Embed presentation







![Md Sohail Ahmad [email_address] Thank You! The Global Leader in Wireless Security Solutions www.airtightnetworks.com](https://image.slidesharecdn.com/wips-100225040655-phpapp02/75/Wireless-Intrusion-Prevention-Systems-or-WIPS-25-2048.jpg)
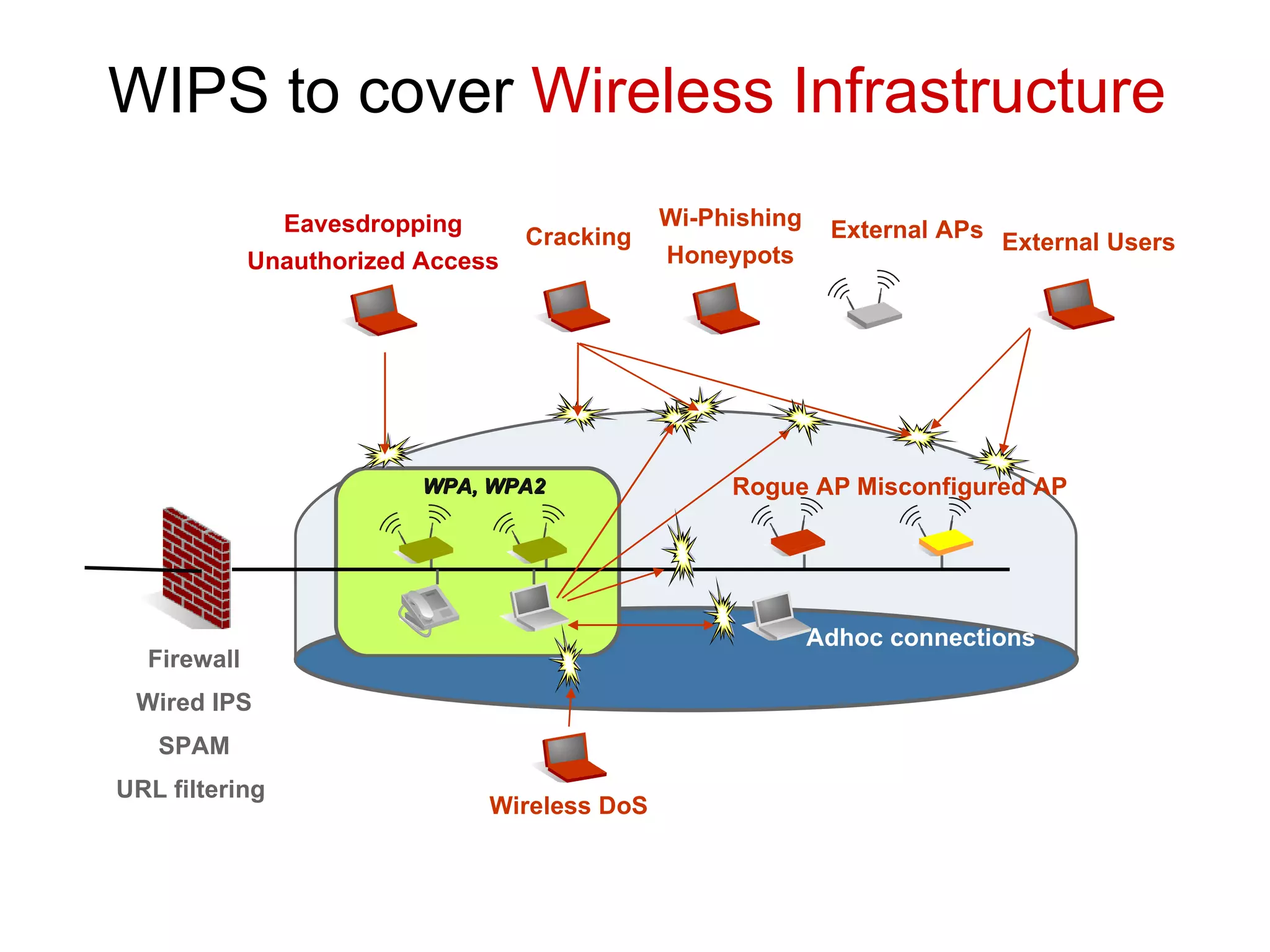
The document discusses Wireless Intrusion Prevention Systems (WIPS) as essential for protecting wireless infrastructures from security threats such as eavesdropping and unauthorized access. It emphasizes the limitations of traditional firewalls in safeguarding against wireless vulnerabilities and outlines various threats and methods to mitigate them. Recommendations include using WPA/WPA2 security measures and implementing WIPS to detect and block misuse of Wi-Fi networks.







![Md Sohail Ahmad [email_address] Thank You! The Global Leader in Wireless Security Solutions www.airtightnetworks.com](https://image.slidesharecdn.com/wips-100225040655-phpapp02/75/Wireless-Intrusion-Prevention-Systems-or-WIPS-25-2048.jpg)
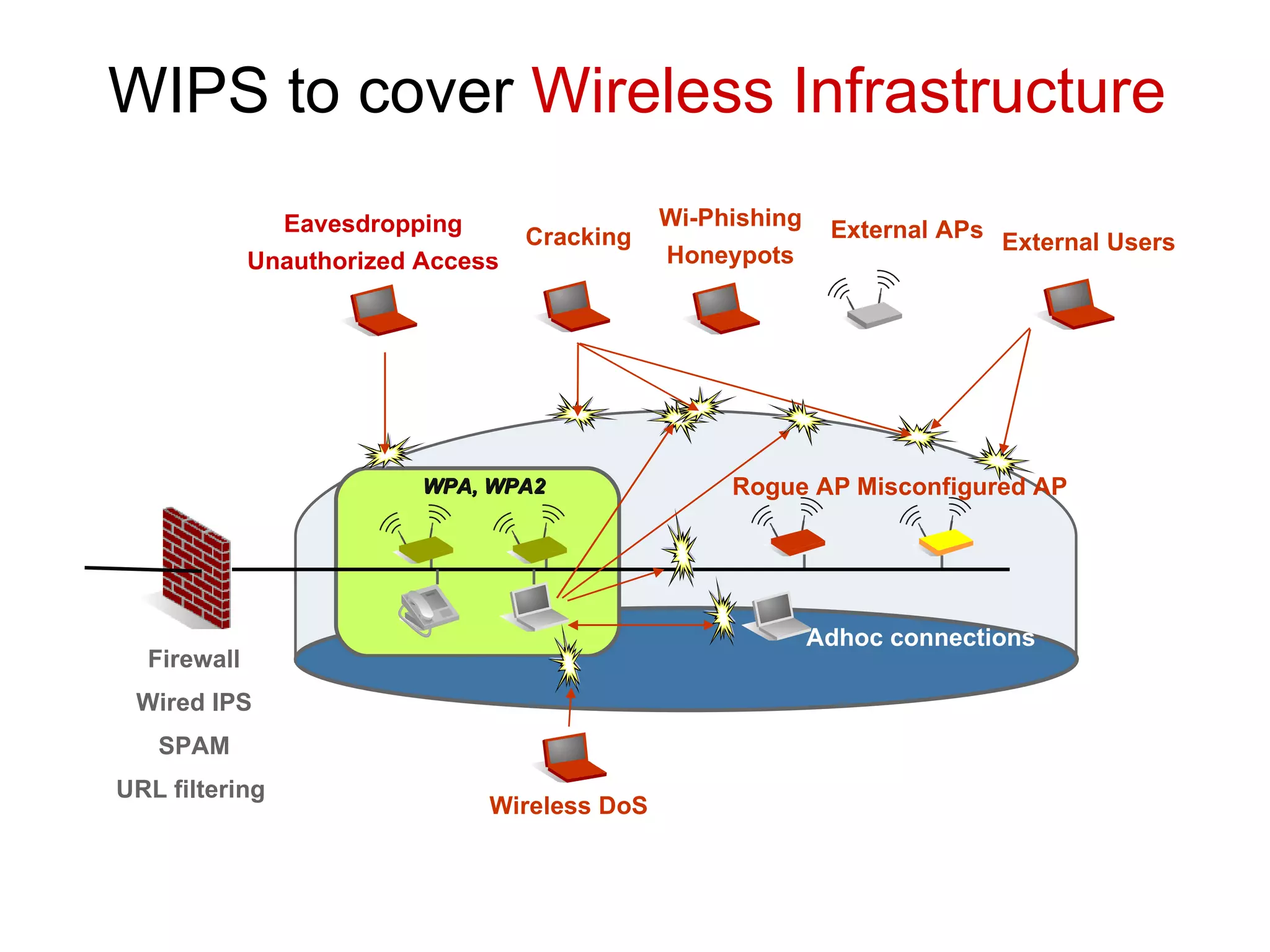
W I PS stands for Wireless Intrusion Prevention Systems, providing security cover to wireless infrastructure.
Security involves the protection of assets, specifically in Information Technology.
Security measures include locking, watching, monitoring, and utilizing training, processes, and technology.
Security involves the protection of assets, specifically in Information Technology.
Security measures include locking, watching, monitoring, and utilizing training, processes, and technology.
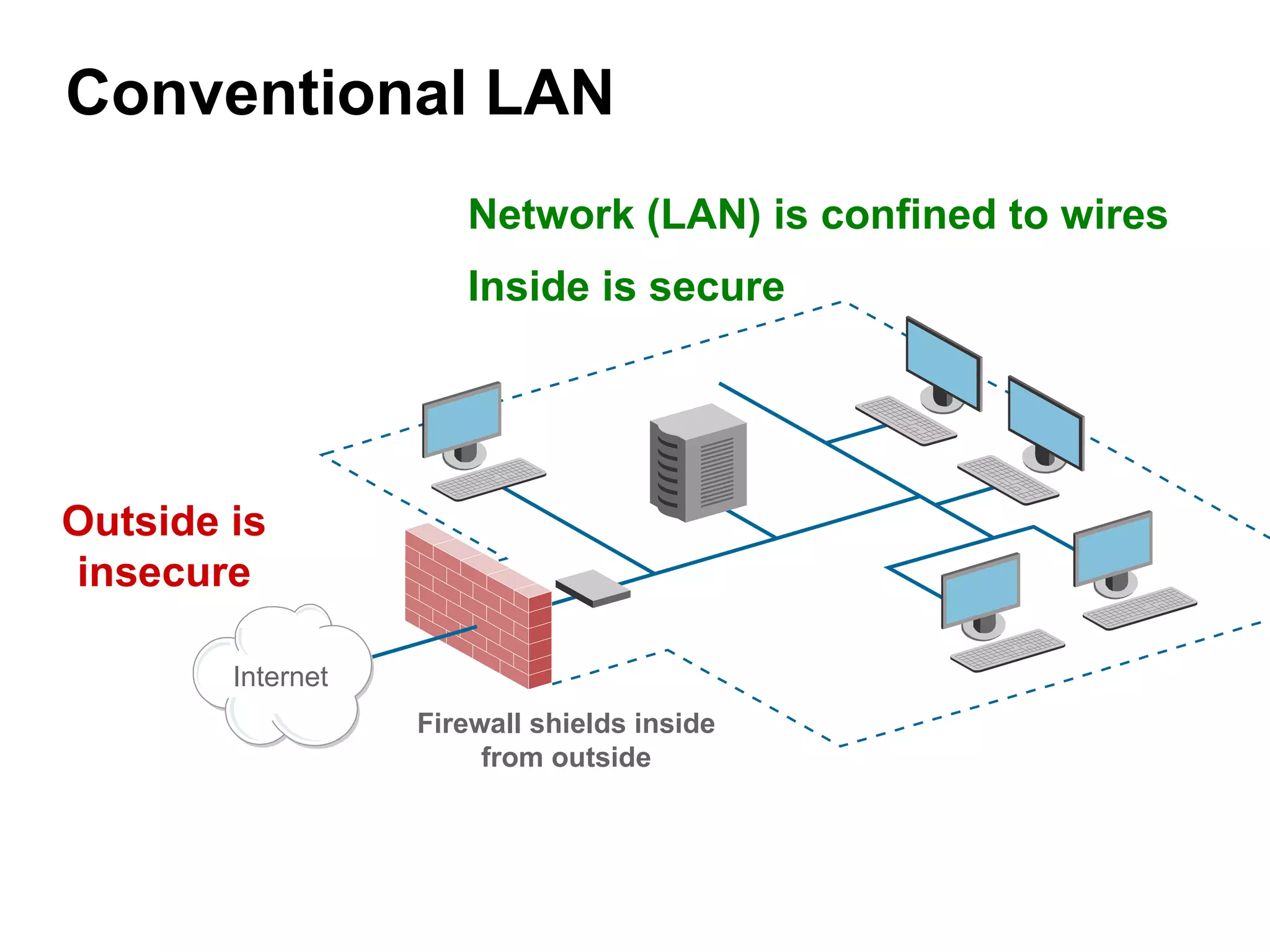
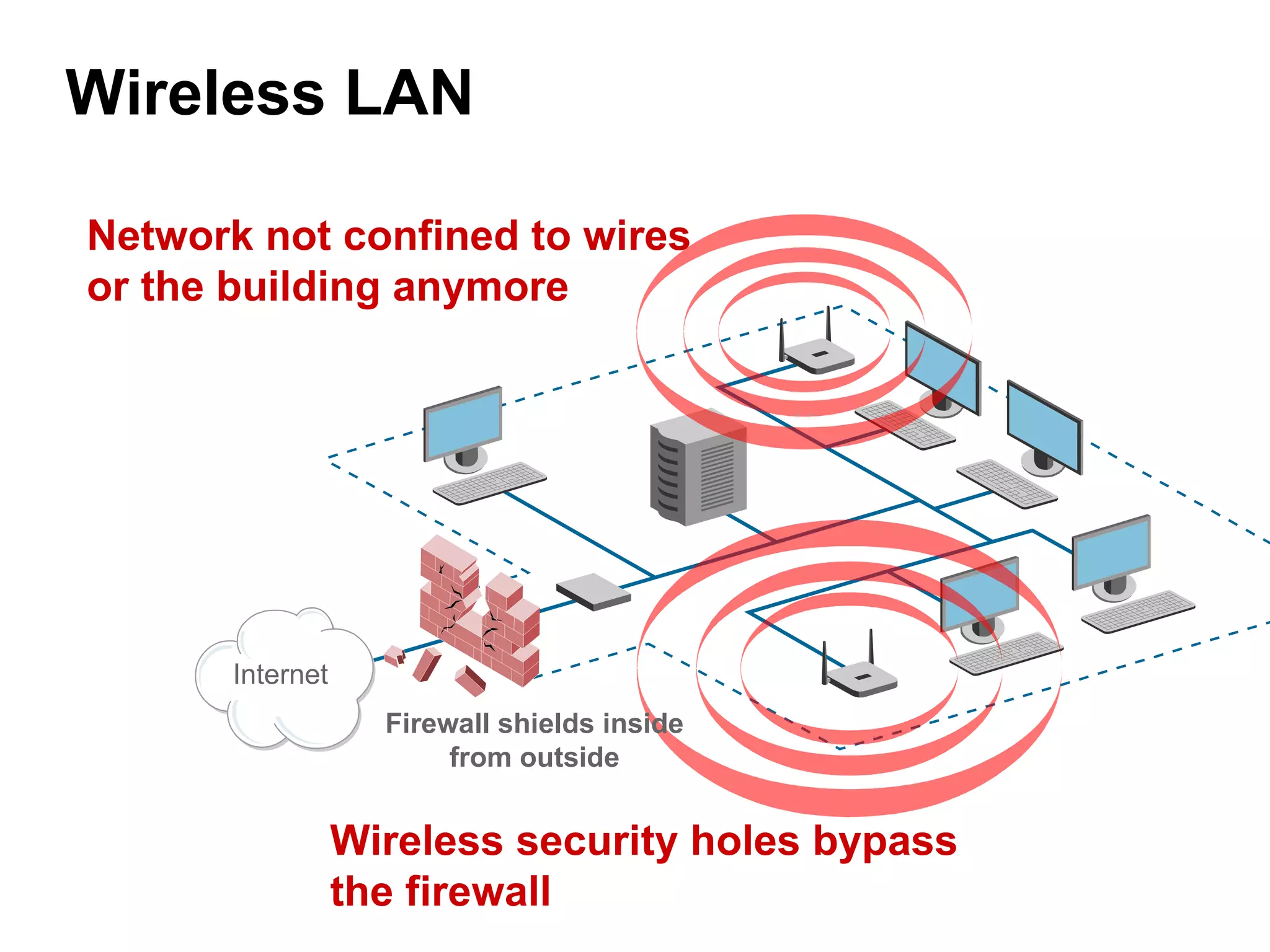
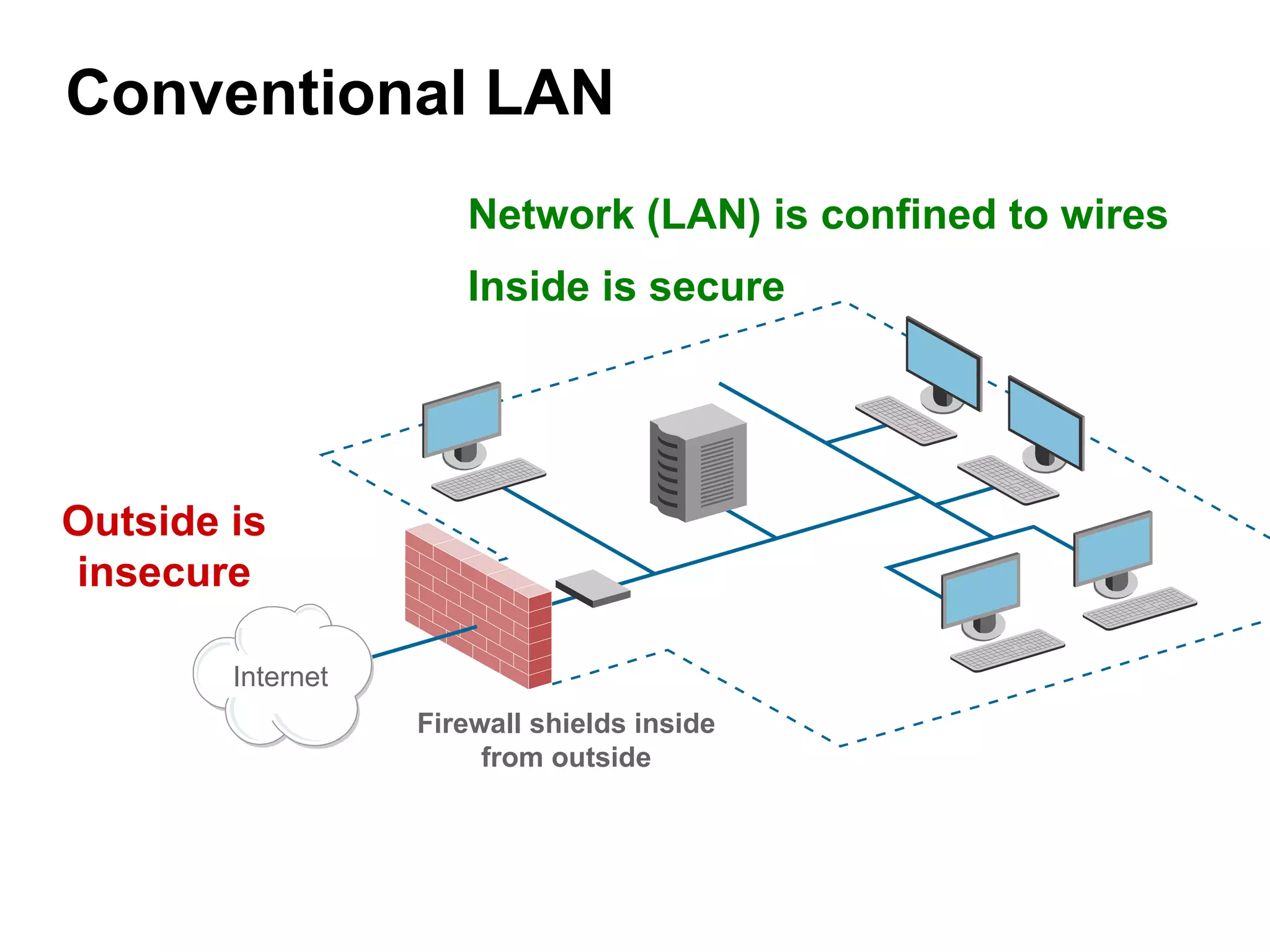
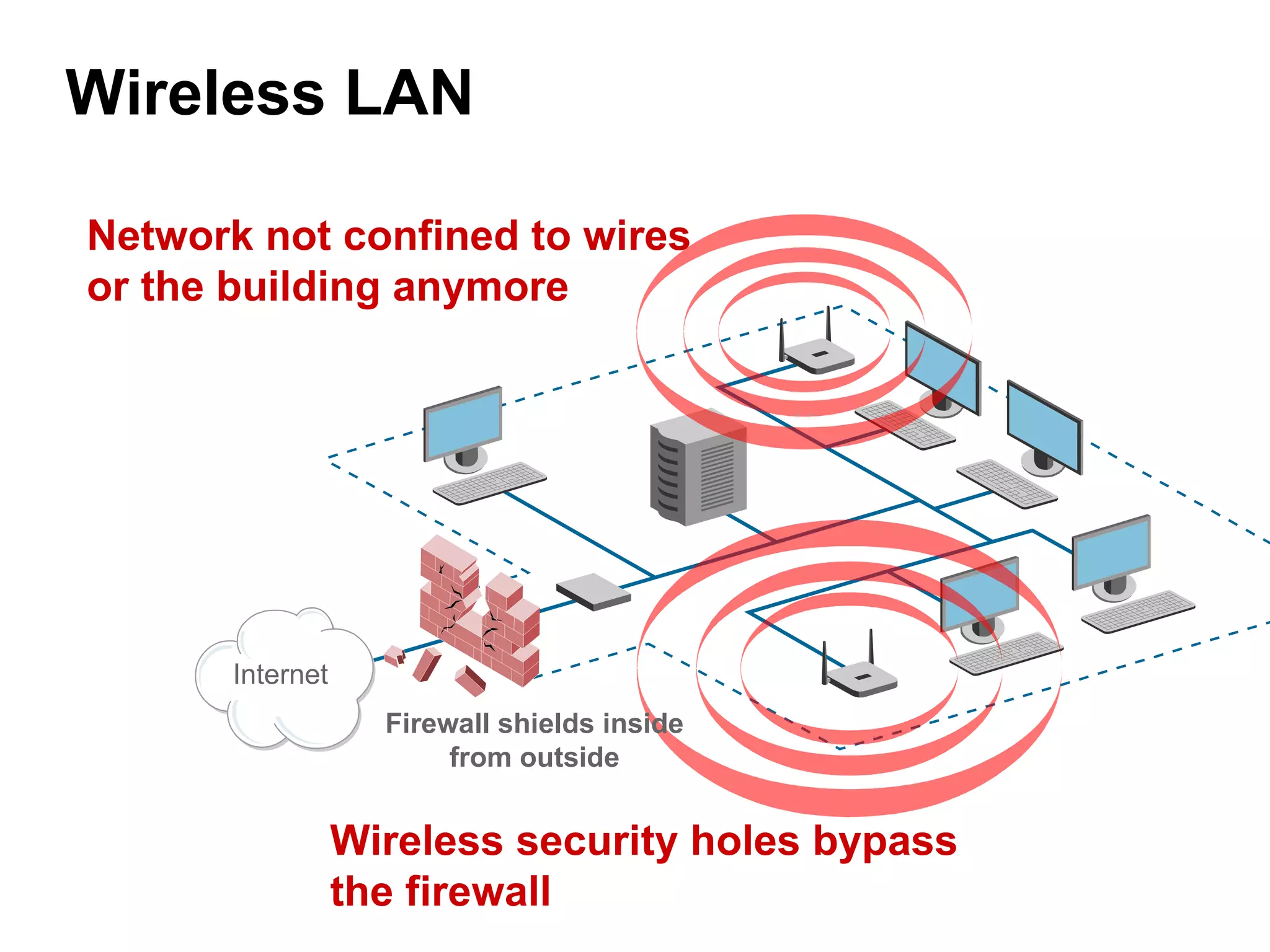
Comparison of traditional wired LAN and wireless LAN security with respective firewalls and vulnerabilities.
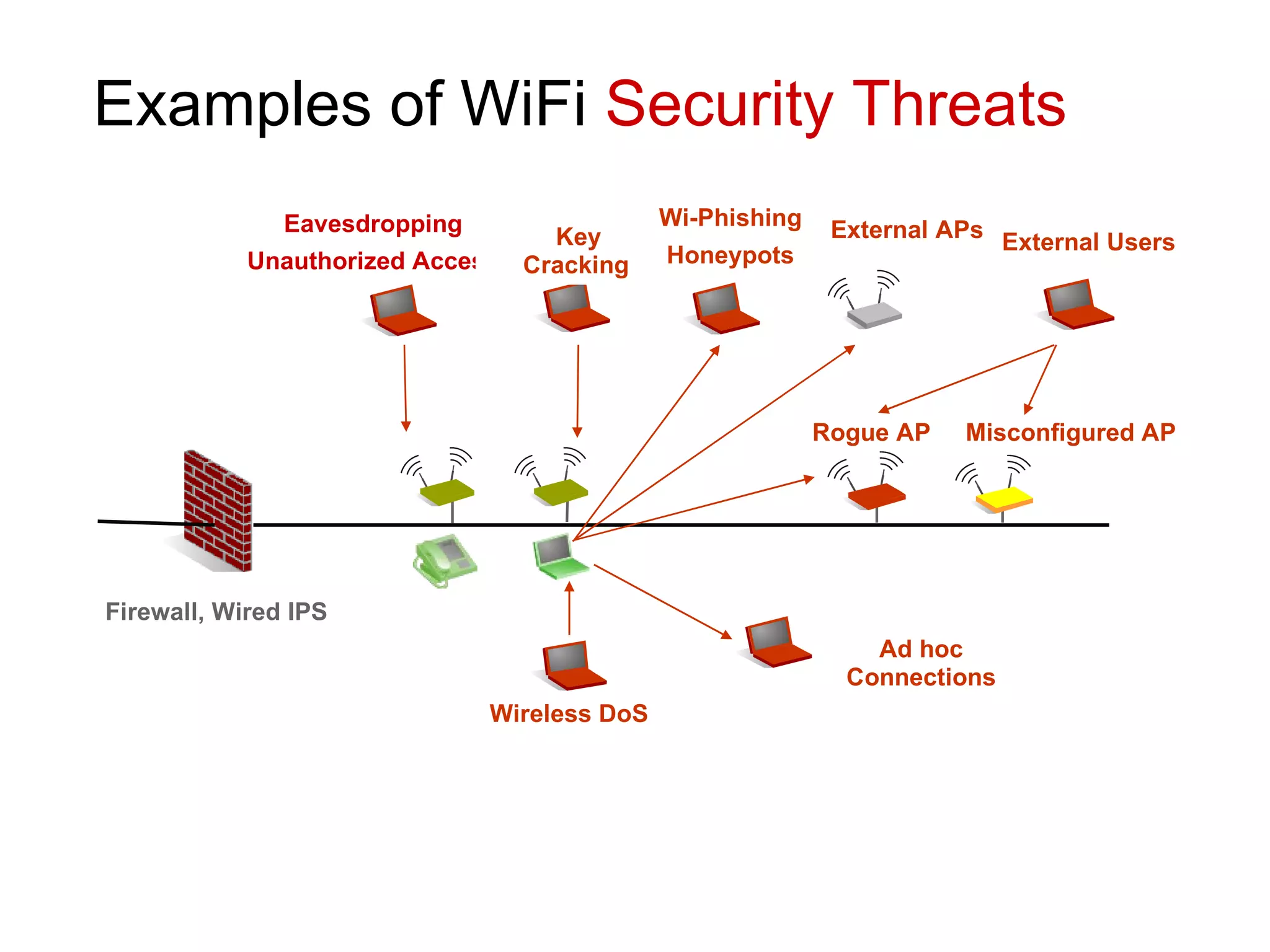
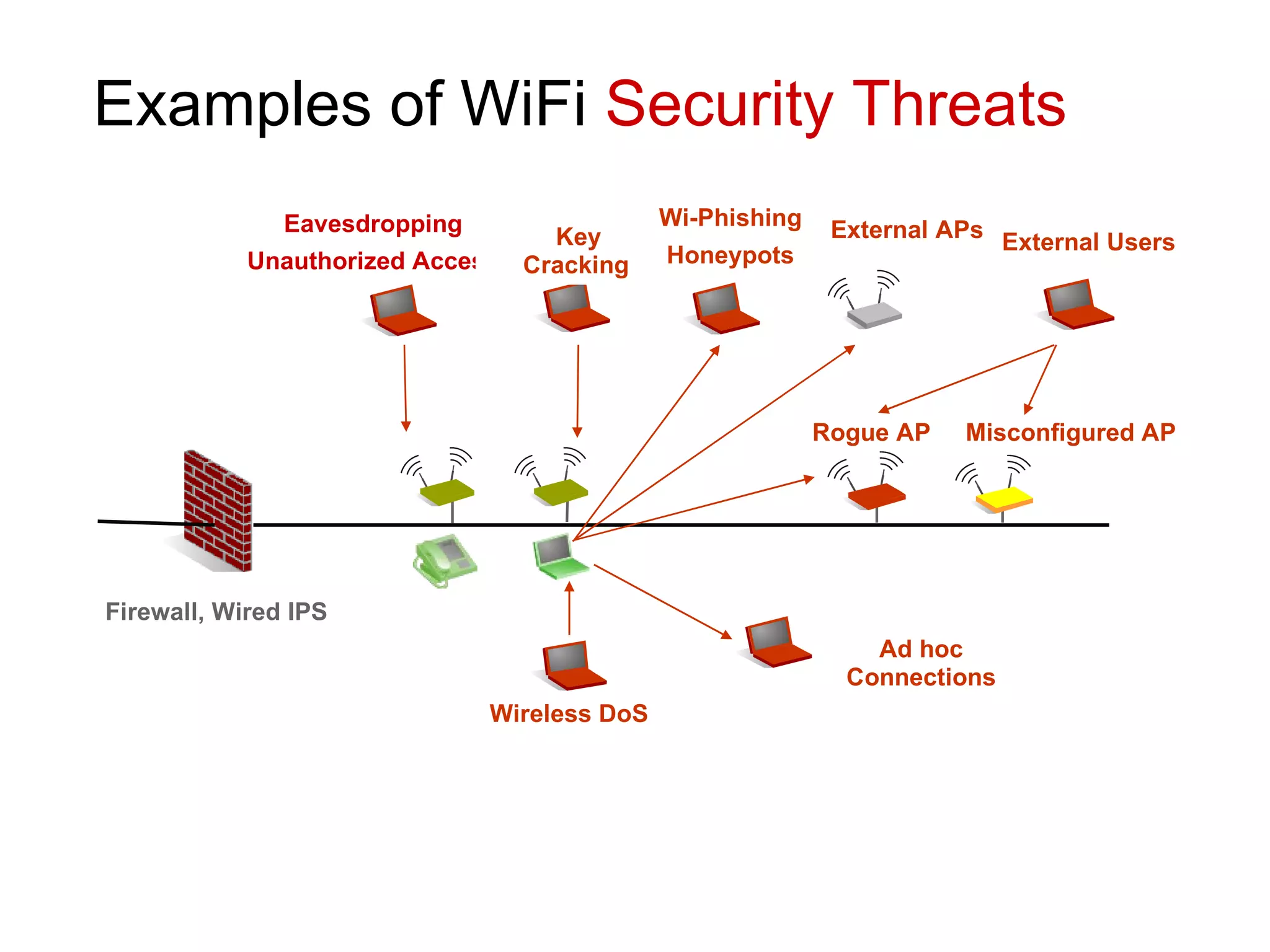
RF signals are prone to spillage, leading to serious threats like eavesdropping, unauthorized access, and more.
Banning WiFi does not eliminate threats; questions arise on effective security measures.
Security measures include locking, watching, monitoring, and utilizing training, processes, and technology.
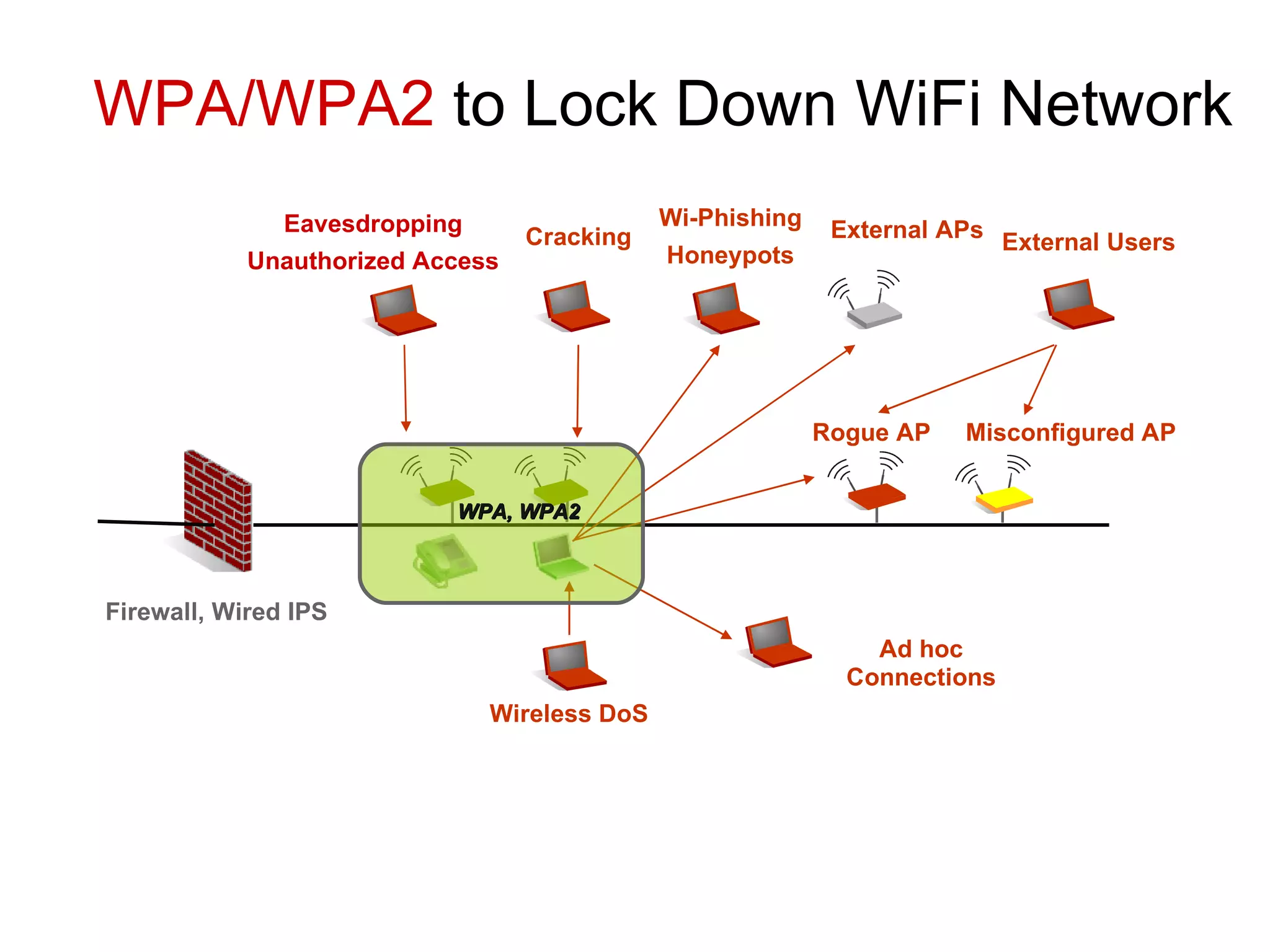
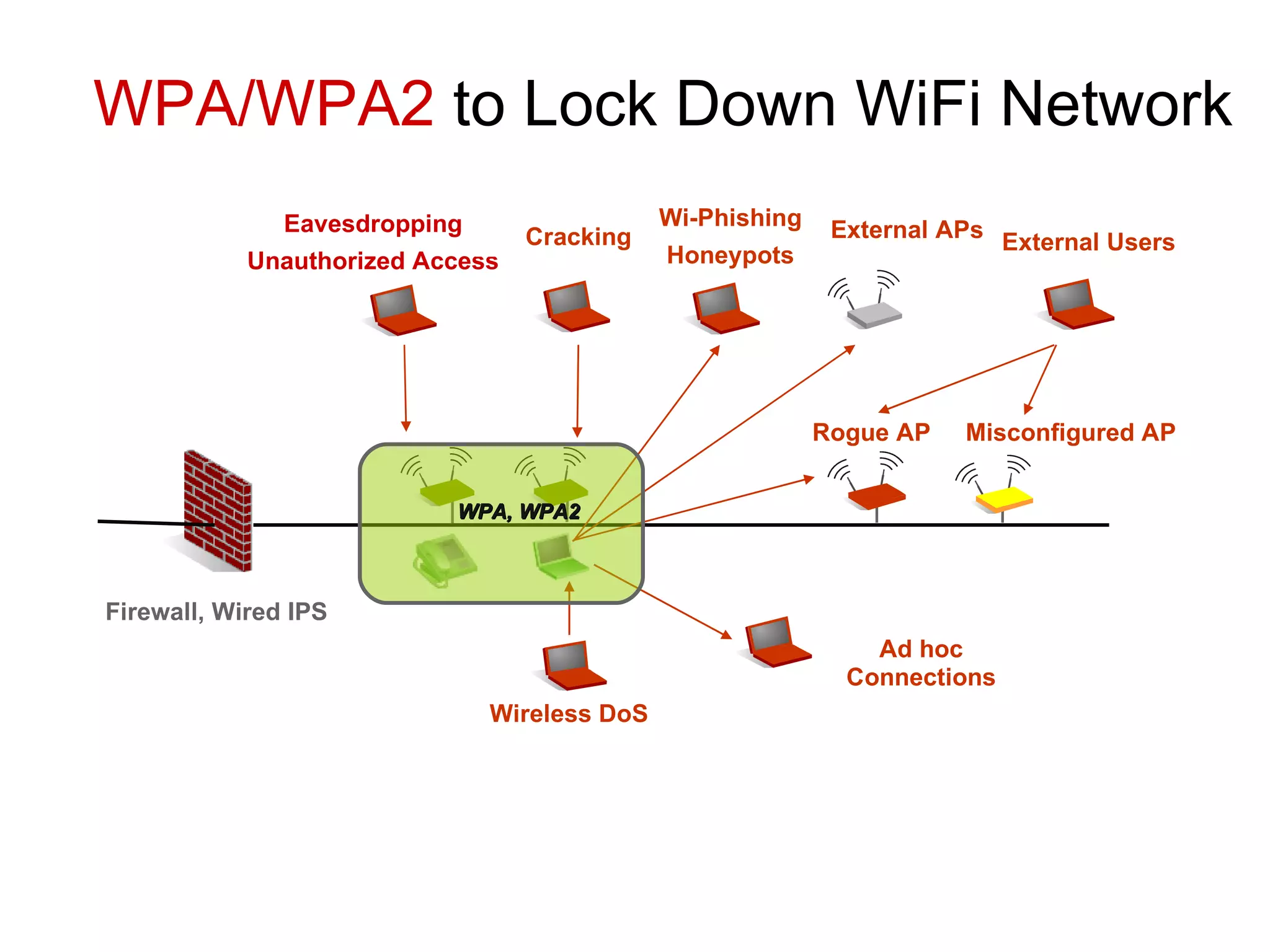
Using WPA/WPA2 and WIPS for securing WiFi; methods to detect, block, and locate WiFi misuse and attacks.
Thank you note and contact information for Md Sohail Ahmad, highlighting the global leadership in wireless security solutions.