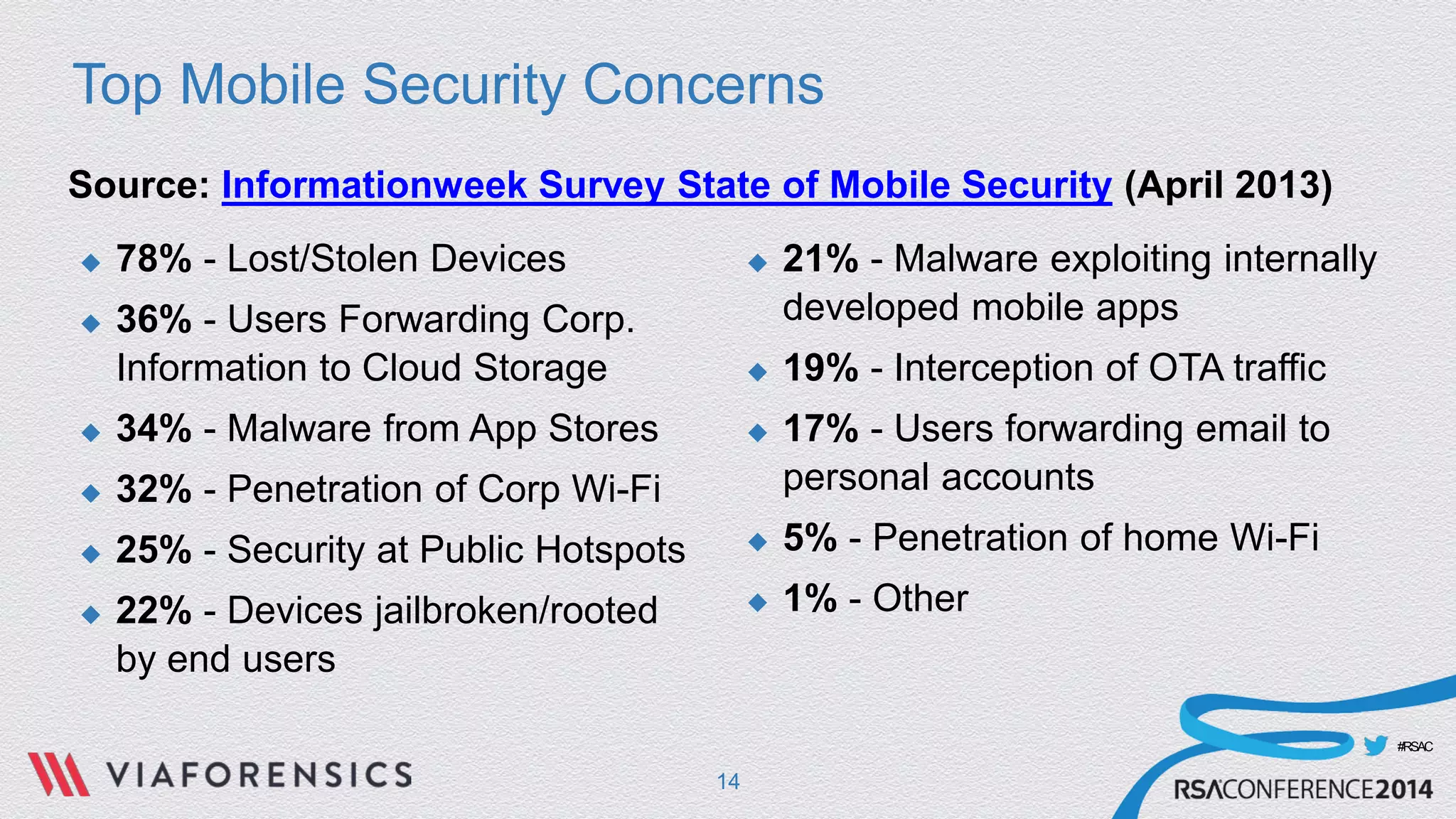
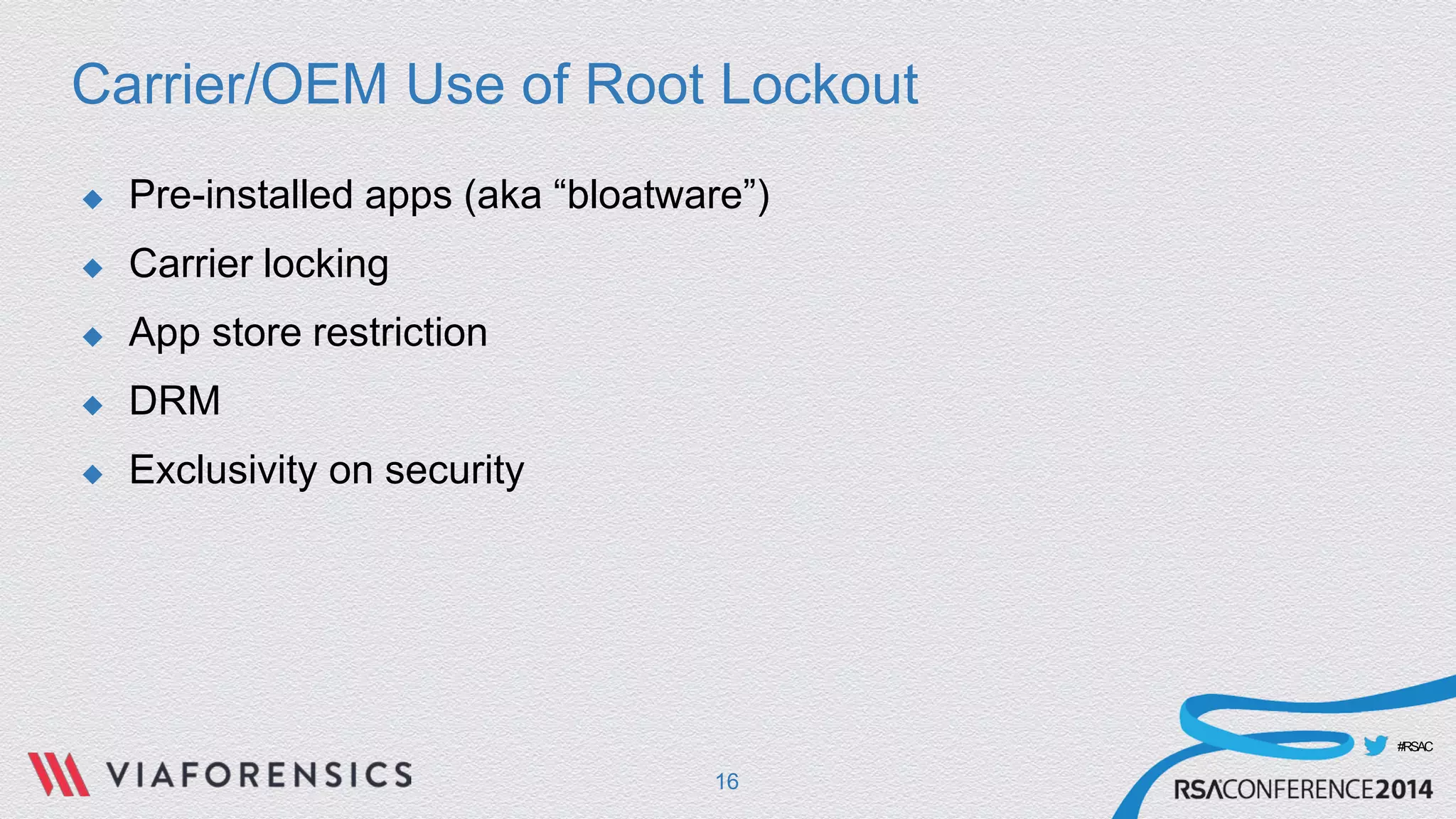
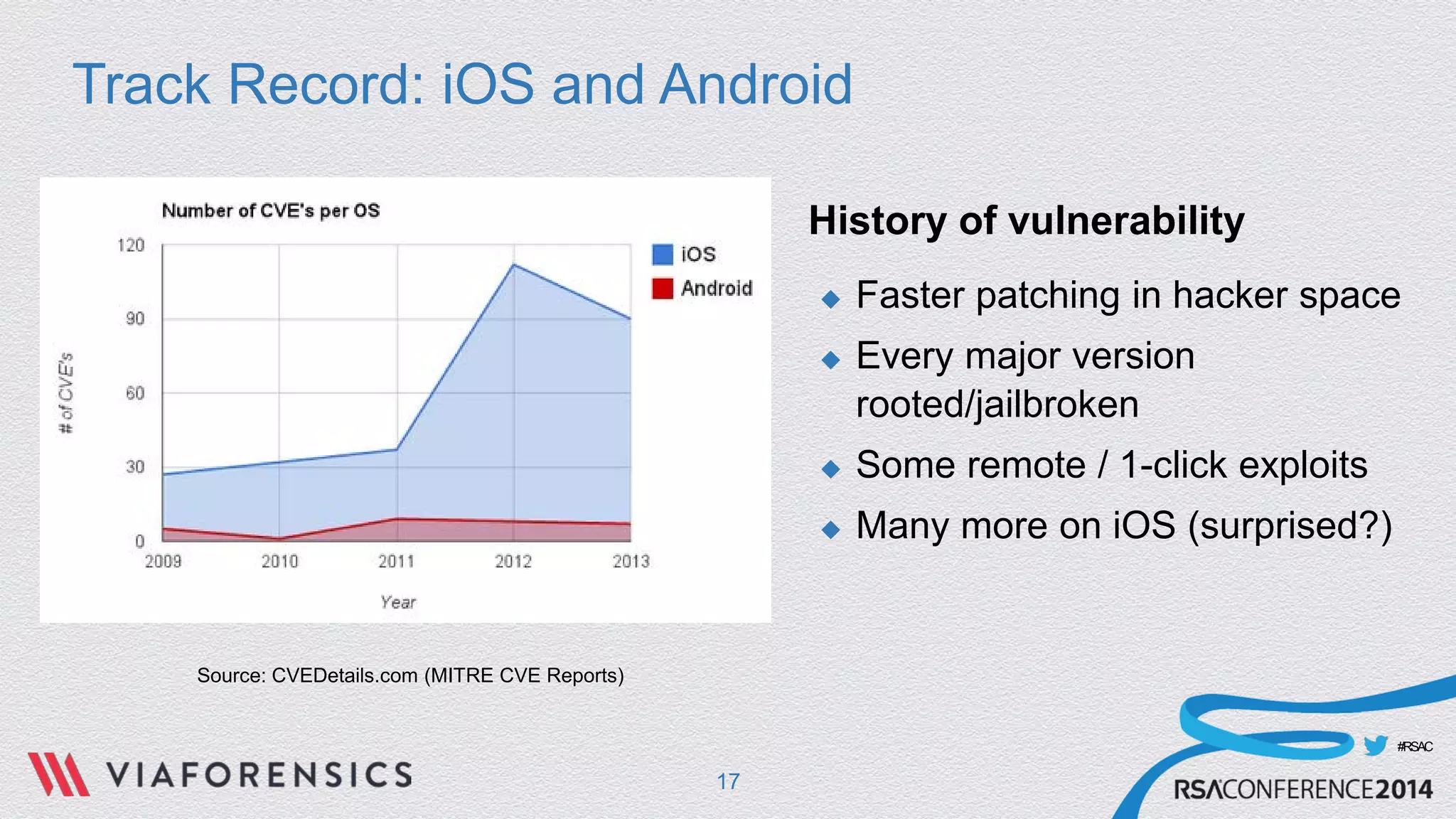
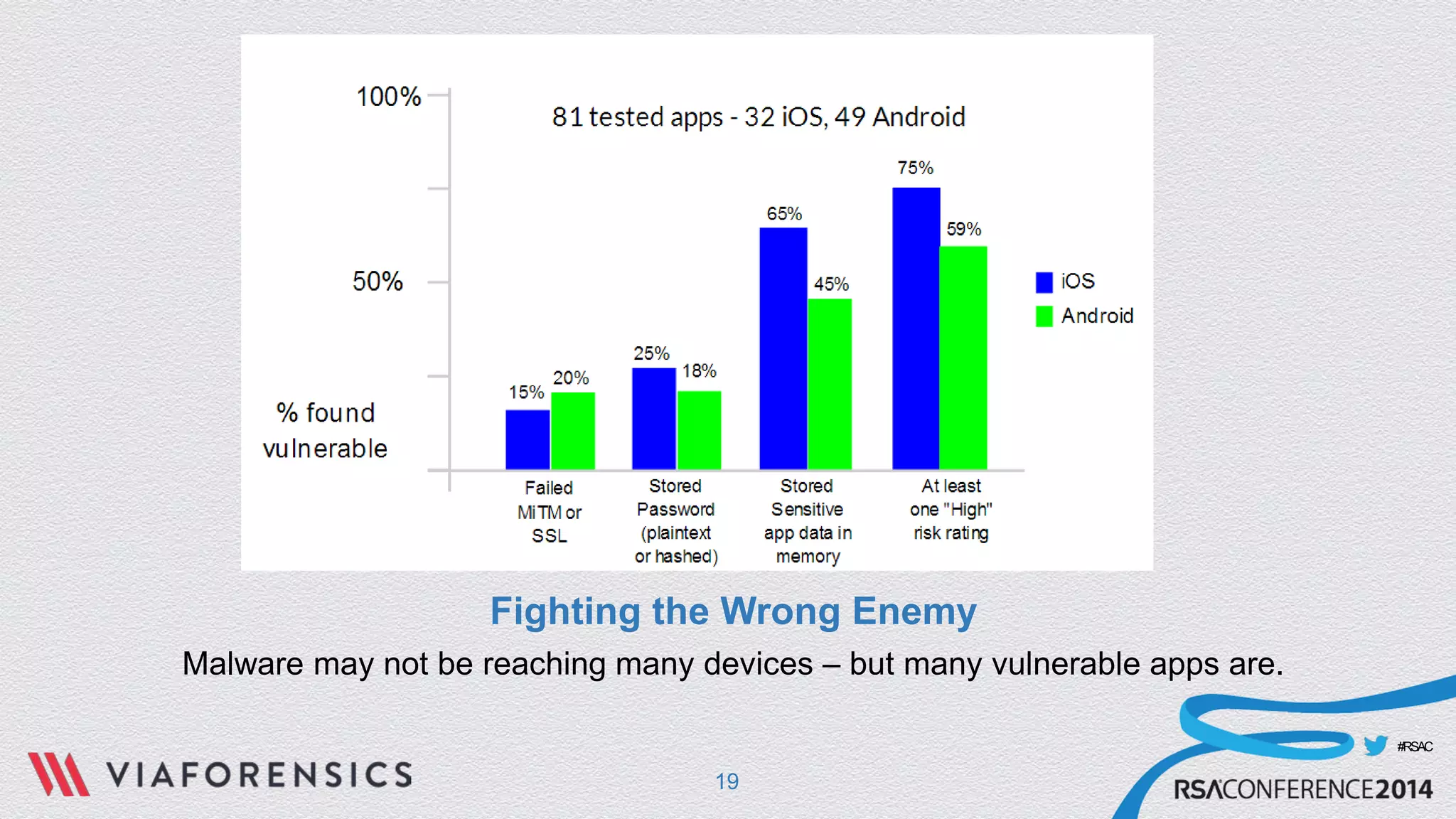
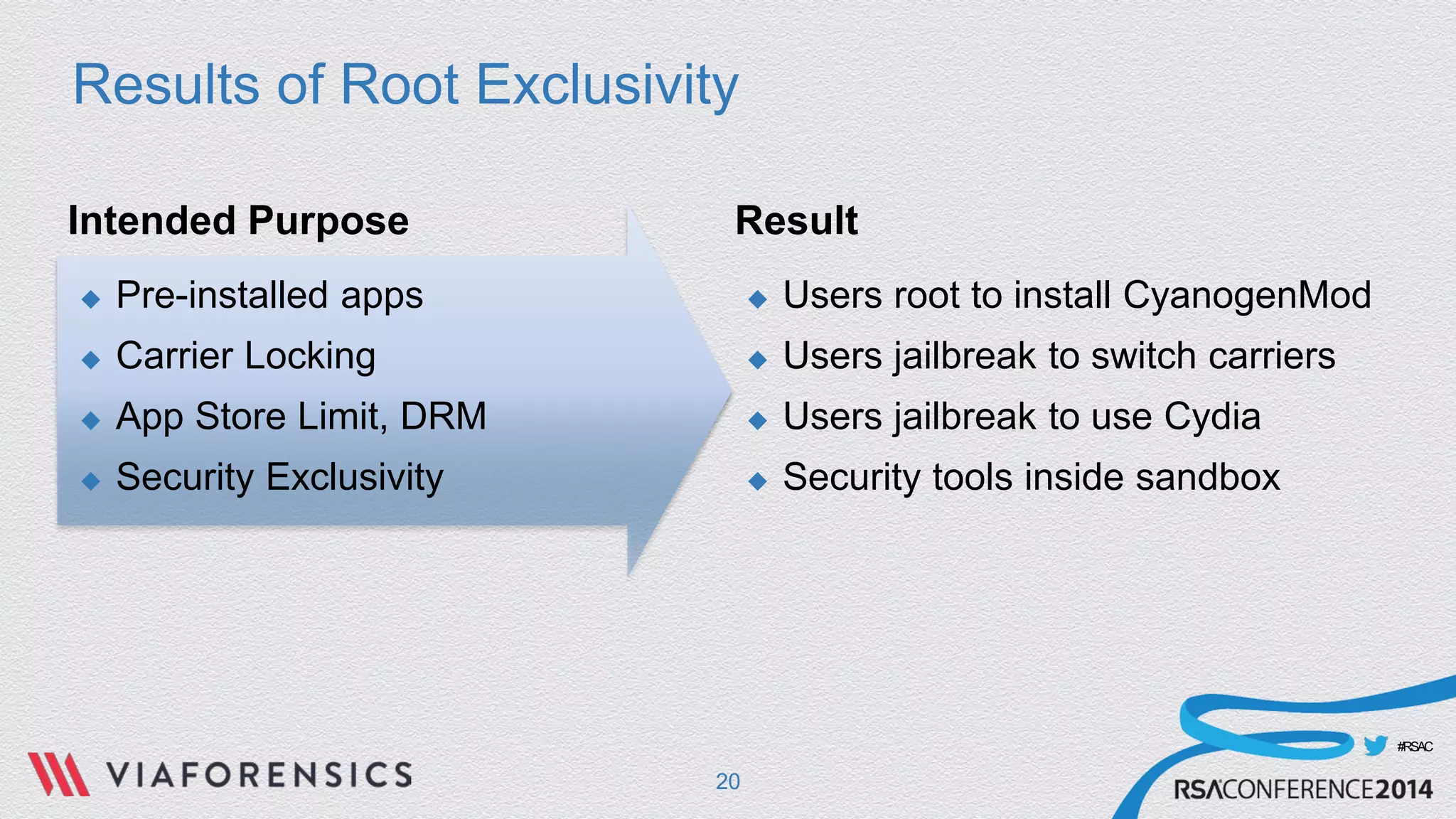
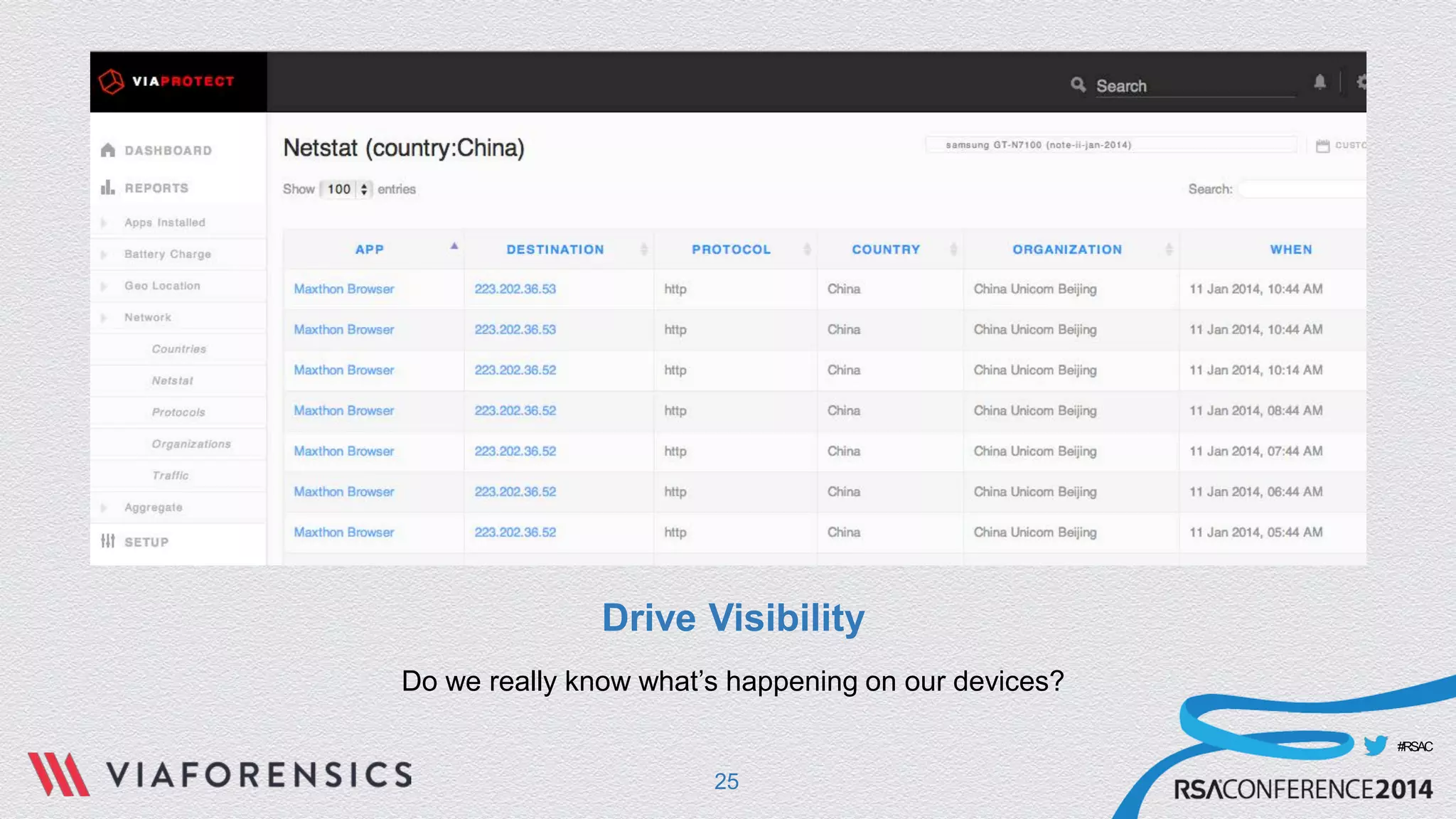
This document discusses the history of root access on mobile devices and argues that mobile devices should stop locking out root access. It outlines the main security concerns about mobile devices, such as lost/stolen devices and malware, and argues that root access restrictions intended to address carrier/OEM interests have actually resulted in users rooting their devices to install custom software or switch carriers. The document proposes that a better approach would be to give enterprise administrators and security vendors root-level access through OEM programs in order to gain more visibility into devices and better address real mobile security risks like vulnerable apps and insider threats.