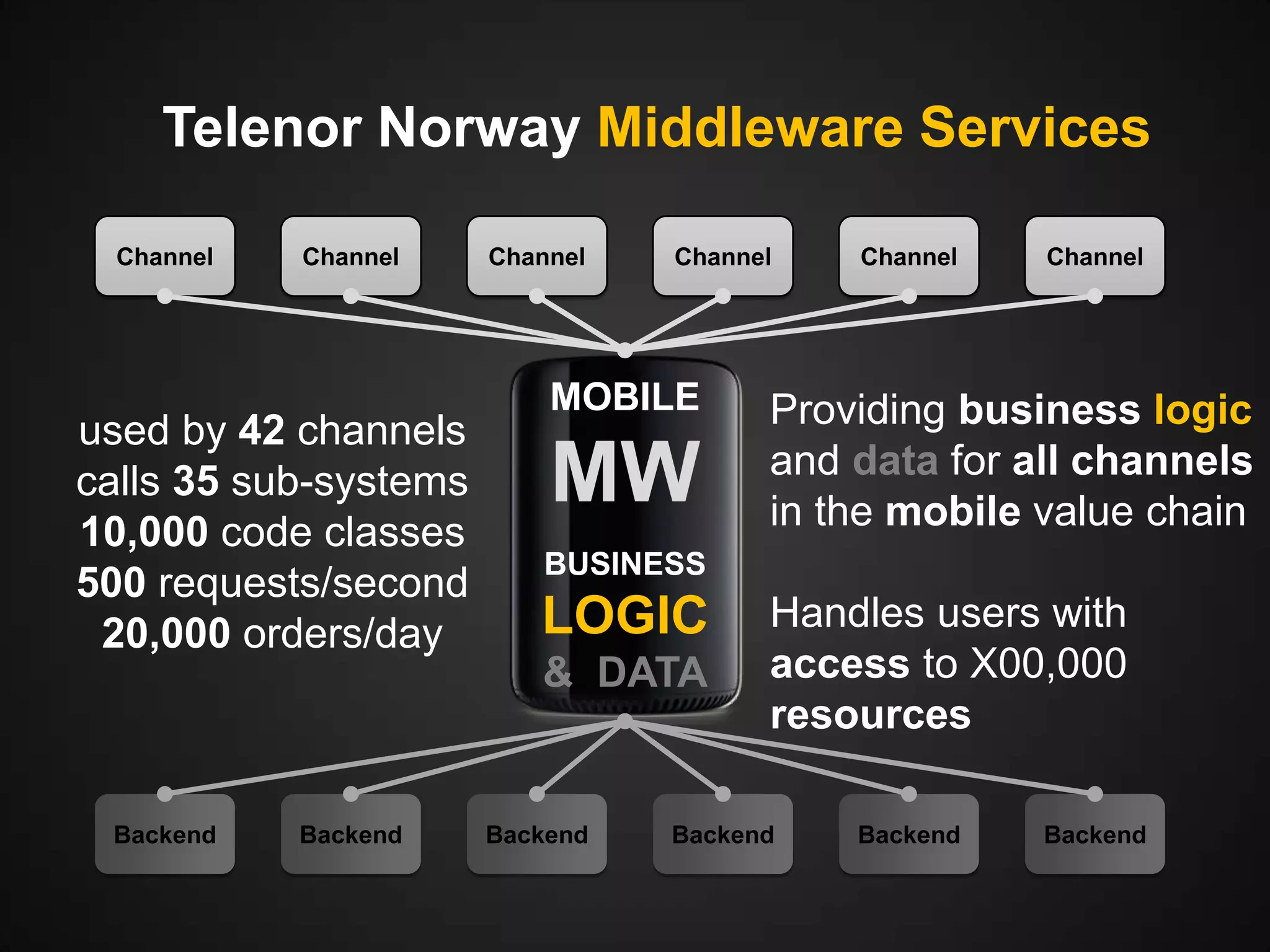
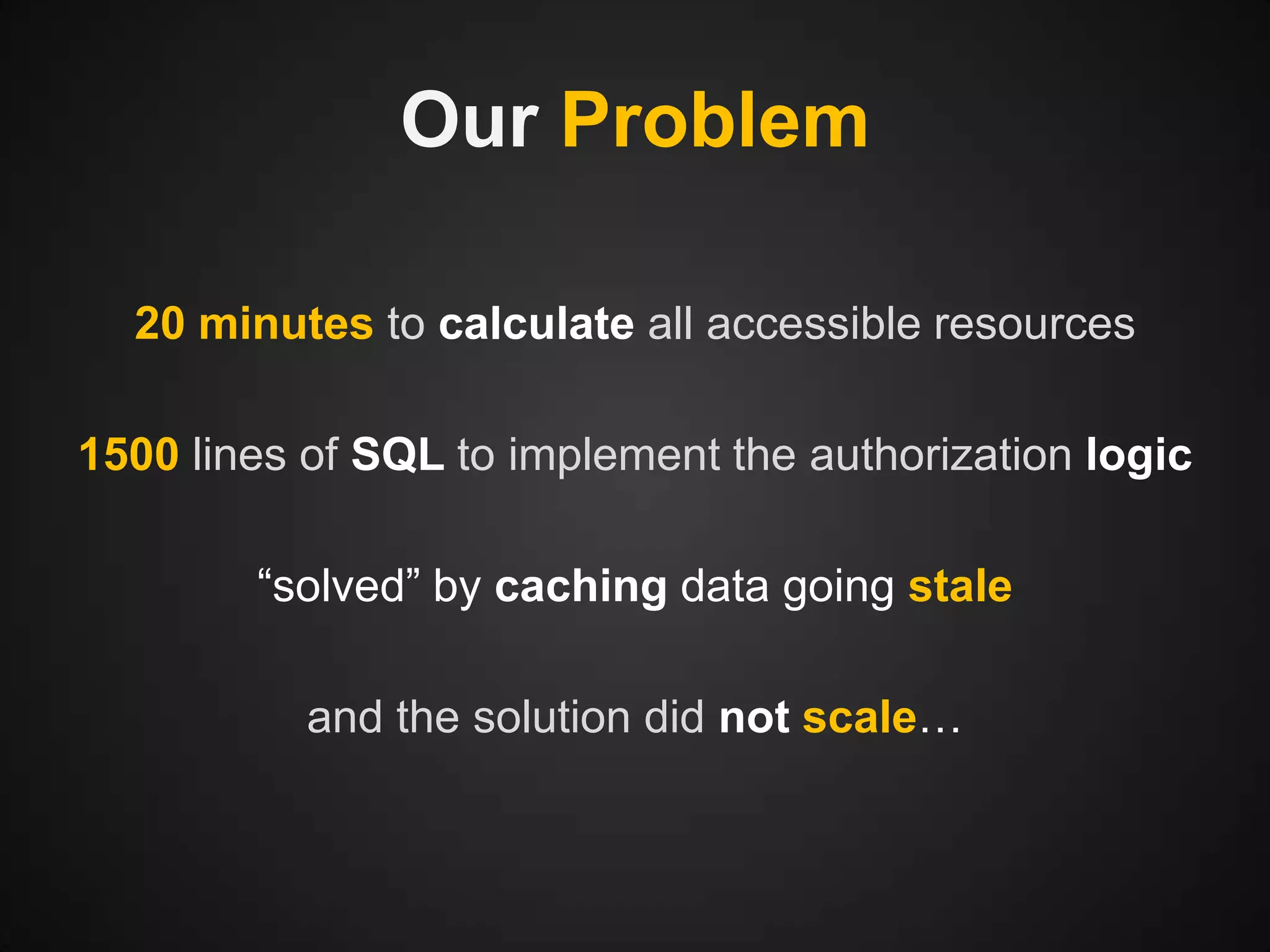
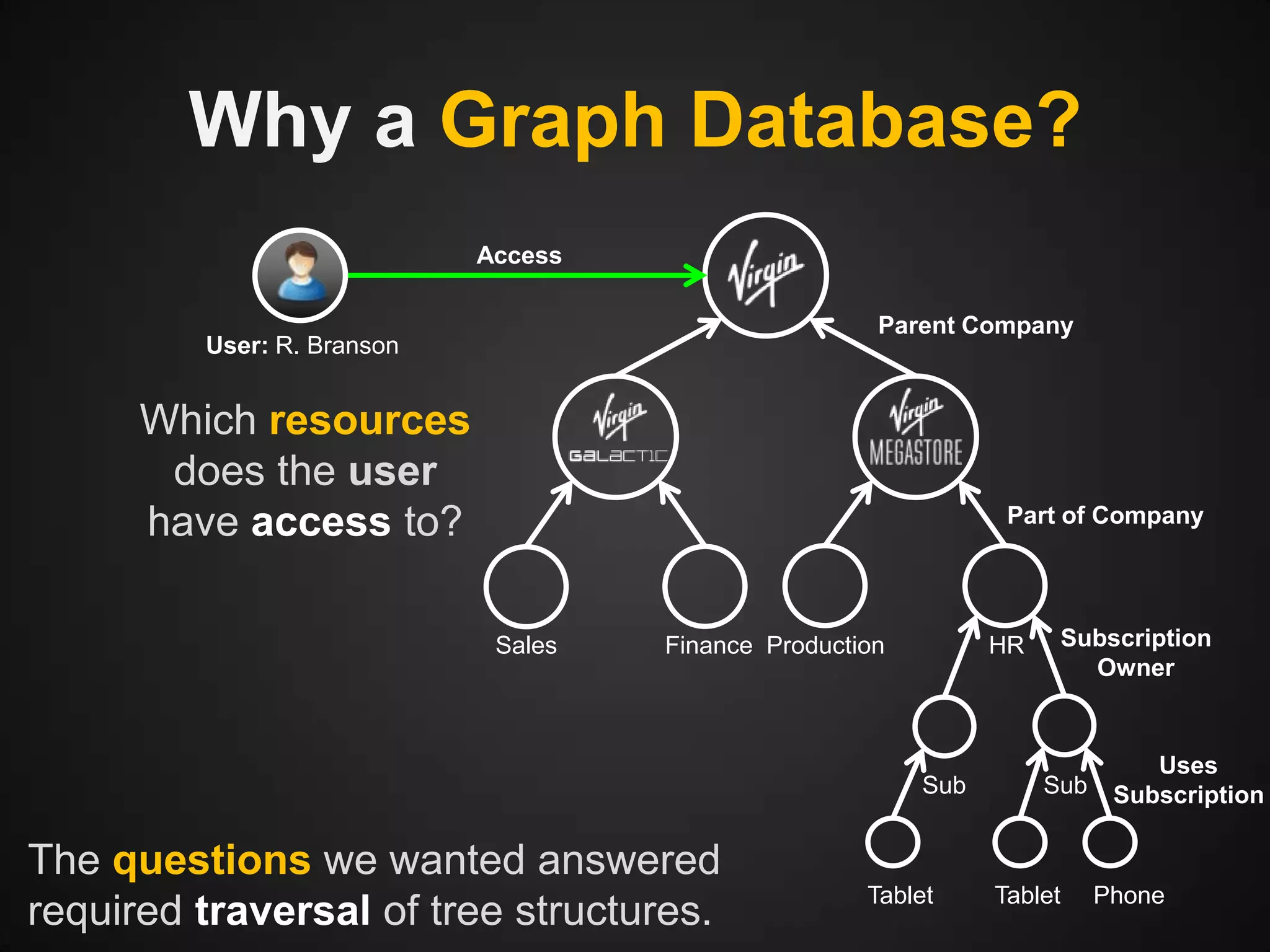
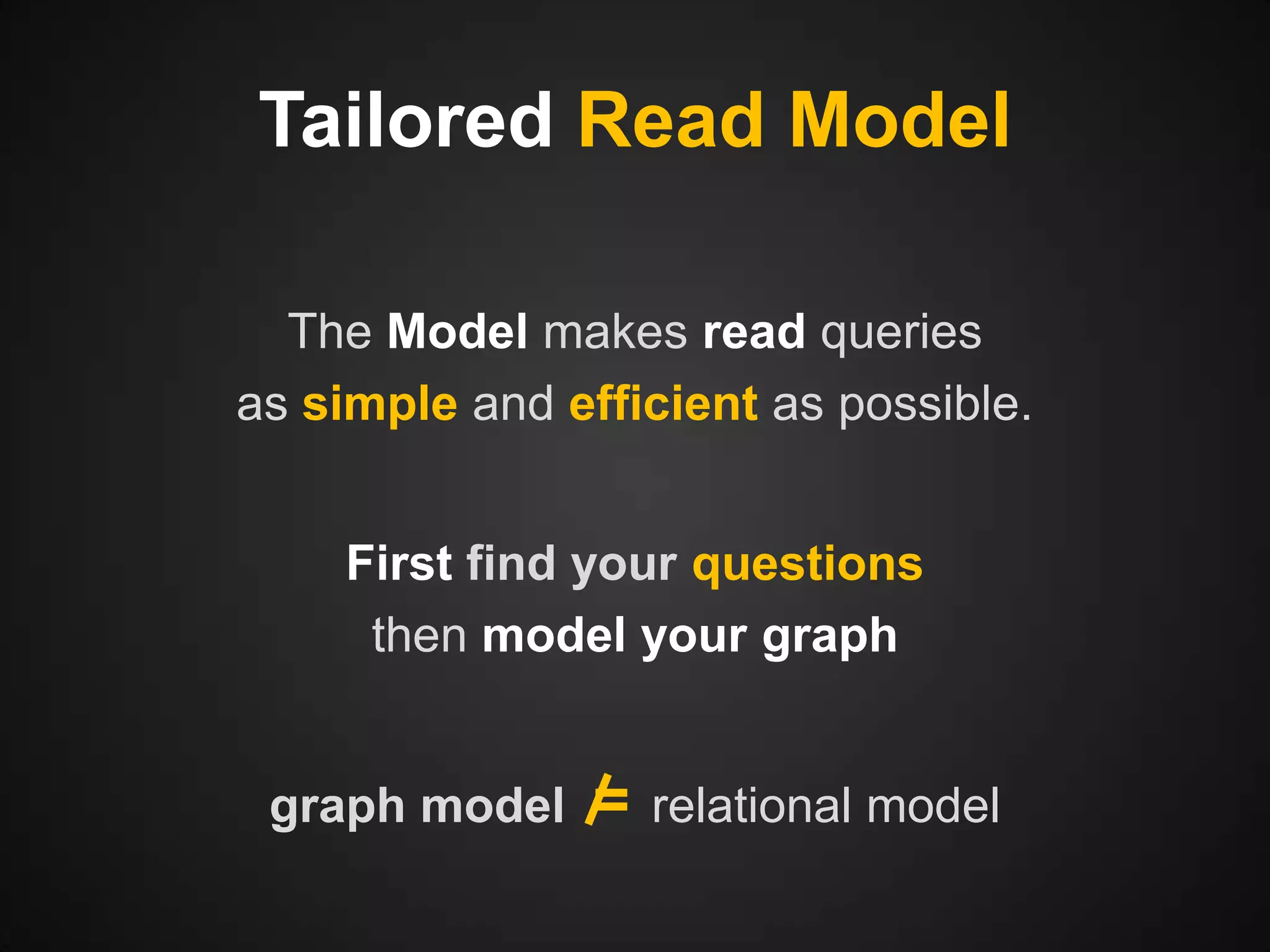
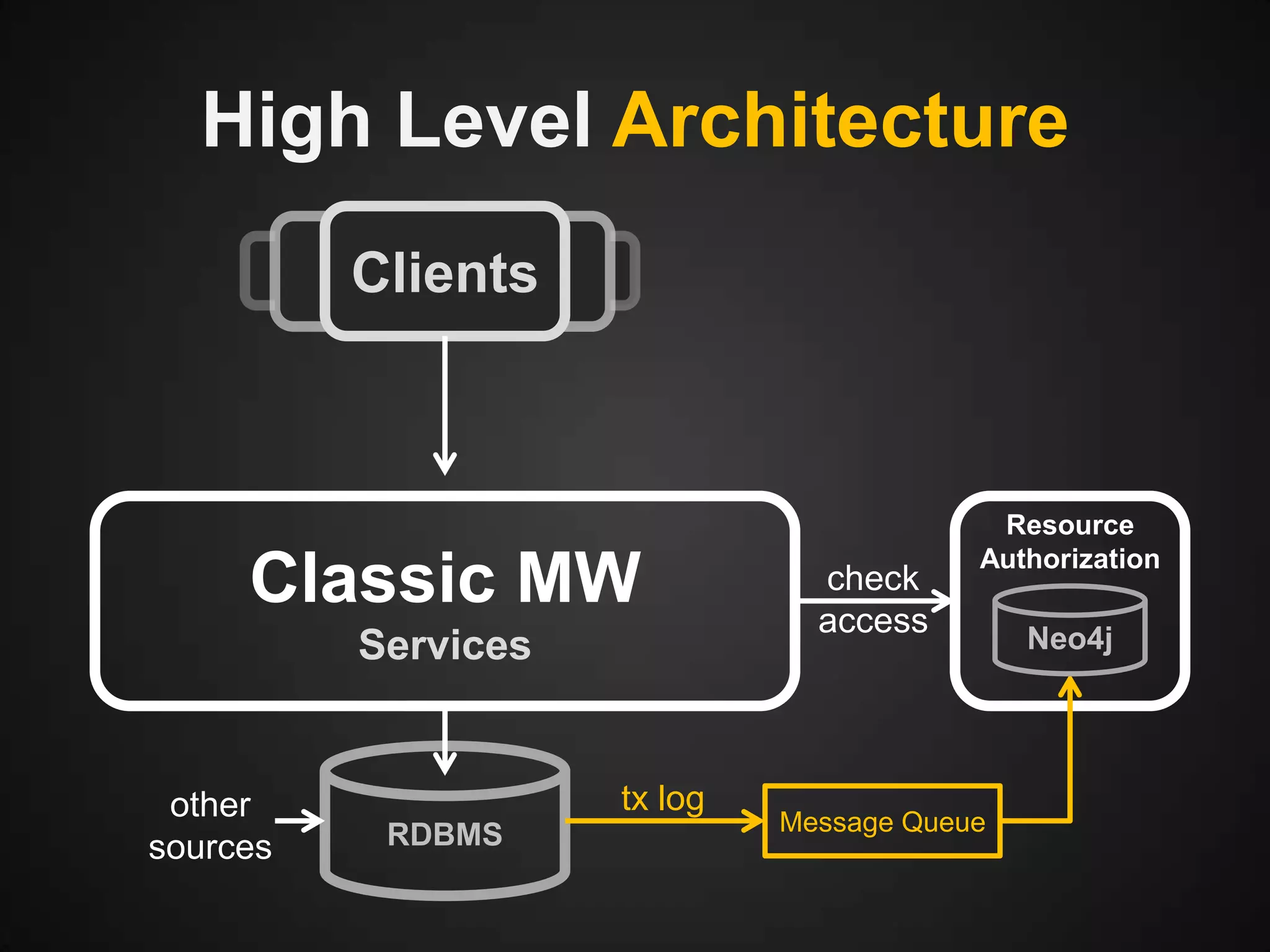
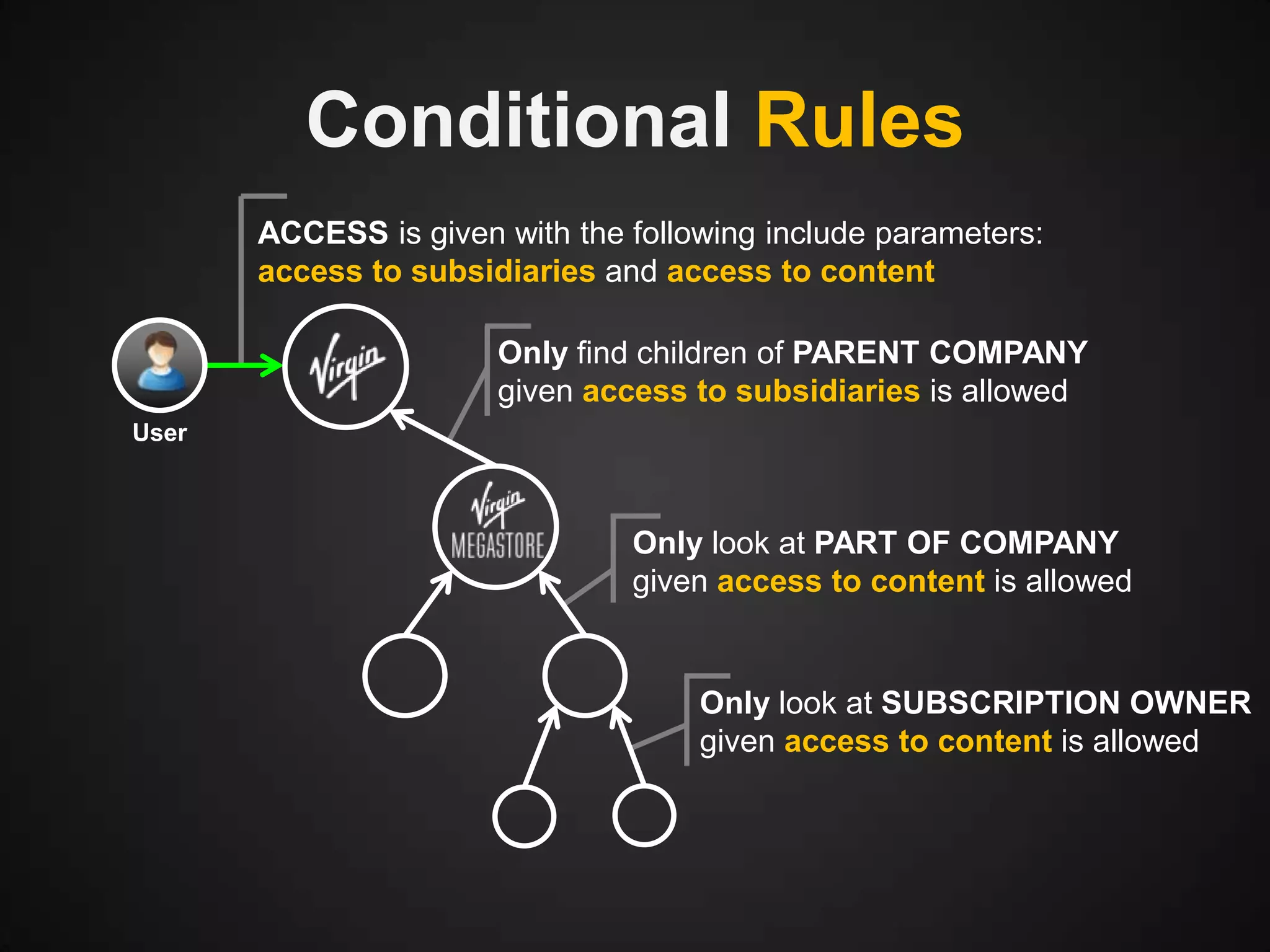
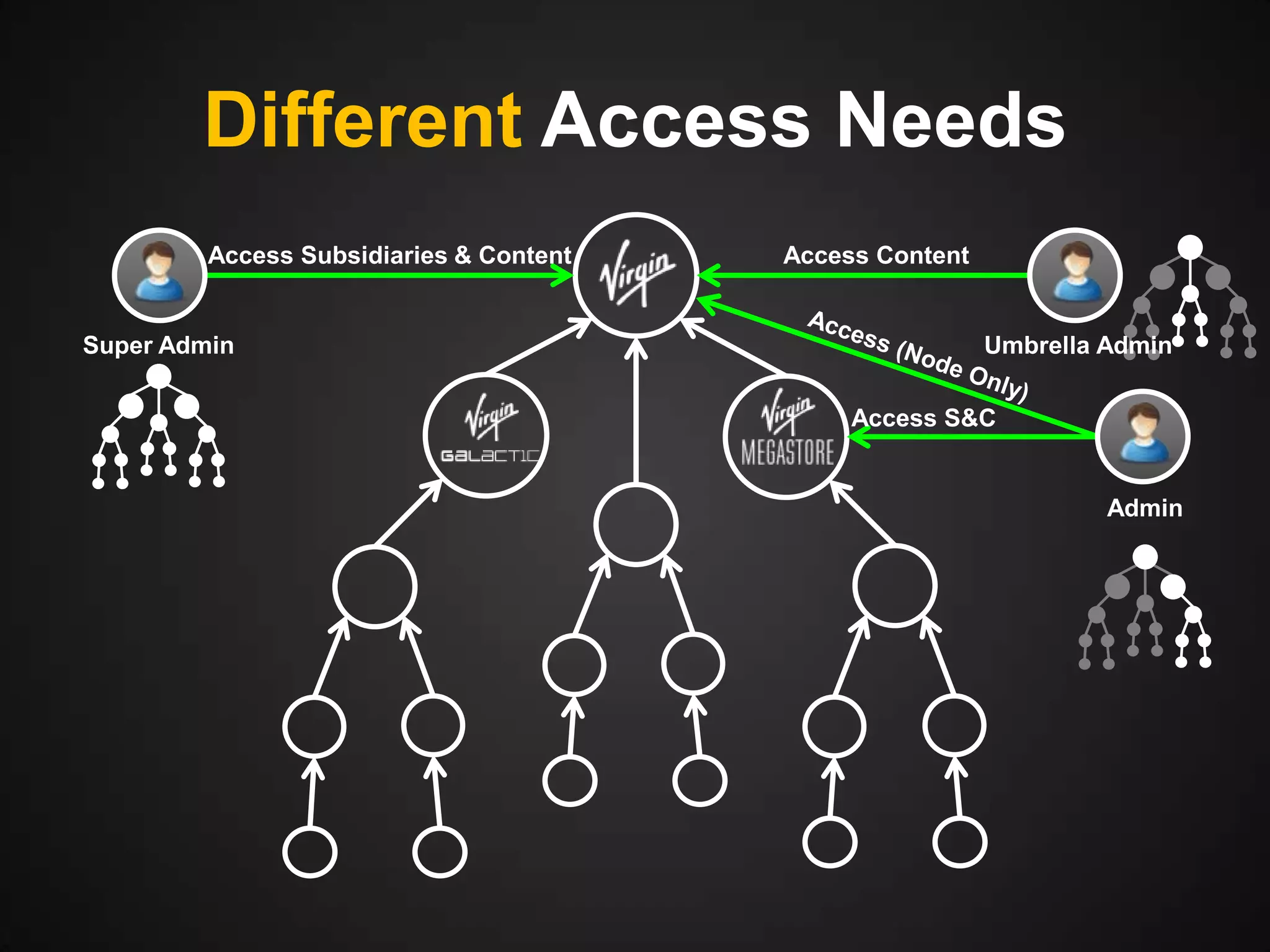
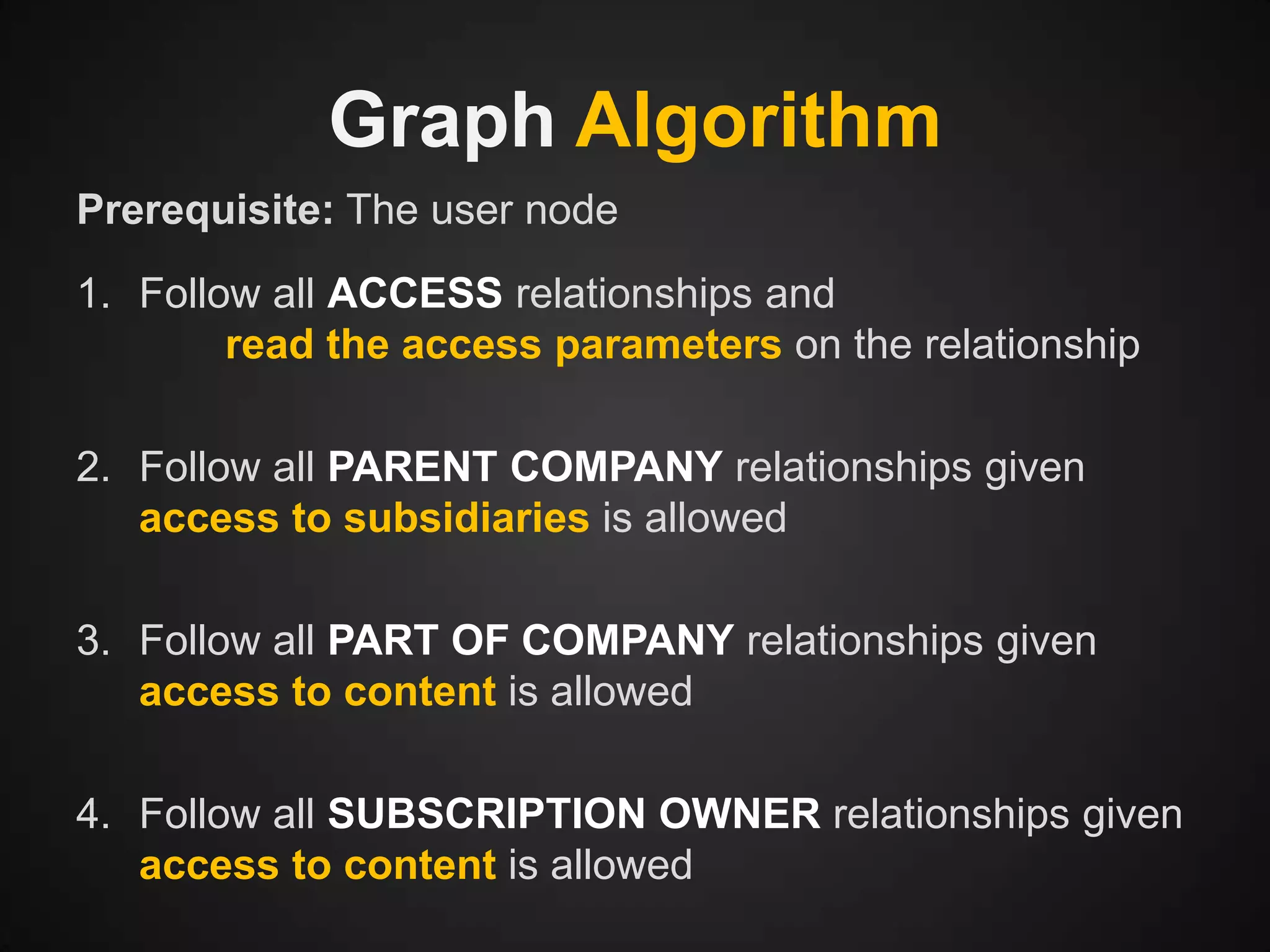
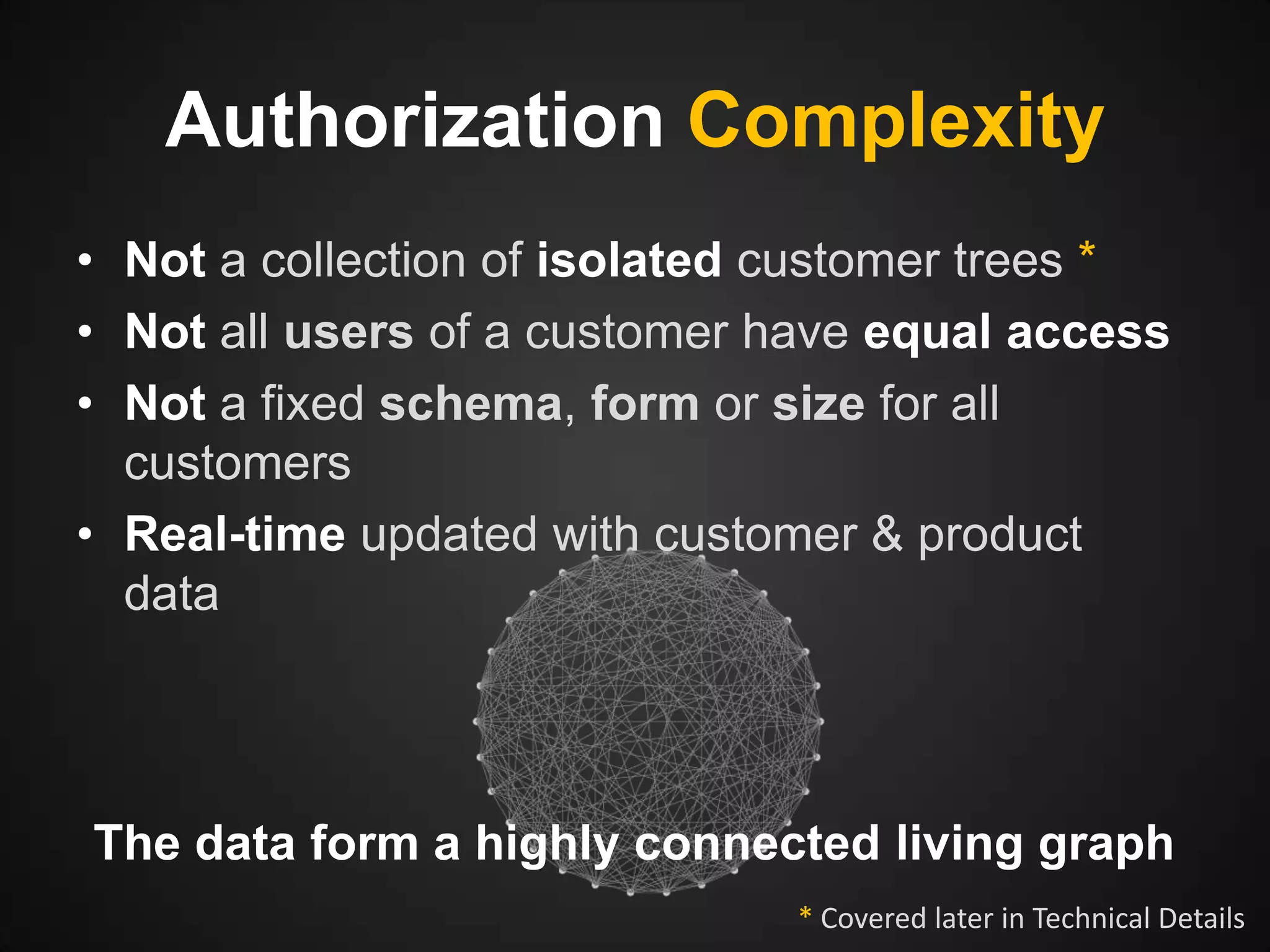
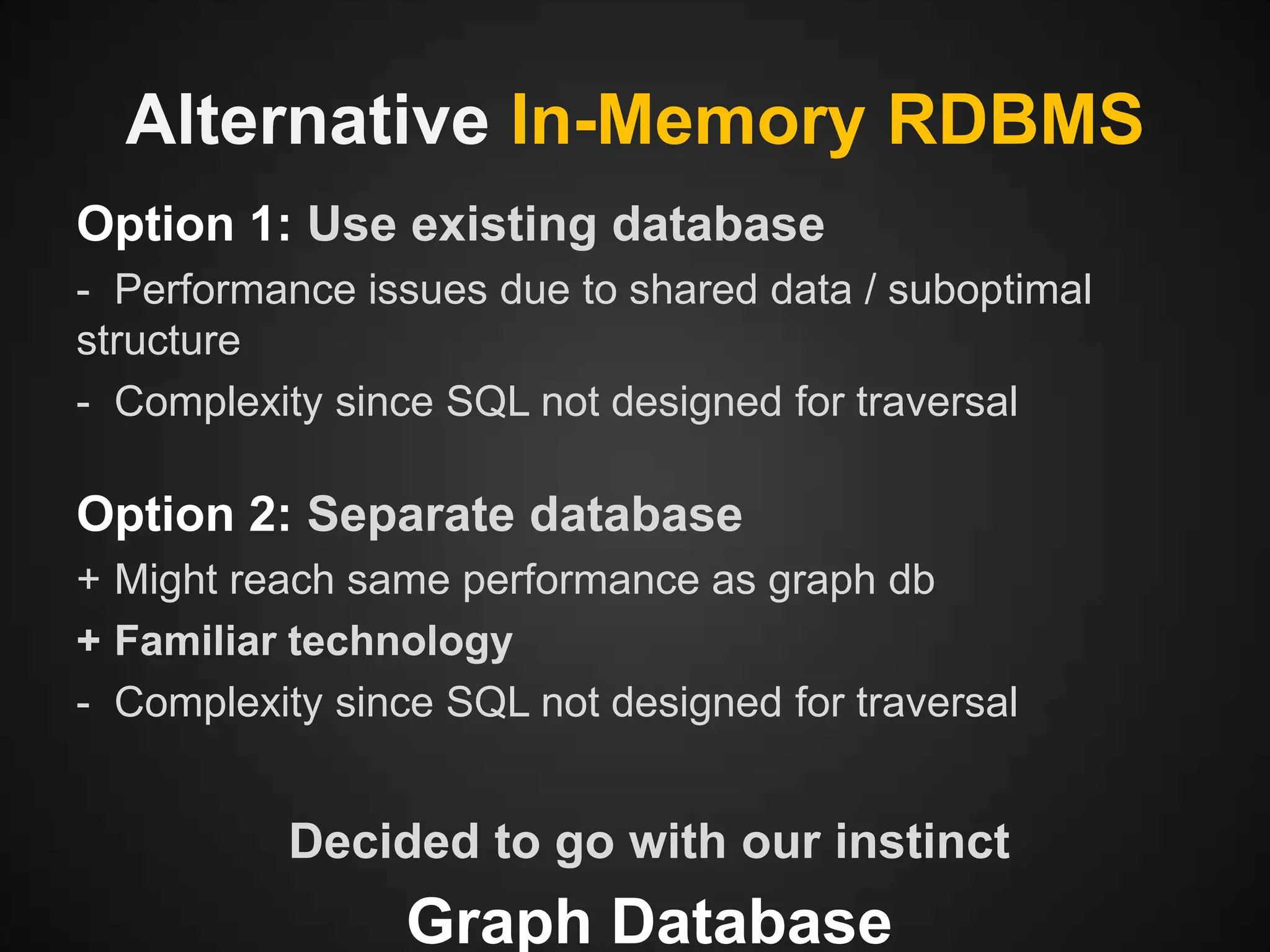
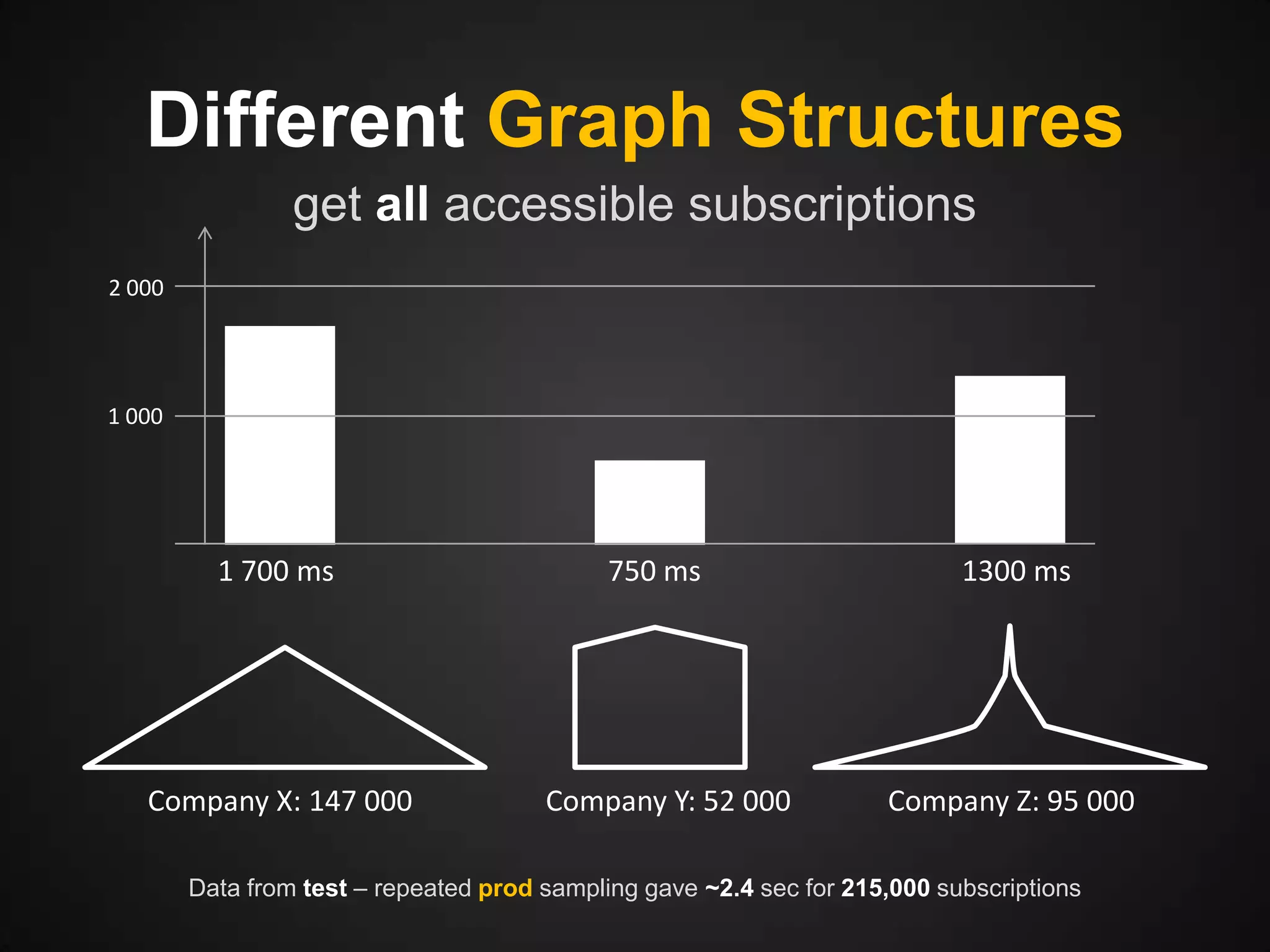
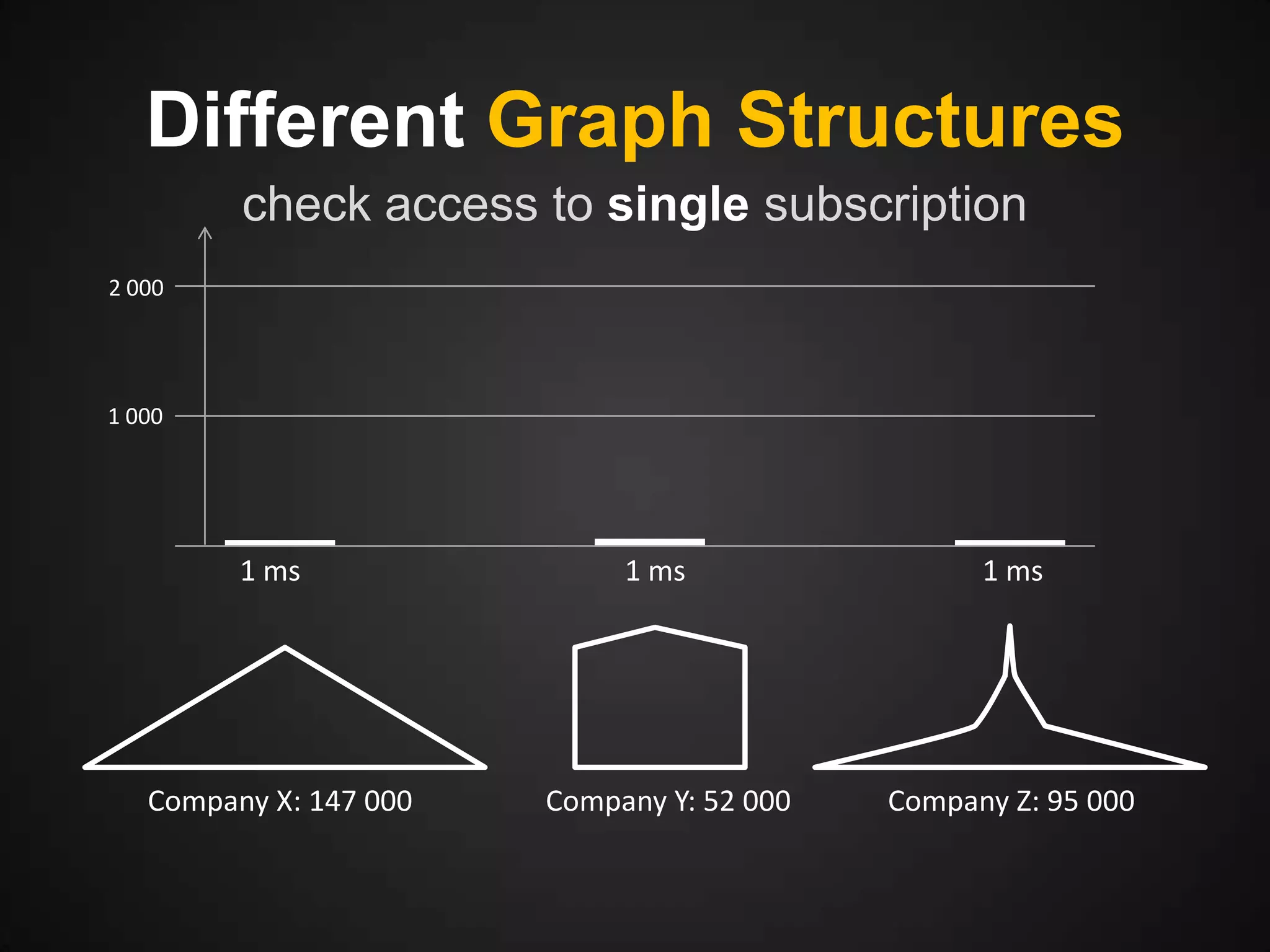
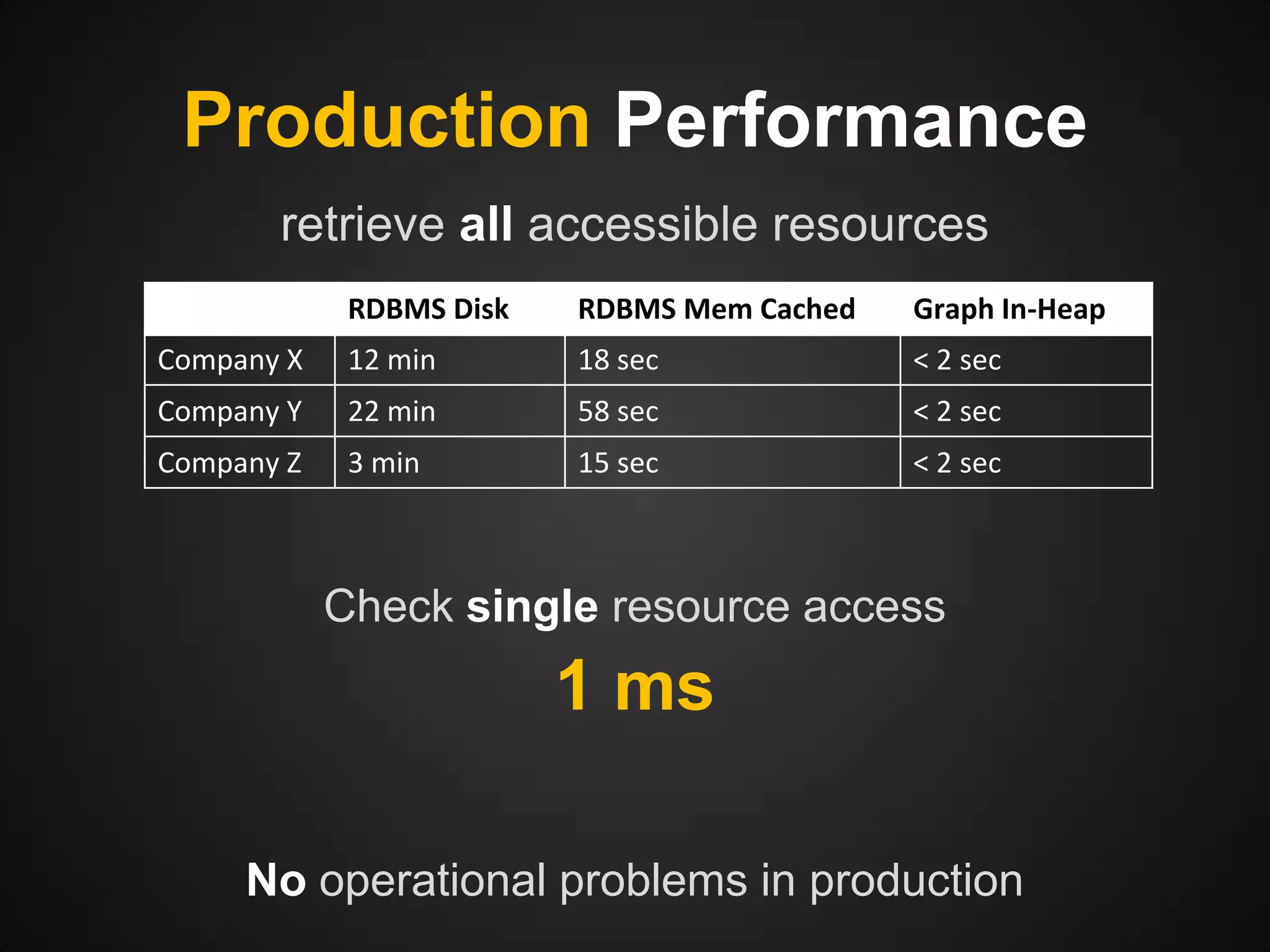
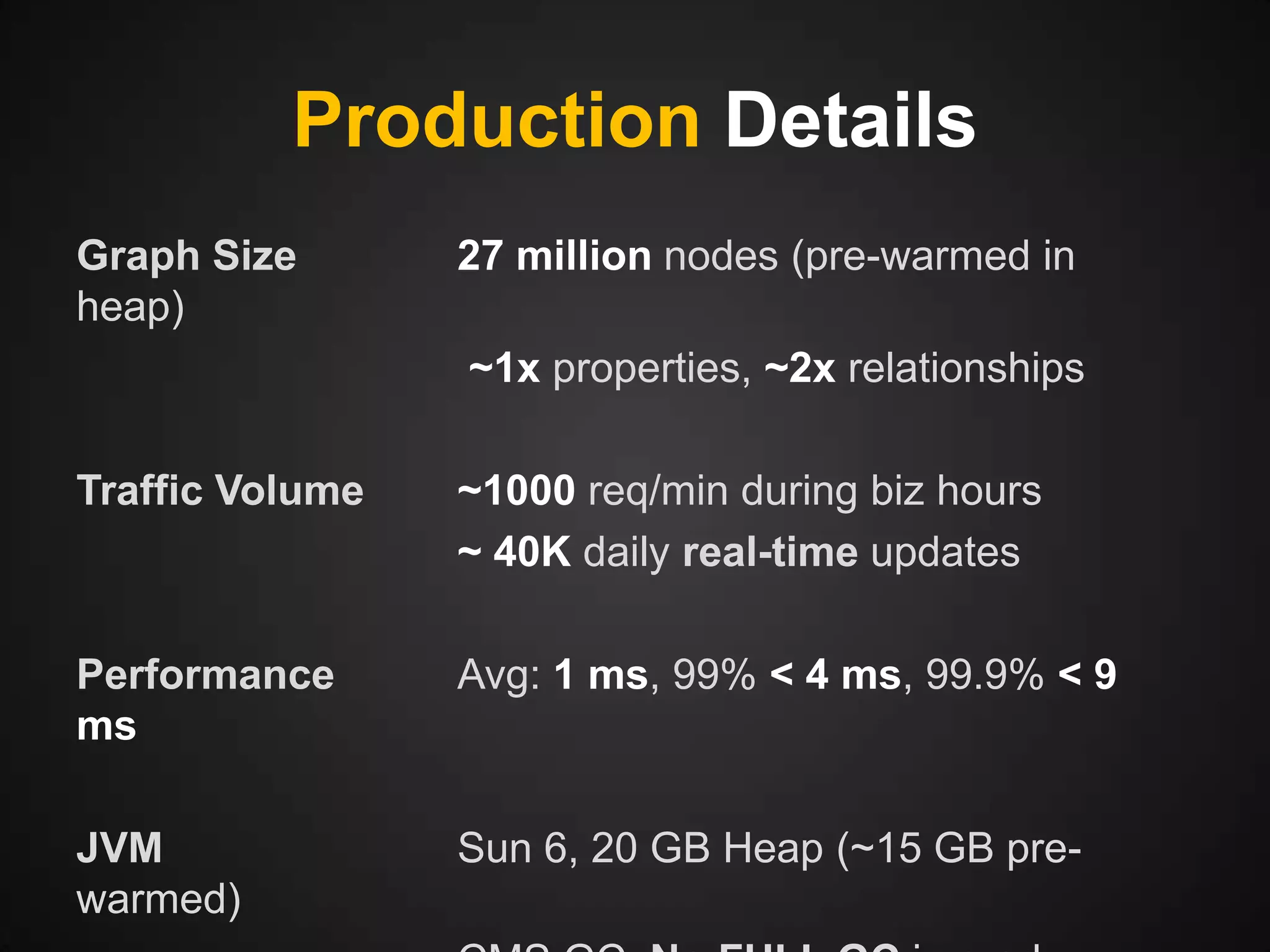
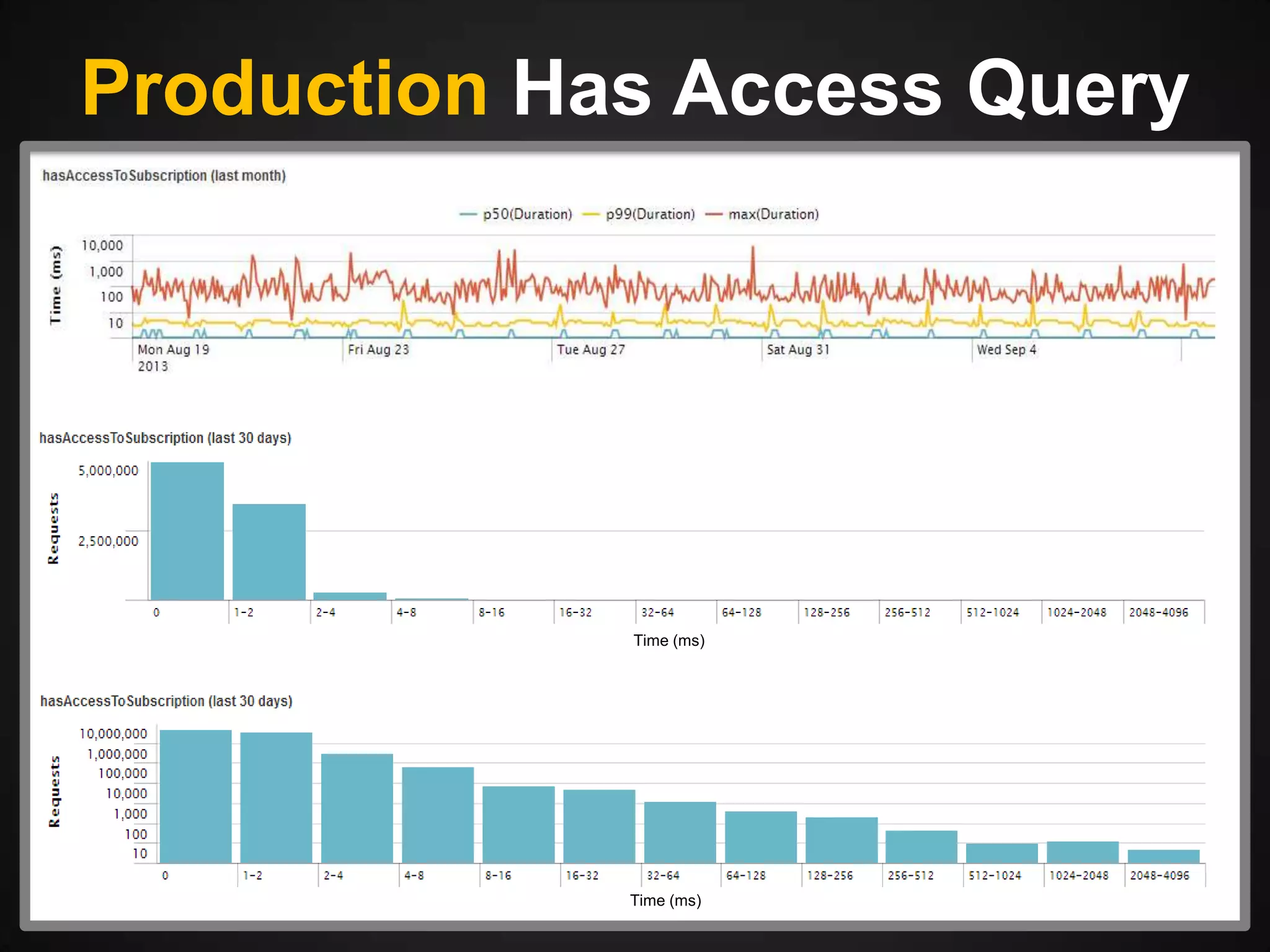
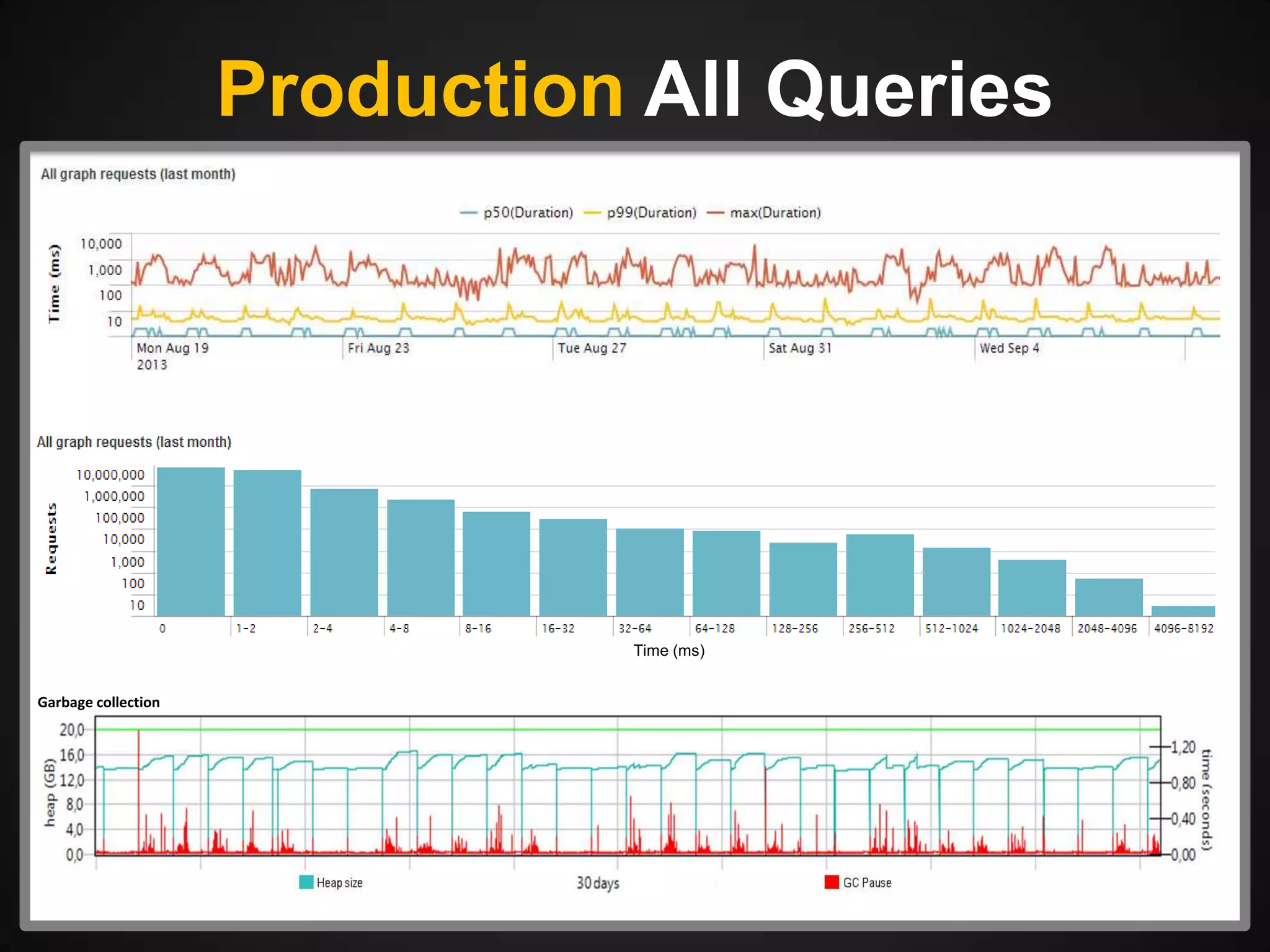
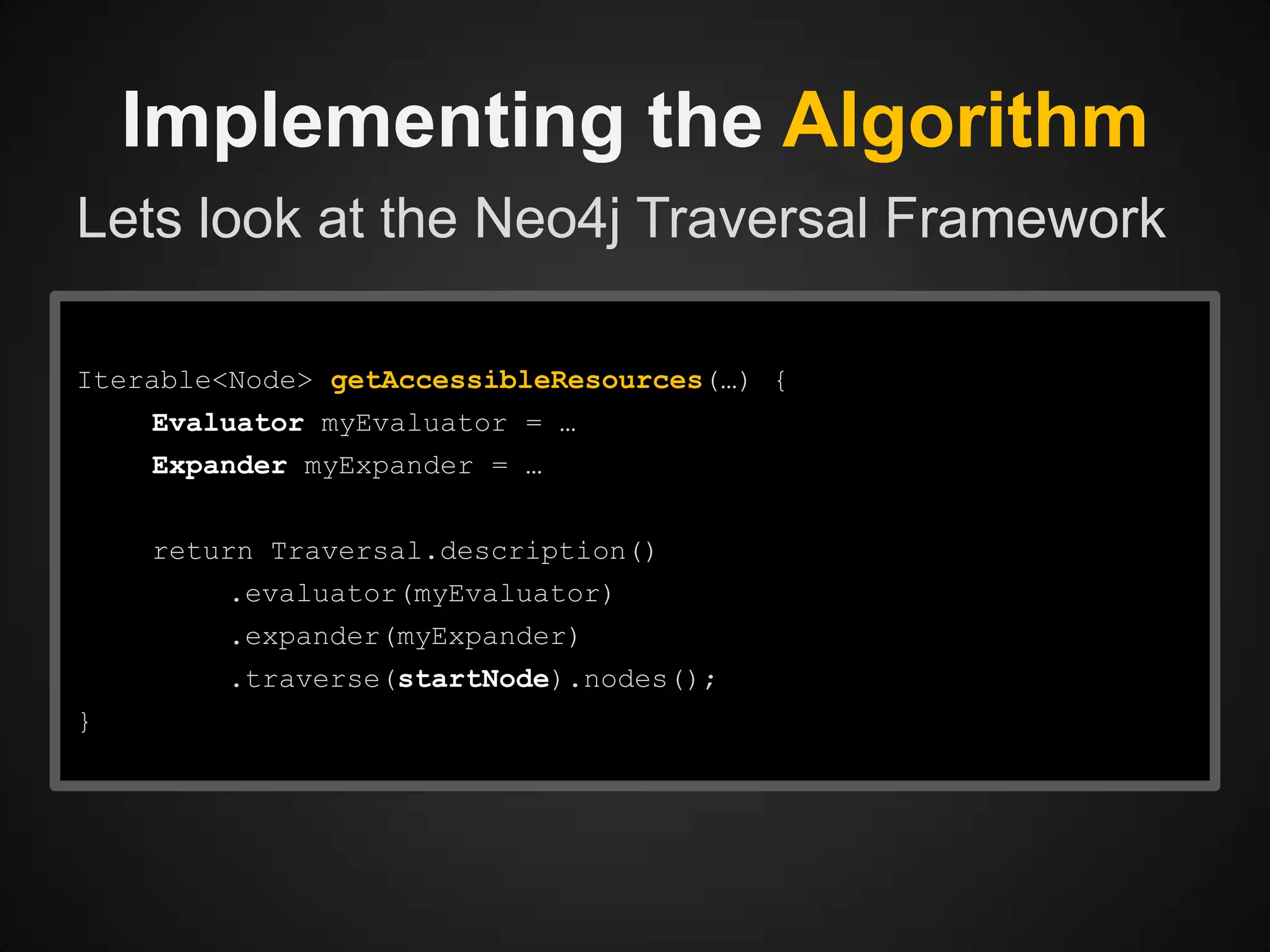
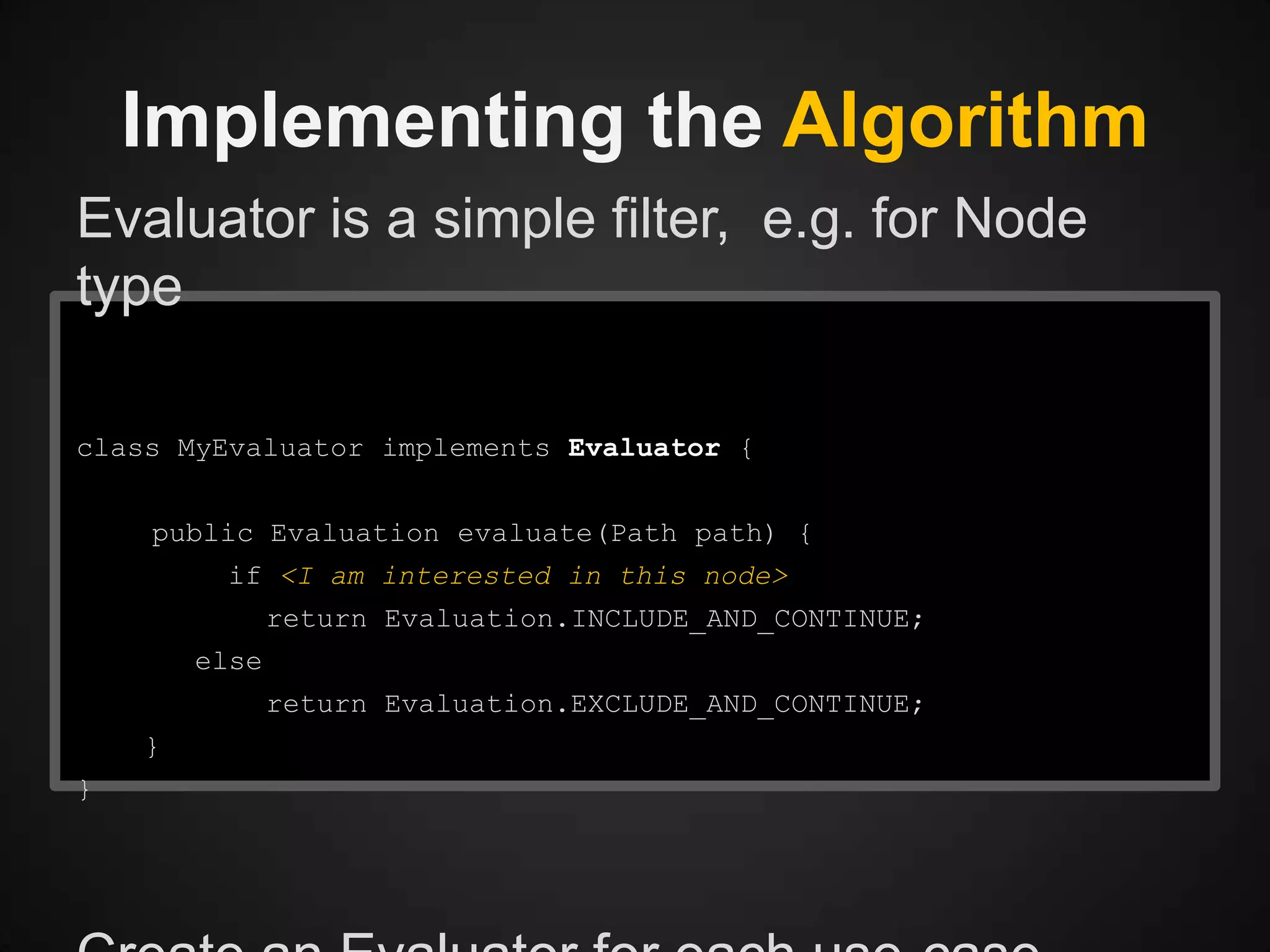
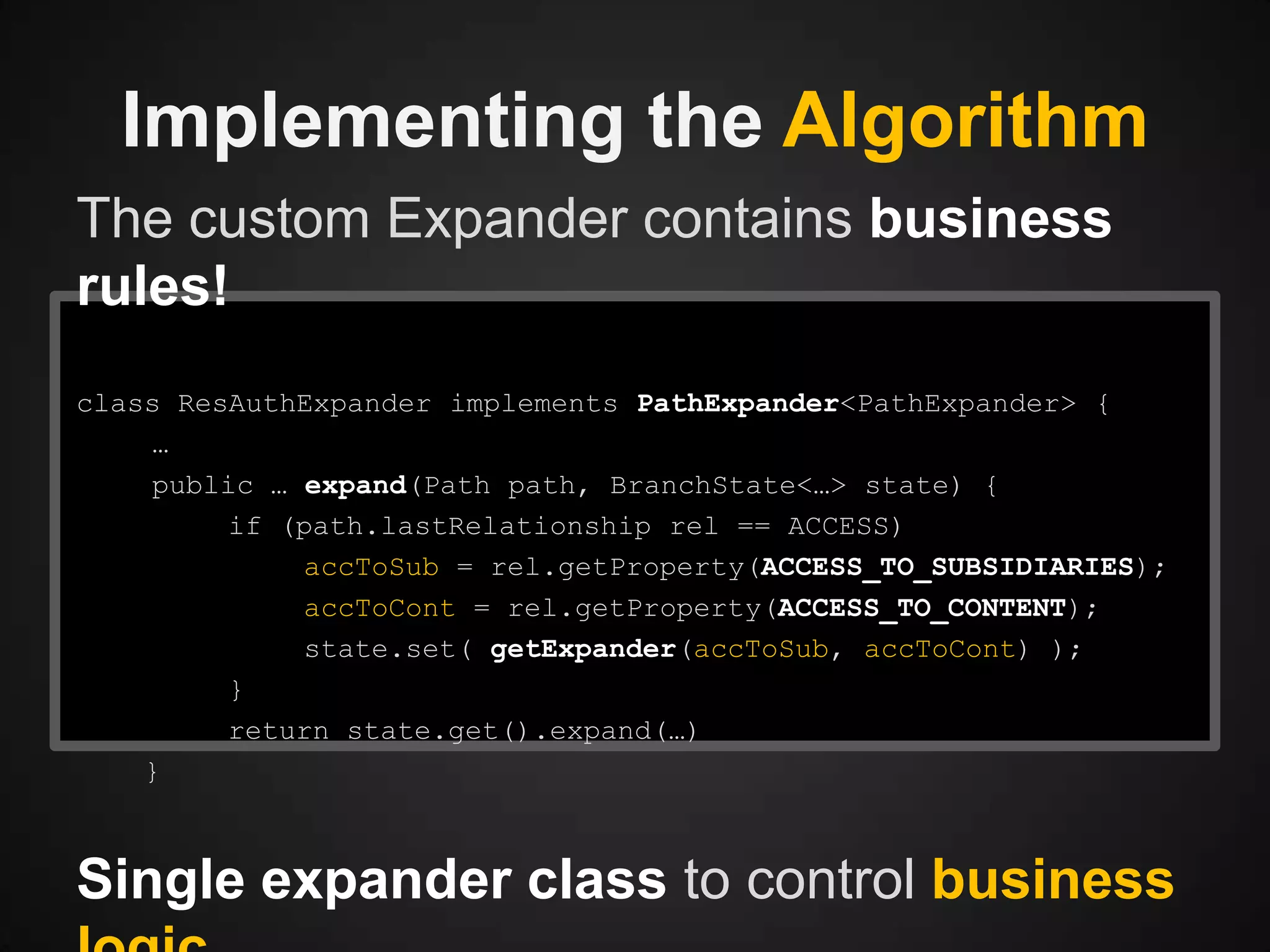
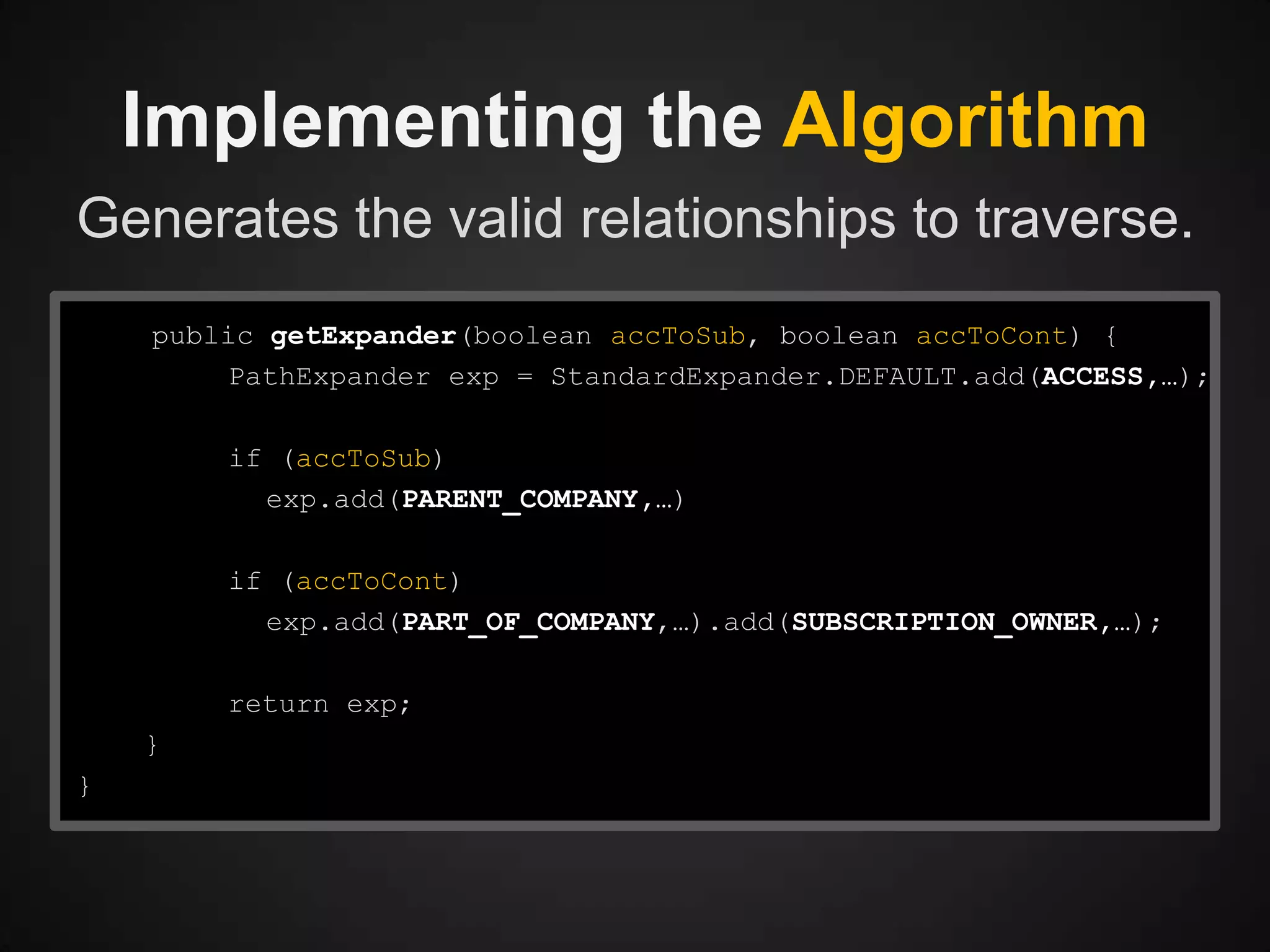
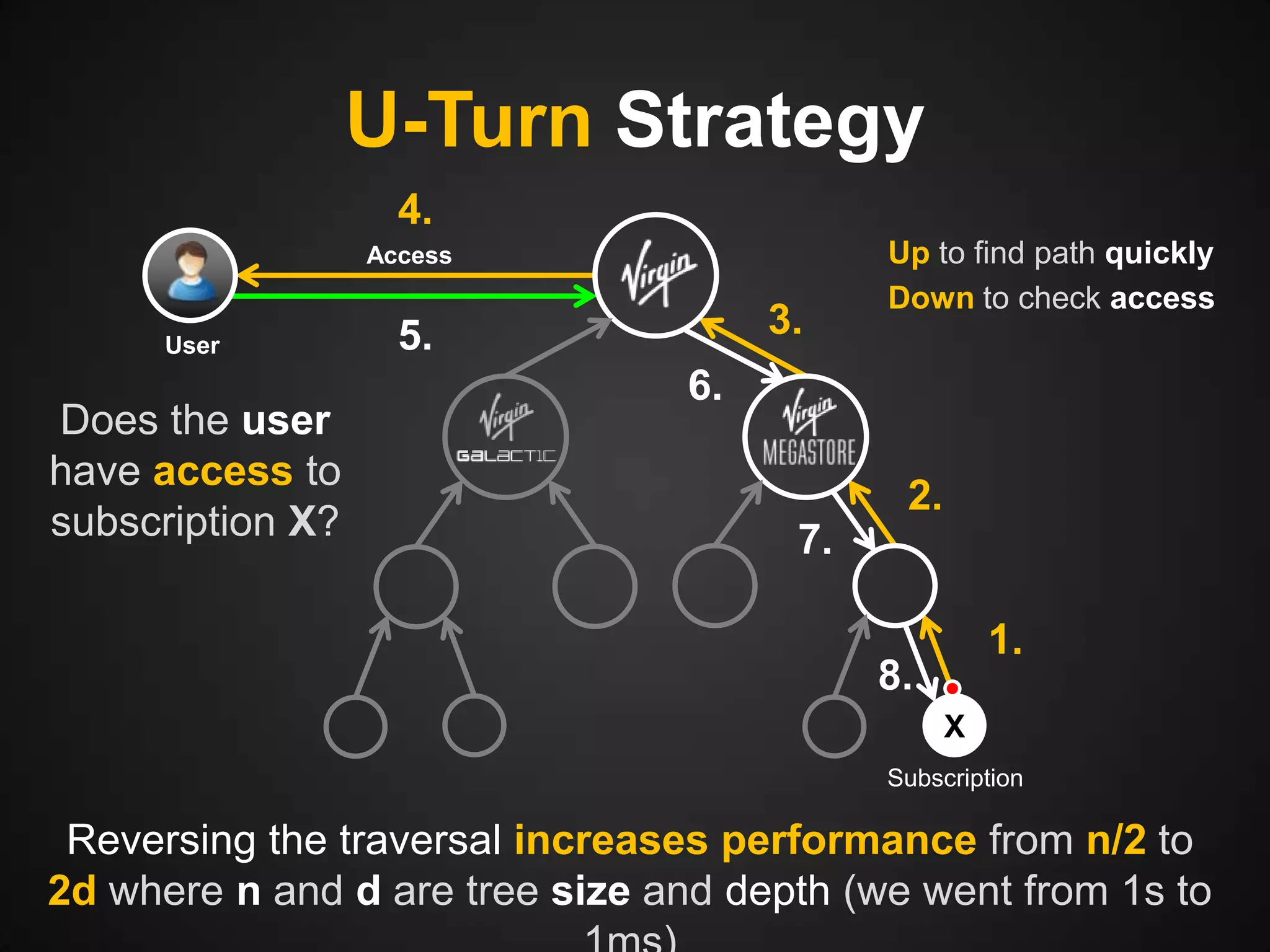
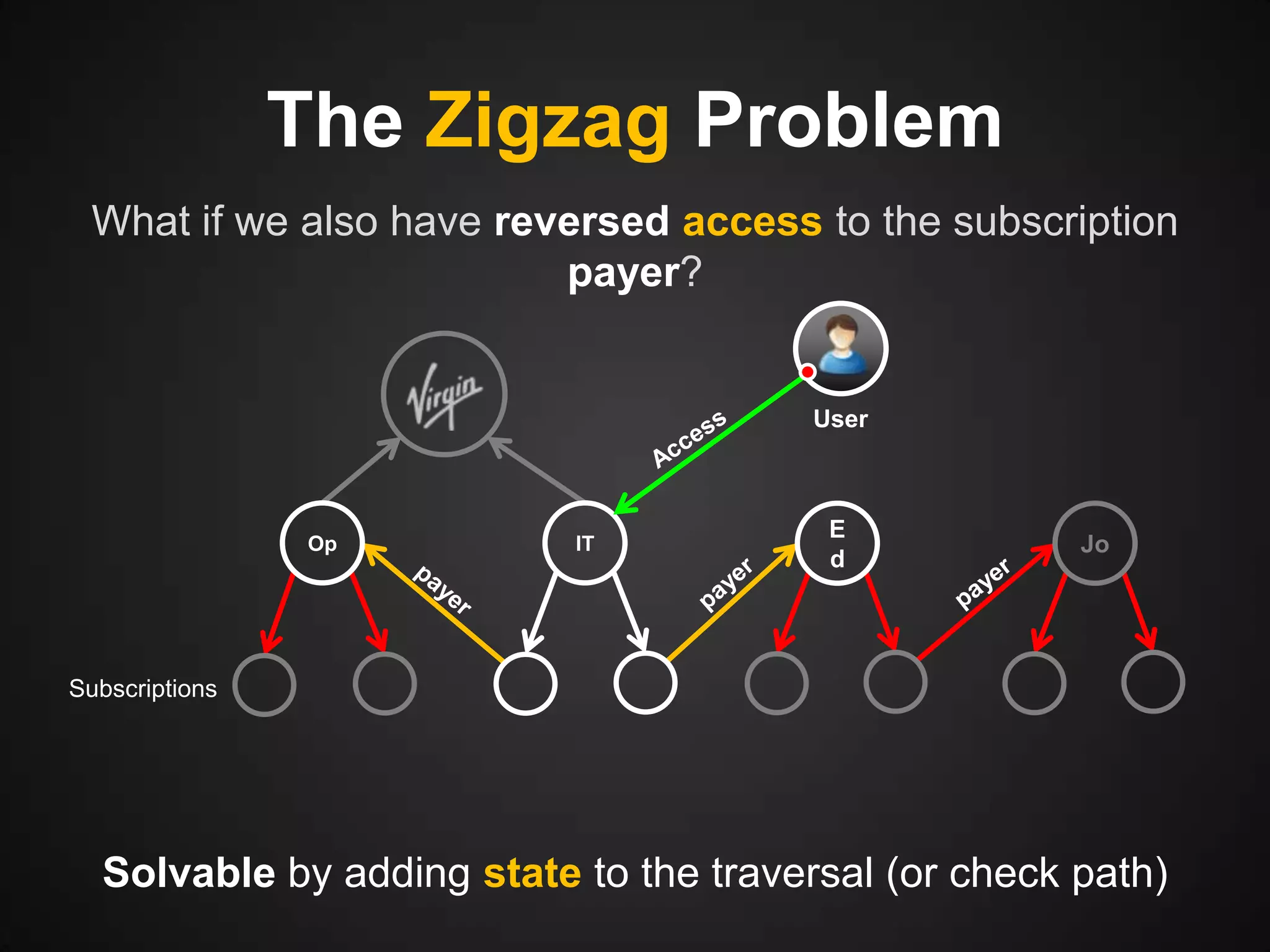
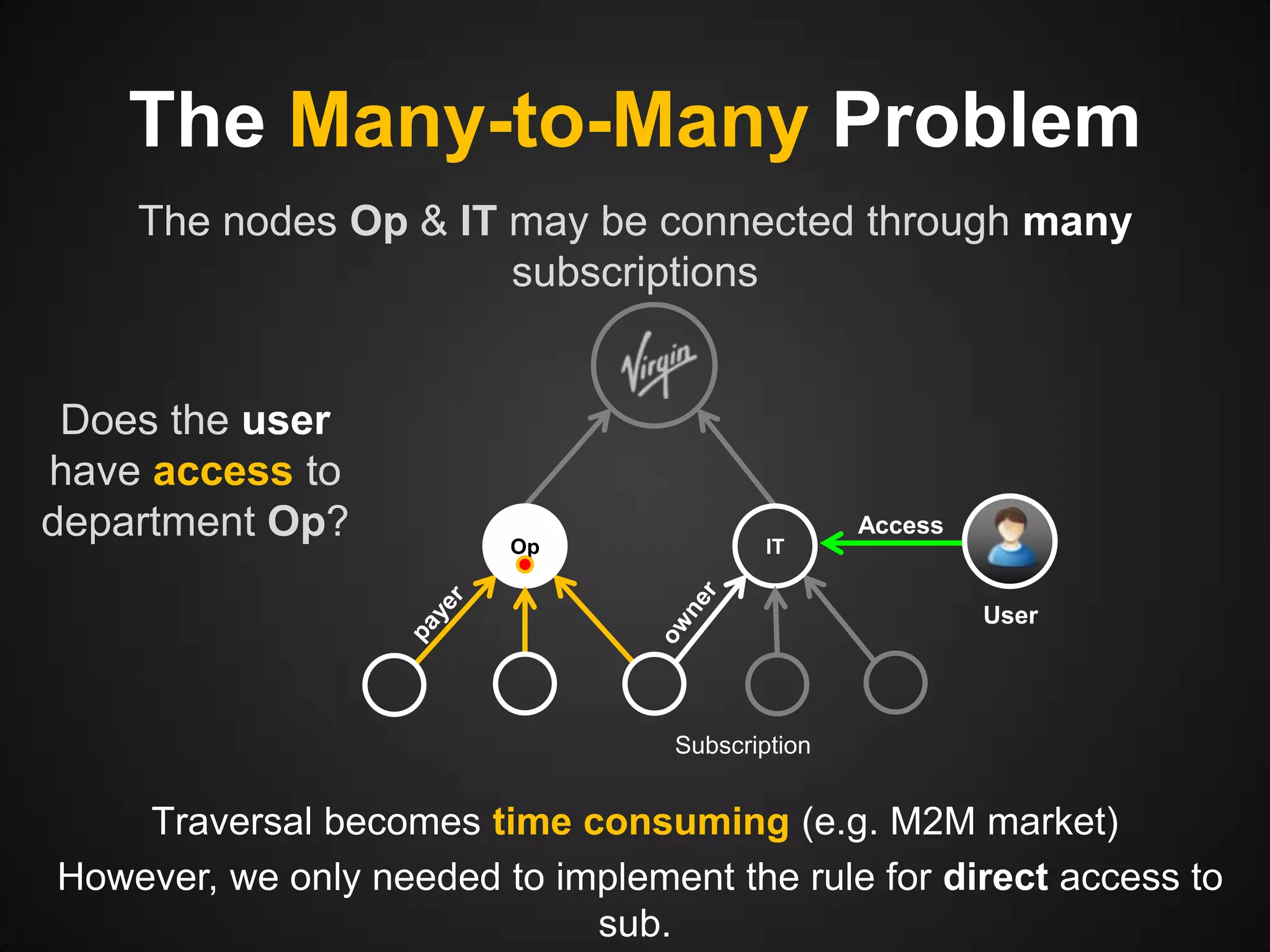
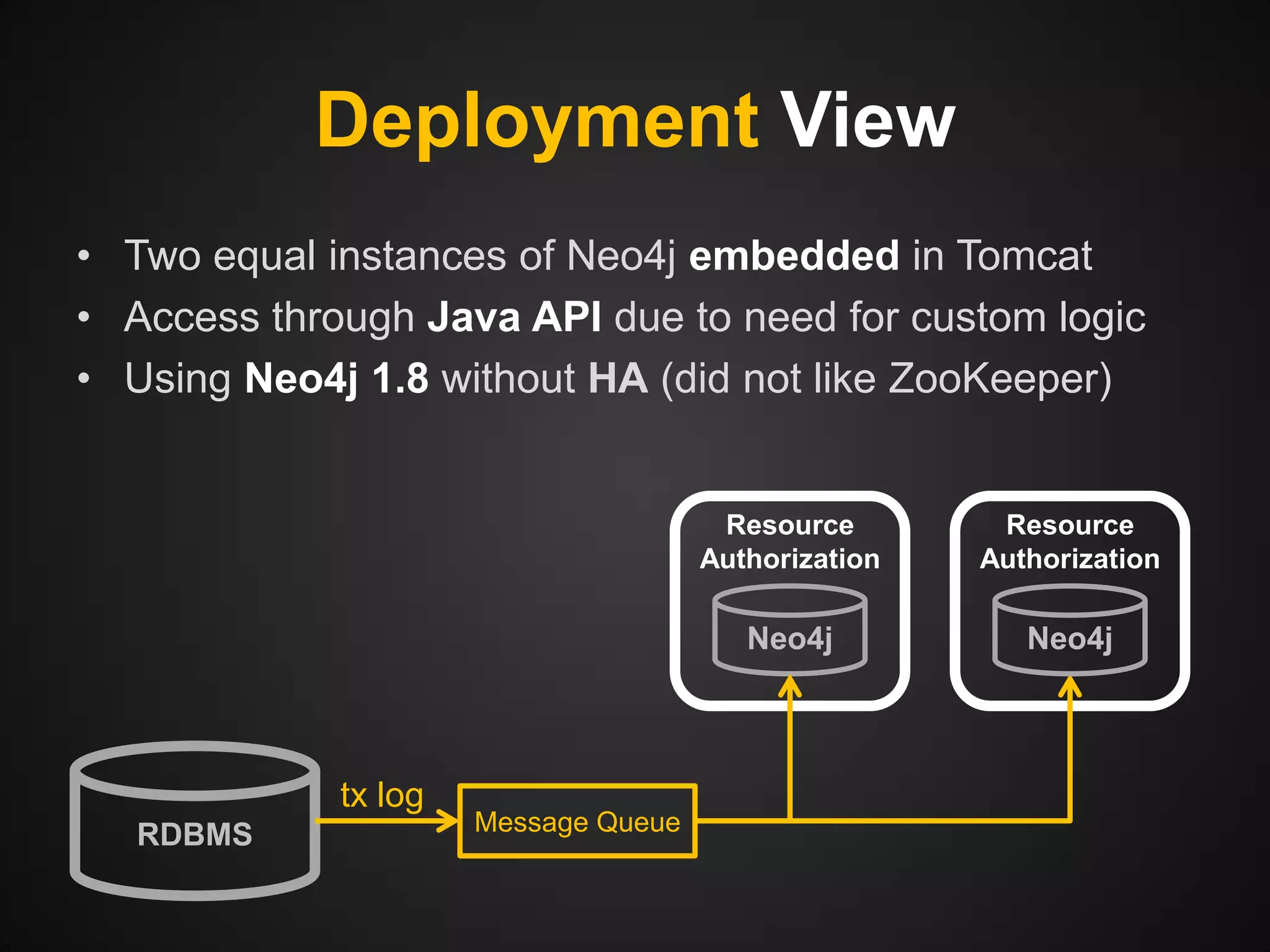
In his presentation, Sebastian Verheughe discusses Telenor's implementation of graph databases to efficiently solve resource authorization issues. By using Neo4j, the process of calculating accessible resources was optimized from minutes to seconds, significantly improving performance and scalability. The approach simplified business rule expressions and addressed the complexities associated with traditional SQL-based methods.