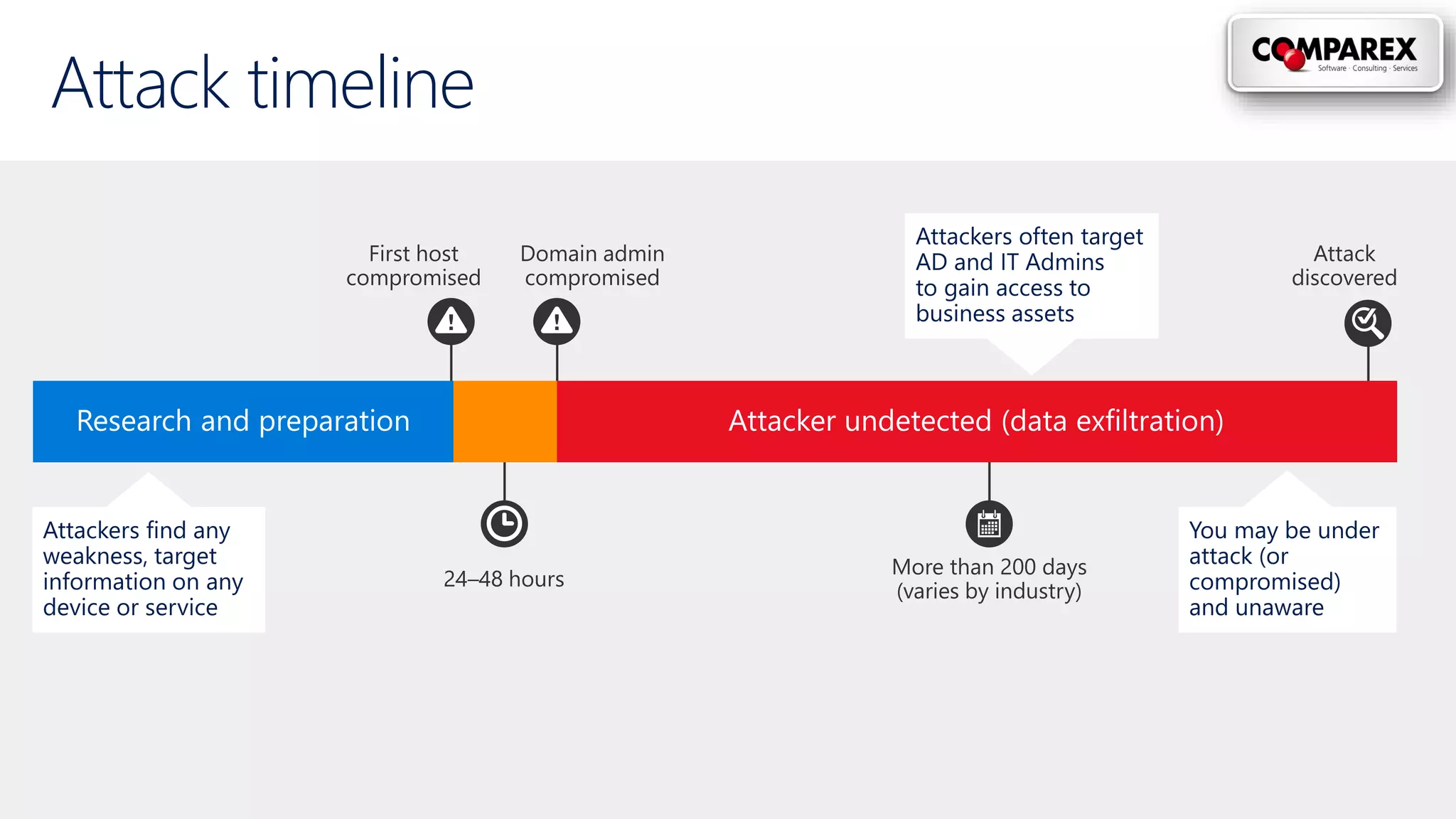
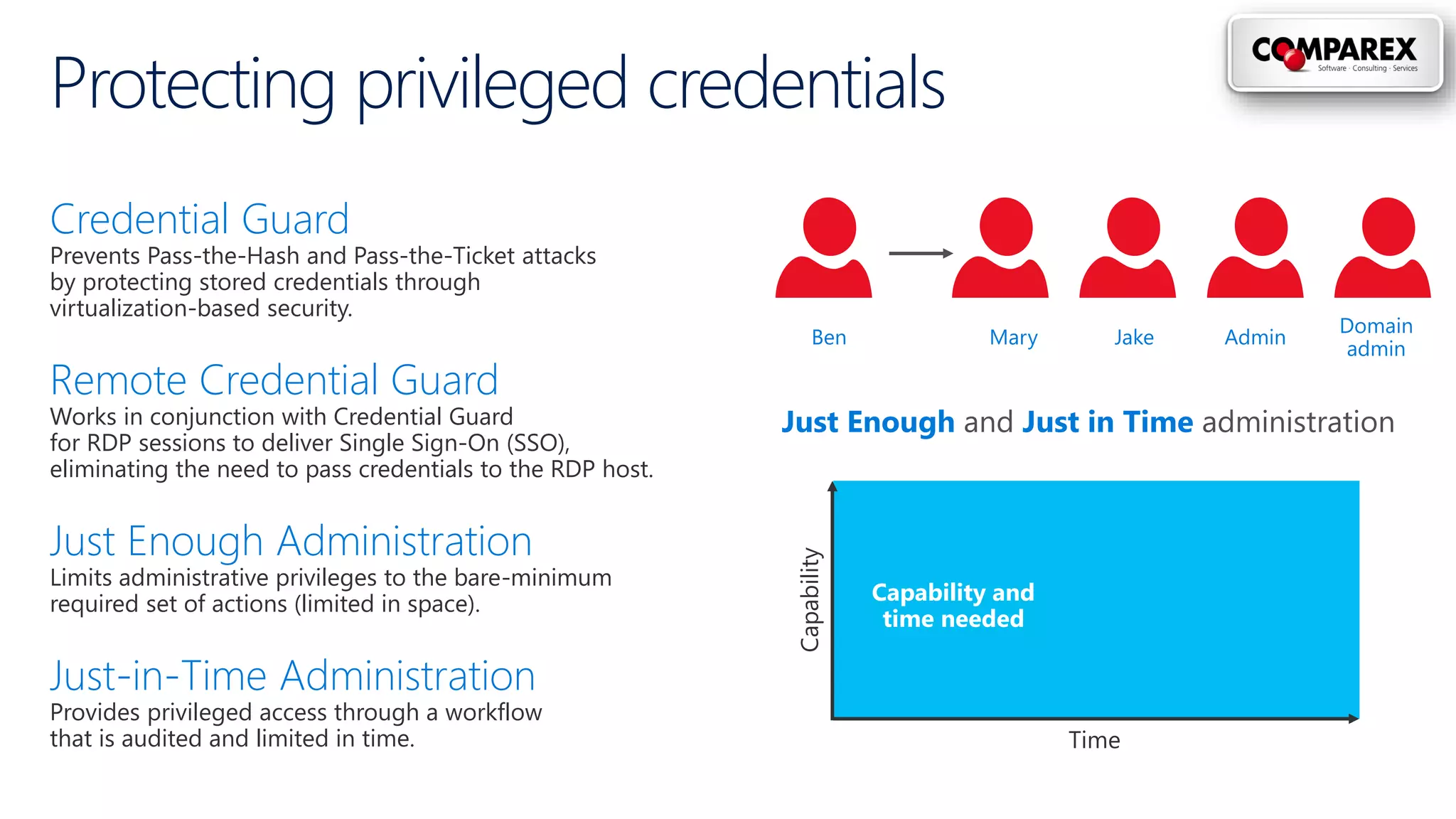
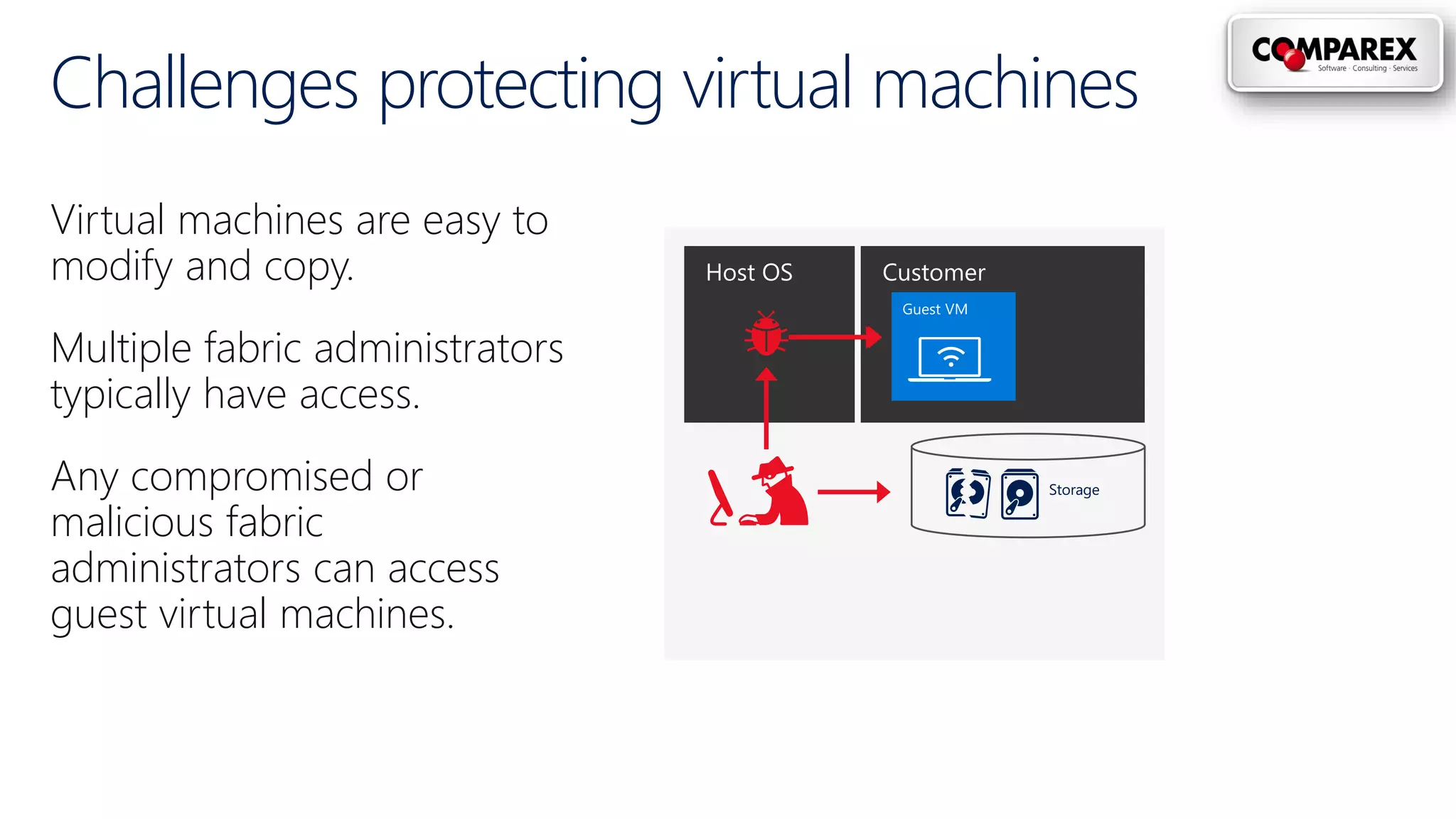
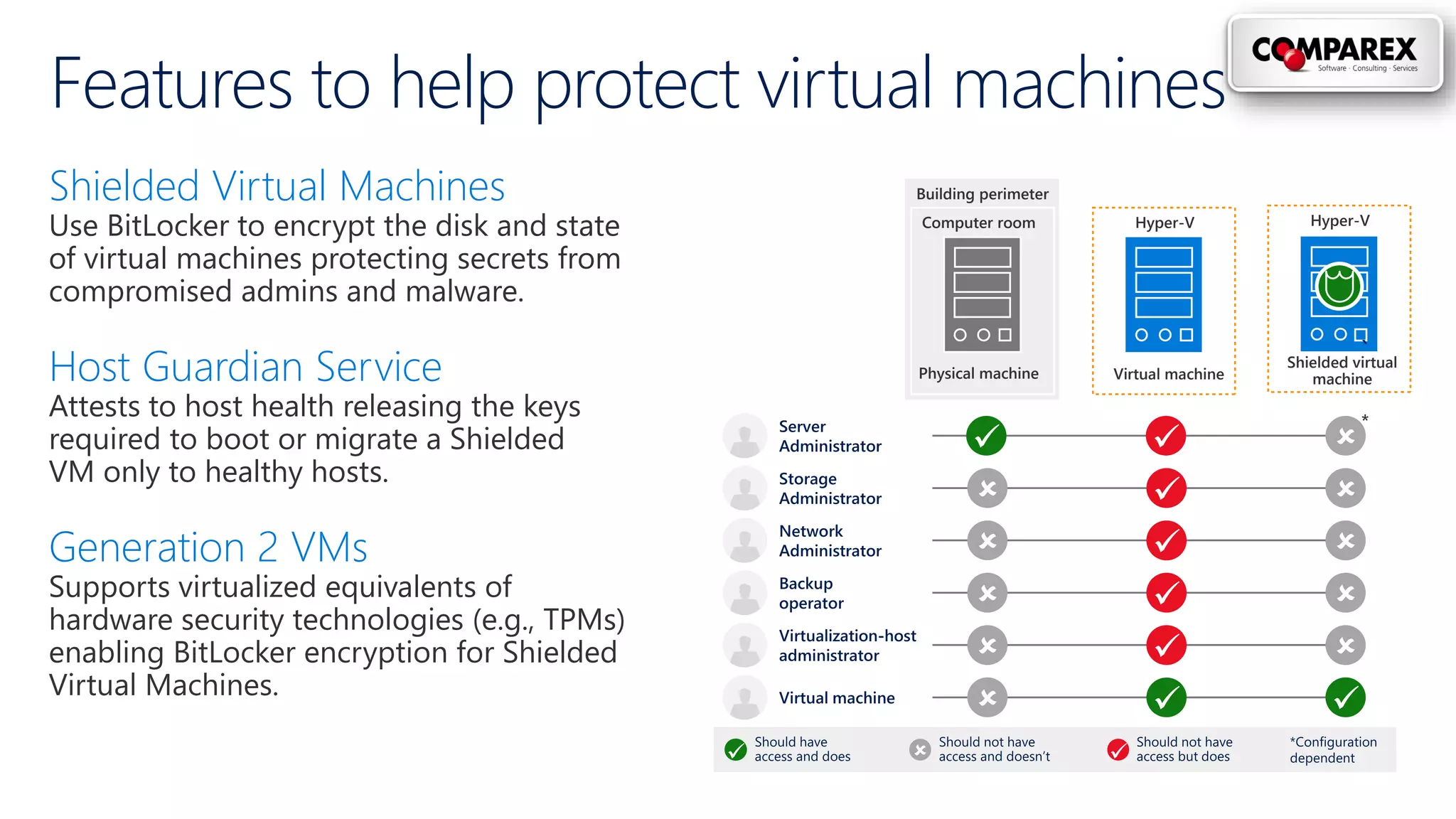
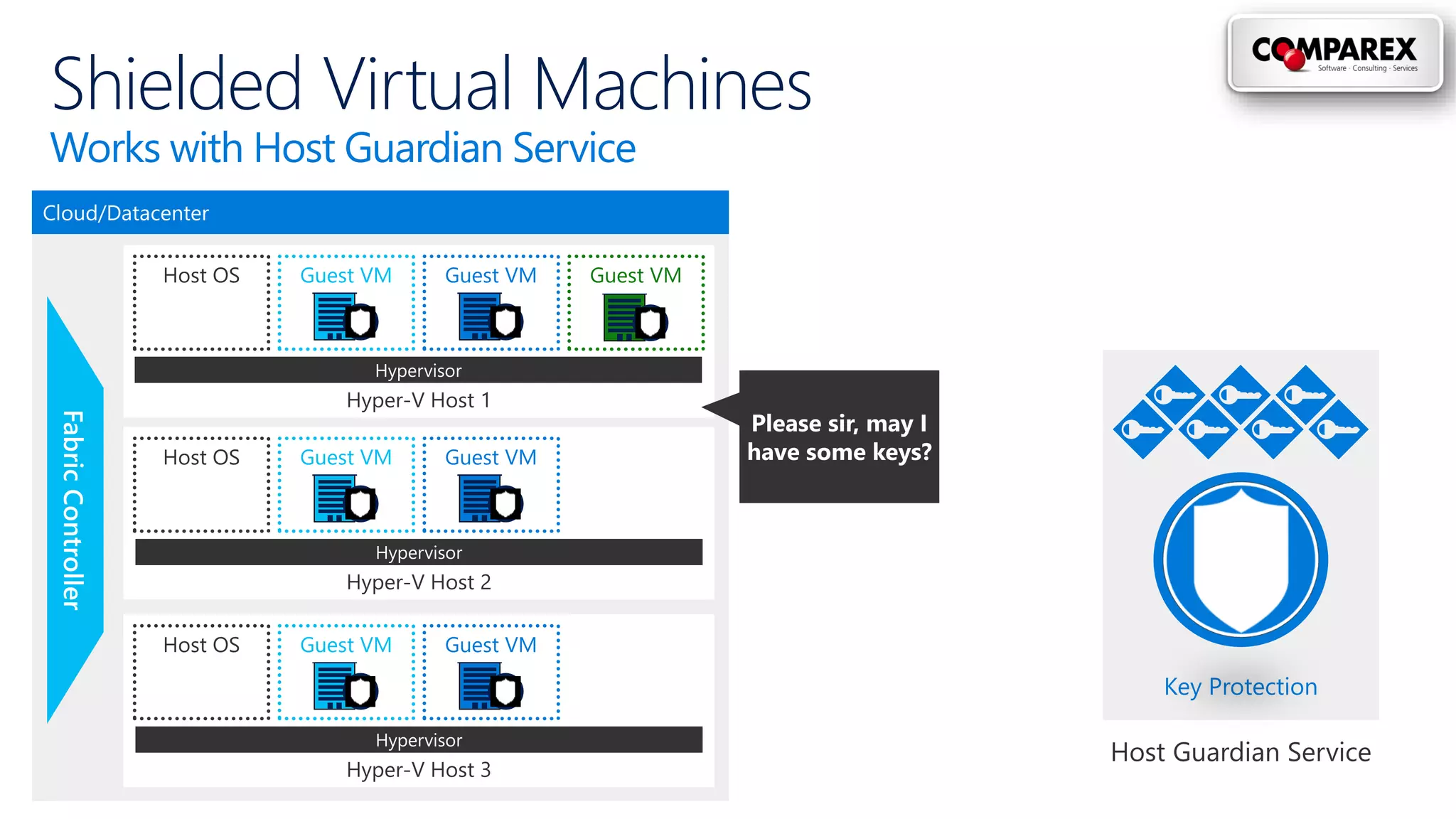
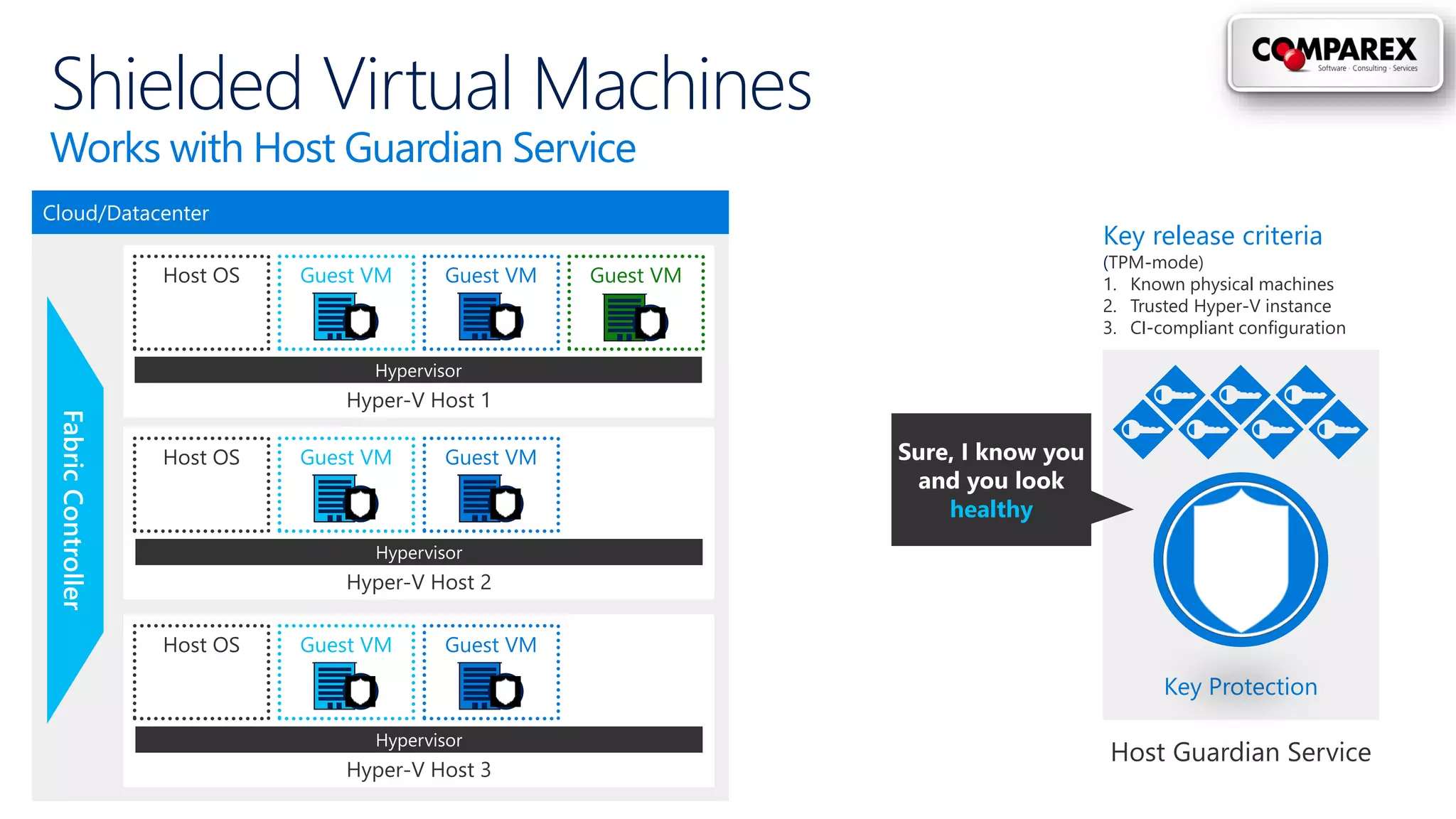
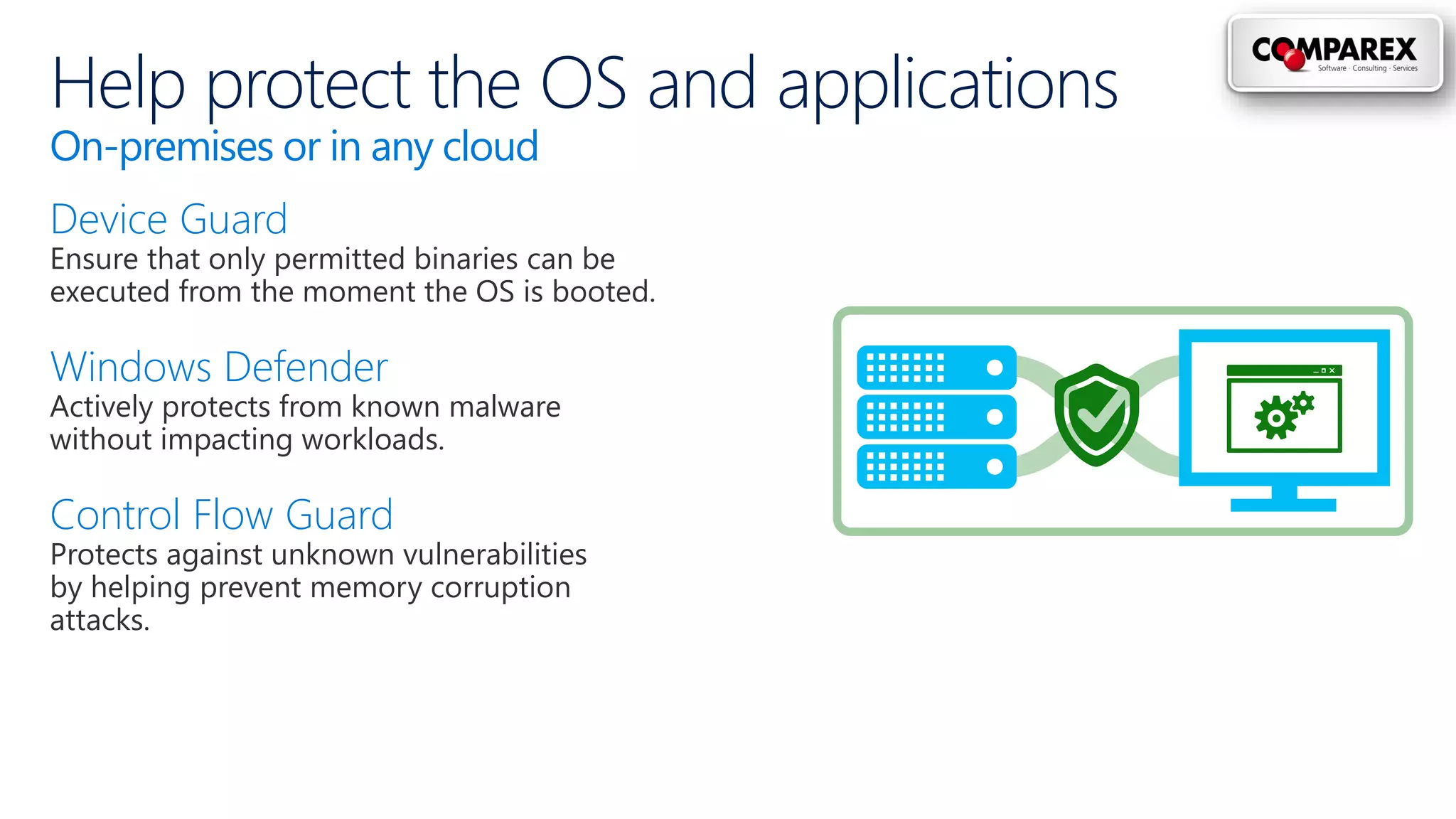
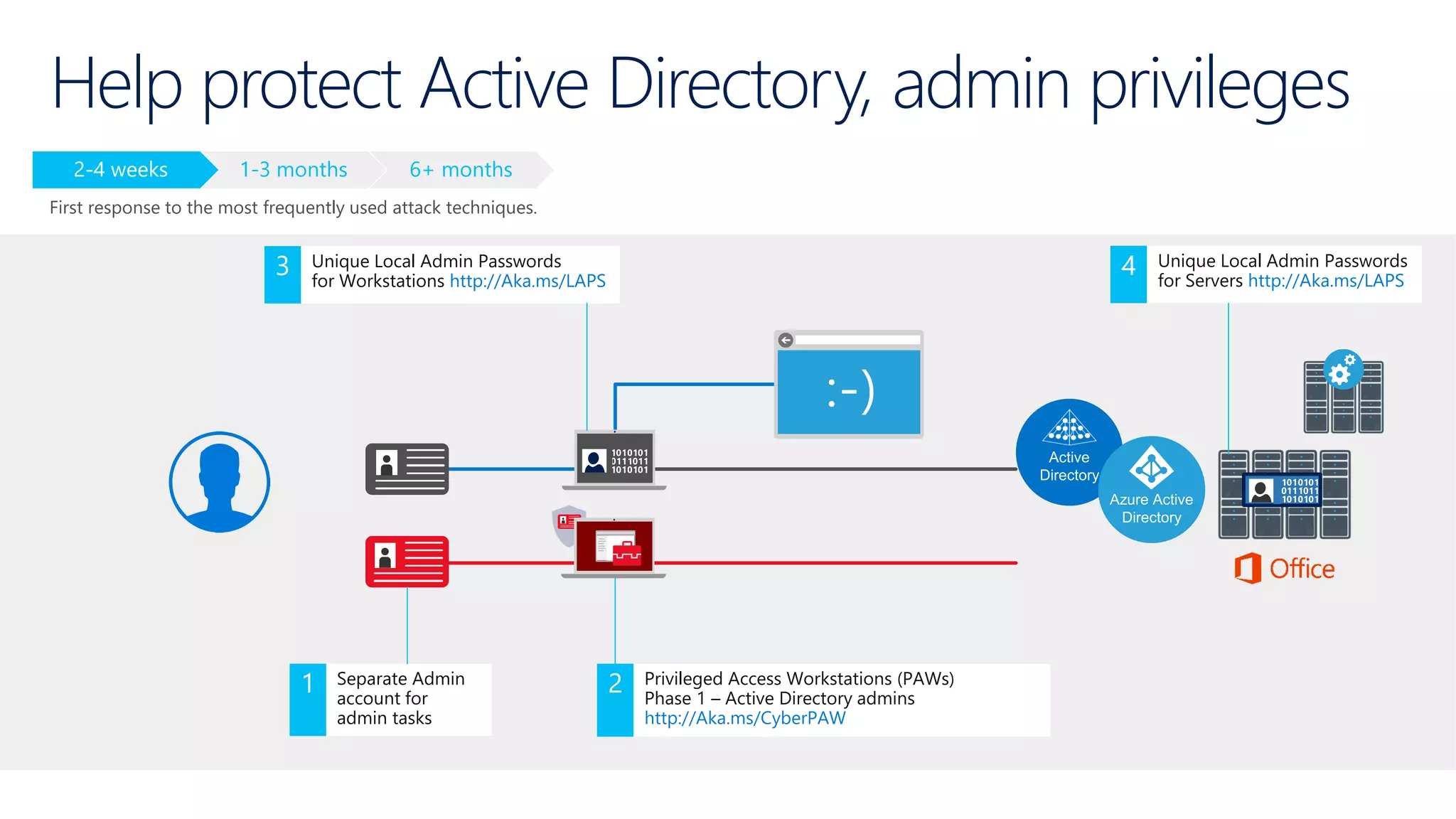
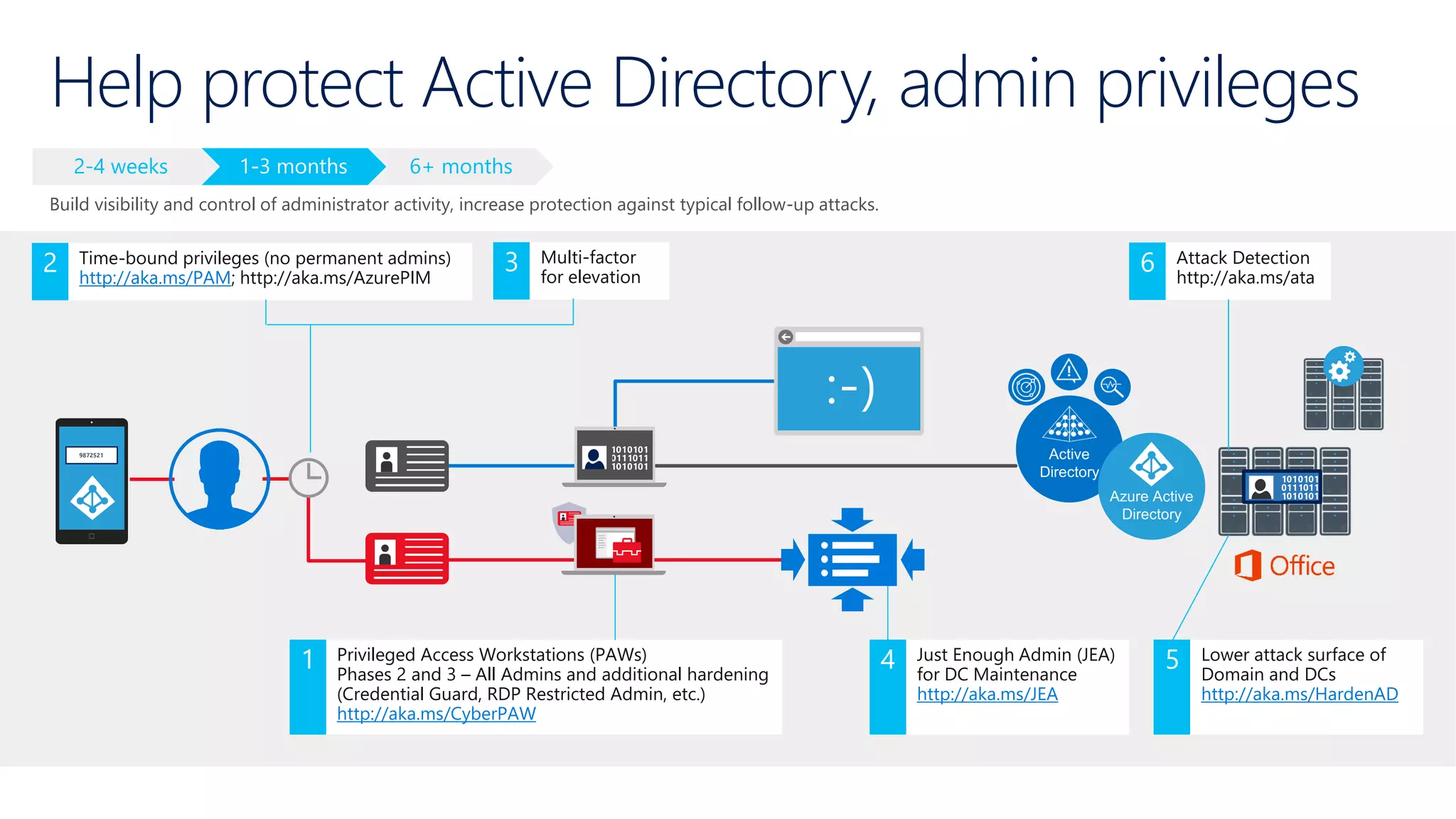
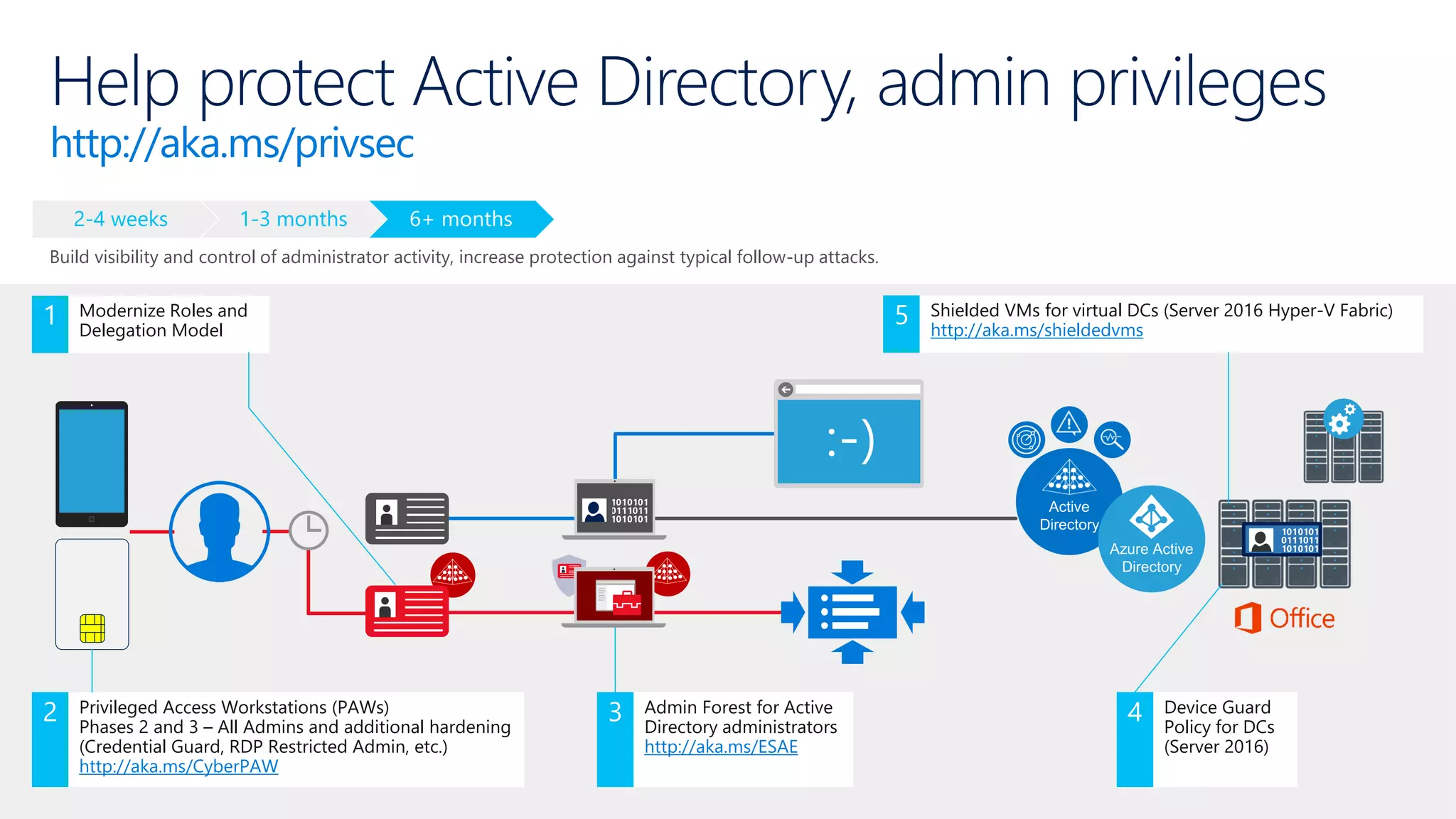
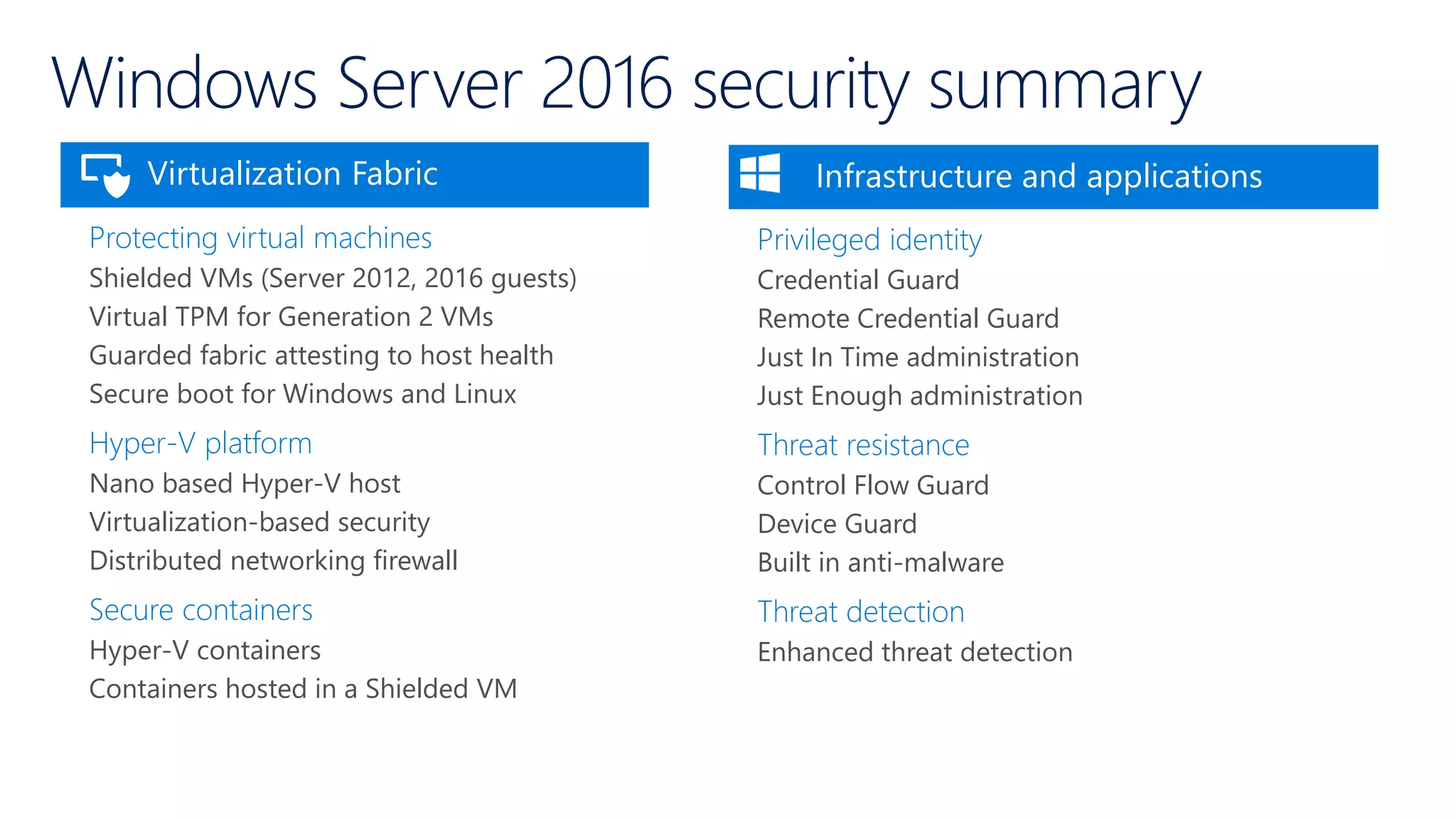
This document discusses security priorities and features in Windows Server 2016. It notes that IT teams are pulled between supporting business agility/innovation and providing secure resources. Security threats are a top IT priority due to increasing incidents and multiple motivations for attacks. Windows Server 2016 includes features like shielded virtual machines, credential guard, and device guard to help protect identities, virtual machines, the operating system, and privileged access. These features aim to provide security while still supporting innovation.