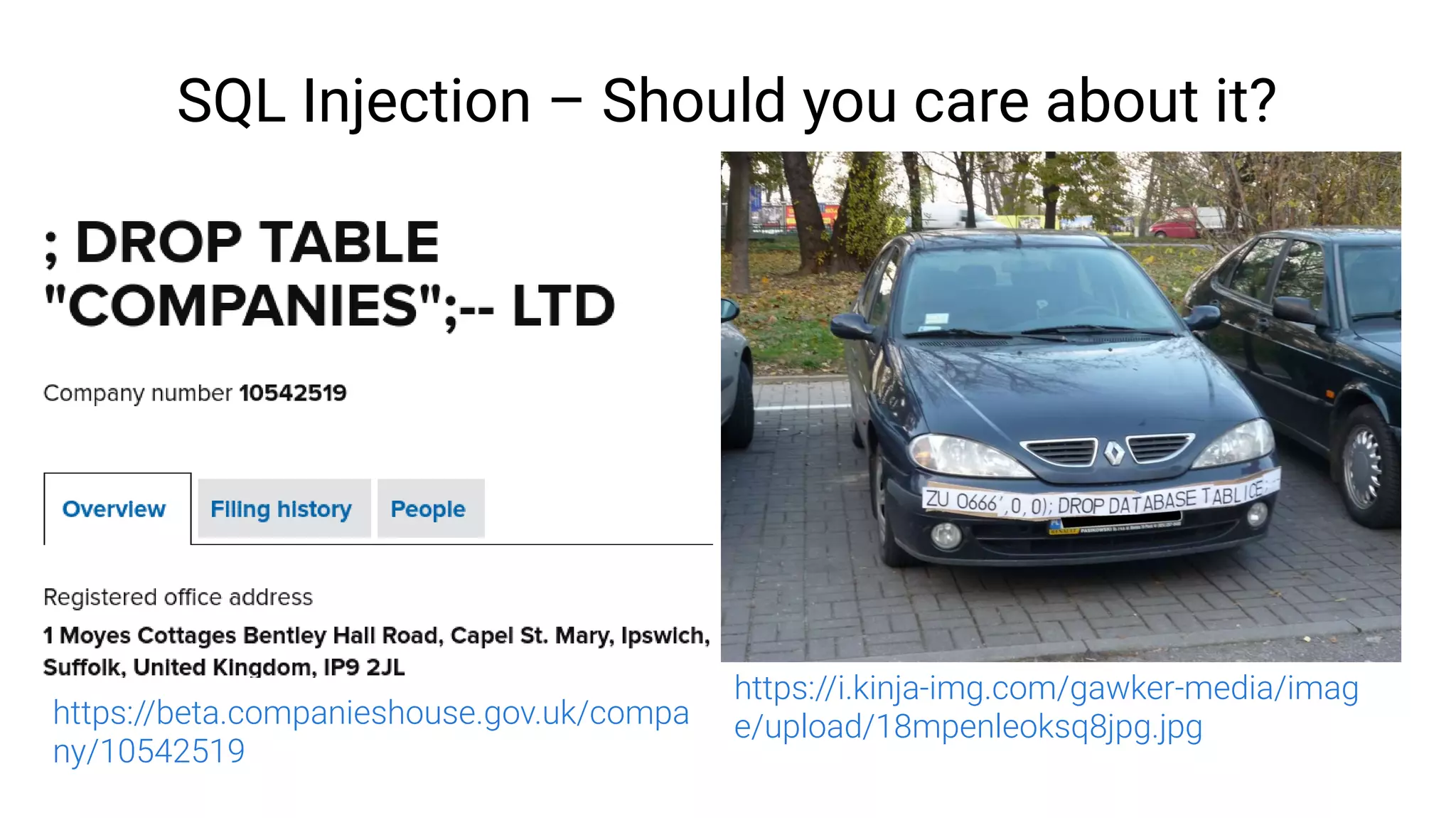
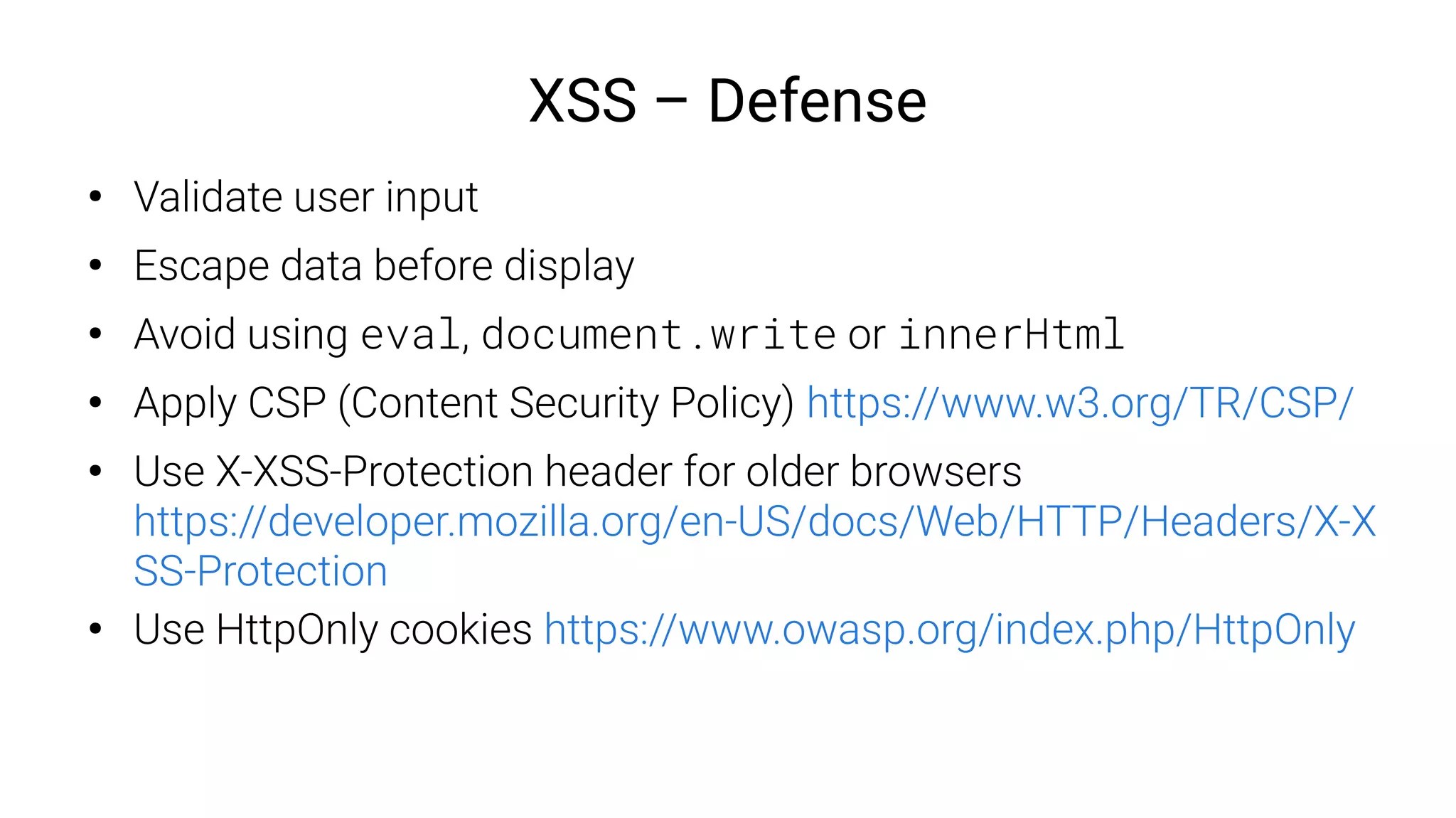
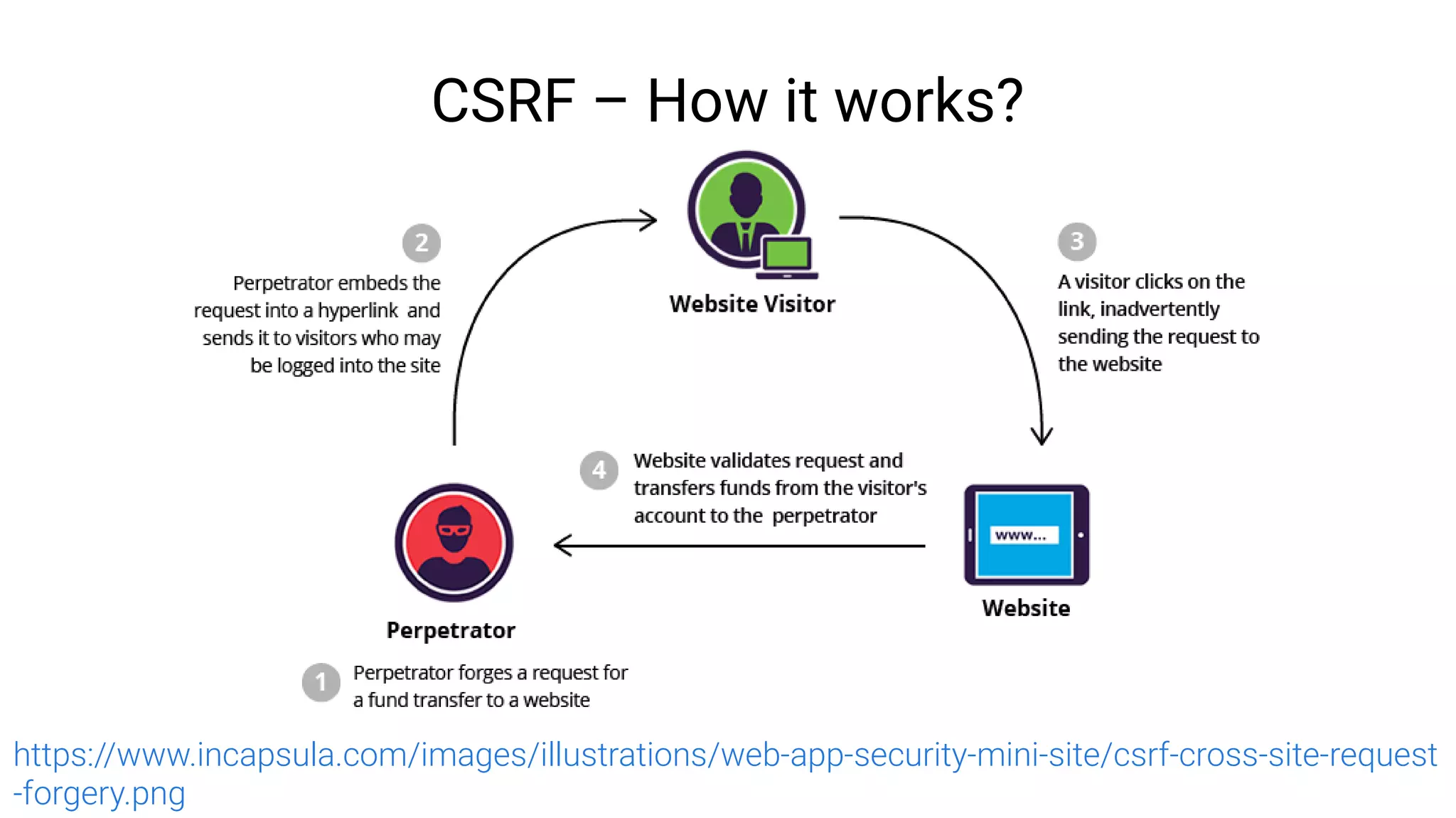
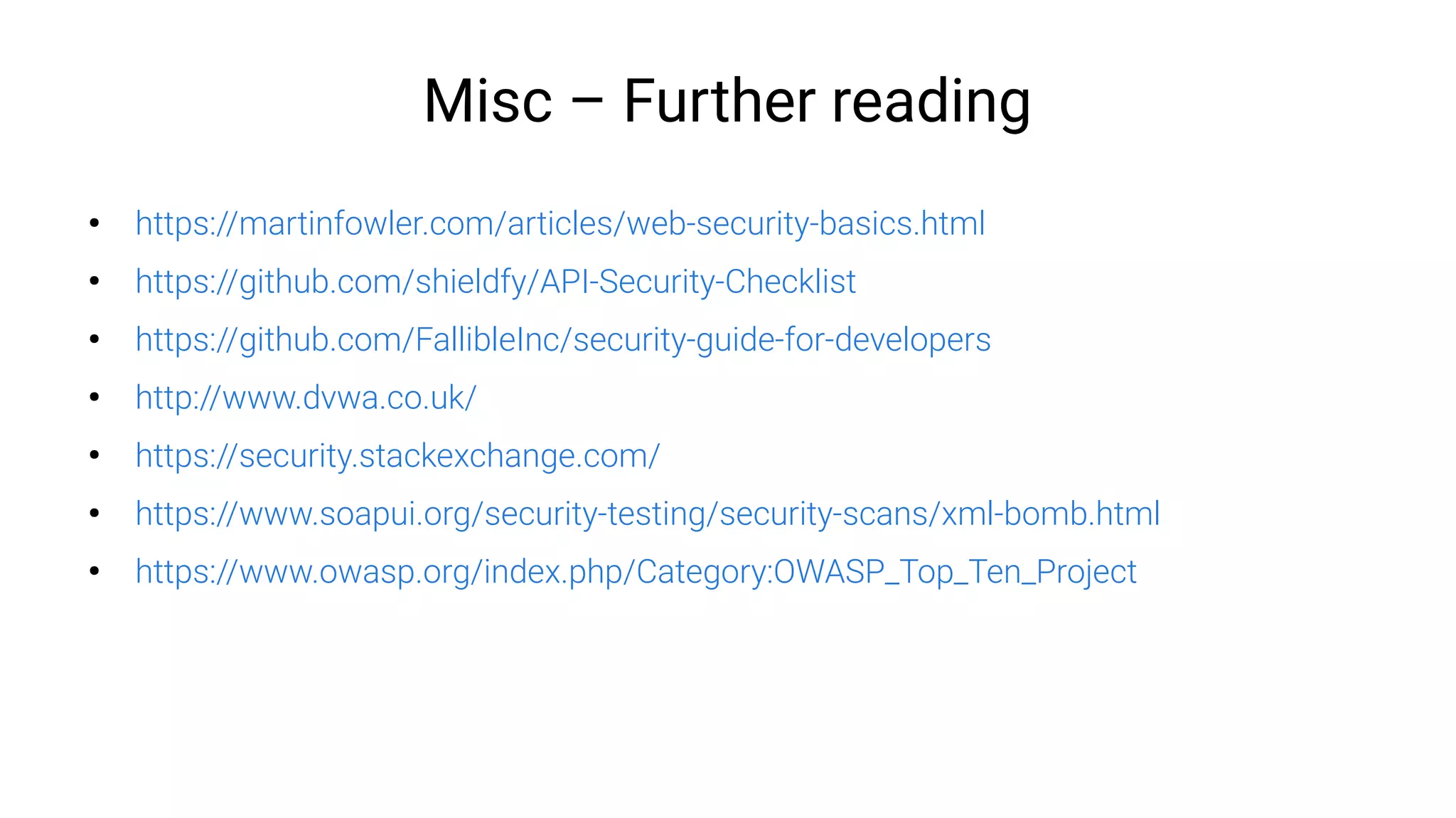
The document outlines various web vulnerabilities including SQL injections, cross-site scripting (XSS), and cross-site request forgery (CSRF), providing definitions, defenses, and further reading resources for each. It emphasizes preventive measures such as validating input, using parameterized queries, and implementing strong password policies to mitigate these threats. Additionally, it covers best practices in session management and the importance of secure authentication methods.