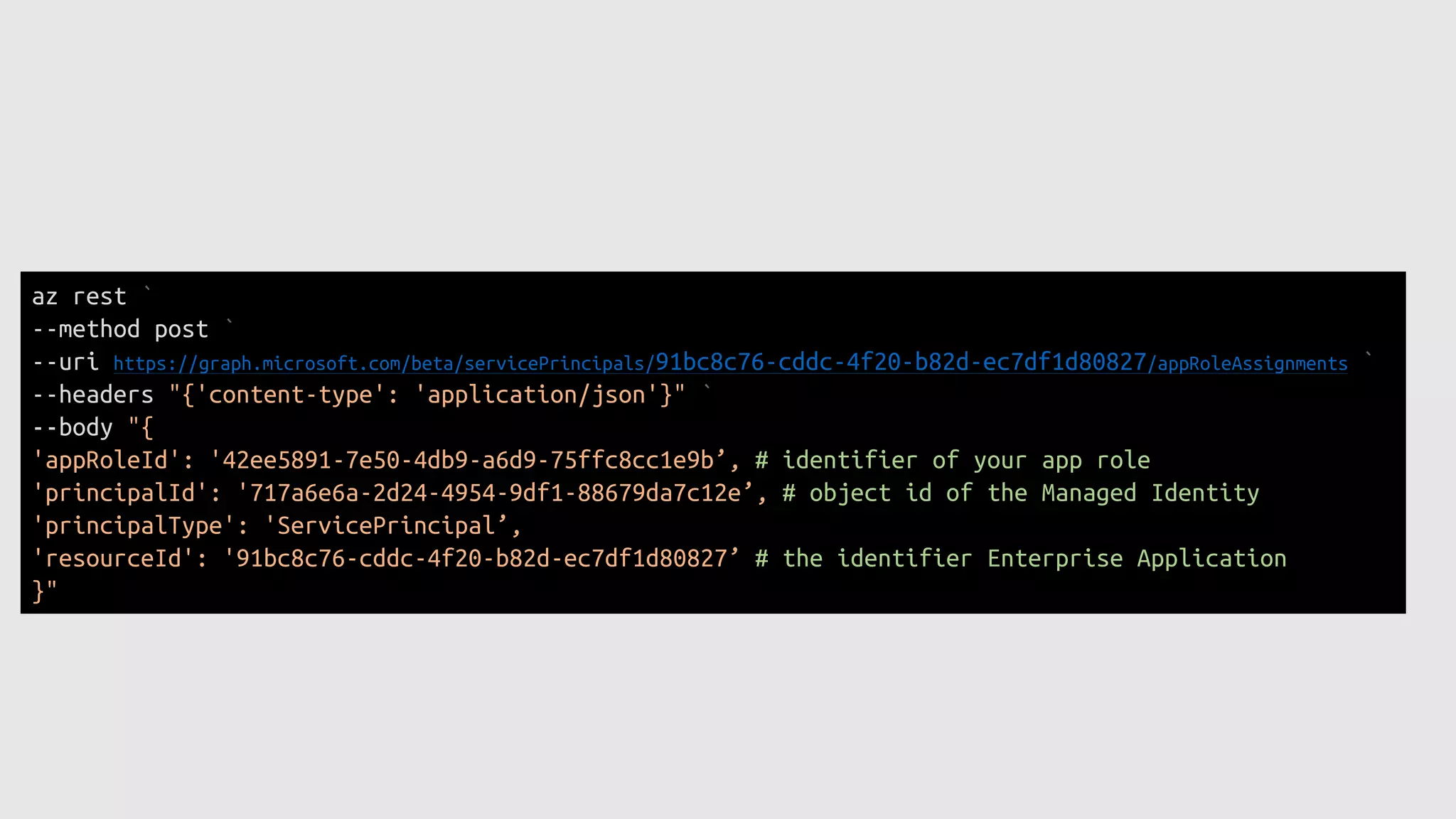
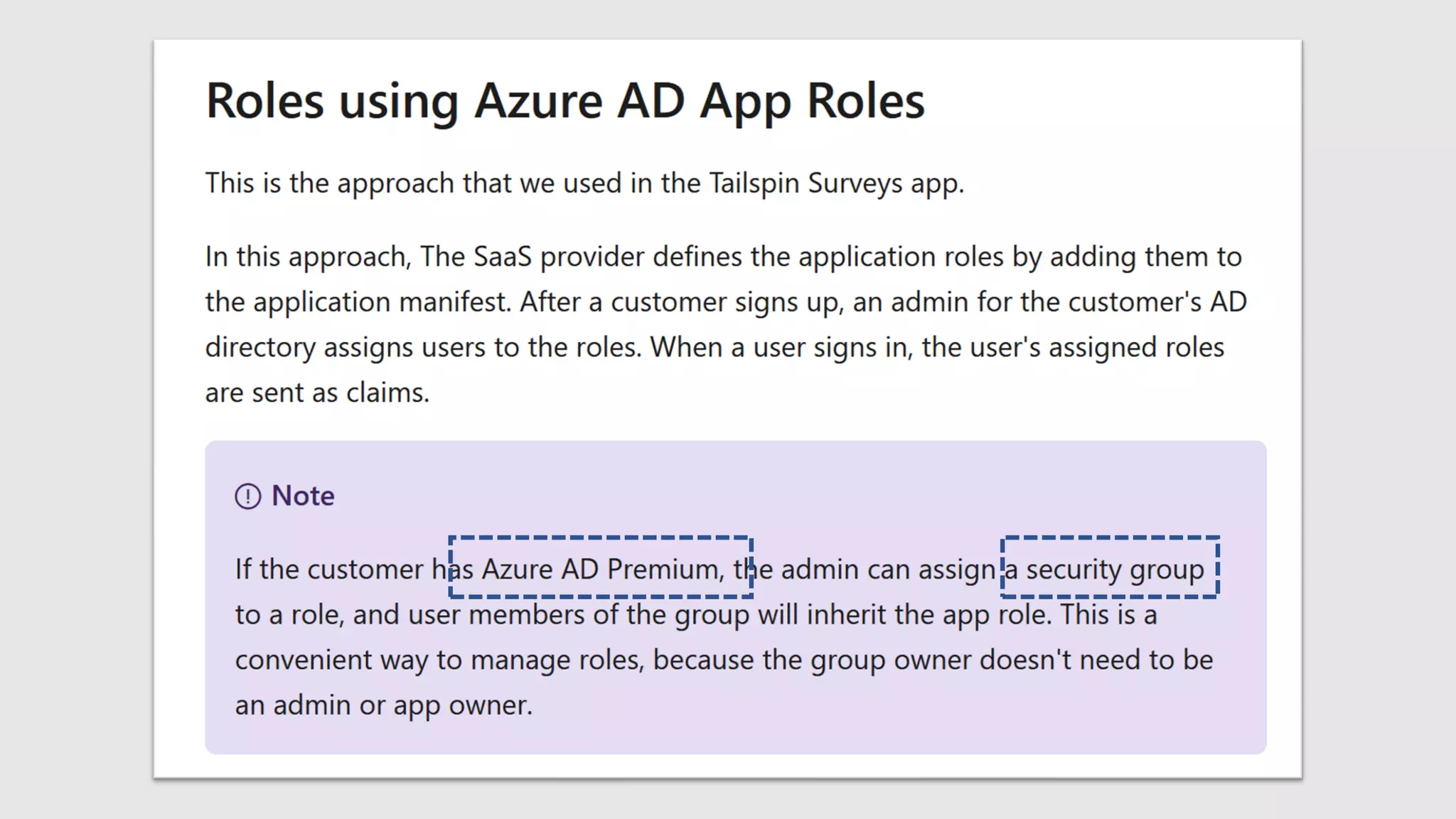
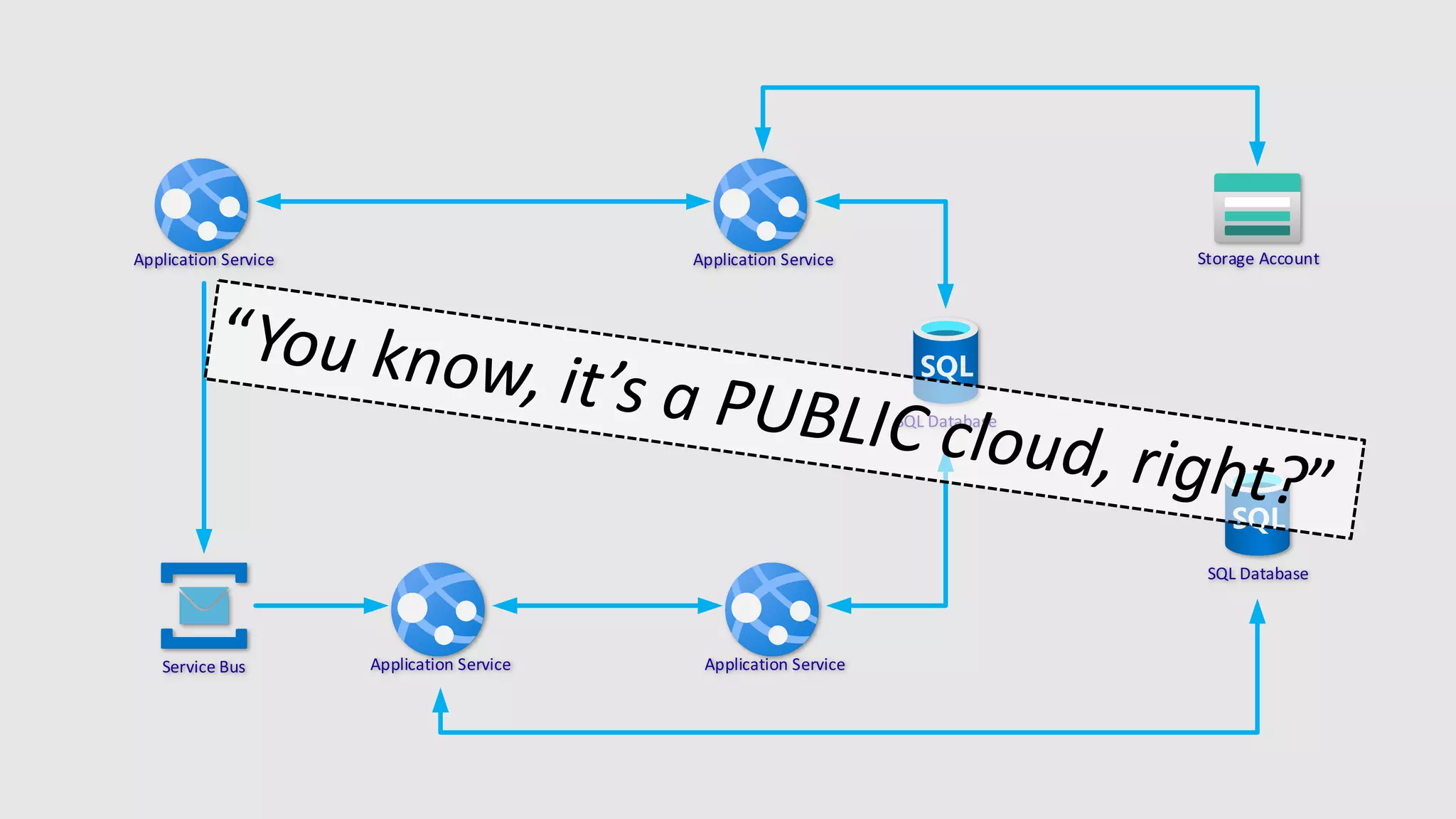
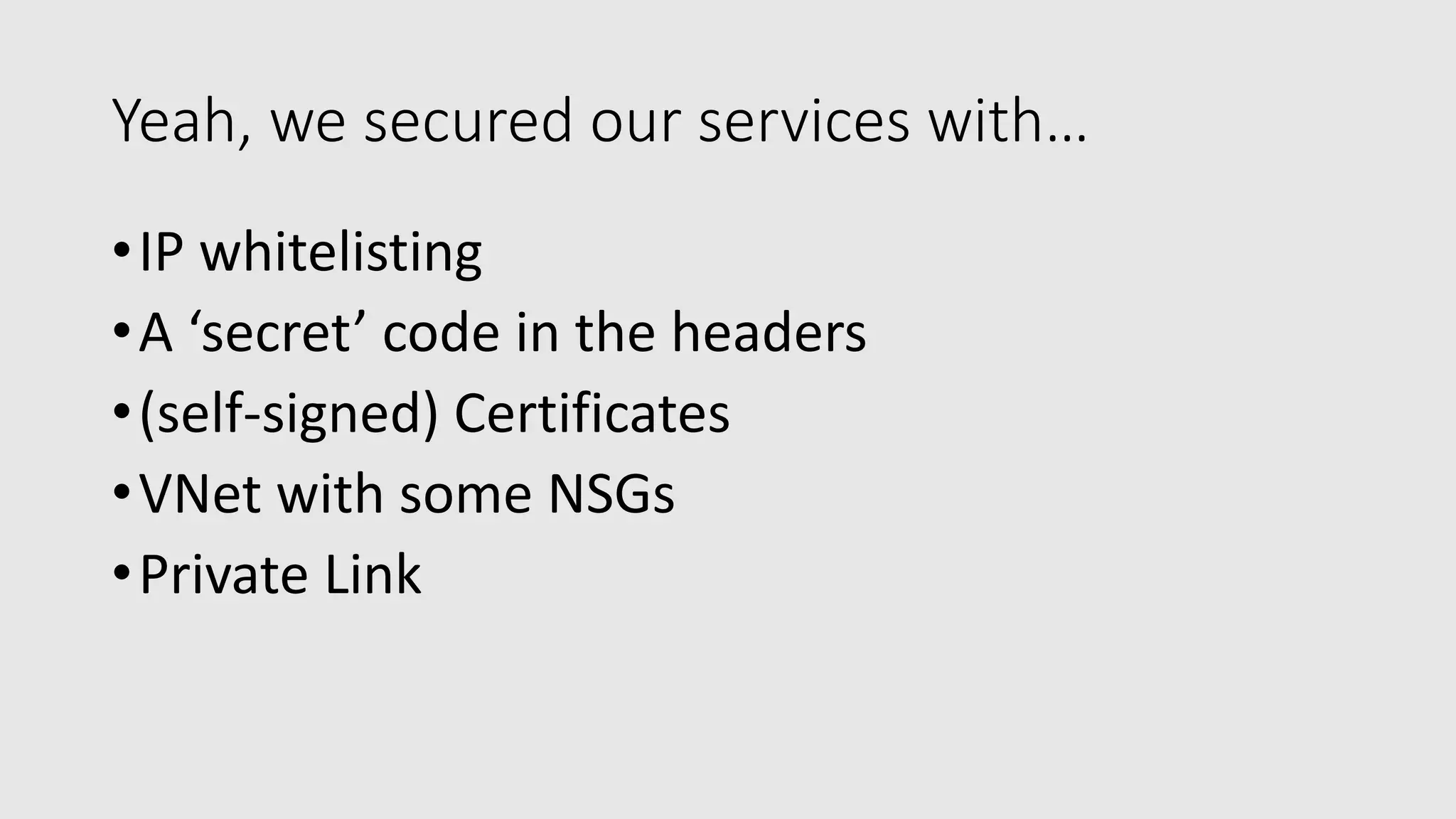
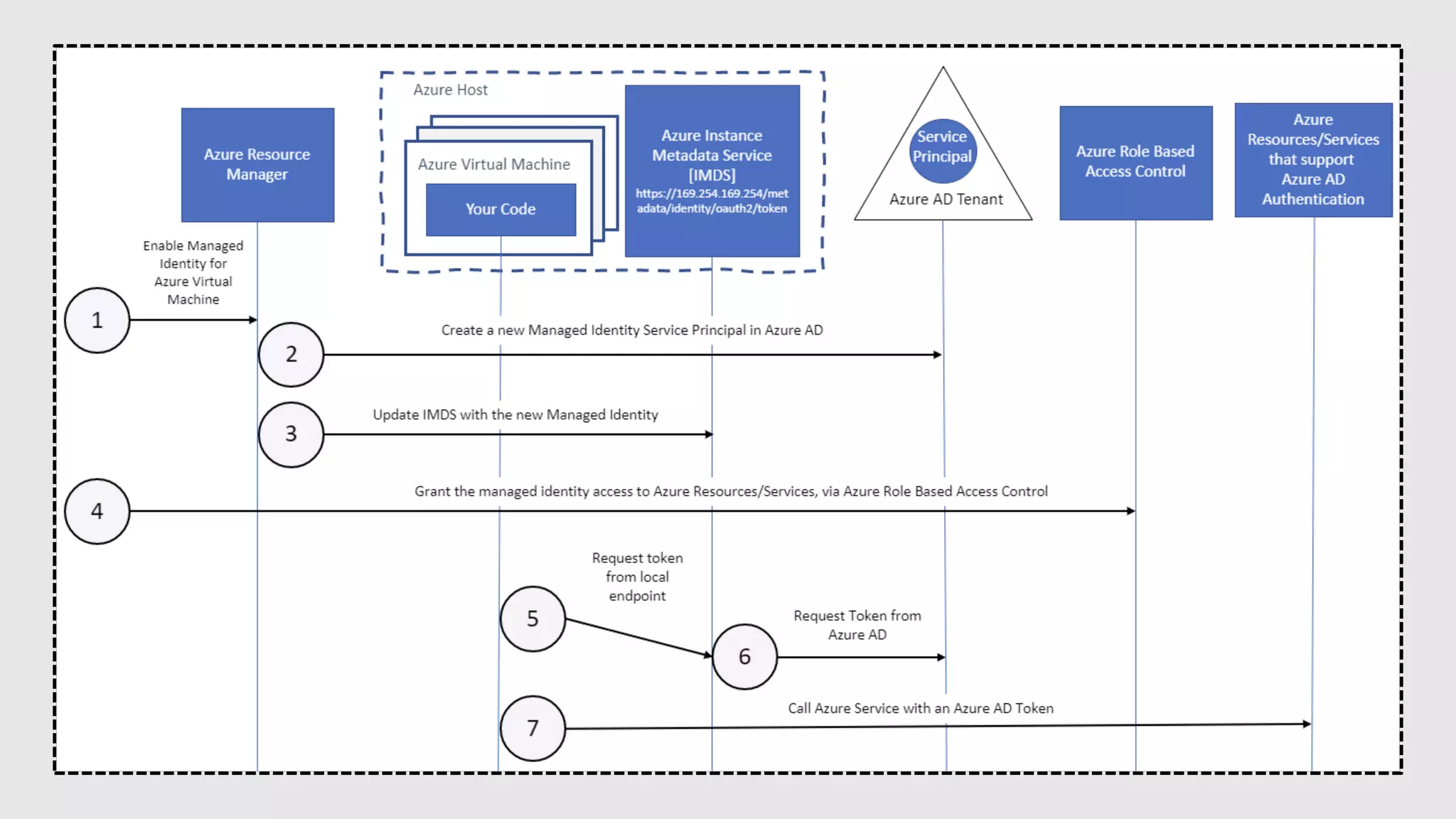
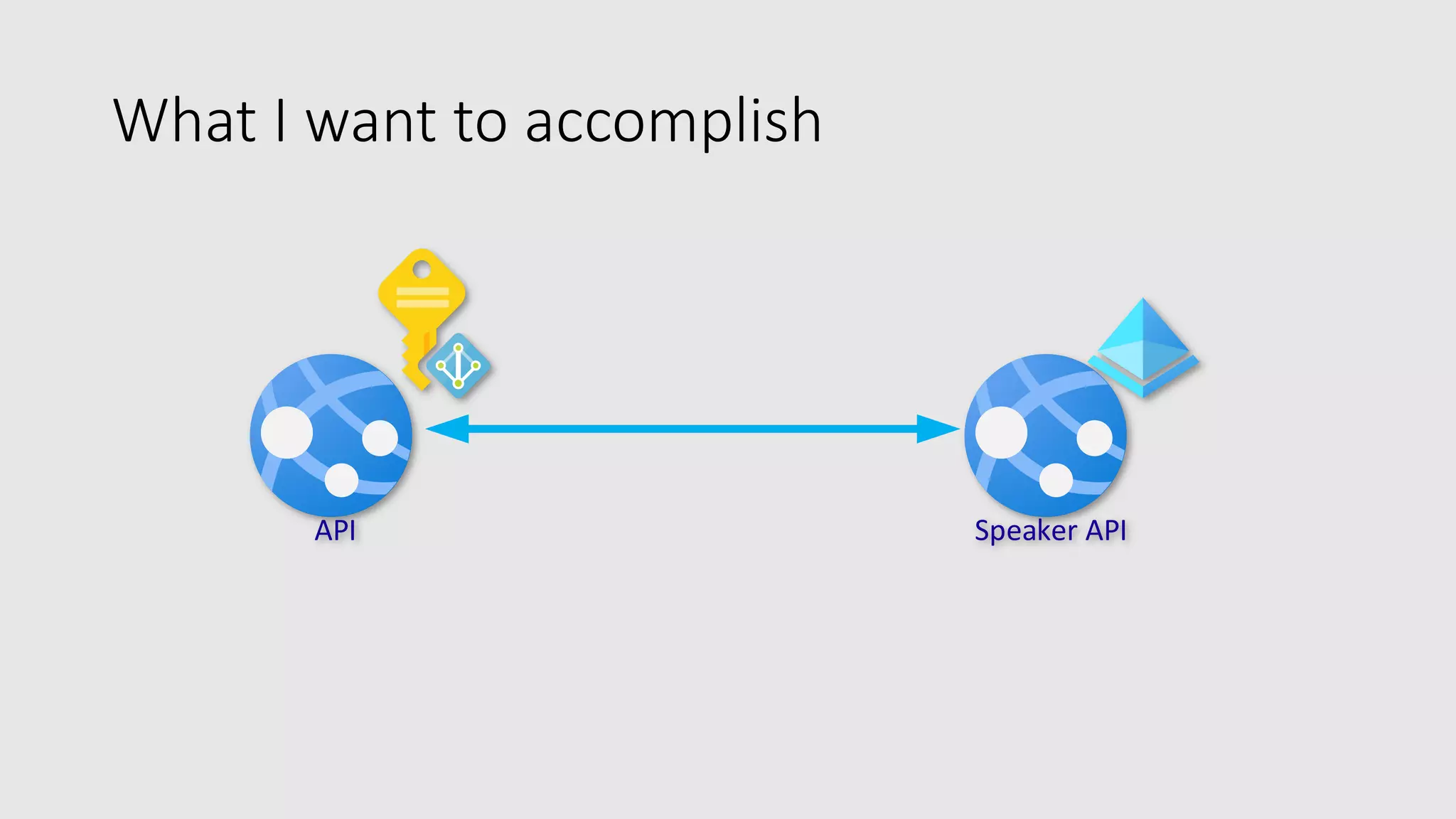
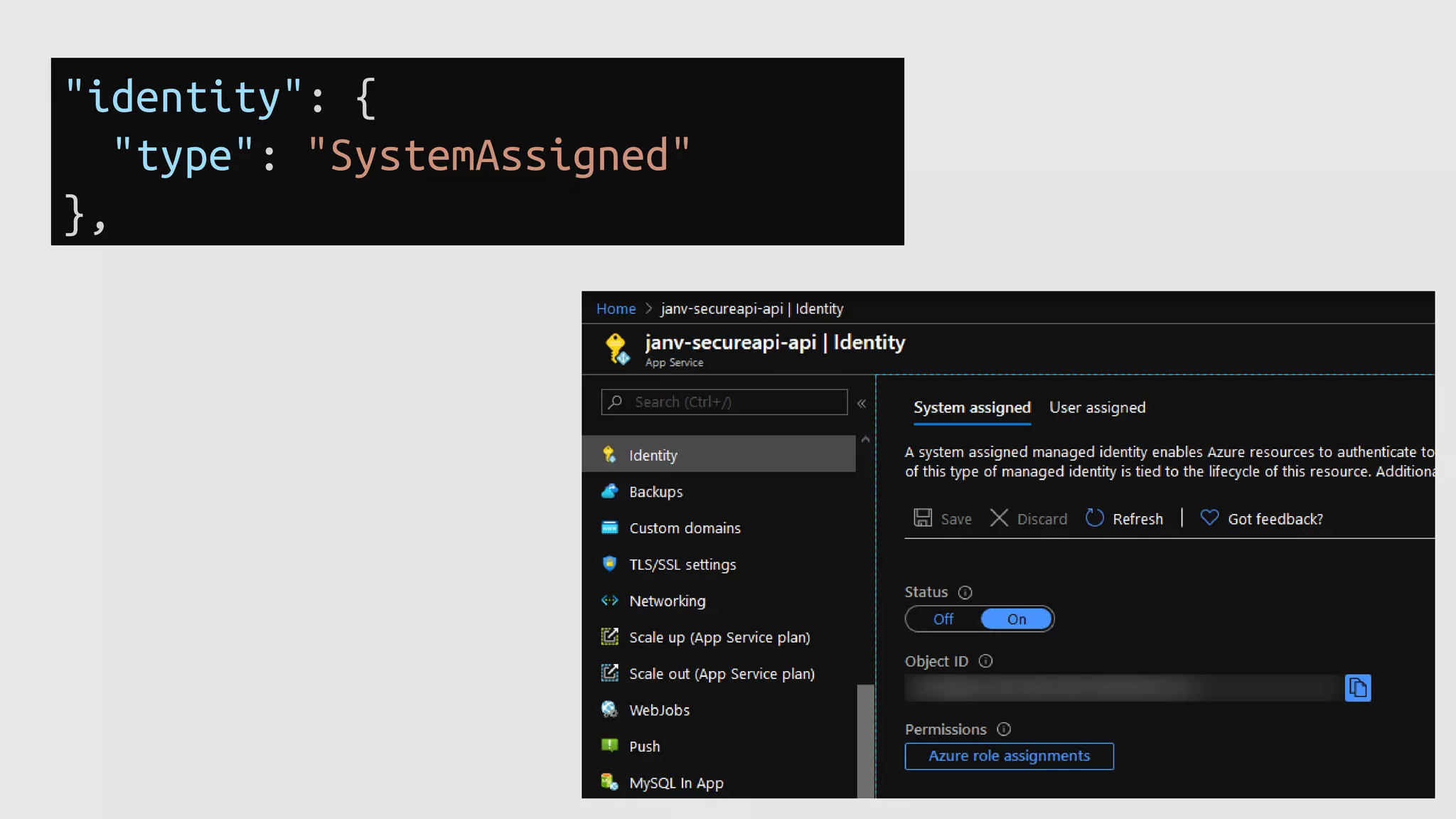
The document discusses the use of Azure Active Directory Managed Identities for securing application services, focusing on design considerations such as security, performance, and maintainability. It provides technical details on implementing managed identities, including the setup of API calls with authentication and role assignments. The content is geared towards cloud solution architects, highlighting best practices for securing services using Azure features.

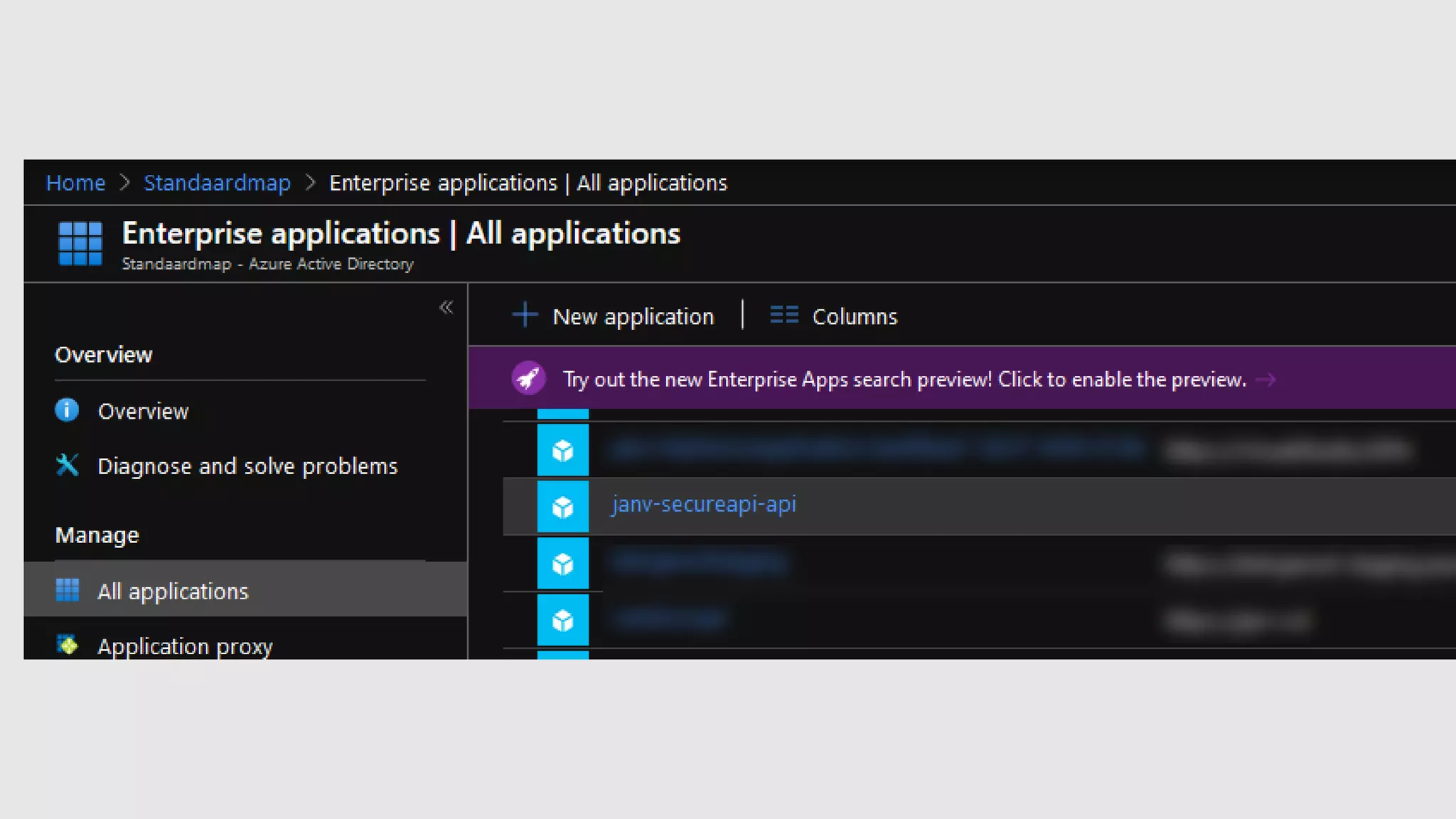
![var tenantId = this.configuration["ActiveDirectory:TenantId"];
var applicationIdUri = this.configuration["ApplicationIdUri"];
var azureServiceTokenProvider = new AzureServiceTokenProvider();
var accessToken = await azureServiceTokenProvider.GetAccessTokenAsync(
applicationIdUri,
tenantId: tenantId);
var httpClient = this.clientFactory.CreateClient();
httpClient.DefaultRequestHeaders.Authorization =
new AuthenticationHeaderValue("Bearer", accessToken);
var response = await httpClient.GetAsync(endpointUrlOfYourBackendService);](https://image.slidesharecdn.com/devclub-useazureactivedirectorymanagedidentitiesforyourservices-200625081625/75/Using-Azure-Managed-Identities-for-your-App-Services-by-Jan-de-Vries-from-4DotNet-at-Azure-focused-87th-DevClub-lv-12-2048.jpg)
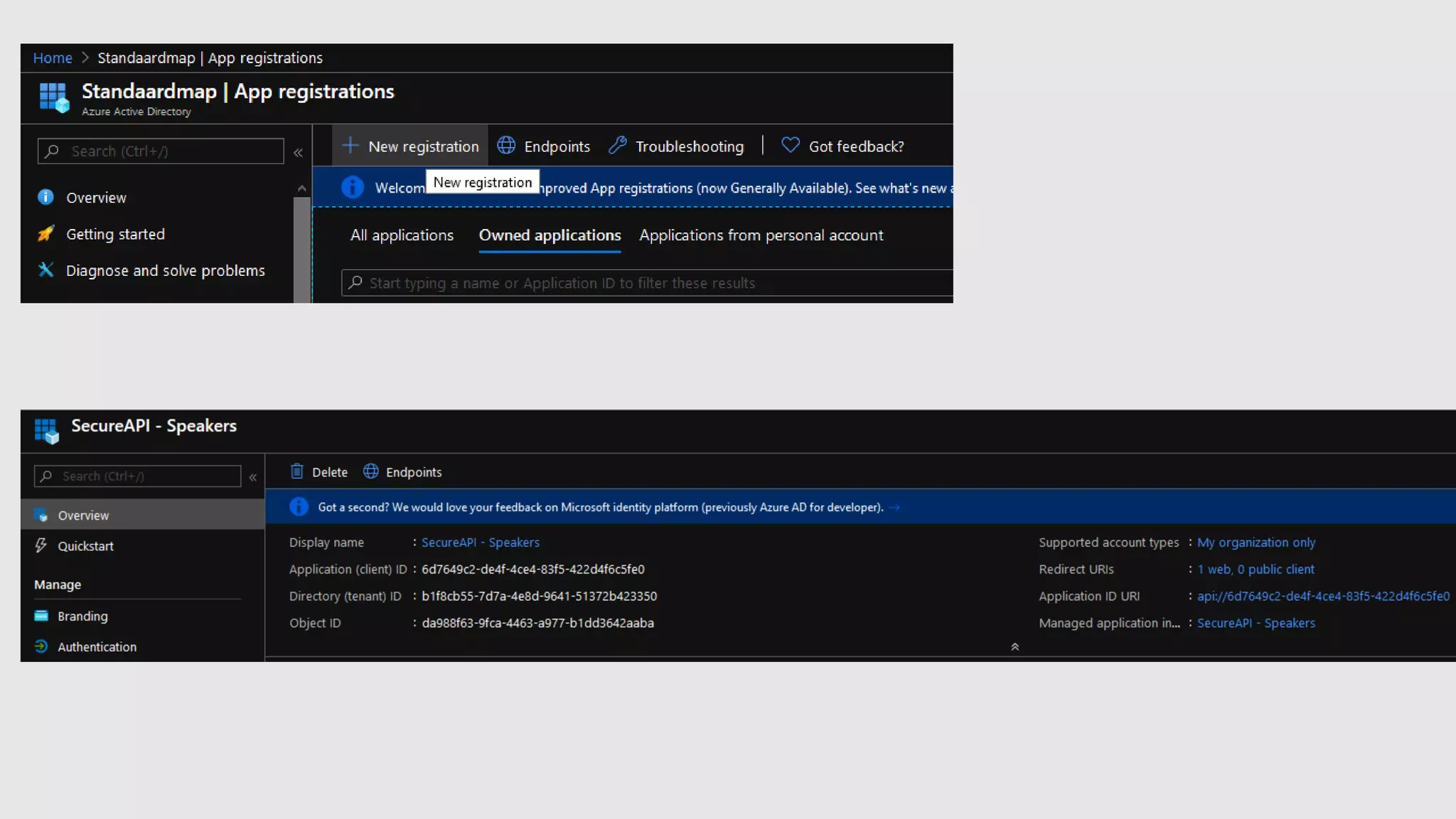
![Manifest
"appRoles": [
{
"allowedMemberTypes": [
"Application",
"User"
],
"description": "Reader Role",
"displayName": "Speaker service reader",
"id": "42ee5891-7e50-4db9-a6d9-75ffc8cc1e9b",
"isEnabled": true,
"lang": null,
"origin": "Application",
"value": "SecureApi.Speaker.Reader"
},
...
],](https://image.slidesharecdn.com/devclub-useazureactivedirectorymanagedidentitiesforyourservices-200625081625/75/Using-Azure-Managed-Identities-for-your-App-Services-by-Jan-de-Vries-from-4DotNet-at-Azure-focused-87th-DevClub-lv-15-2048.jpg)
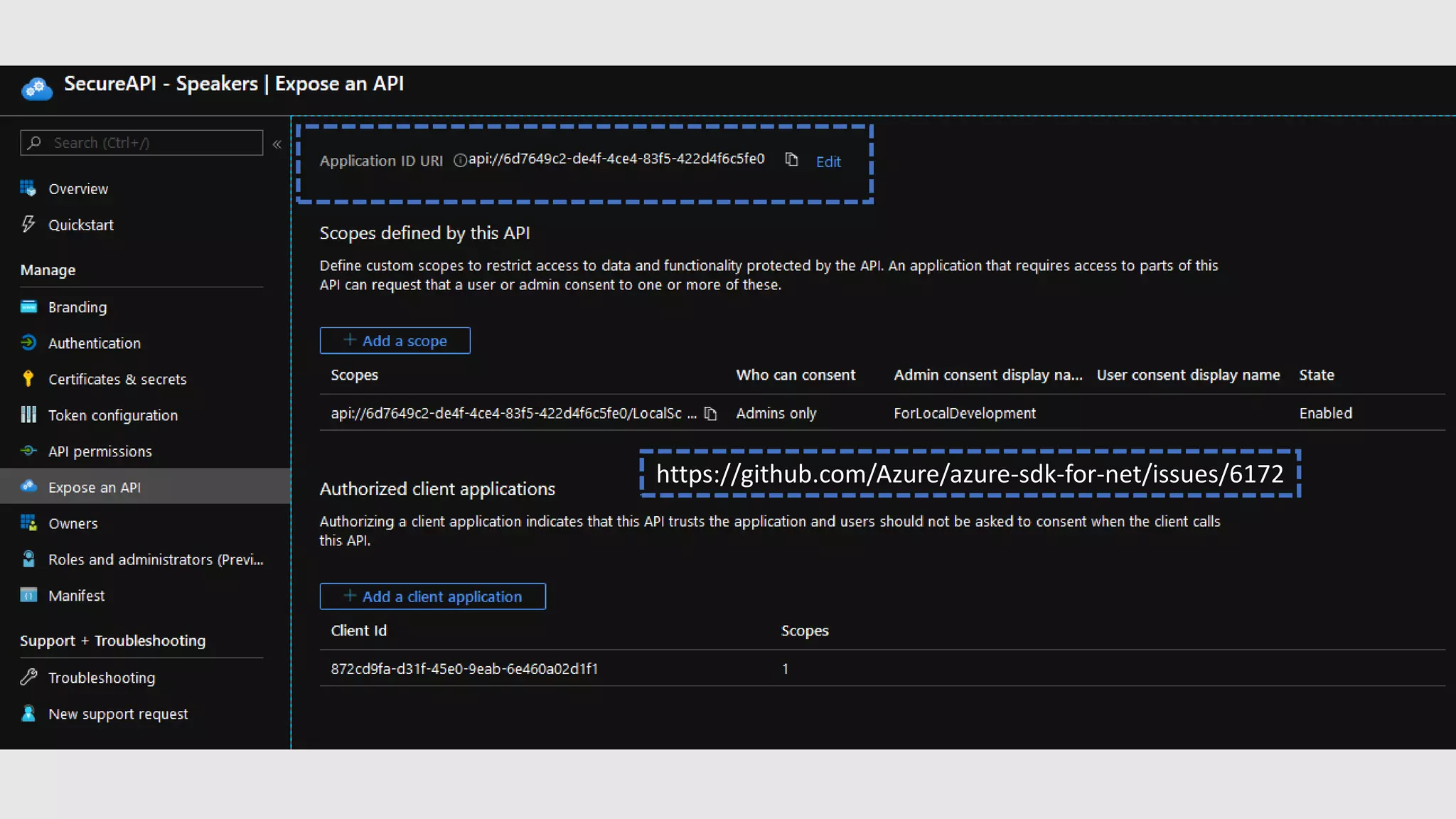
!["Authentication": {
"Authority": "https://login.microsoftonline.com/[tenantId]",
"ClientId": "[theApplicationIdOfTheApplicationRegistration]",
"AppIdUri": "[theApplicationIDURI]"
}
app.UseAuthentication();
app.UseAuthorization();
services.AddAuthentication(o => {
o.DefaultScheme = JwtBearerDefaults.AuthenticationScheme;
})
.AddJwtBearer(o => {
o.Authority = Configuration["Authentication:Authority"];
o.TokenValidationParameters = new Microsoft.IdentityModel.Tokens.TokenValidationParameters
{
ValidAudiences = new List<string>
{
Configuration["Authentication:AppIdUri"],
Configuration["Authentication:ClientId"]
}
};
});](https://image.slidesharecdn.com/devclub-useazureactivedirectorymanagedidentitiesforyourservices-200625081625/75/Using-Azure-Managed-Identities-for-your-App-Services-by-Jan-de-Vries-from-4DotNet-at-Azure-focused-87th-DevClub-lv-16-2048.jpg)