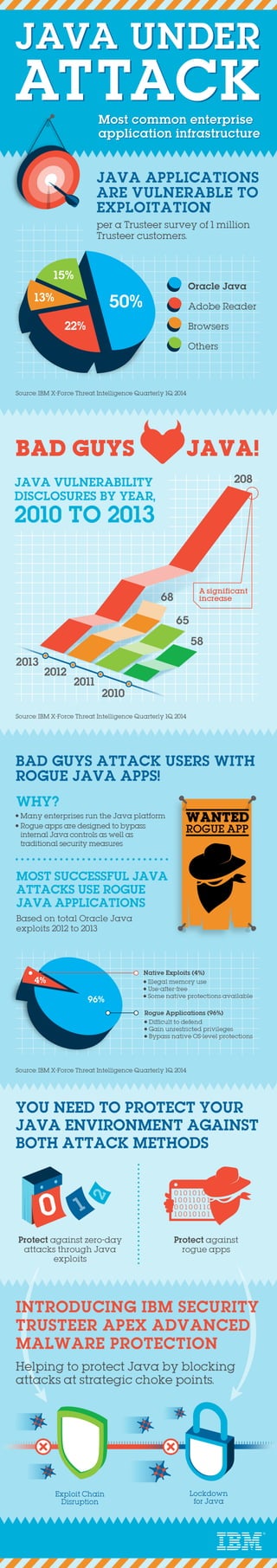
INFOGRAPHIC: Java under Attack
Java applications can expose organizations to significant risk as it is one of the most targeted software platform. According to research conducted by IBM Security Trusteer researchers and IBM X-Force, 50% of exploits target Java vulnerabilities. Of these, 96% are malicious Java applications that manage to break Java’s internal security mechanisms and gain elevated privileges. Because these operate maliciously inside the Java virtual machine, these attacks may easily bypass OS-level controls which may be blind to such manipulations. A comprehensive threat protection approach must consider the potential implications and perils of this popular platform. Considering Java and how to best protect against cybercriminals targeting Java vulnerabilities or creating rogue Java apps needs to be among security professionals top of mind when choosing a protection system. For more information, please visit http://ibm.co/158OTLn.