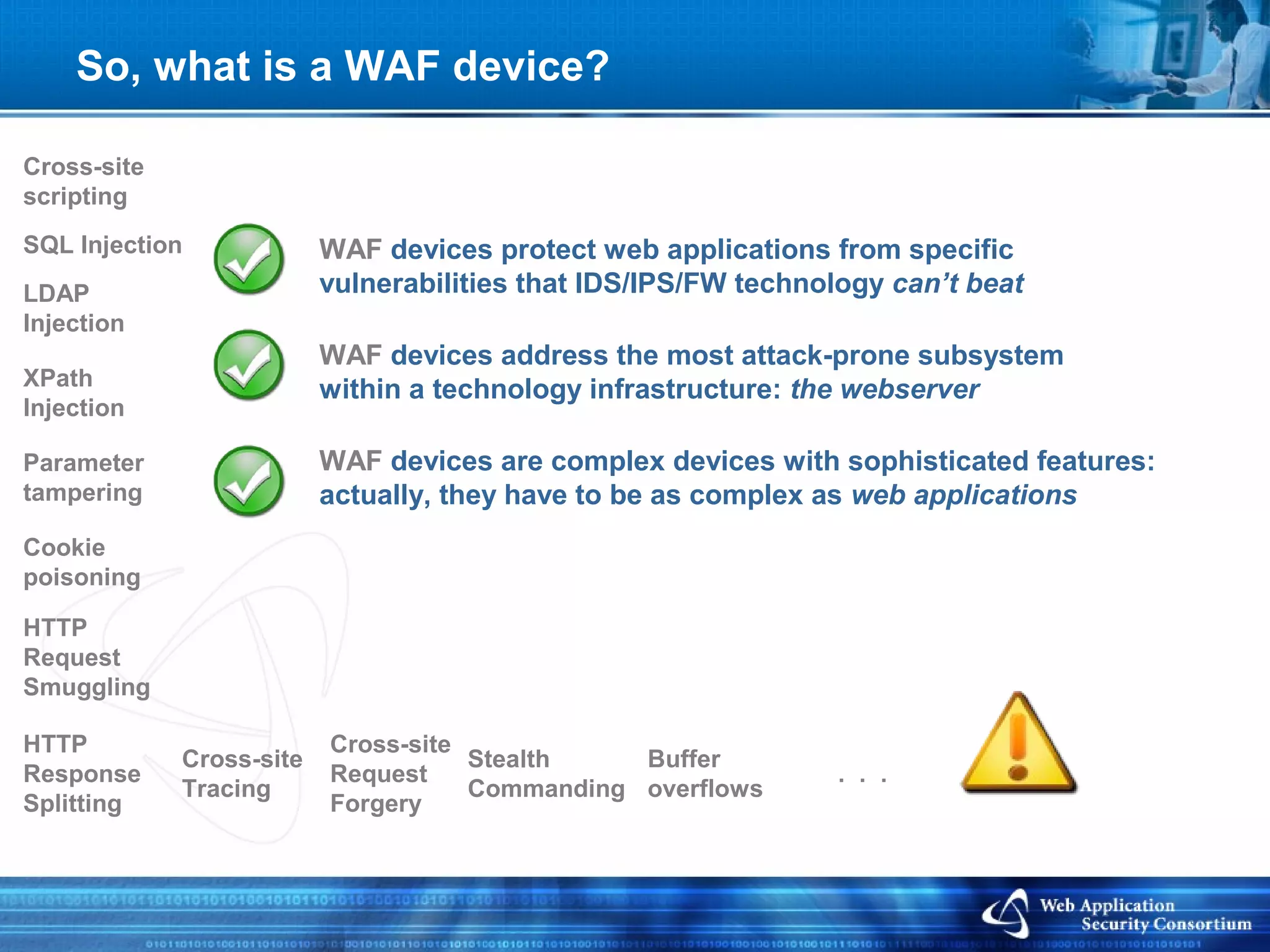
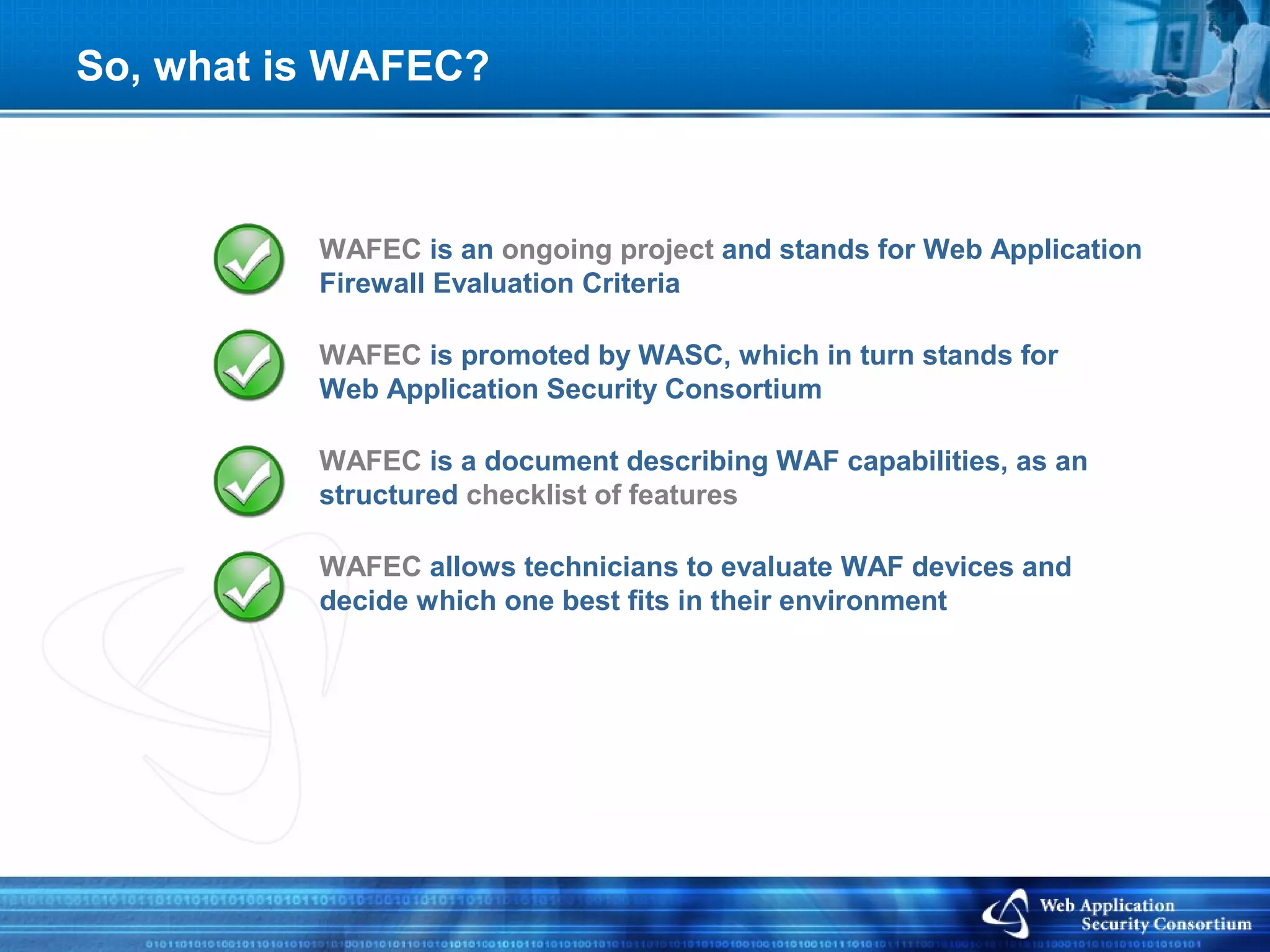
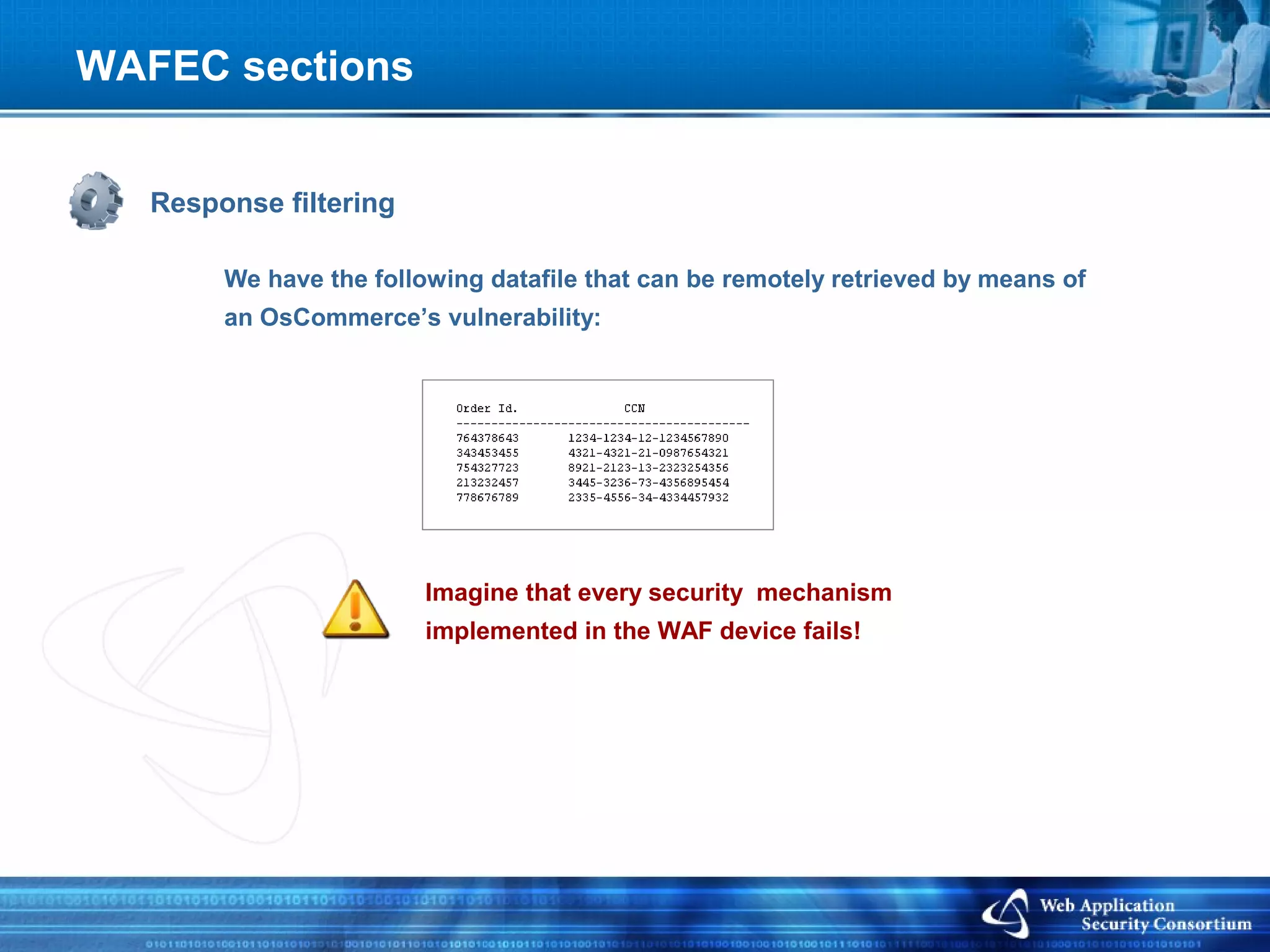
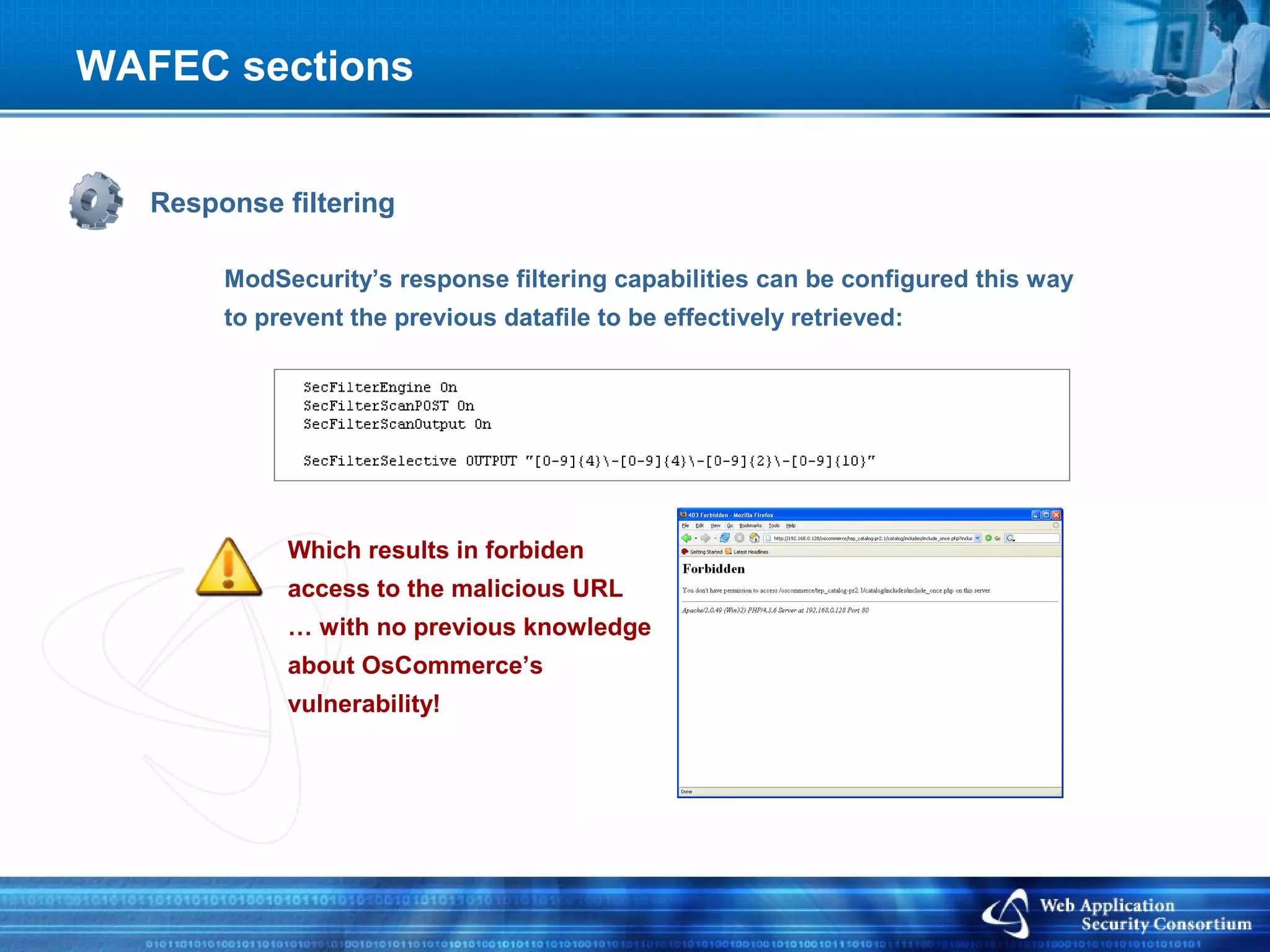
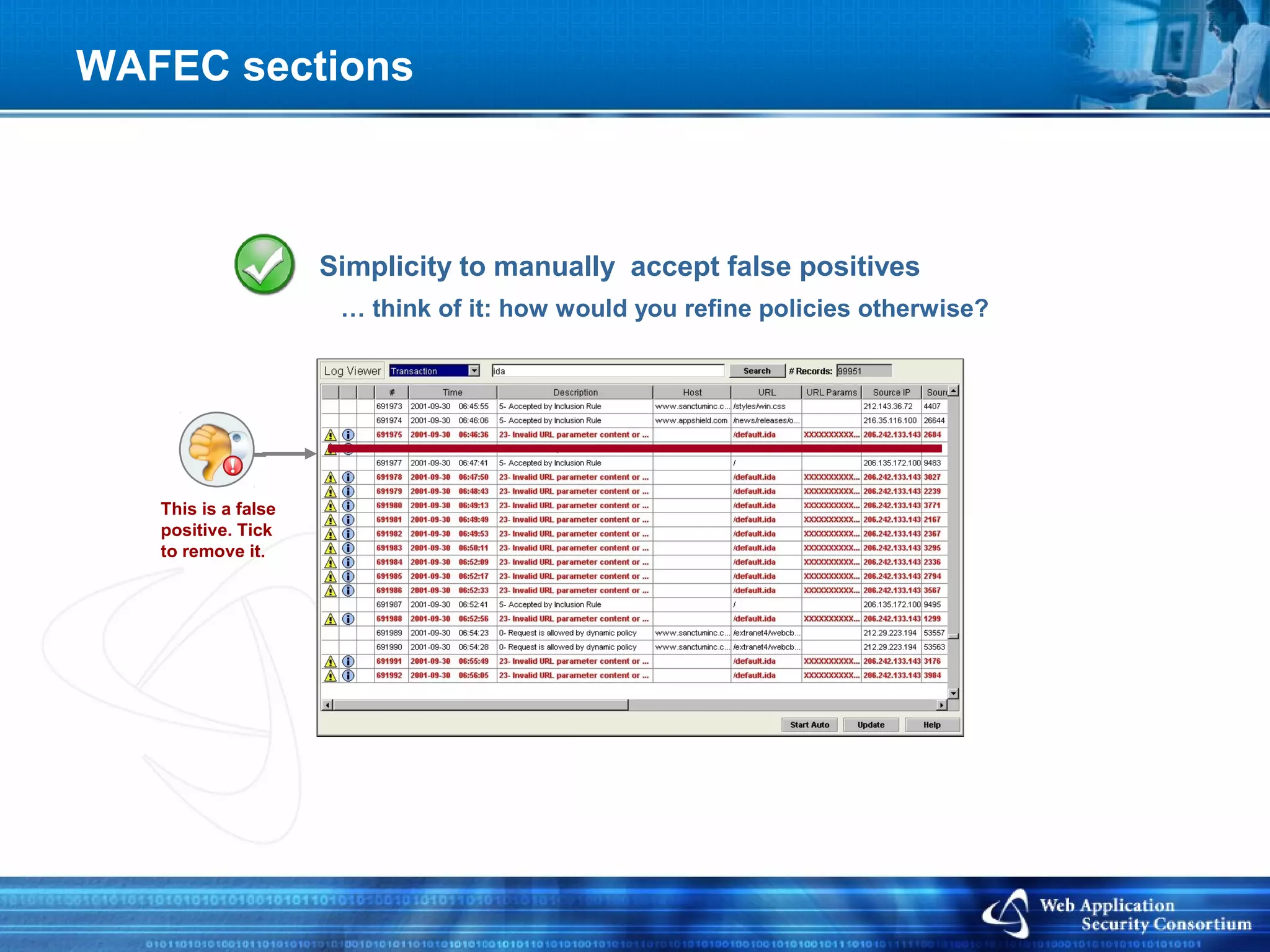
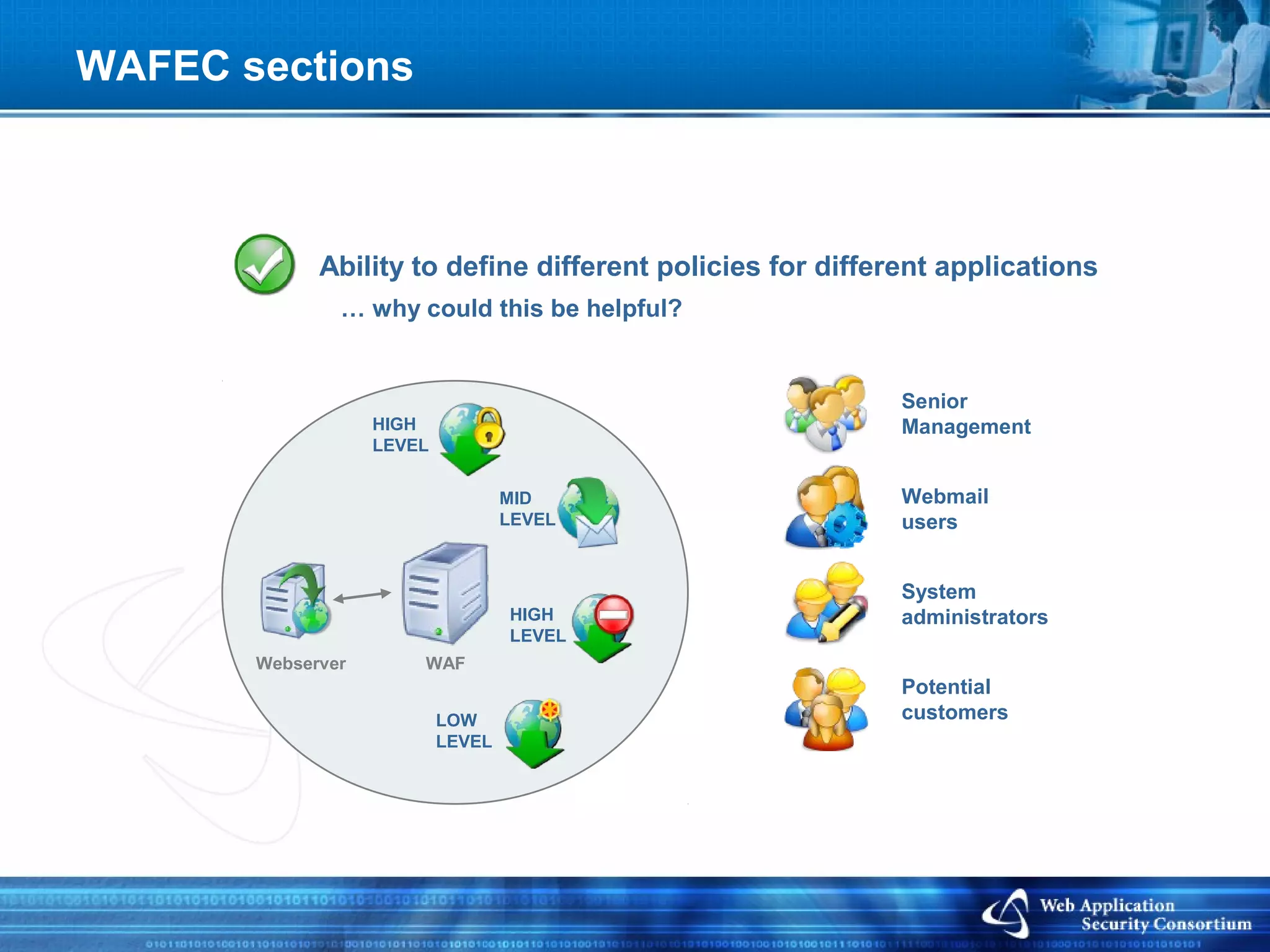
The document discusses WAFEC (Web Application Firewall Evaluation Criteria), which is a structured checklist created by WASC to help technicians evaluate and select WAF devices. It describes what WAFEC covers, including the capabilities, features, deployment options, detection techniques, and protection mechanisms of WAF technologies. The goal of WAFEC is to provide clarity in an emerging market that can be confusing due to marketing influences and the proliferation of WAF vendors and products.