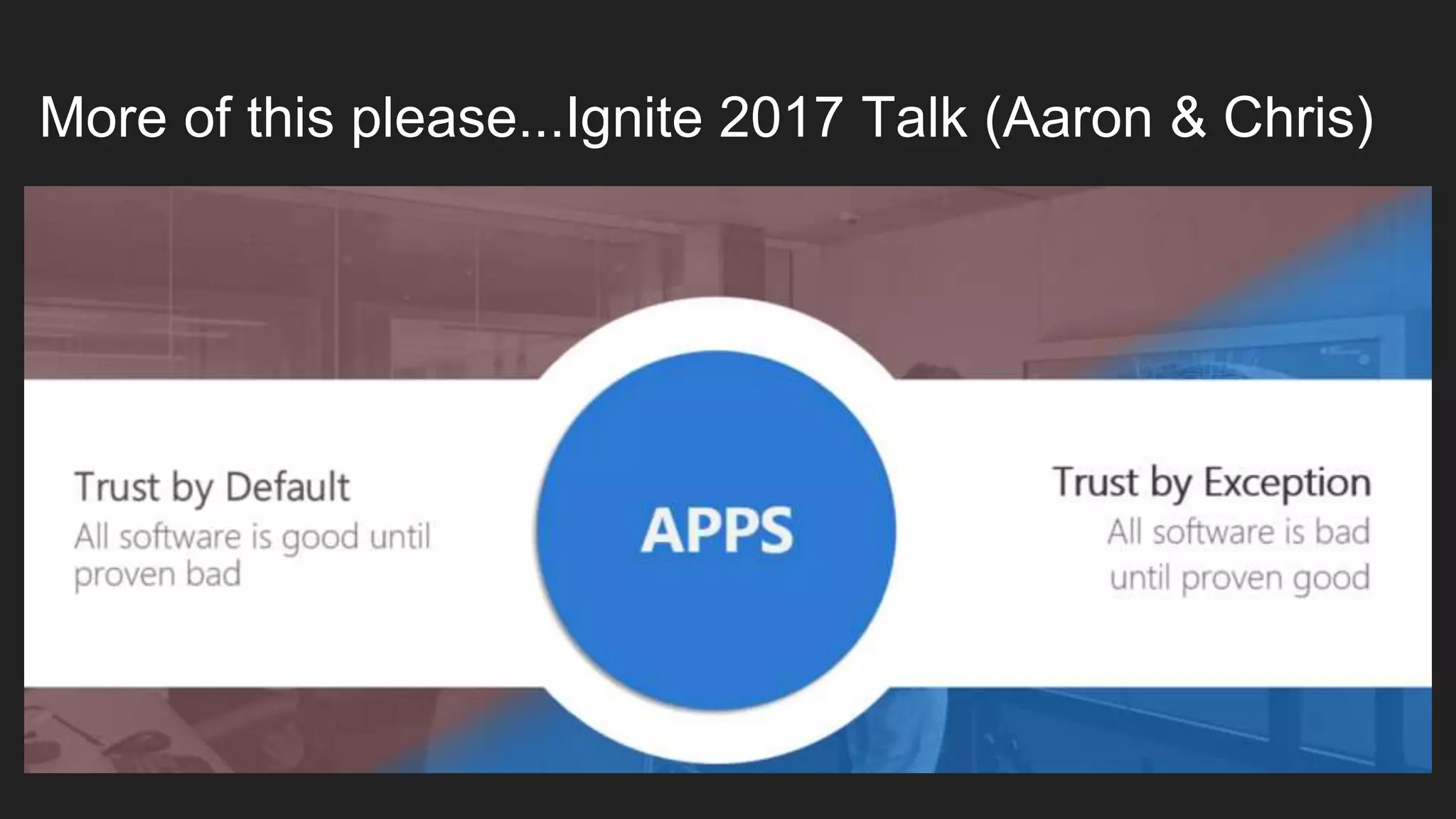
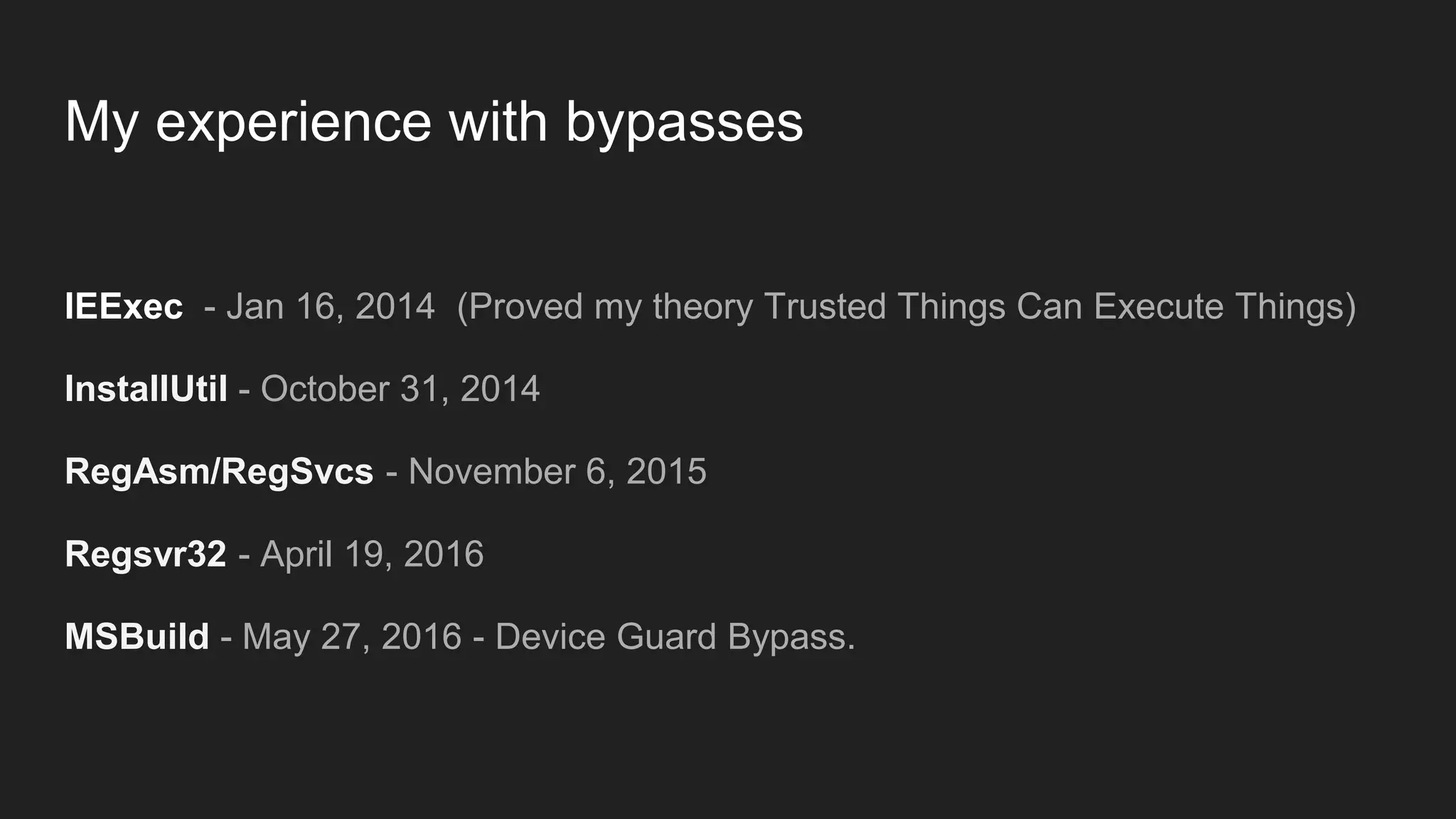
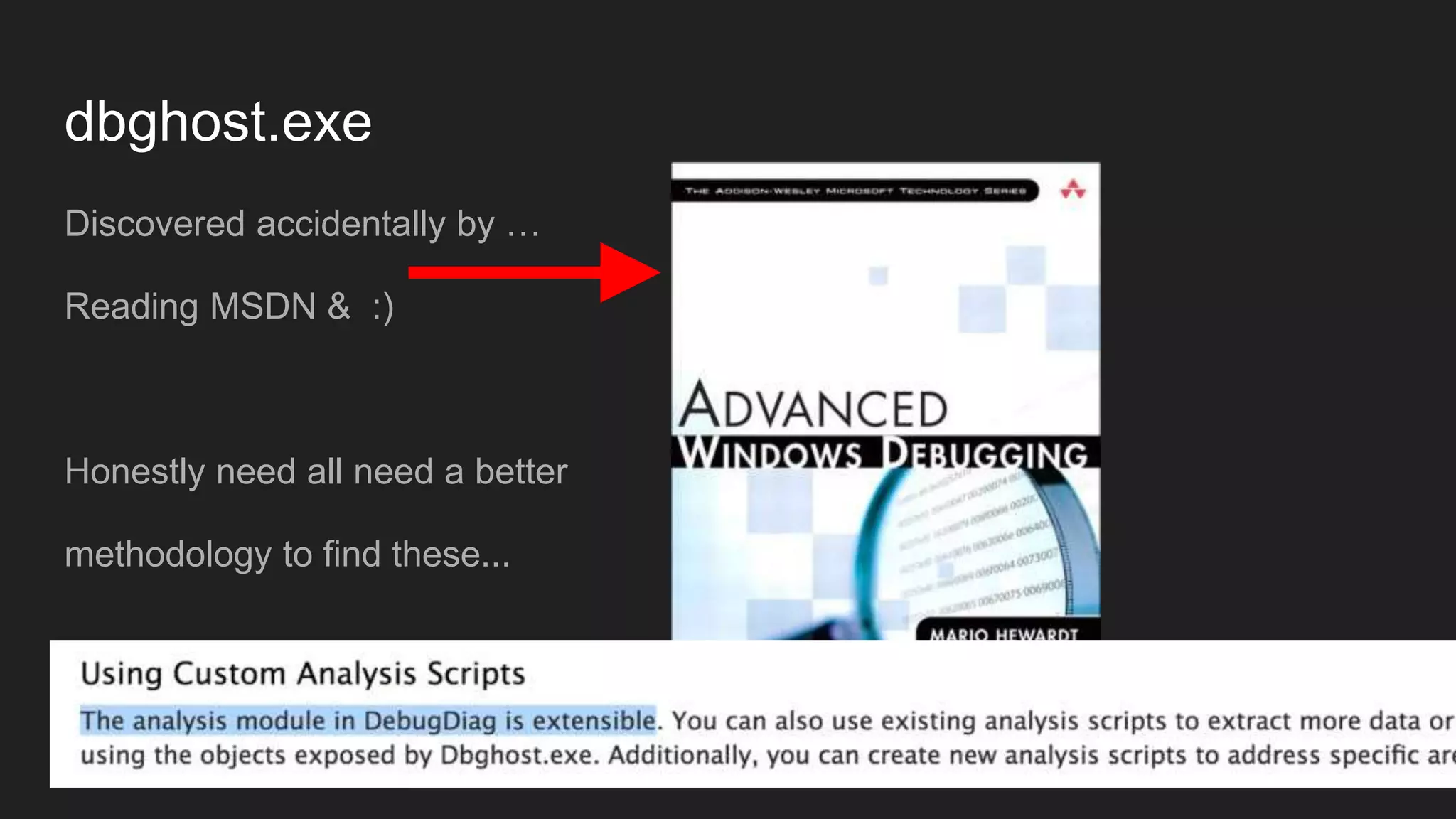
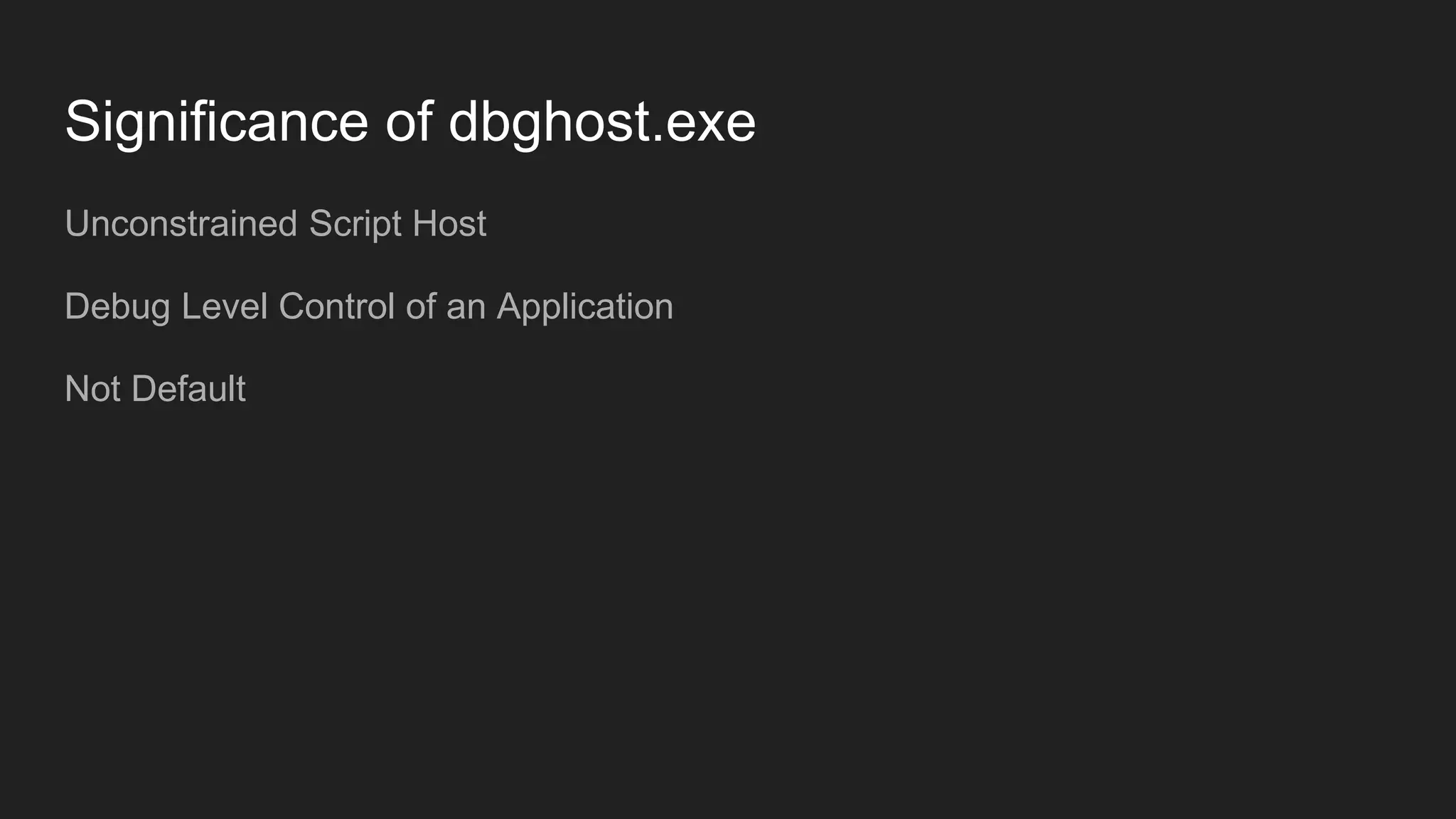
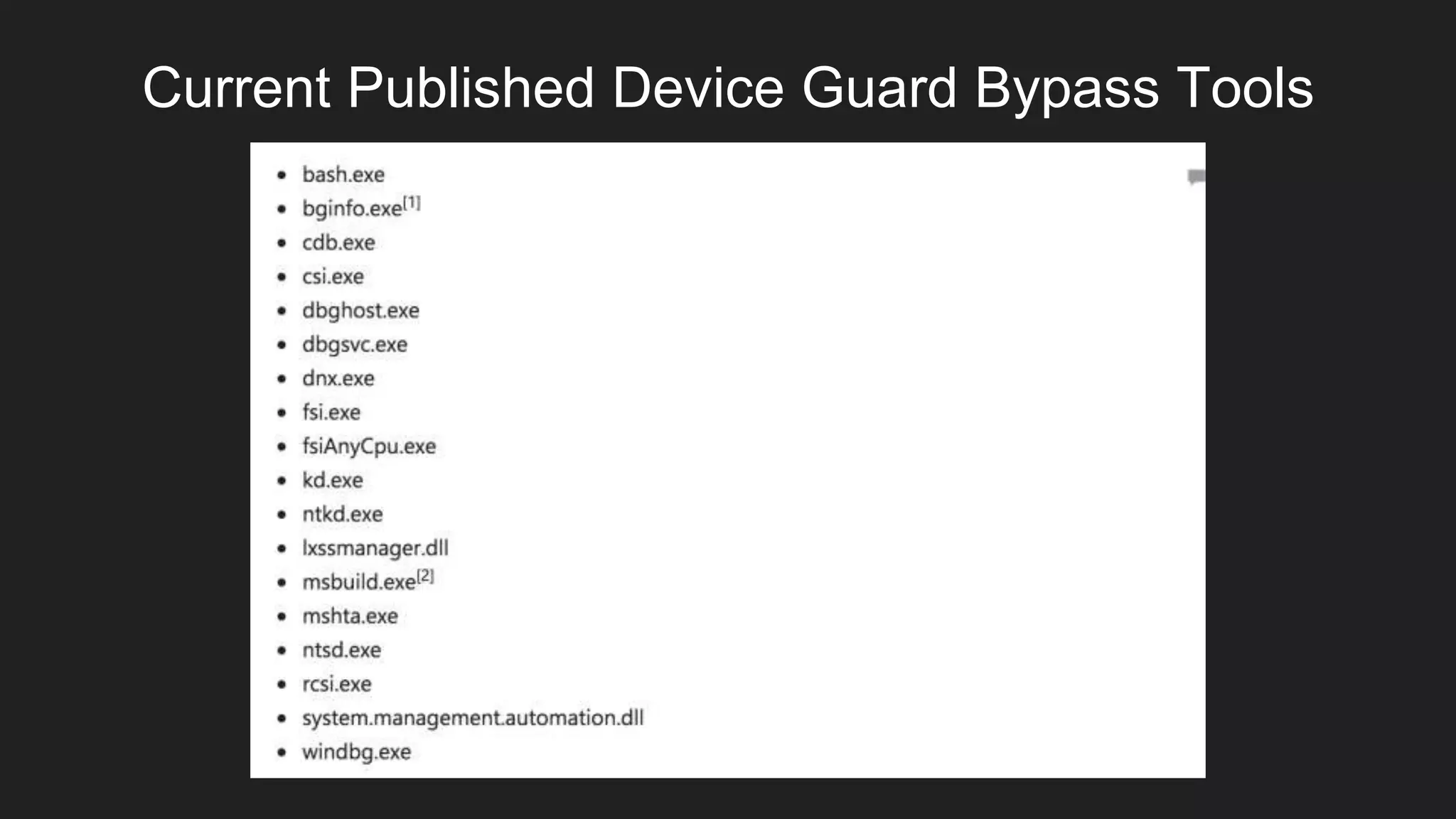
The document discusses the challenges and effectiveness of whitelisting in cybersecurity, highlighting its potential successes and the complexities surrounding its deployment and bypass mechanisms. It emphasizes the need for better methodologies, visibility, and trust in signed tools, while also acknowledging the limitations and evolving tactics used by attackers. Ultimately, the author encourages the adoption of whitelisting as a standard practice to combat opportunistic attacks.