip Call Girls Service In Sector 149,9818099198 Young Female Escorts Serv...

Hot Vip Call Girls Service In Sector 149,9818099198 Young Female Escorts Serv...
+91-9310611641 Russian Call Girls In New Delhi Independent Russian Call Girls...

+91-9310611641 Russian Call Girls In New Delhi Independent Russian Call Girls...
Jamshedpur ❤CALL GIRL 89101*77447 ❤CALL GIRLS IN Jamshedpur ESCORT SERVICE❤CA...

Jamshedpur ❤CALL GIRL 89101*77447 ❤CALL GIRLS IN Jamshedpur ESCORT SERVICE❤CA...
9891550660 Call Girls In Noida Sector 62 Short 1500 Night 6000

9891550660 Call Girls In Noida Sector 62 Short 1500 Night 6000
Adversary Path Analysis 1.pptx
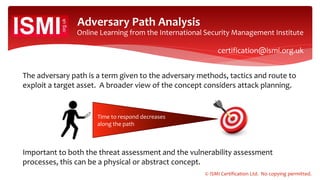
- 1. Online Learning from the International Security Management Institute The adversary path is a term given to the adversary methods, tactics and route to exploit a target asset. A broader view of the concept considers attack planning. Adversary Path Analysis Important to both the threat assessment and the vulnerability assessment processes, this can be a physical or abstract concept. Time to respond decreases along the path © ISMI Certification Ltd. No copying permitted. certification@ismi.org.uk
- 2. Online Learning from the International Security Management Institute Barriers along the adversary path will delay the adversary, and co-located detection systems are intended to activate a response to the action. Adversary Path Analysis The action requires assessment before the remaining time along the adversary path is less than the available response time. This is known as the critical detection point. barriers to delay plus detection and assessment certification@ismi.org.uk © ISMI Certification Ltd. No copying permitted.
- 3. Online Learning from the International Security Management Institute The Unit 5 Textbook (Security Design) of the ISMI® Security Management Body of Knowledge tells us that detection should take place at the earliest point along the adversary path, ideally in the planning stages by means of intelligence. Adversary Path Analysis Consider, for example, terrorism. Can detection be considered satisfactory once the adversary is armed and en route to the target? Conception and planning © ISMI Certification Ltd. No copying permitted. certification@ismi.org.uk
- 4. Online Learning from the International Security Management Institute Adversary Path Analysis Under ideal circumstances, detection should take place: a. At the point where the adversary reaches the target asset. b. Midway along the adversary path at the critical detection point. c. At the earliest point along the adversary path. d. In the adversary planning stage by means of intelligence/surveillance. Not bad, but not the best answer © ISMI Certification Ltd. No copying permitted. certification@ismi.org.uk