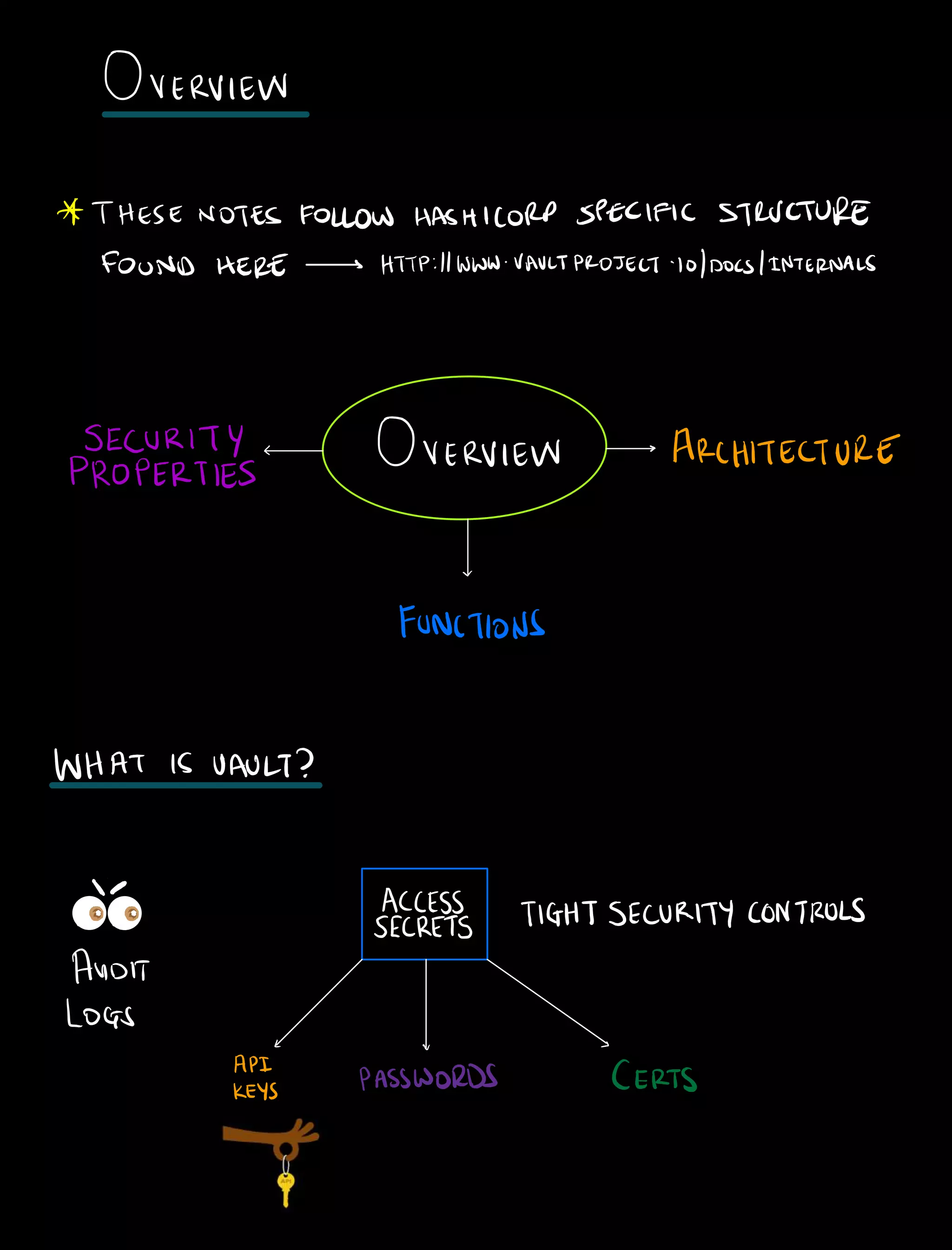
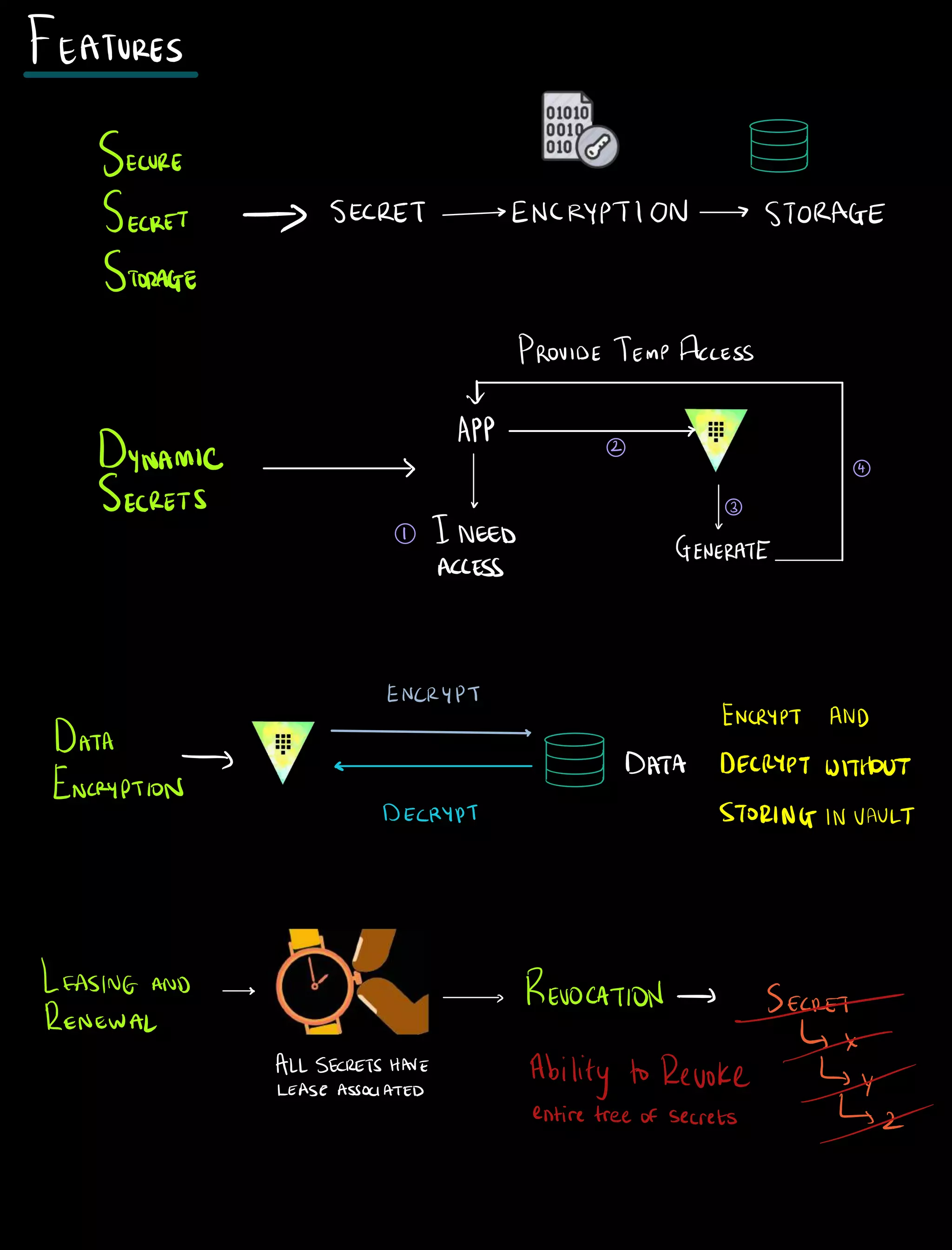
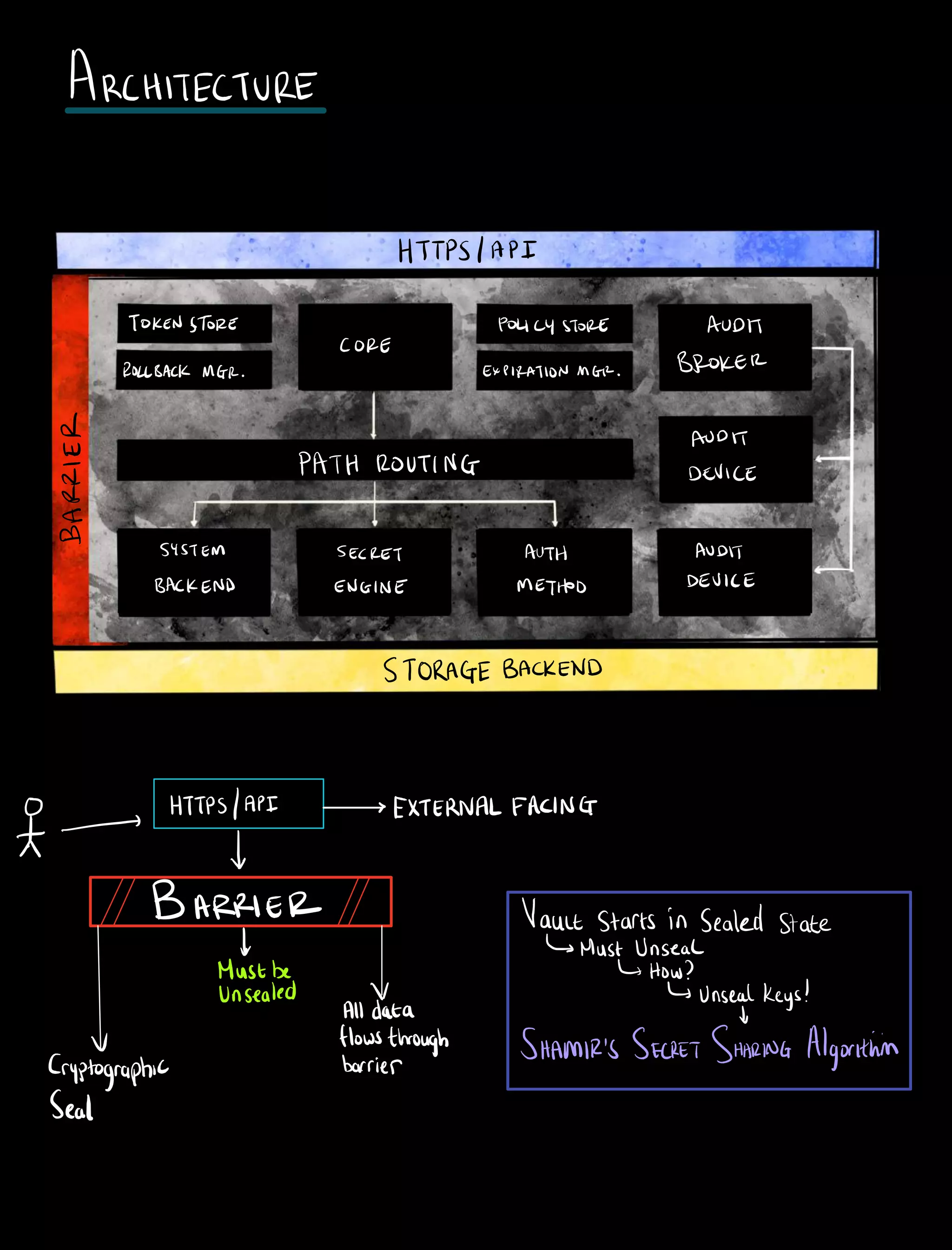
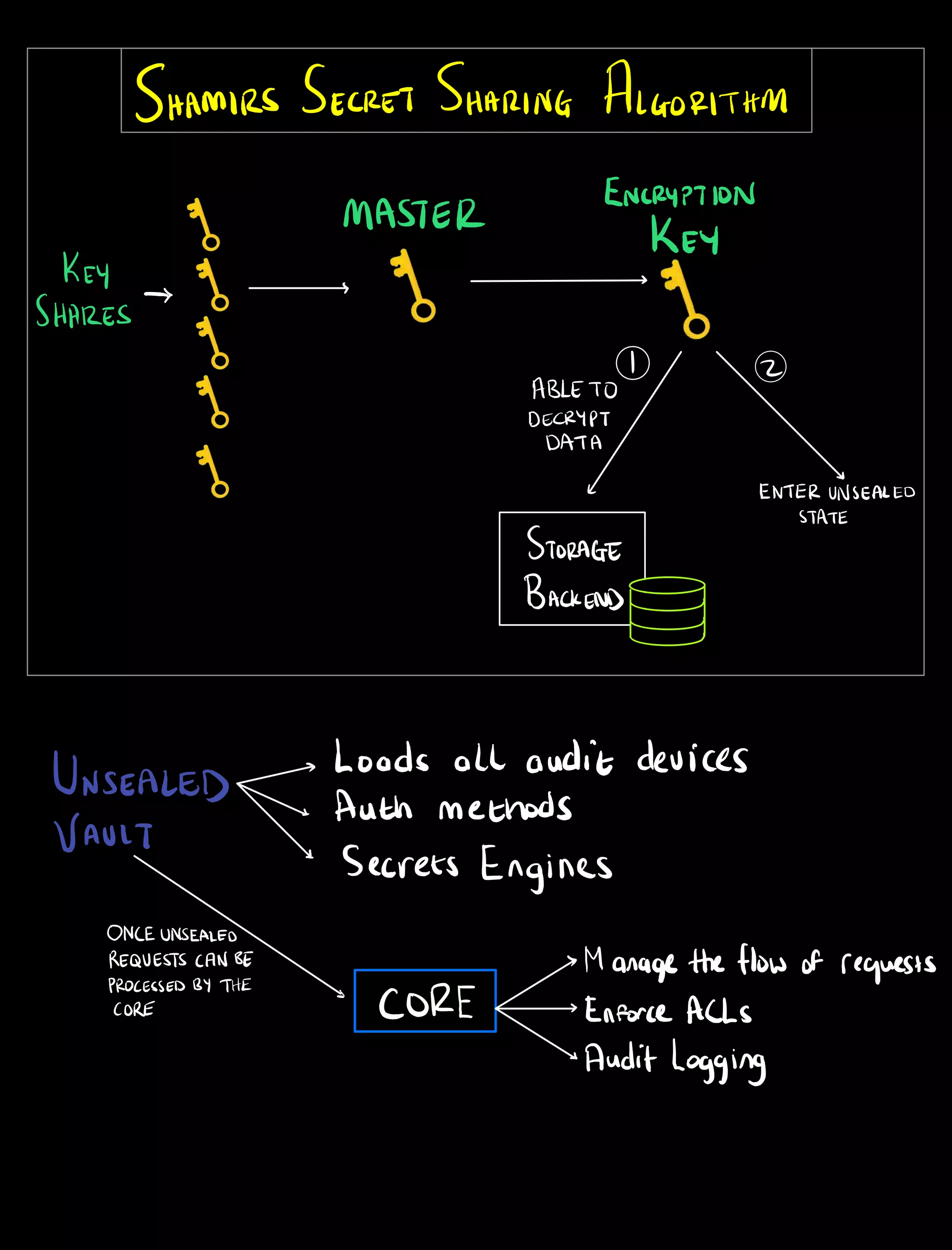
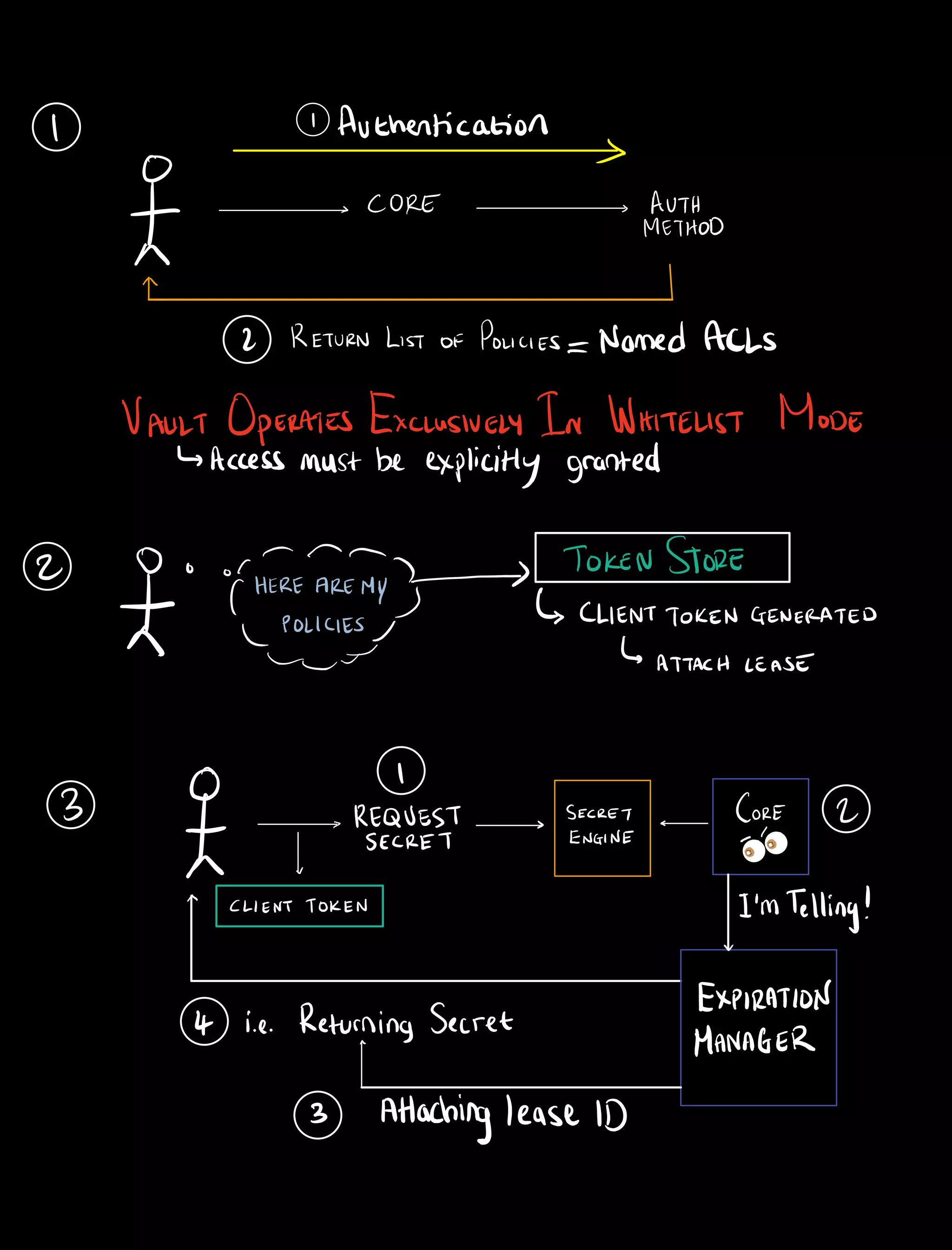
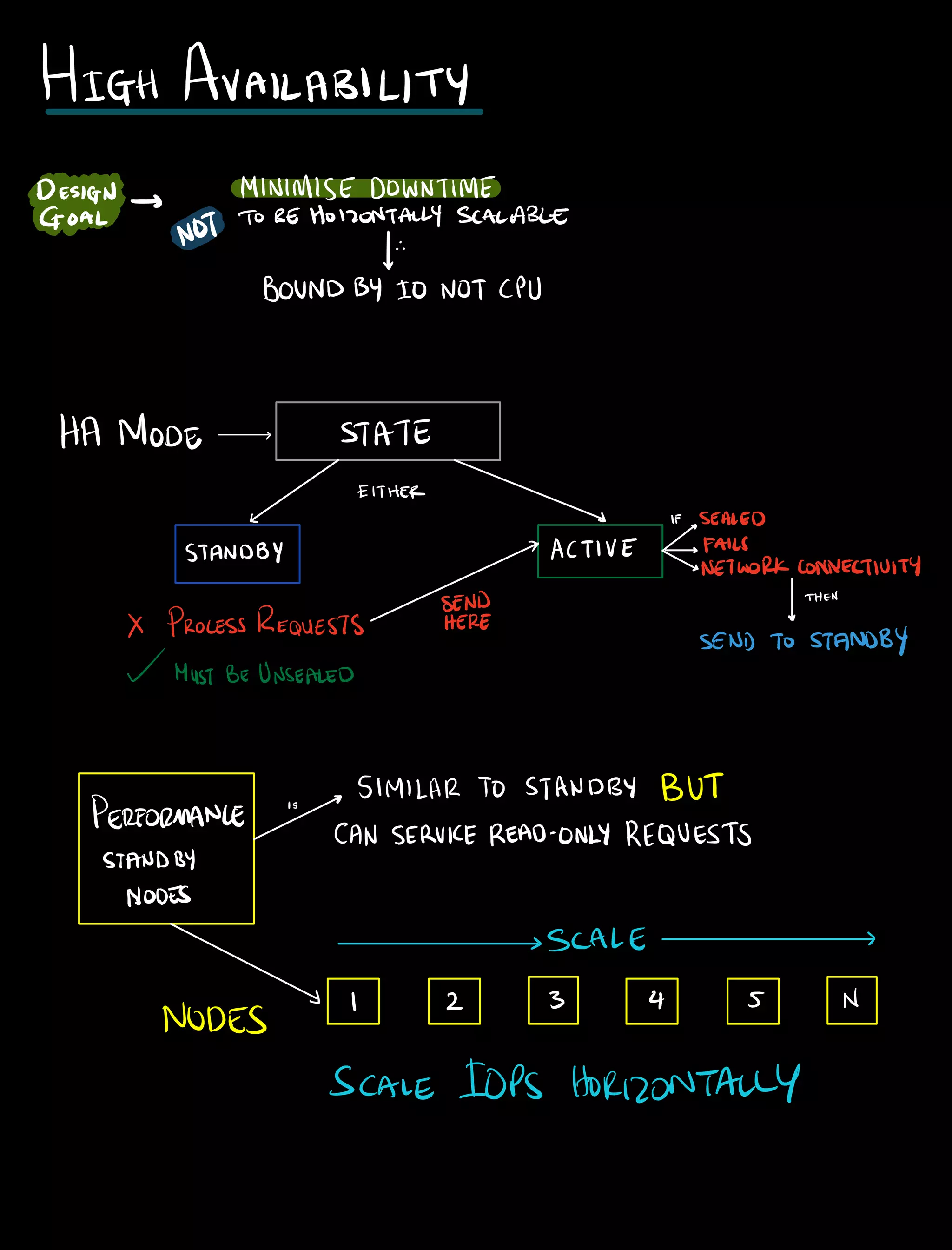
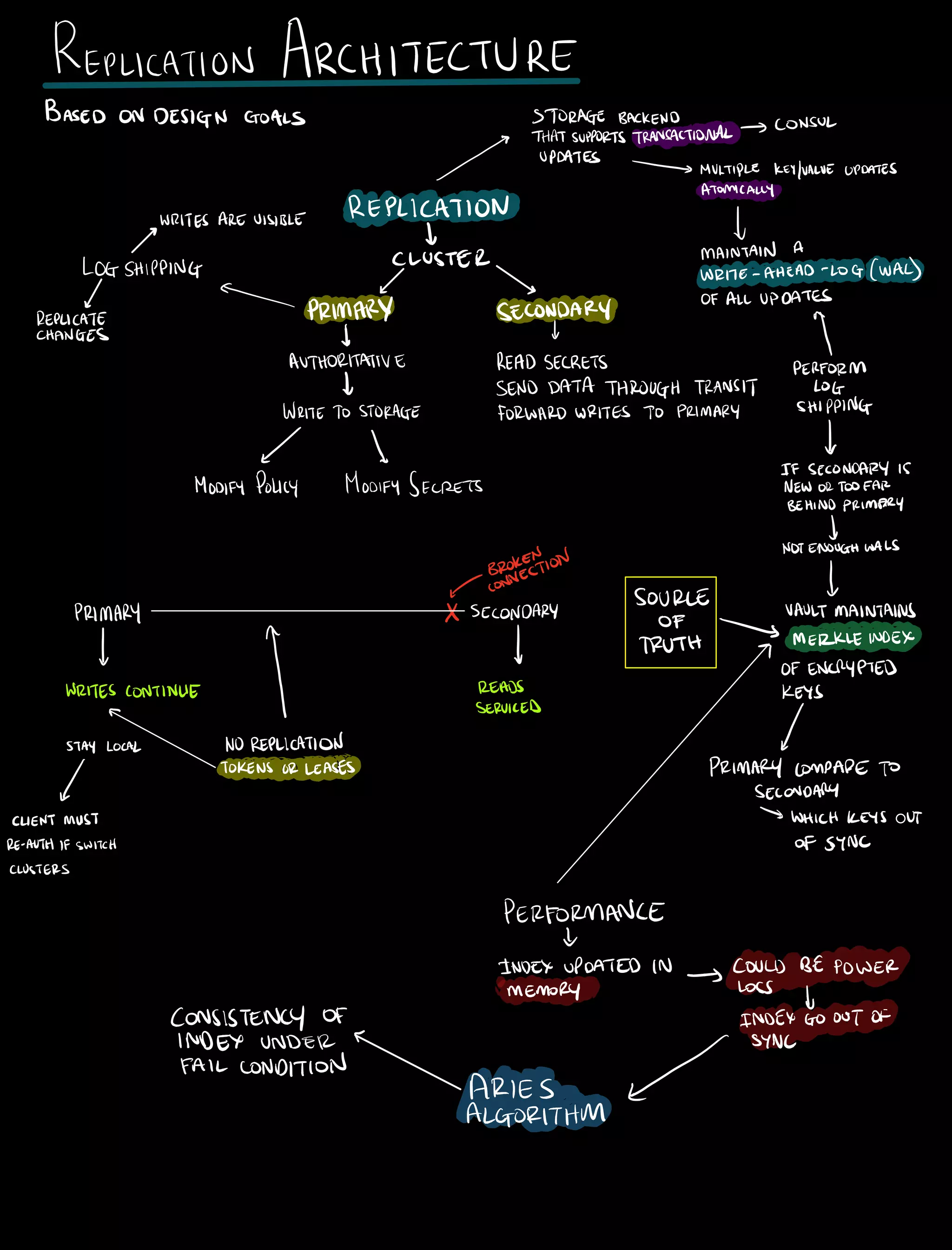
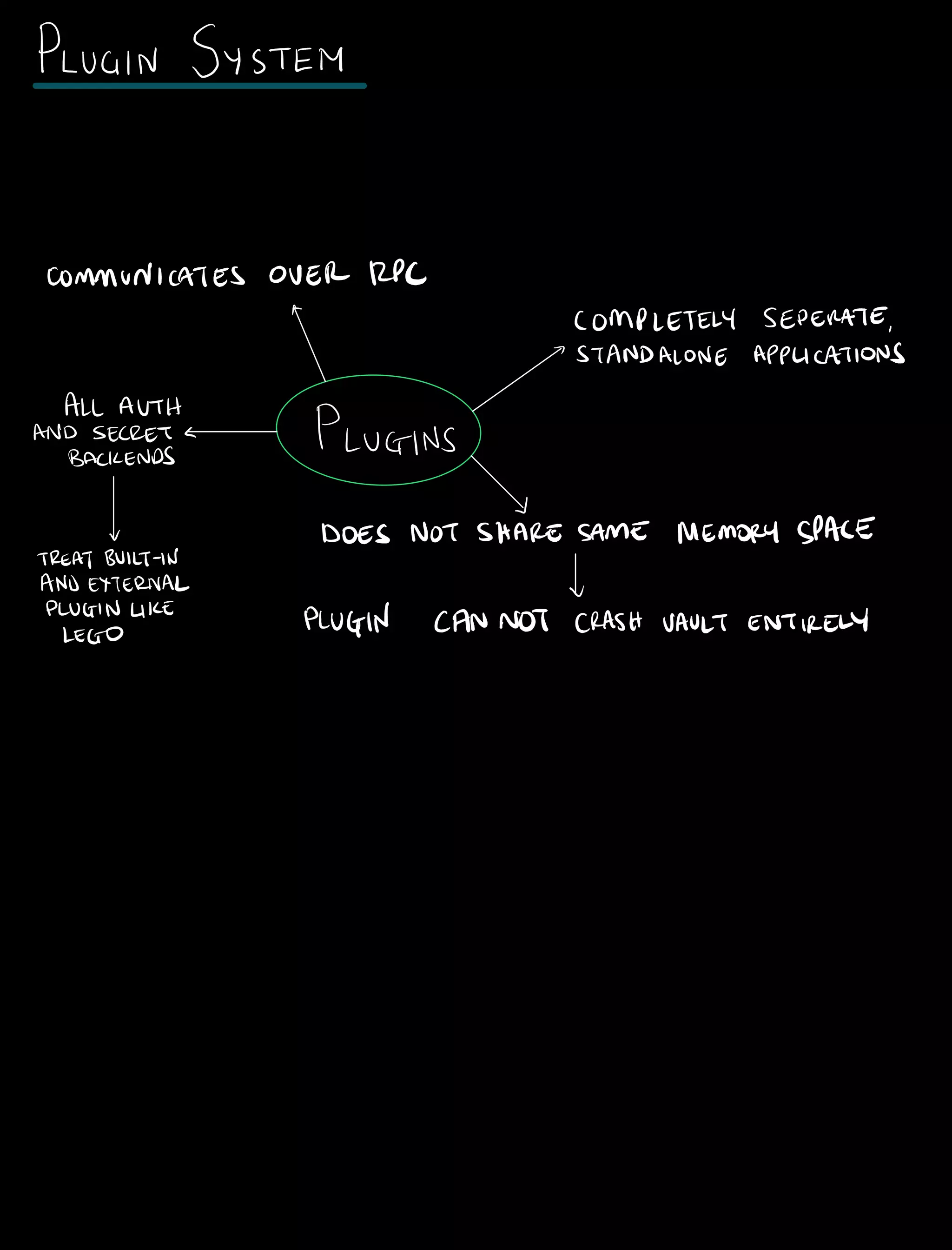
This document provides a detailed overview of HashiCorp Vault, covering its architecture, security features, and operational functionalities. It emphasizes secure secret management, leasing and revocation of secrets, and high availability design through a consensus protocol. The text also discusses authentication mechanisms, token management, and a plugin system facilitating scalability and flexibility in deployments.