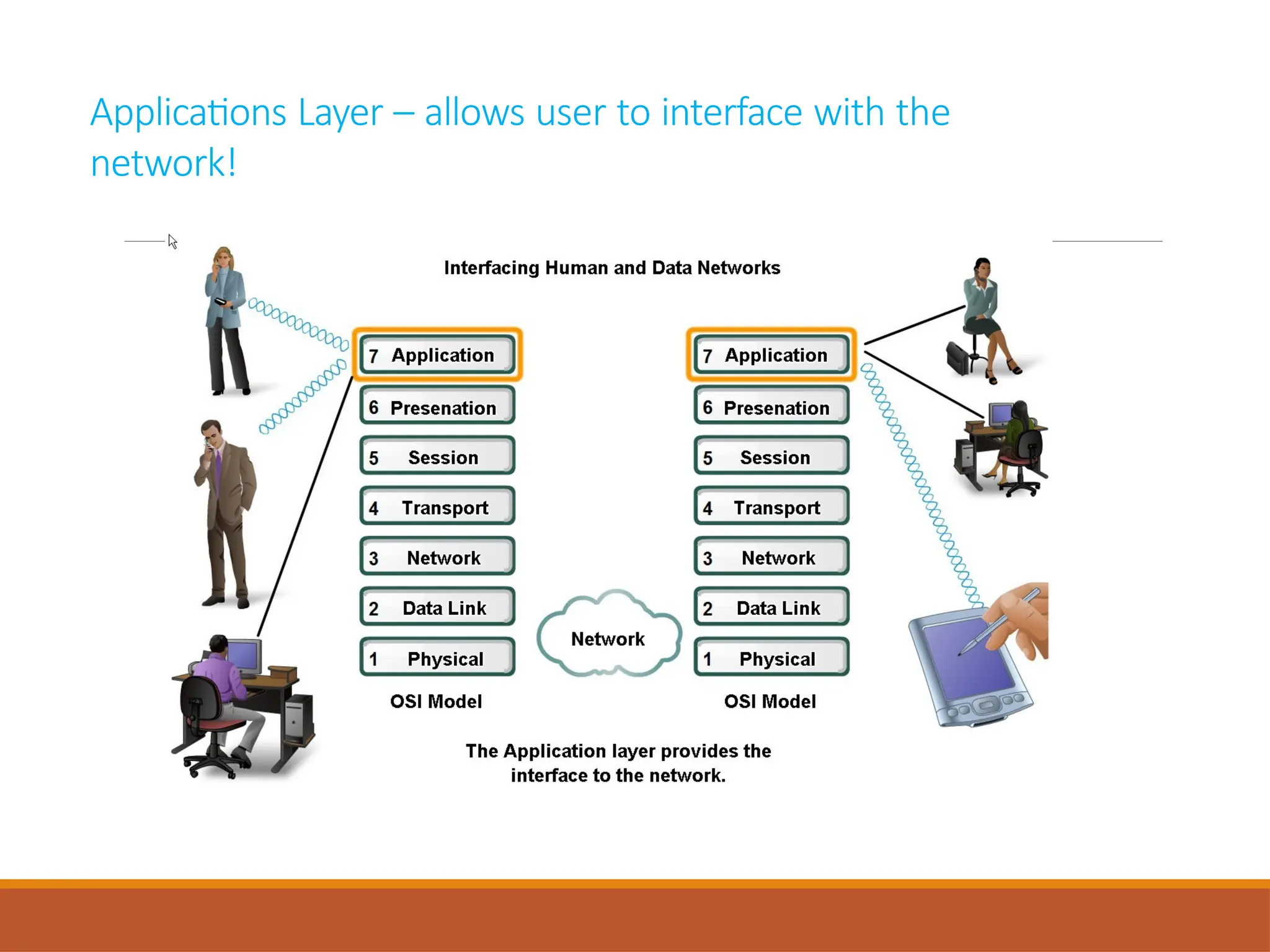
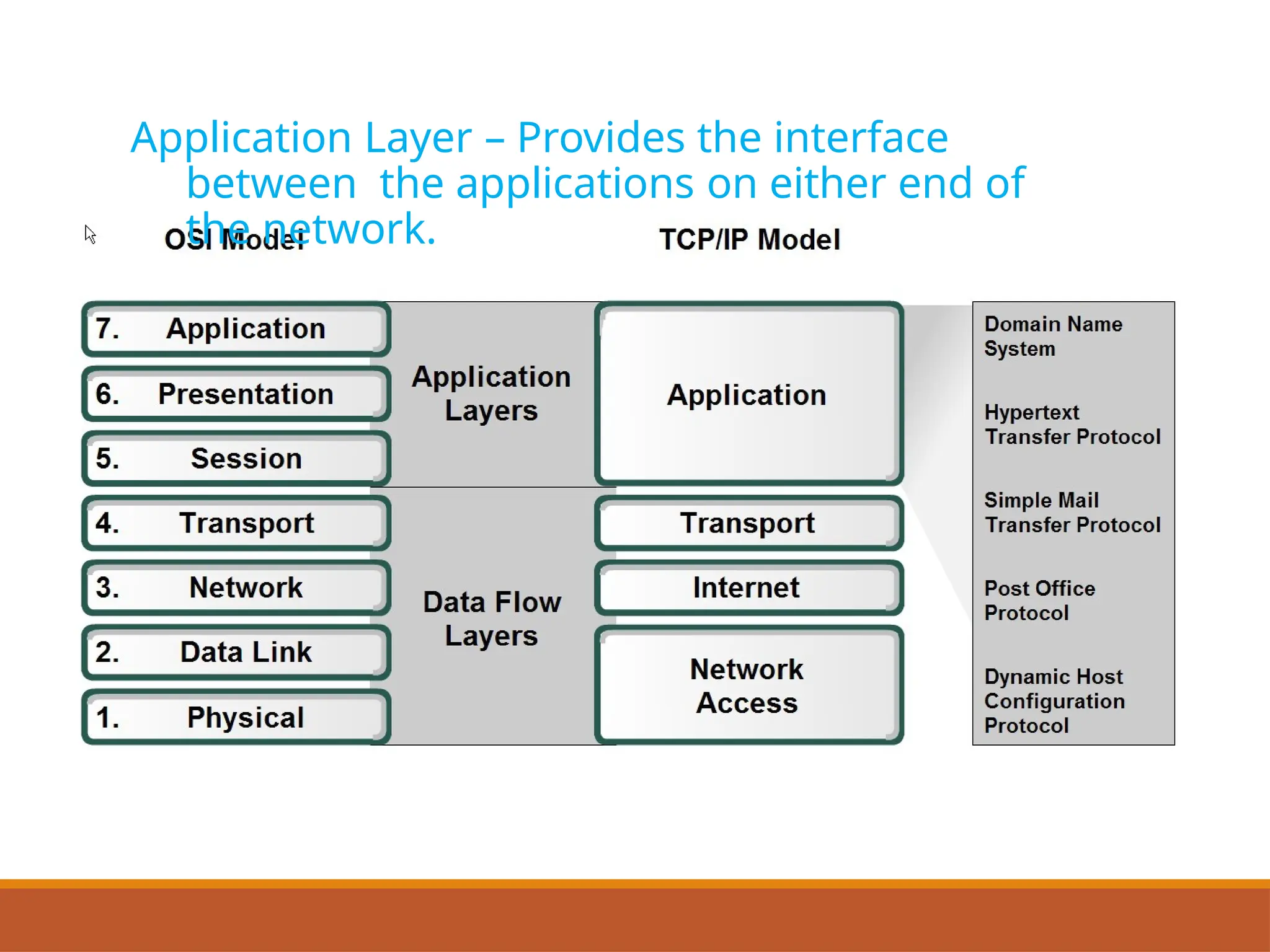
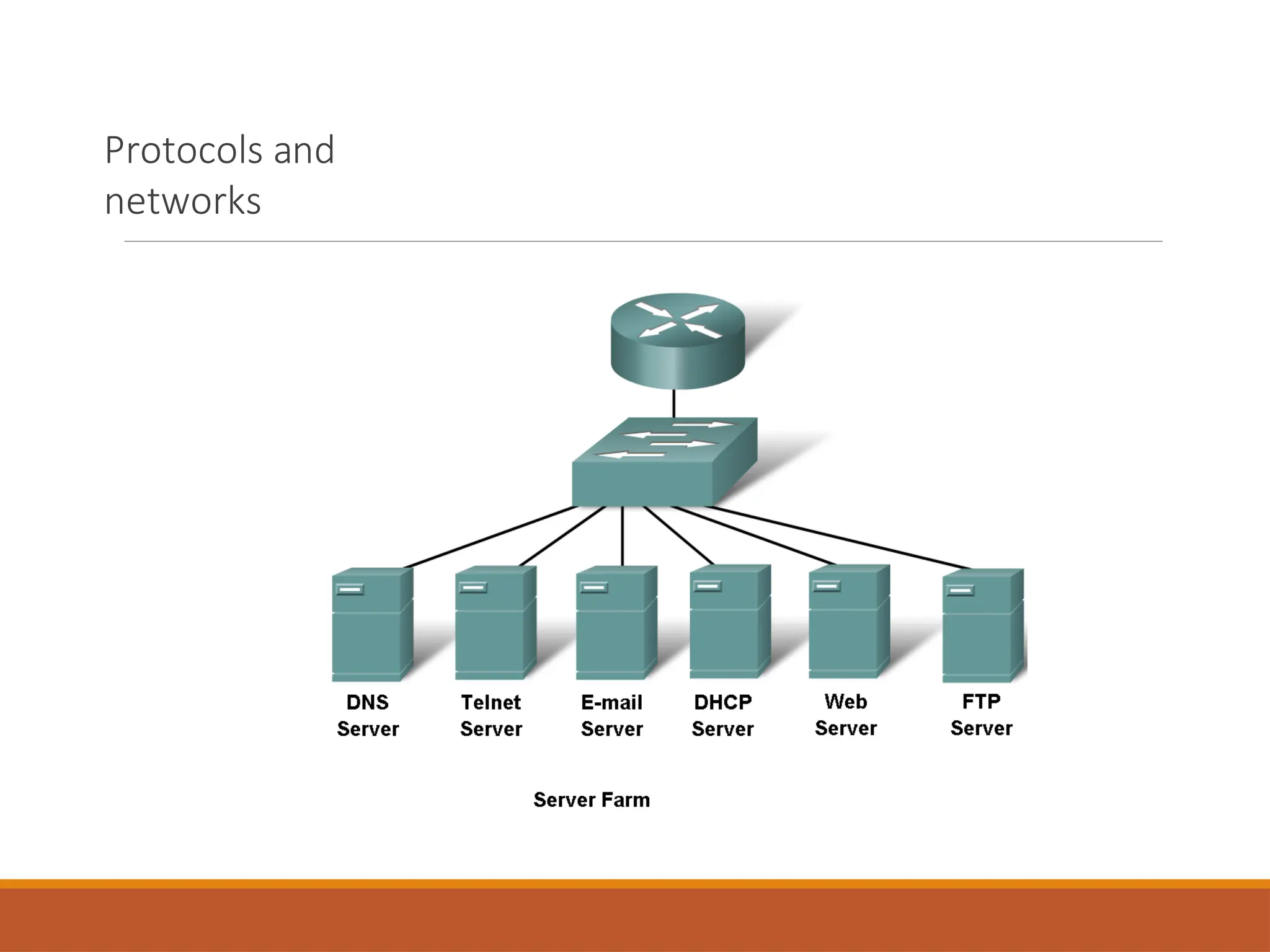
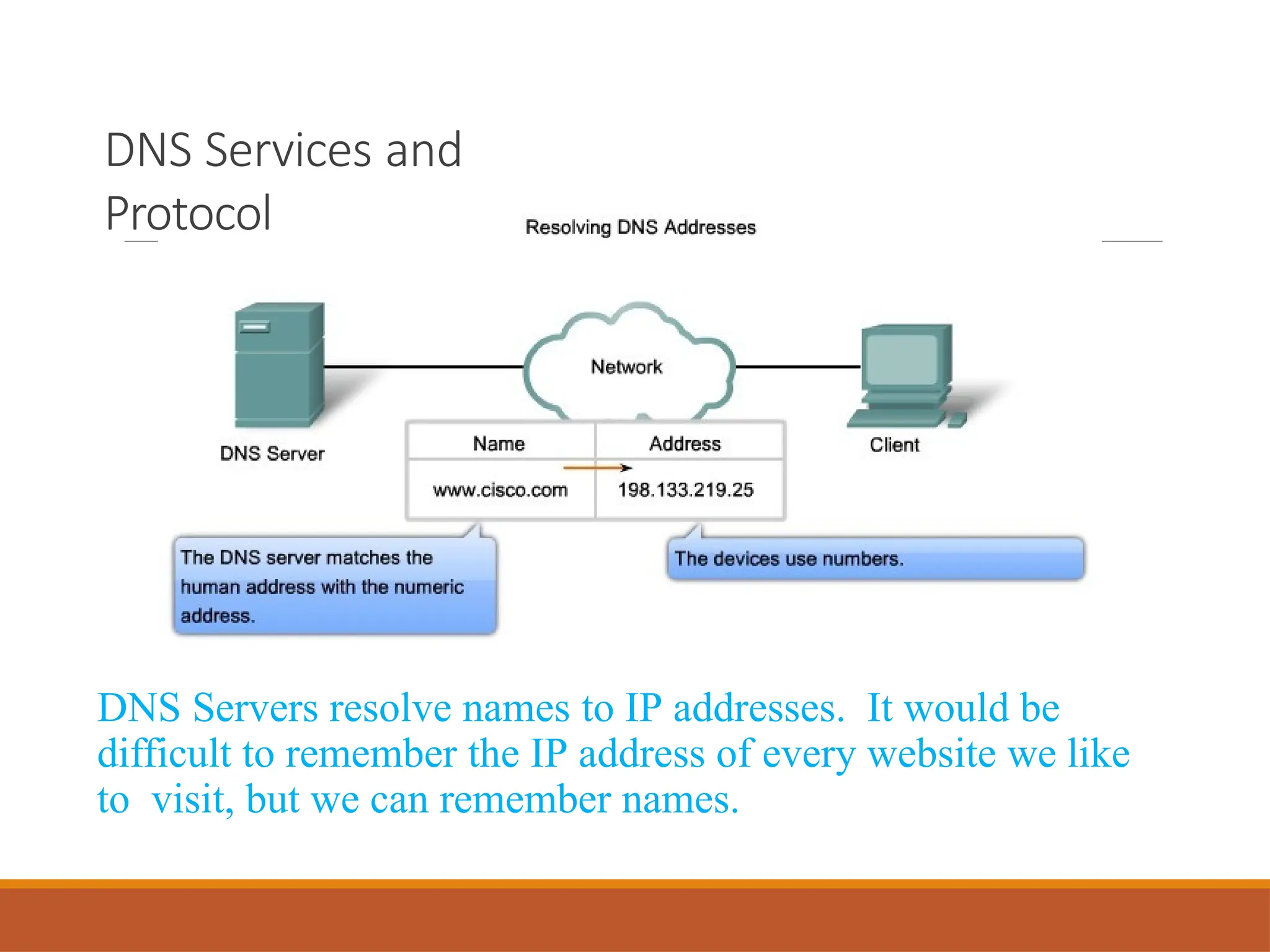
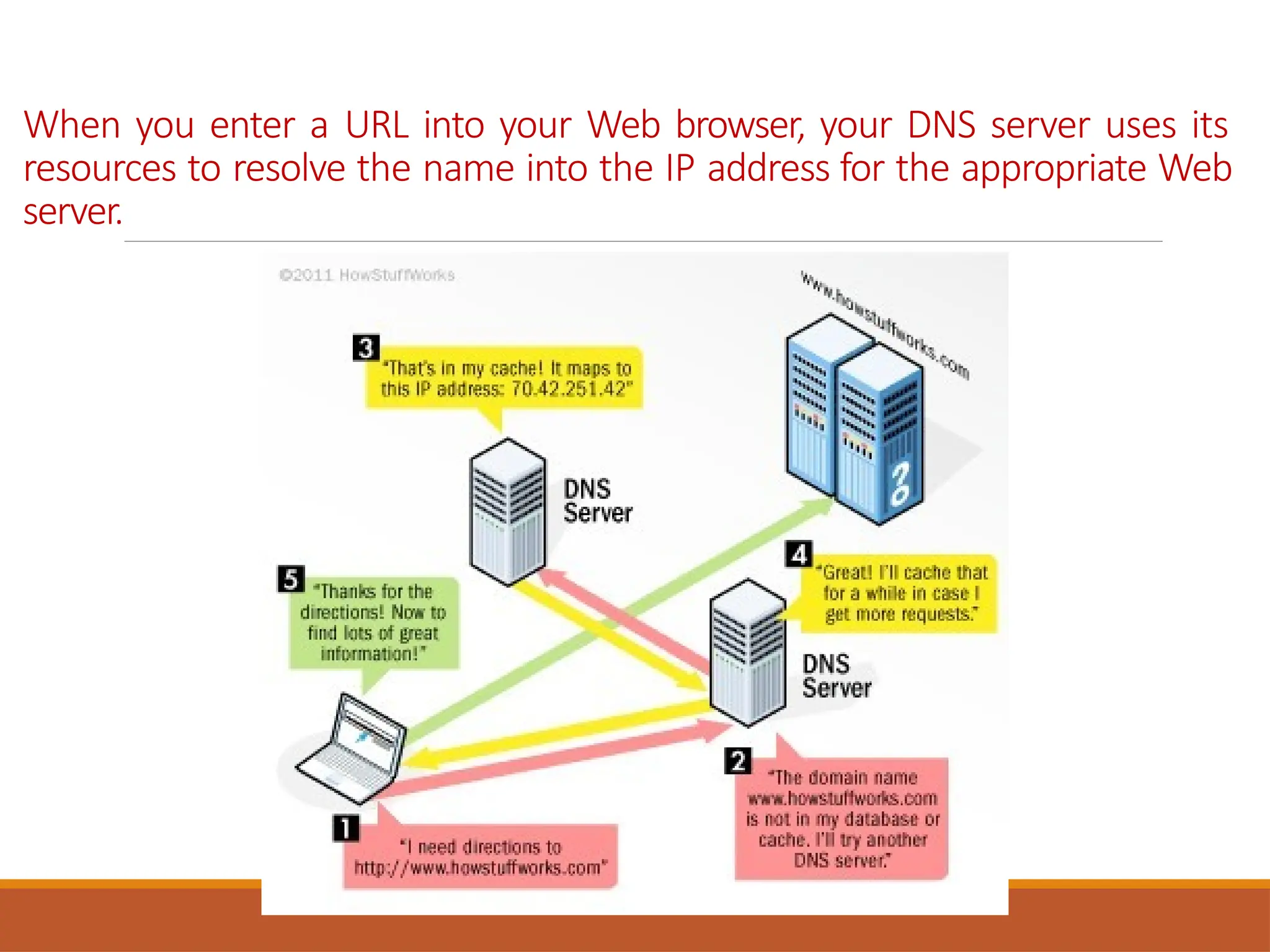
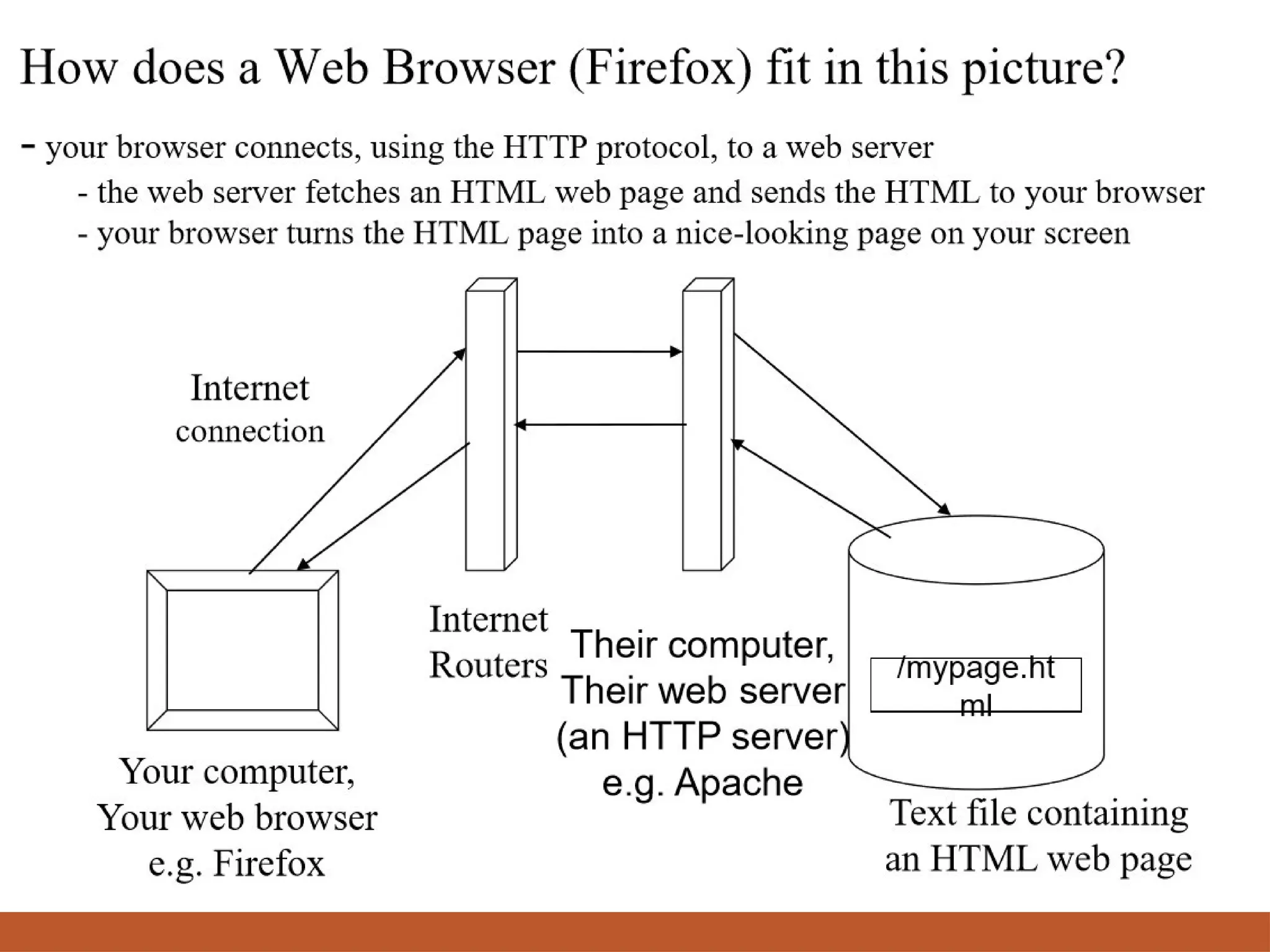
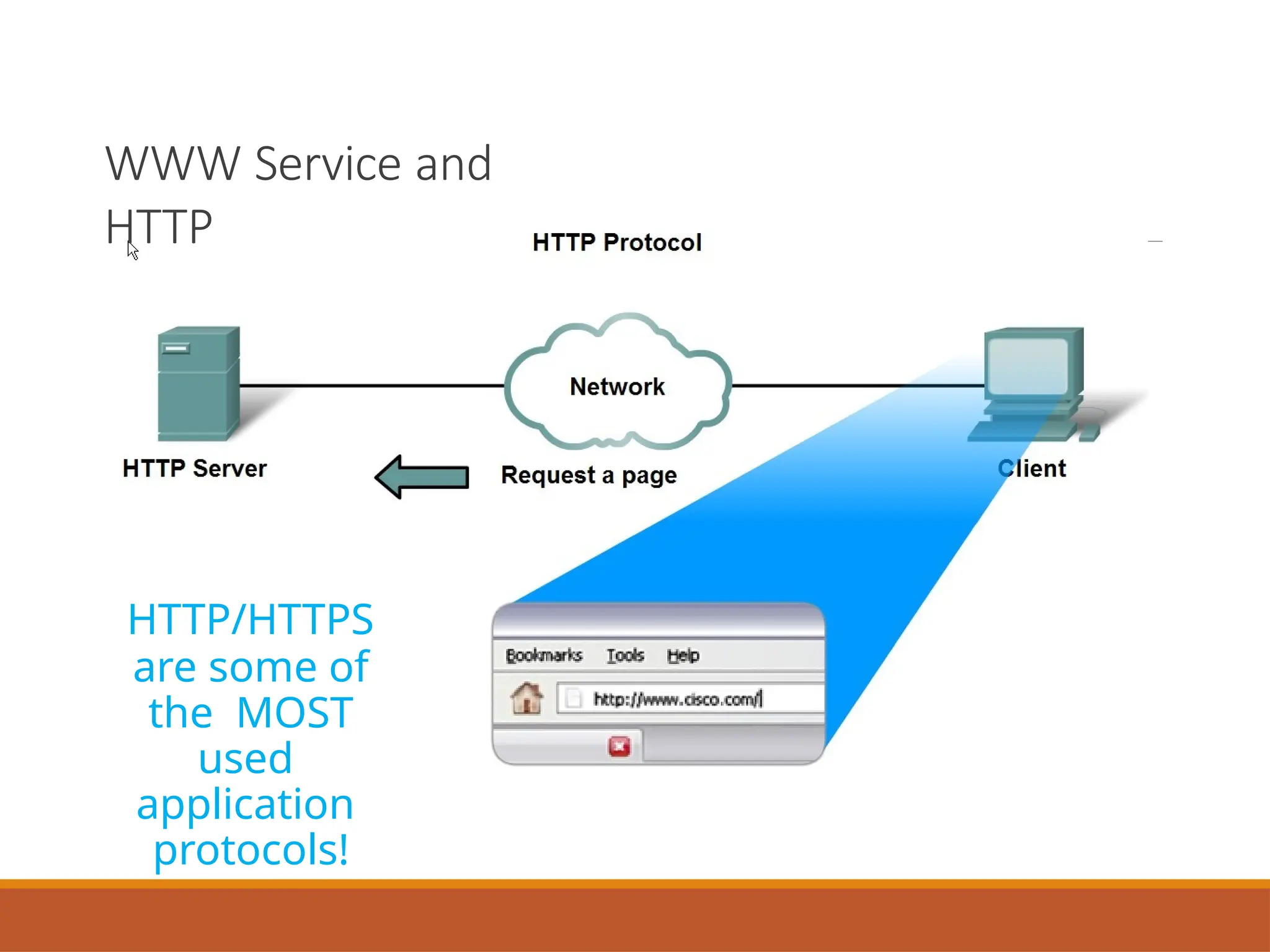
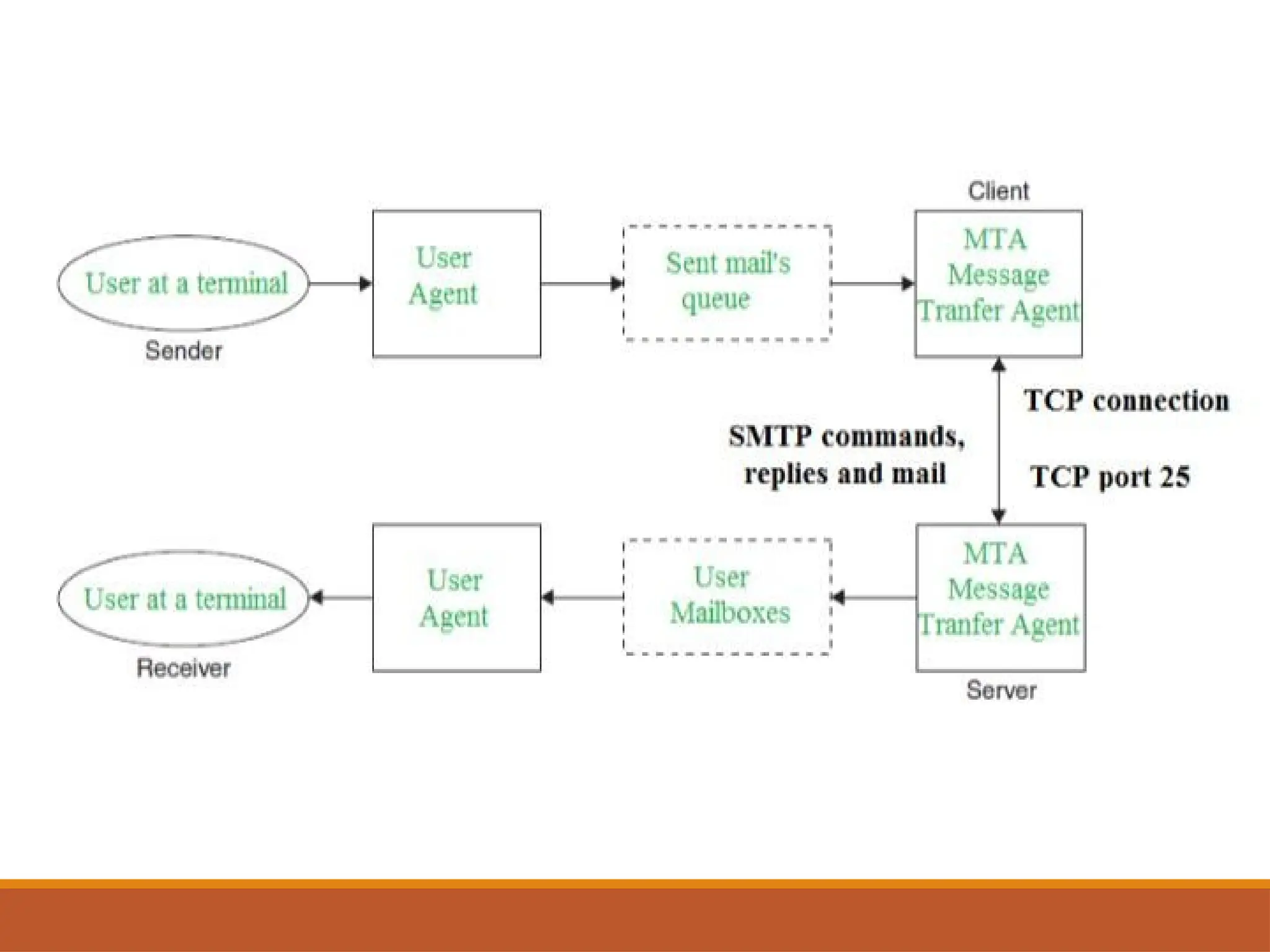
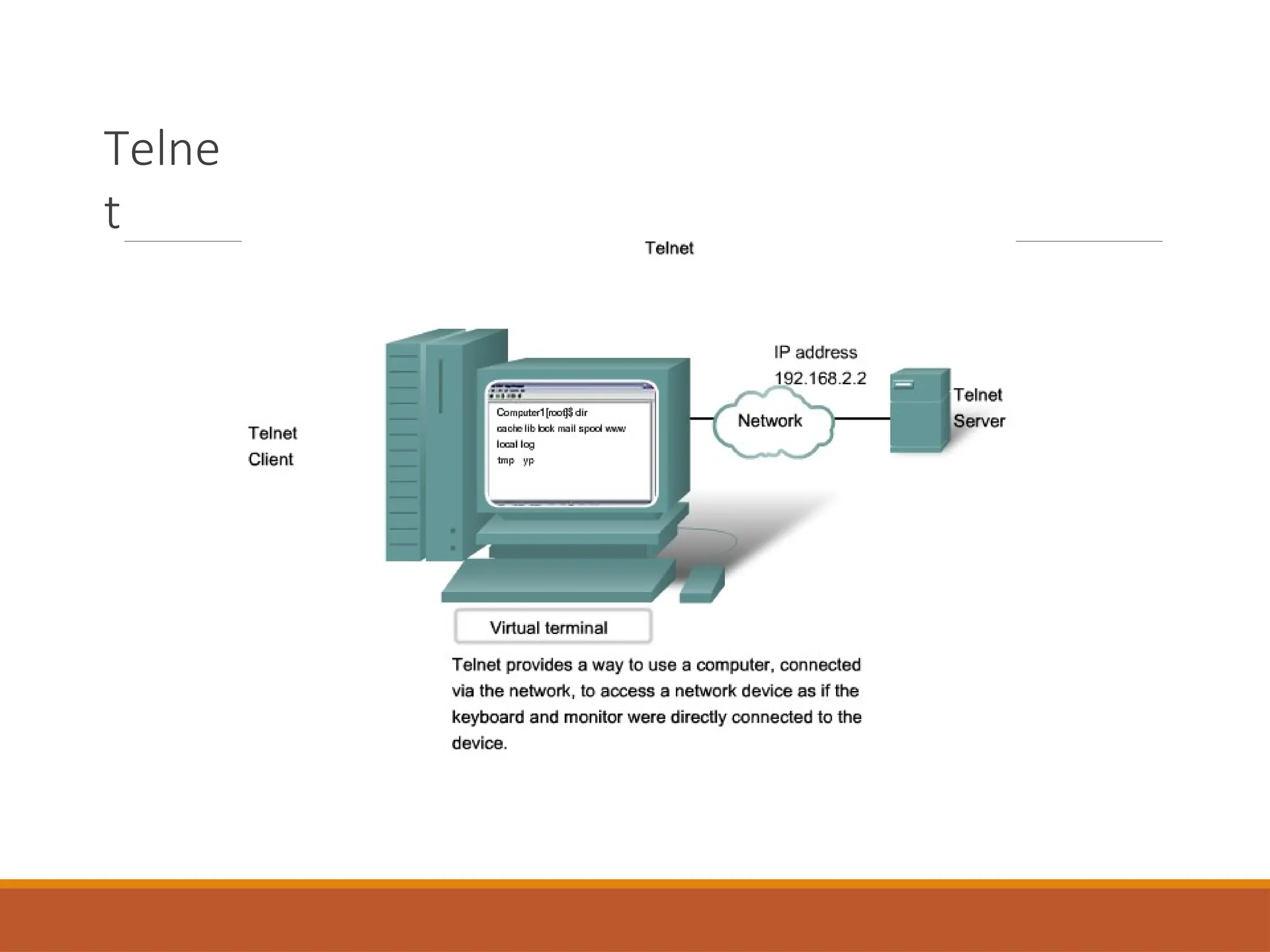
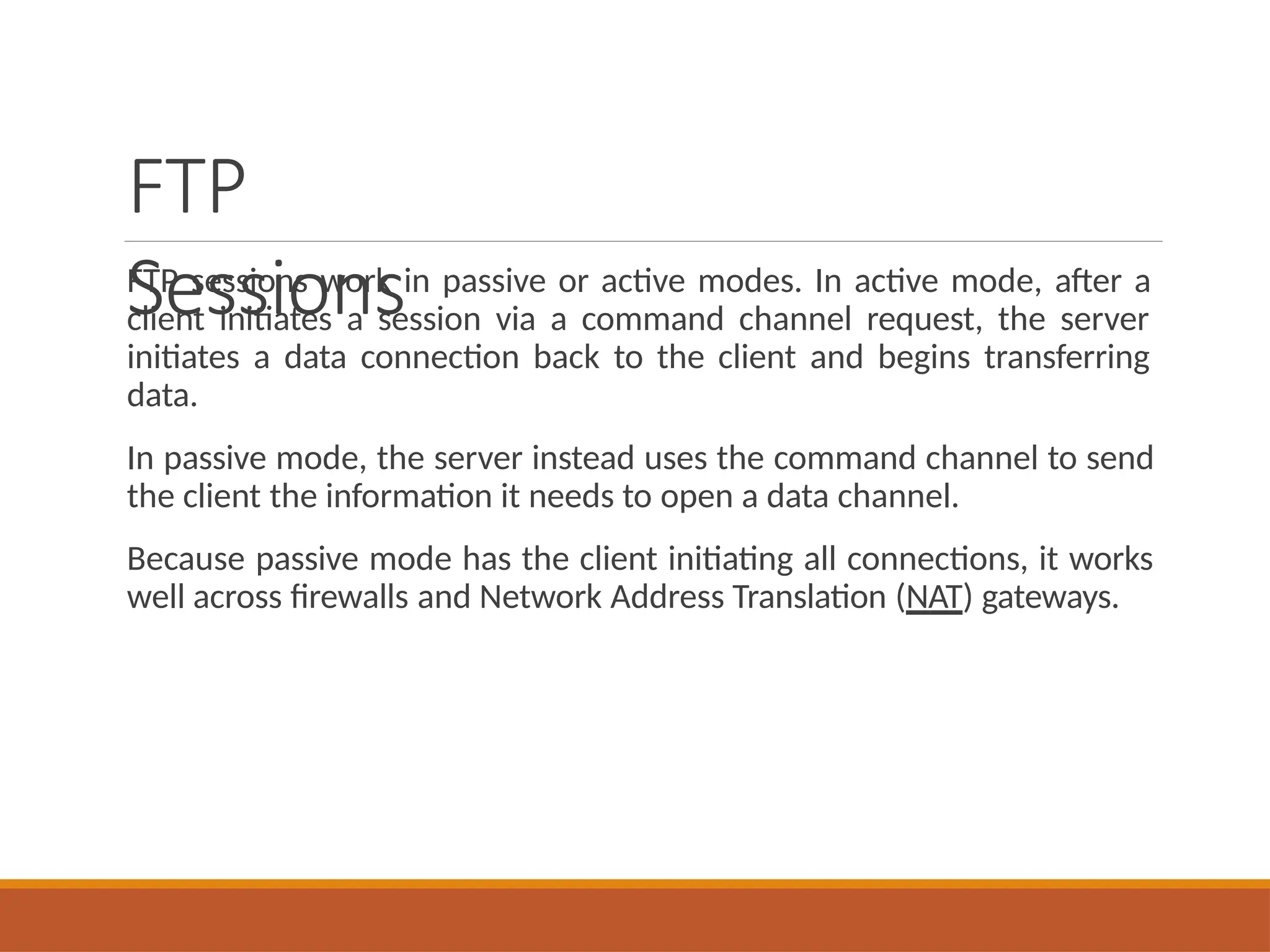
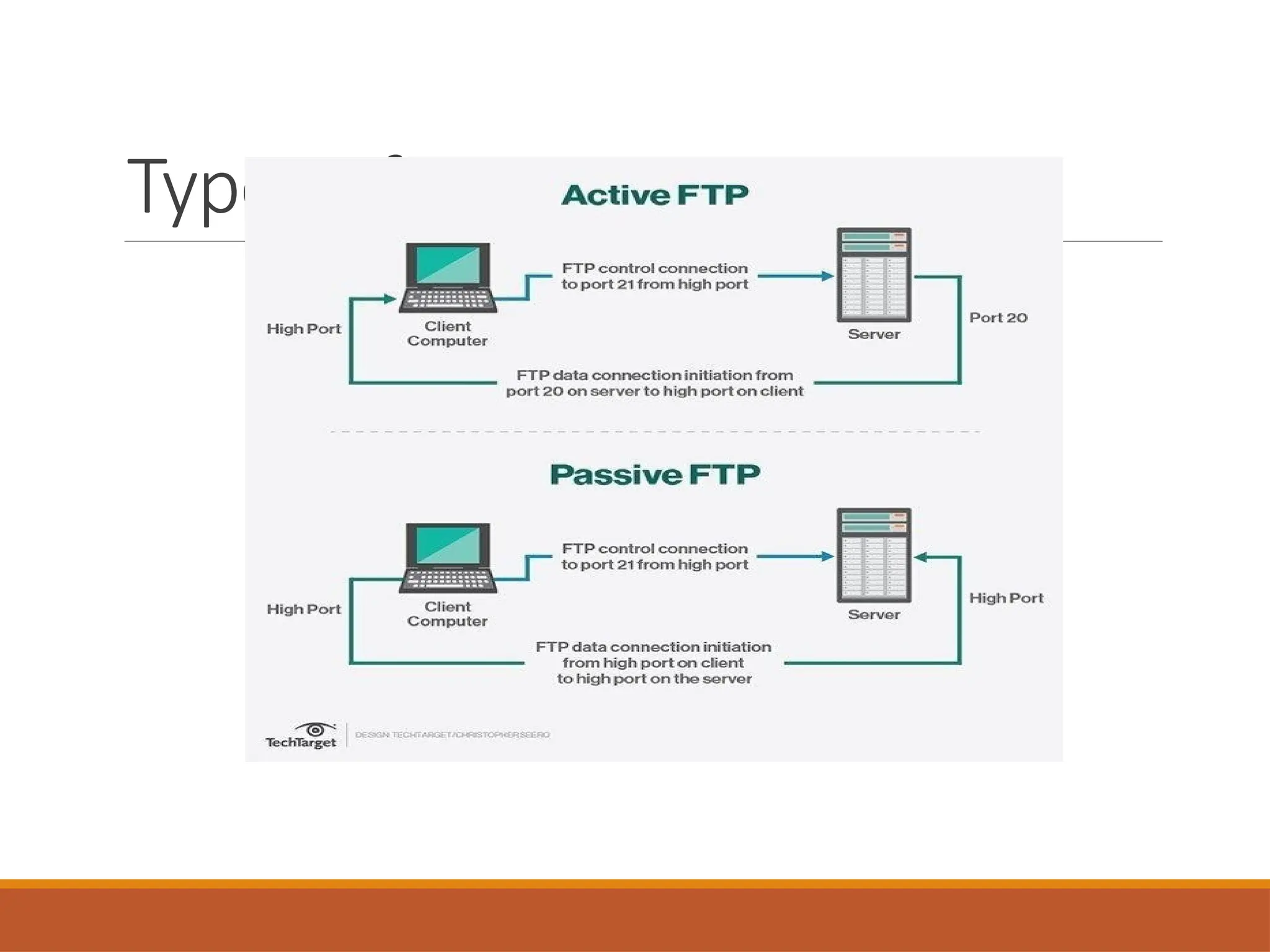
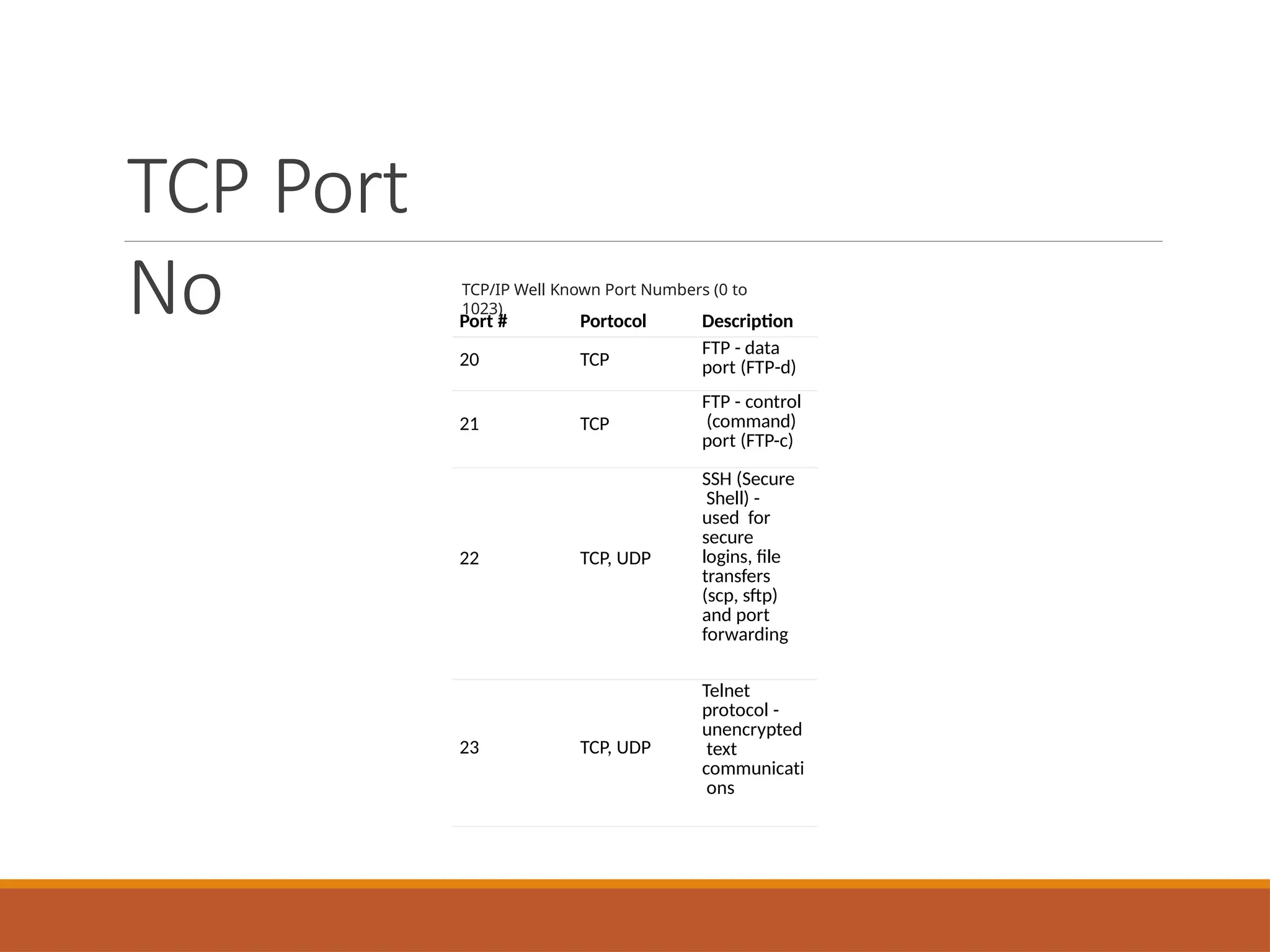
The document details the application layer of network communication, describing key protocols such as DNS, HTTP, SMTP, POP3, FTP, and DHCP. It emphasizes the functionality of these protocols in facilitating tasks like email delivery, web browsing, and file transfer, alongside outlining the differences between client/server and peer-to-peer models. Additionally, it discusses security implications and operational characteristics of each protocol, providing insights into how devices communicate over the web.