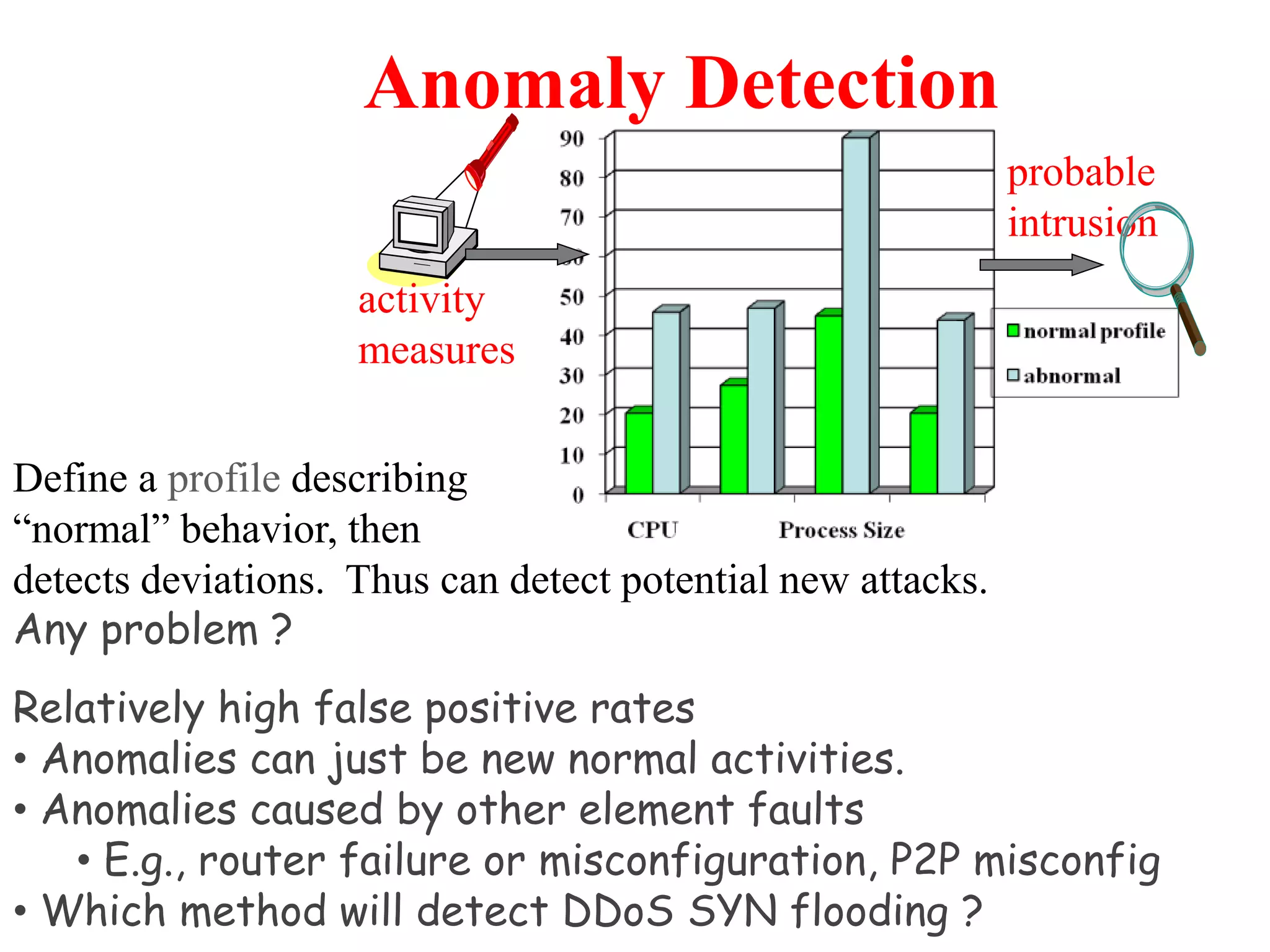
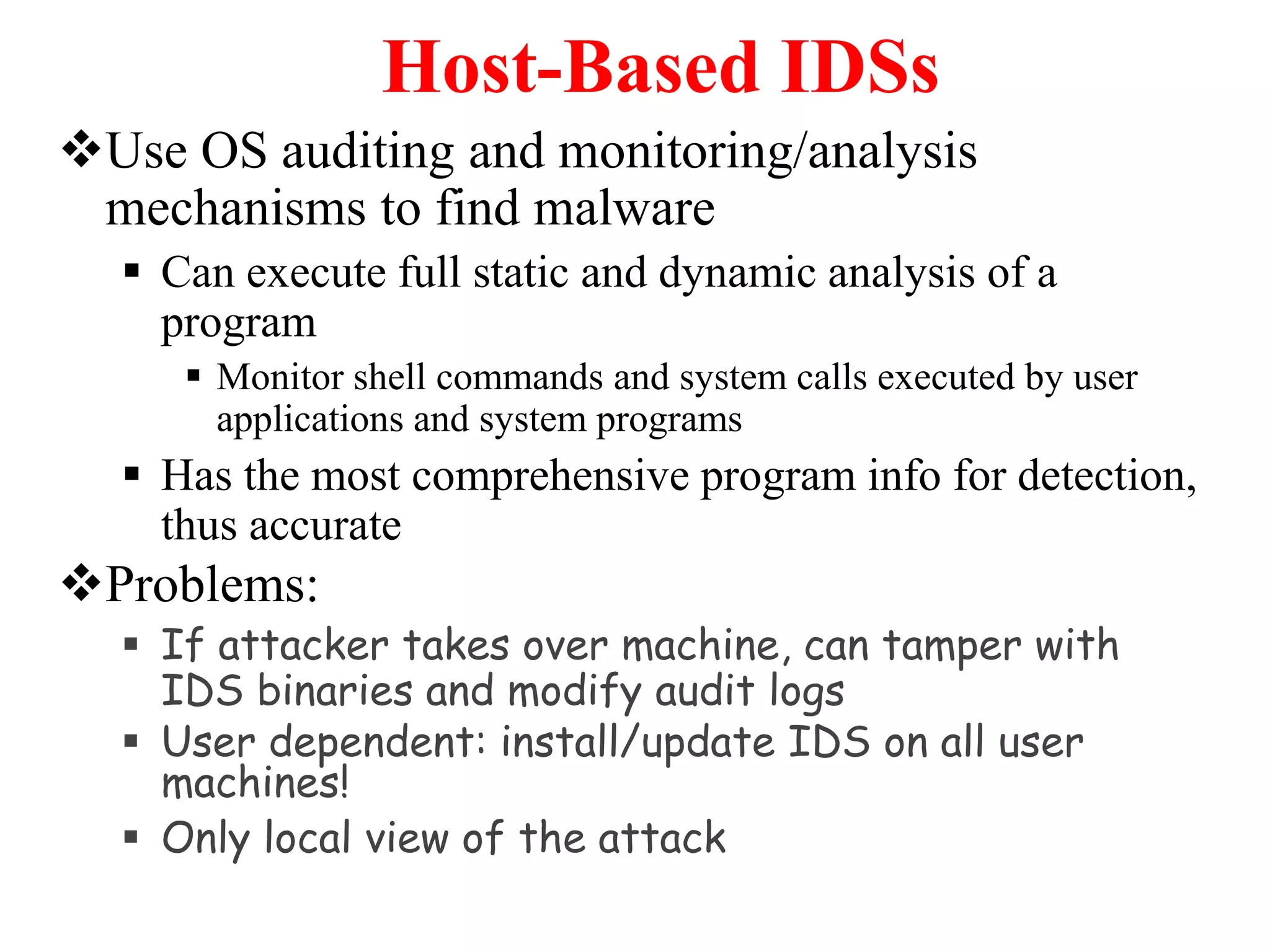
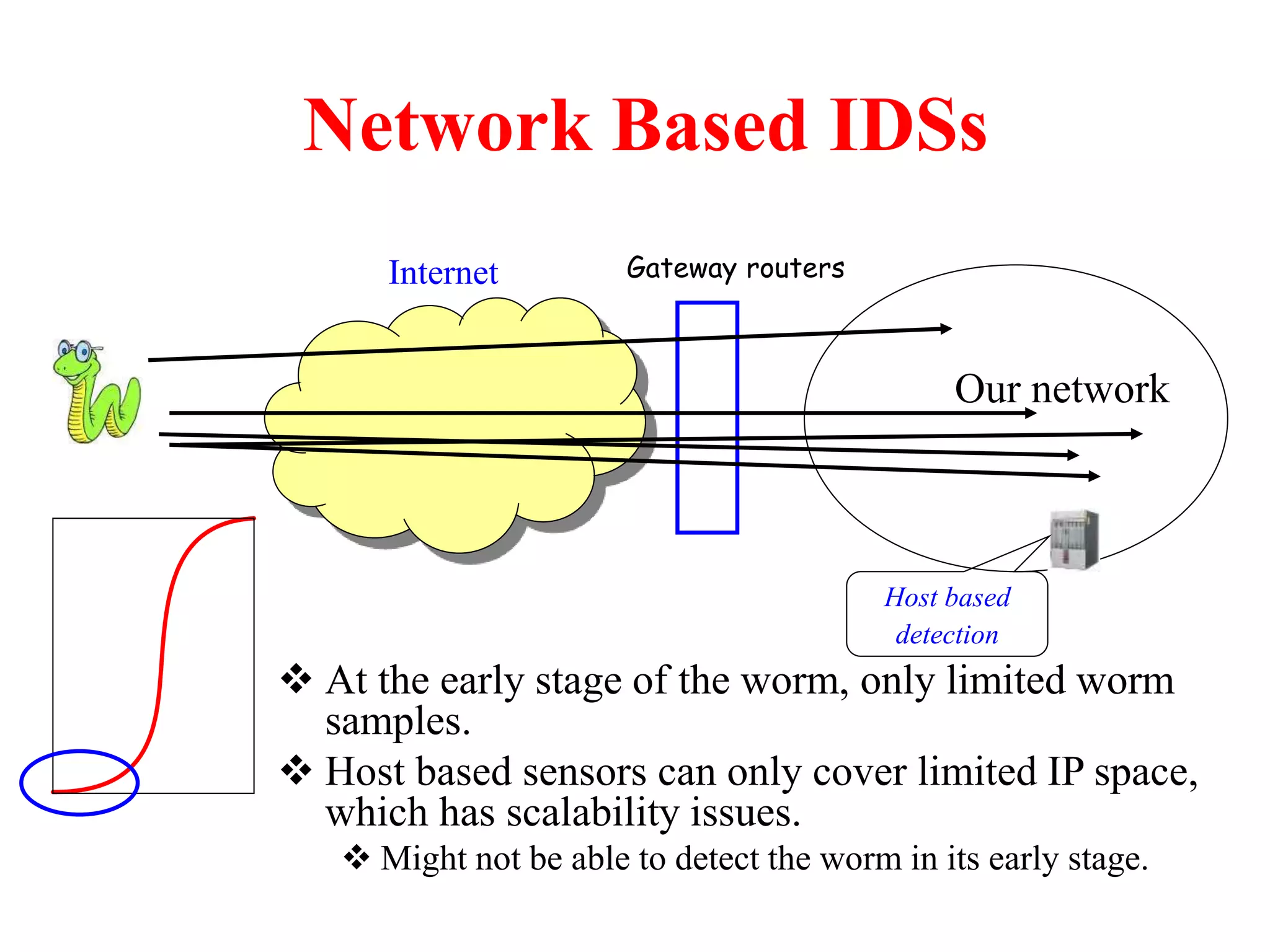
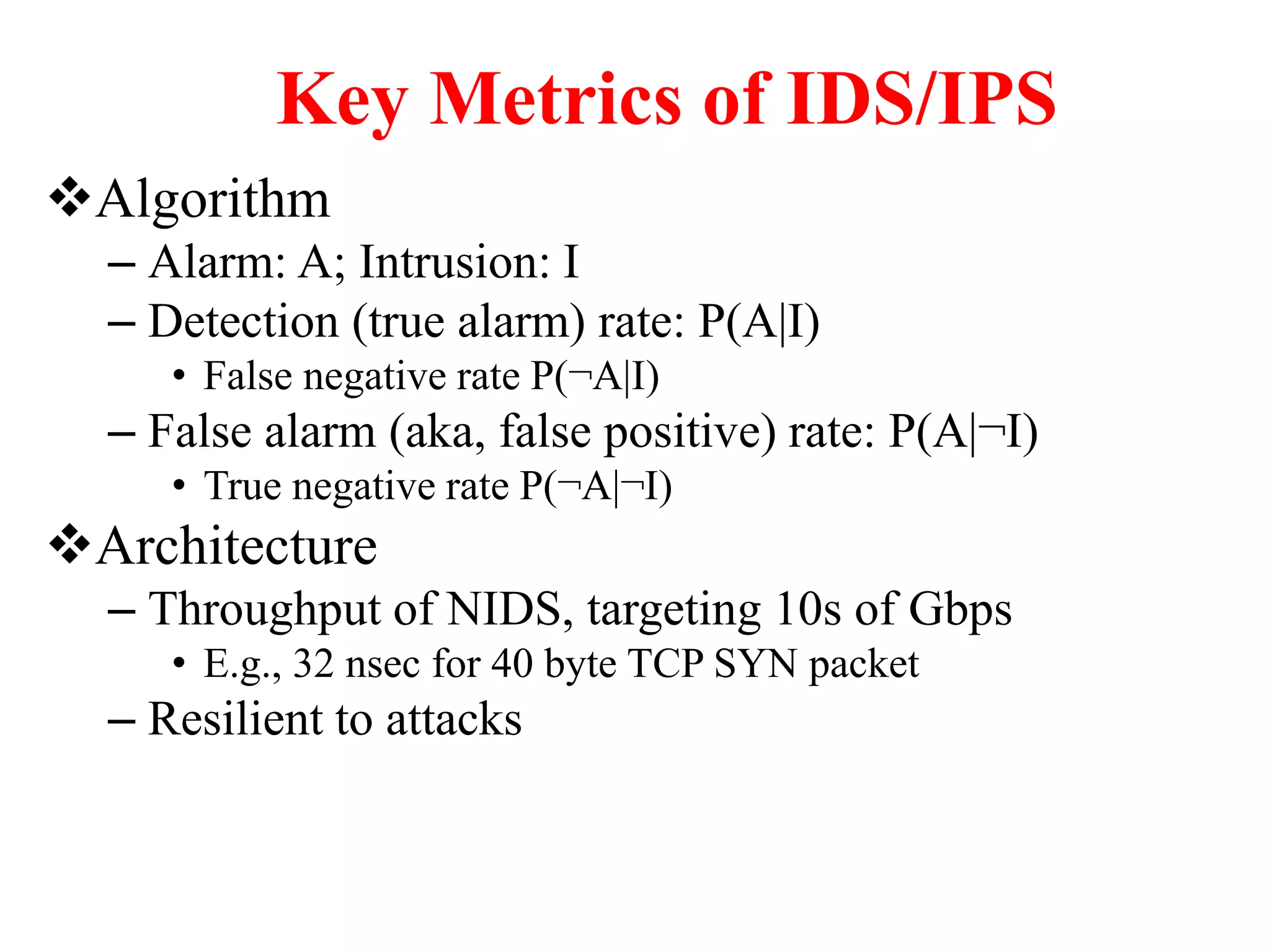
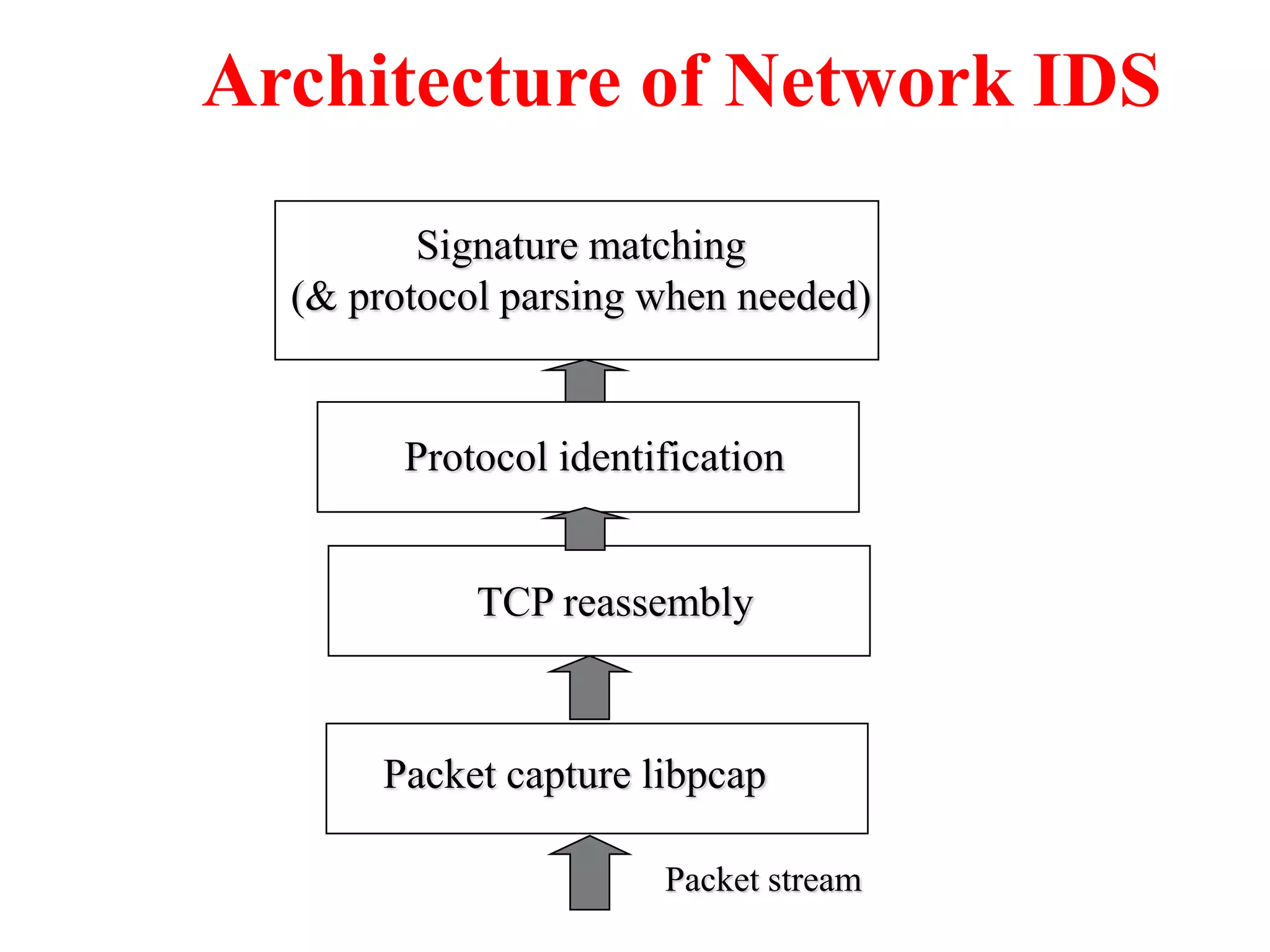
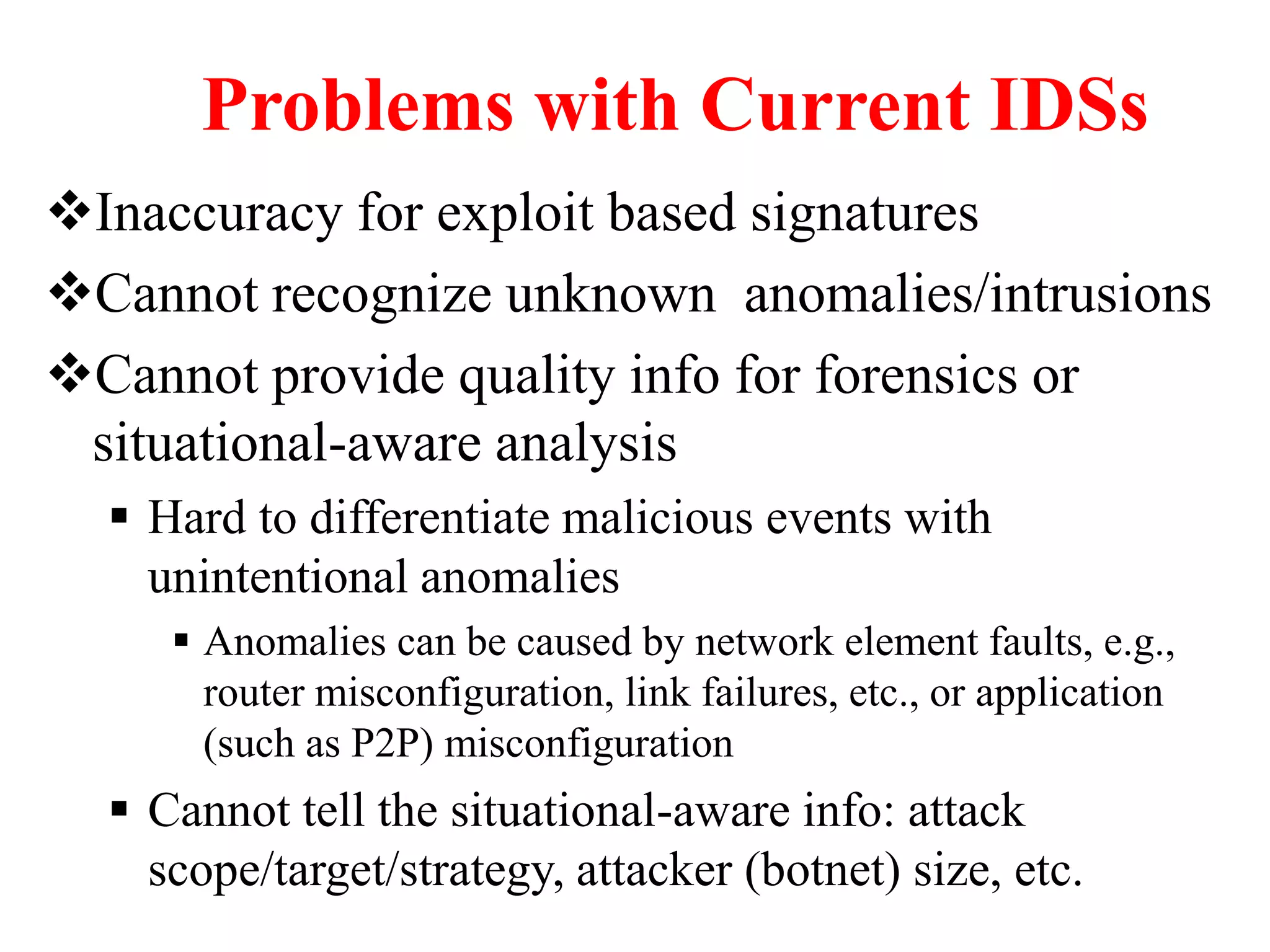
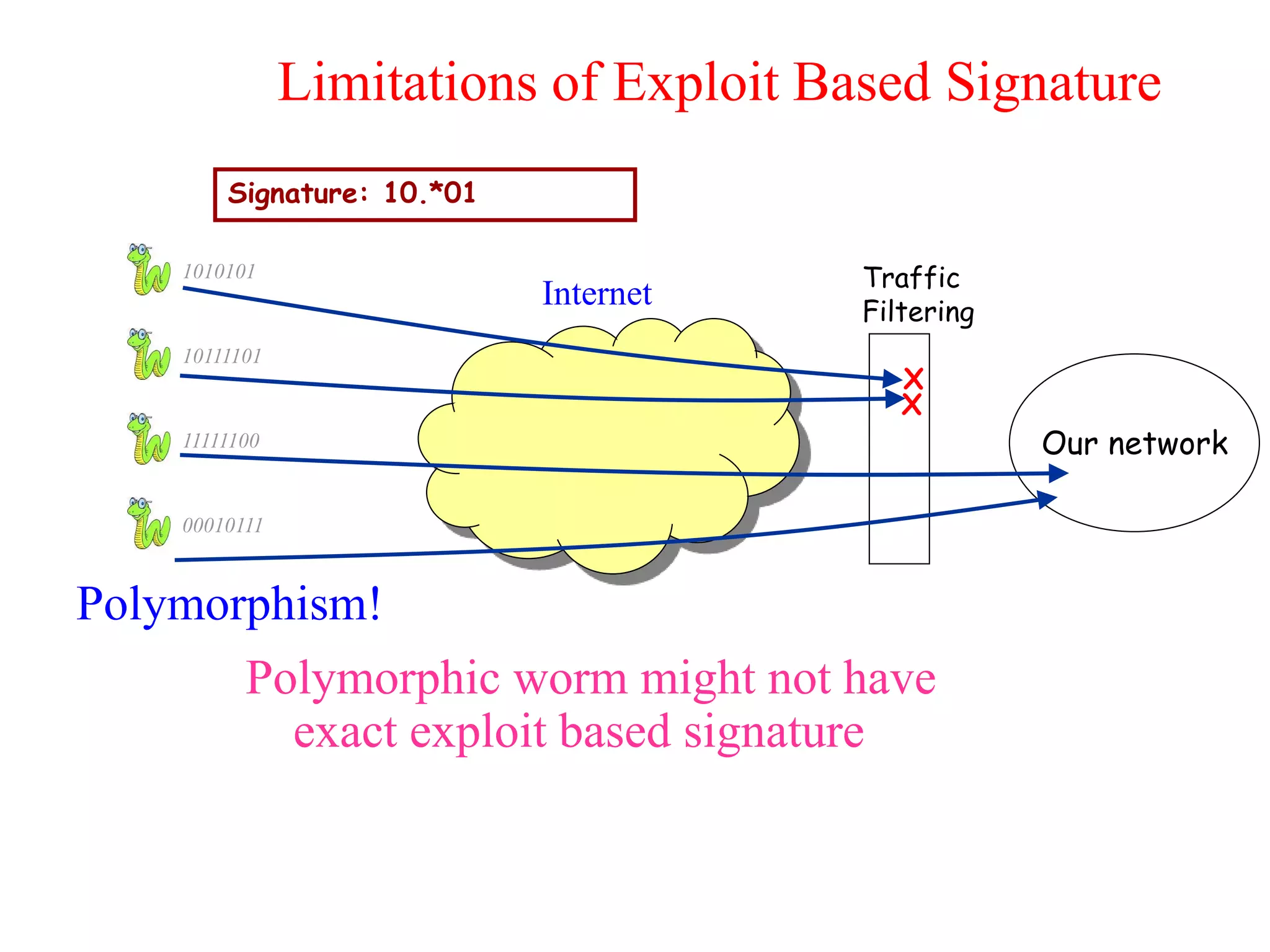
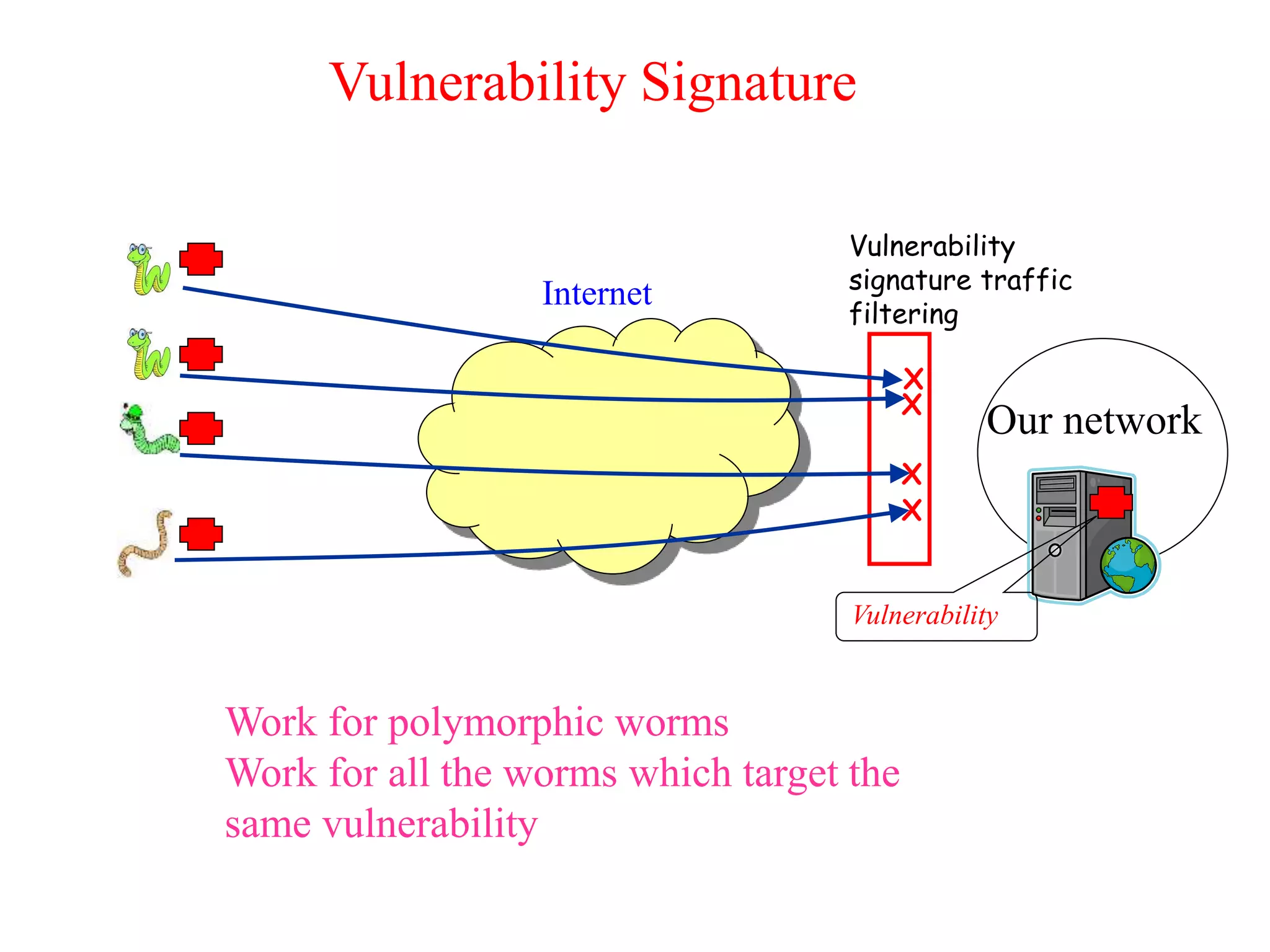
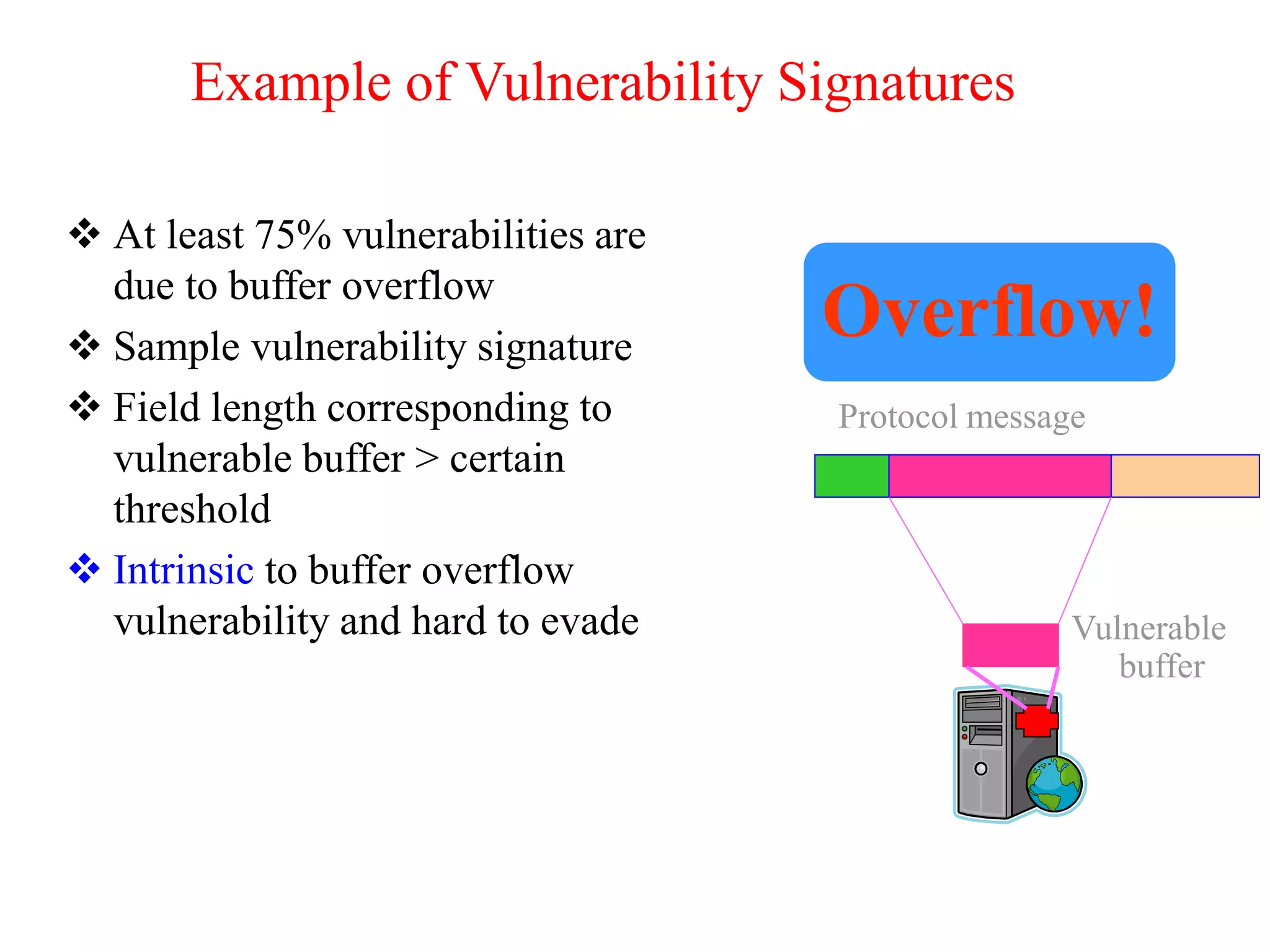
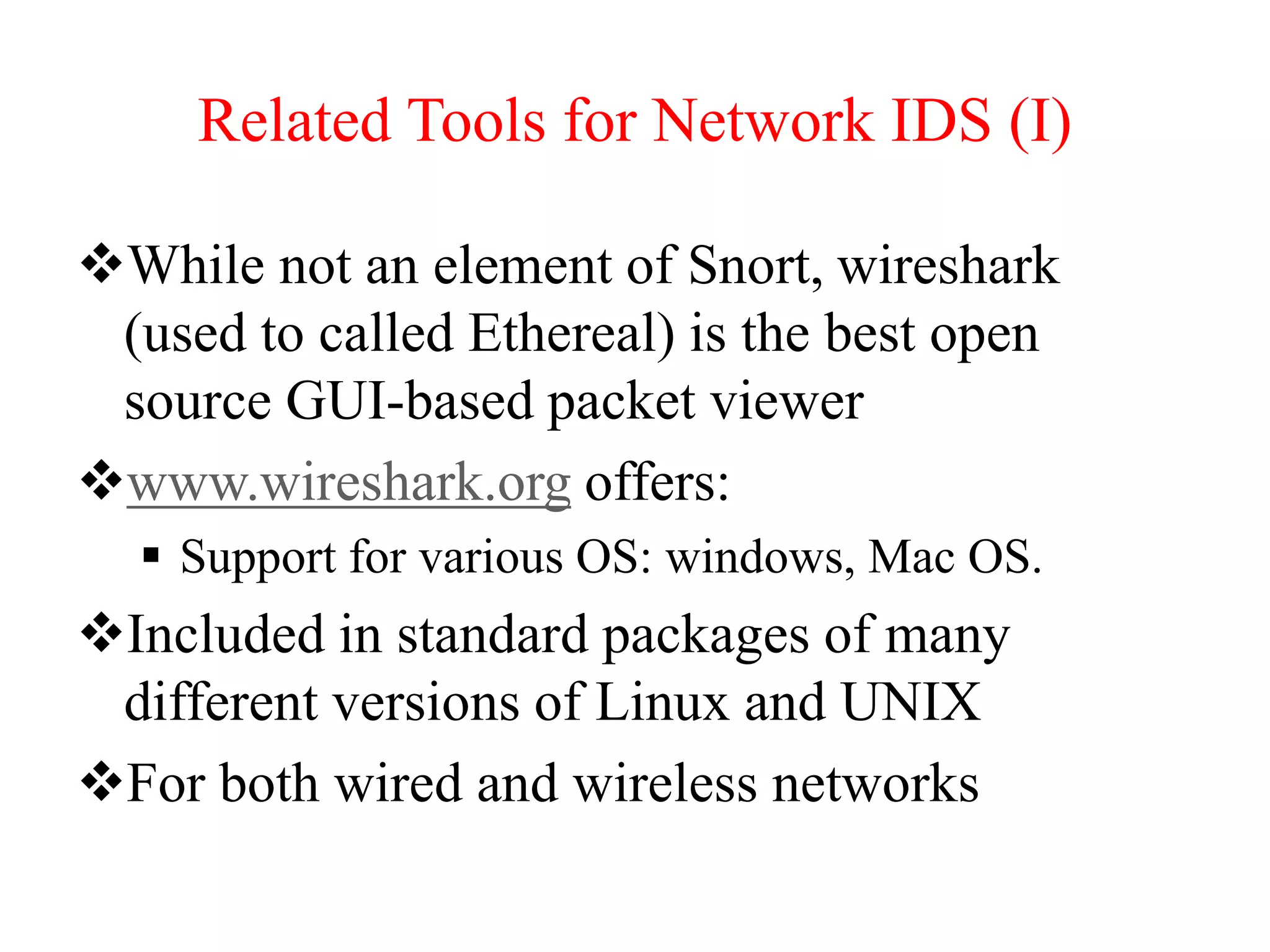
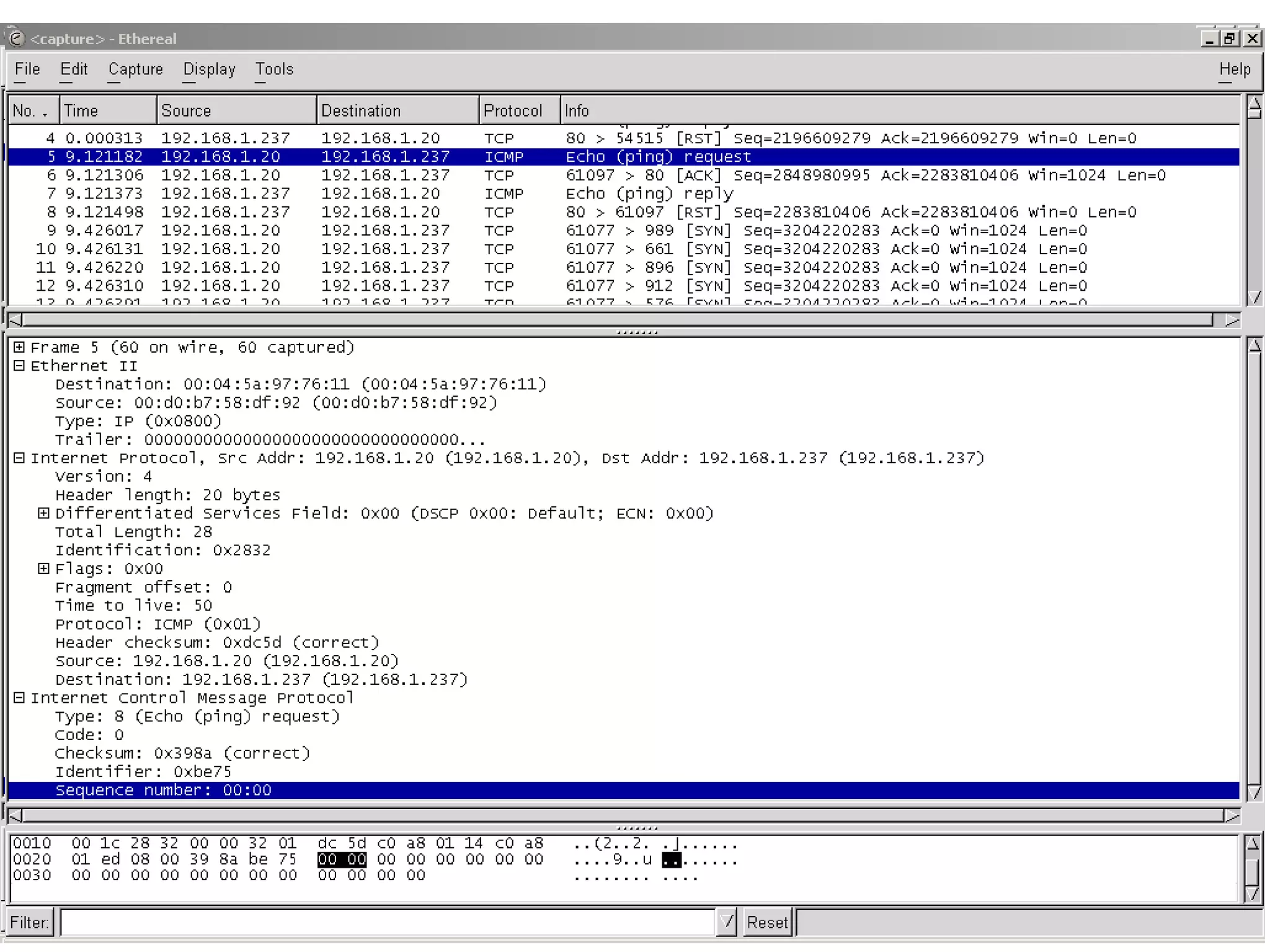
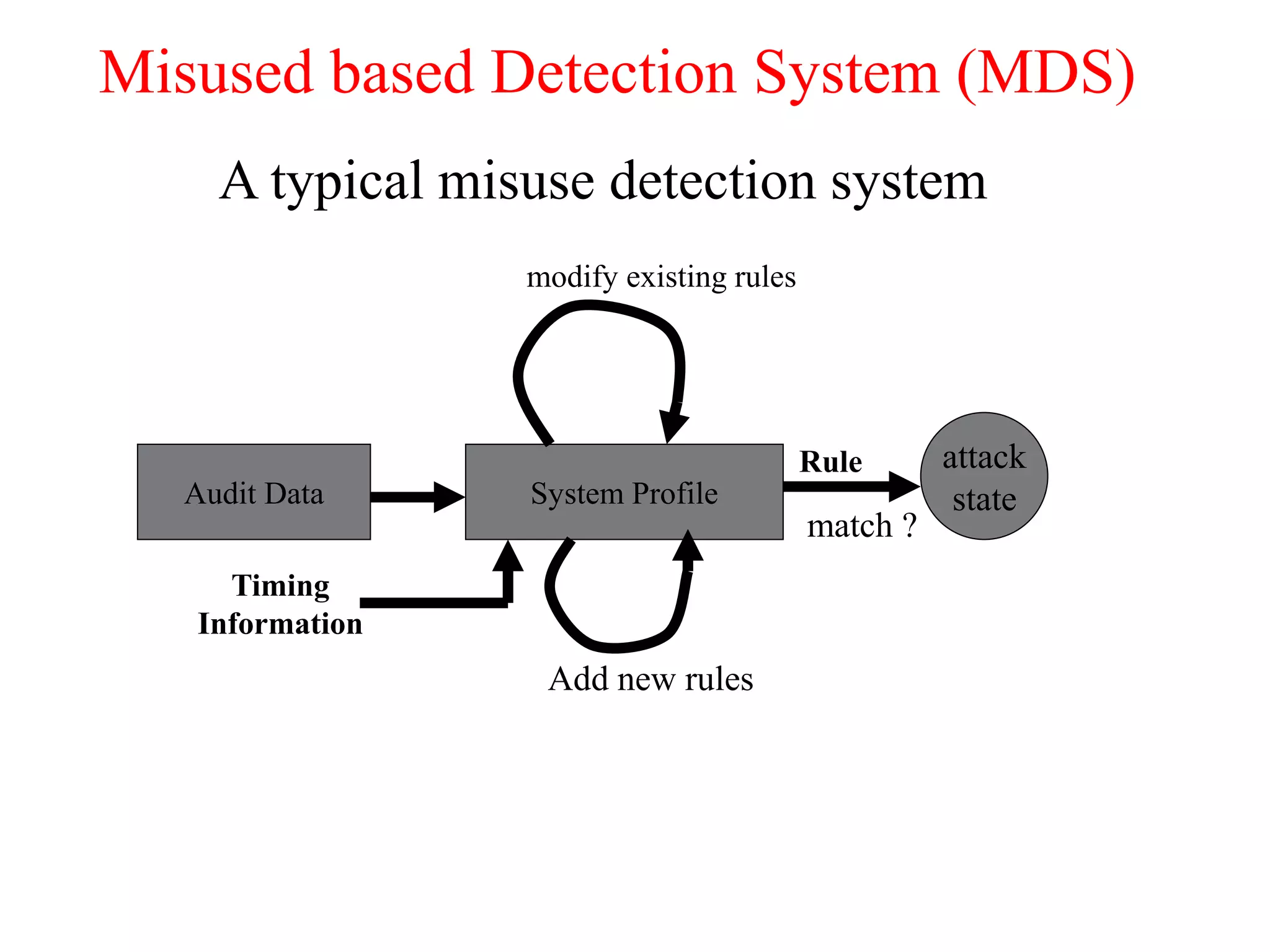
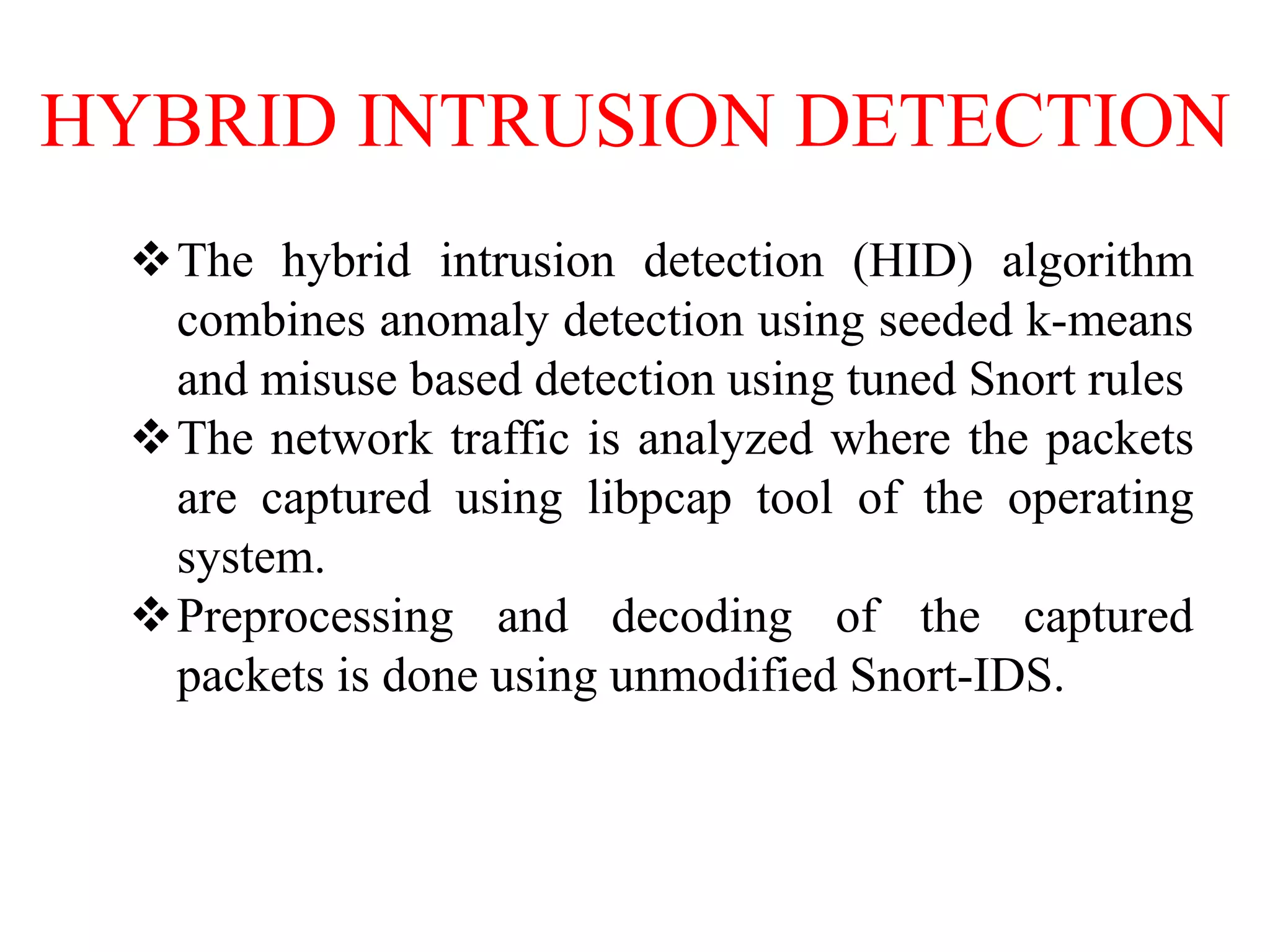
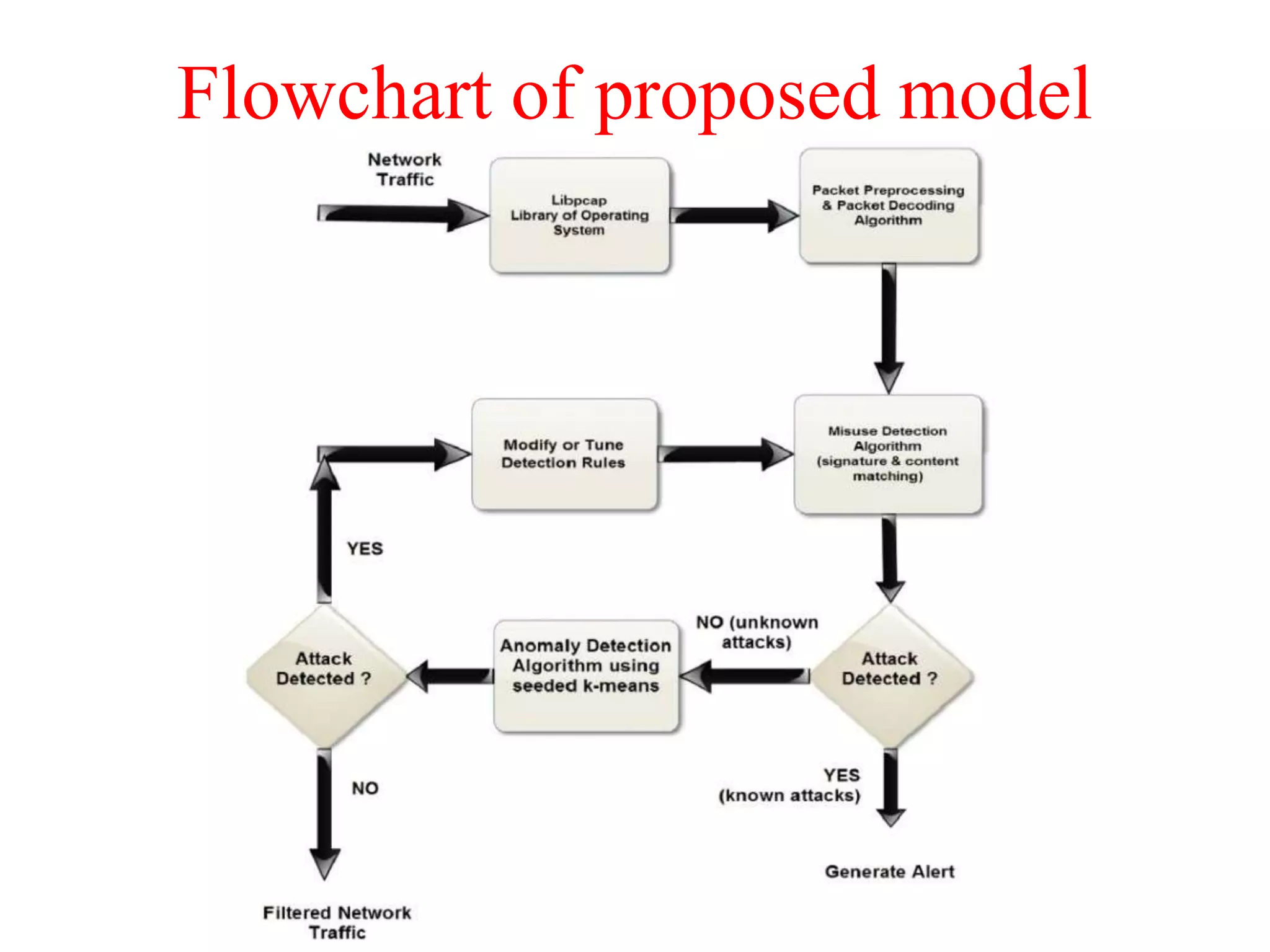
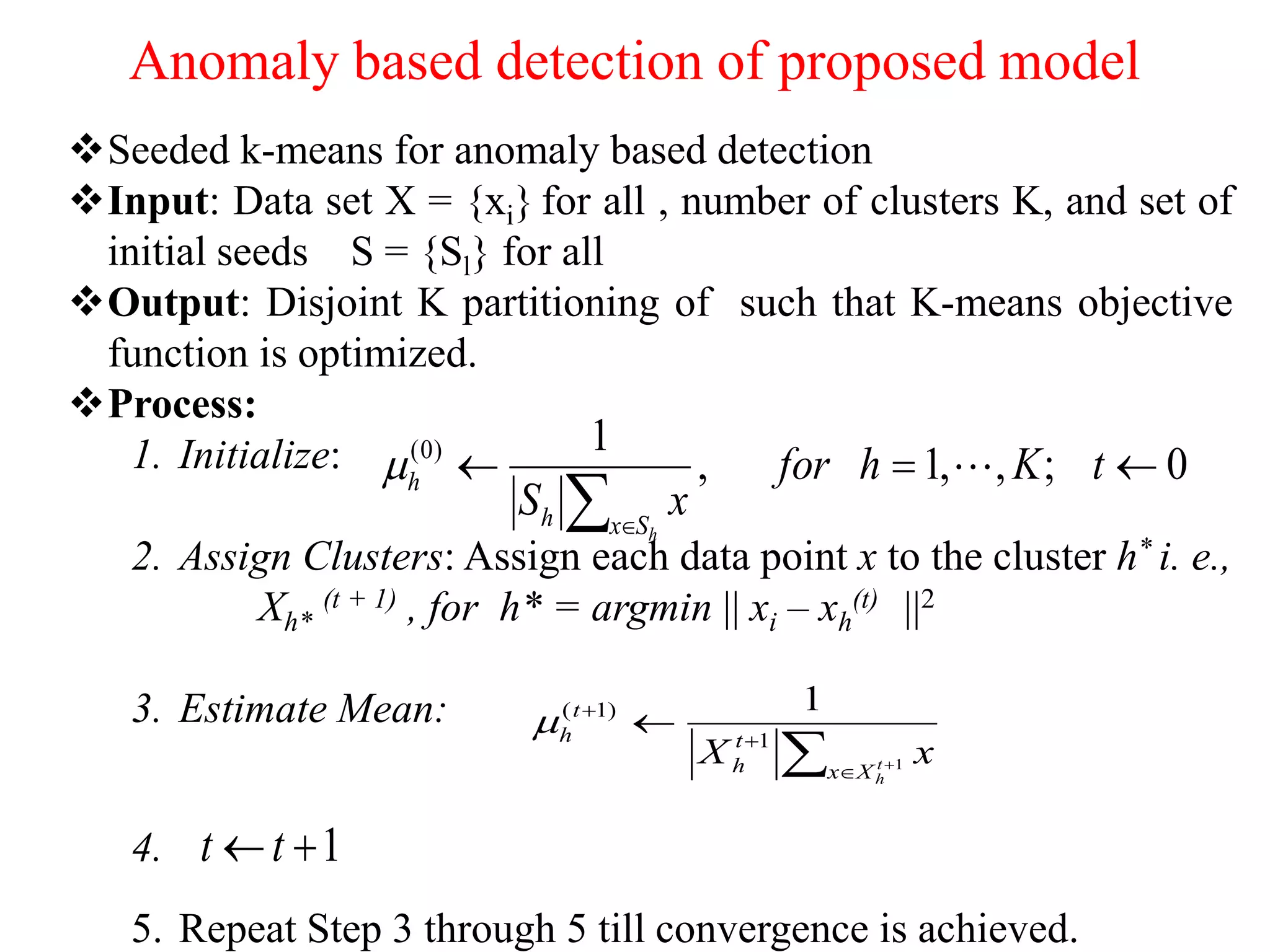
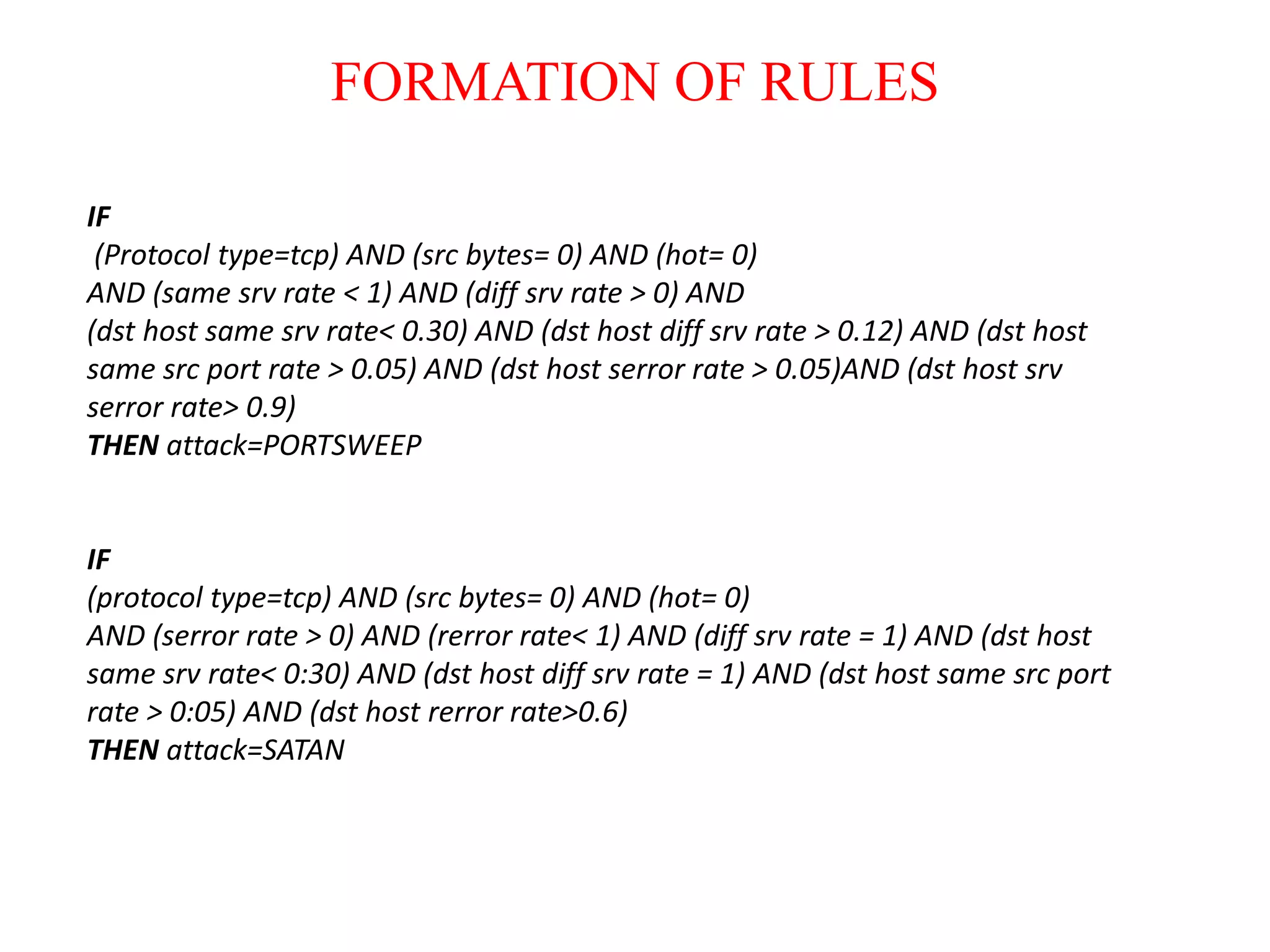
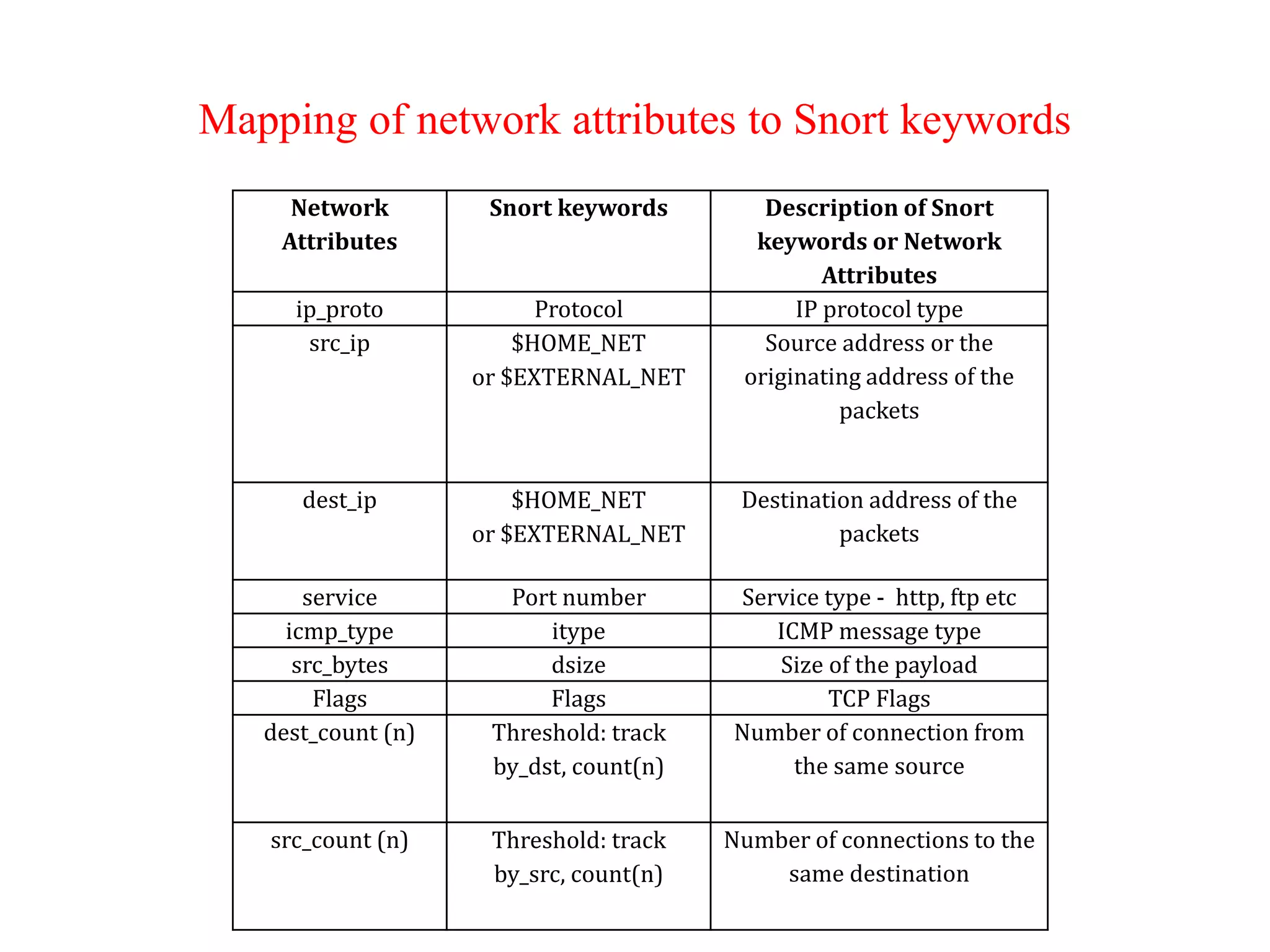
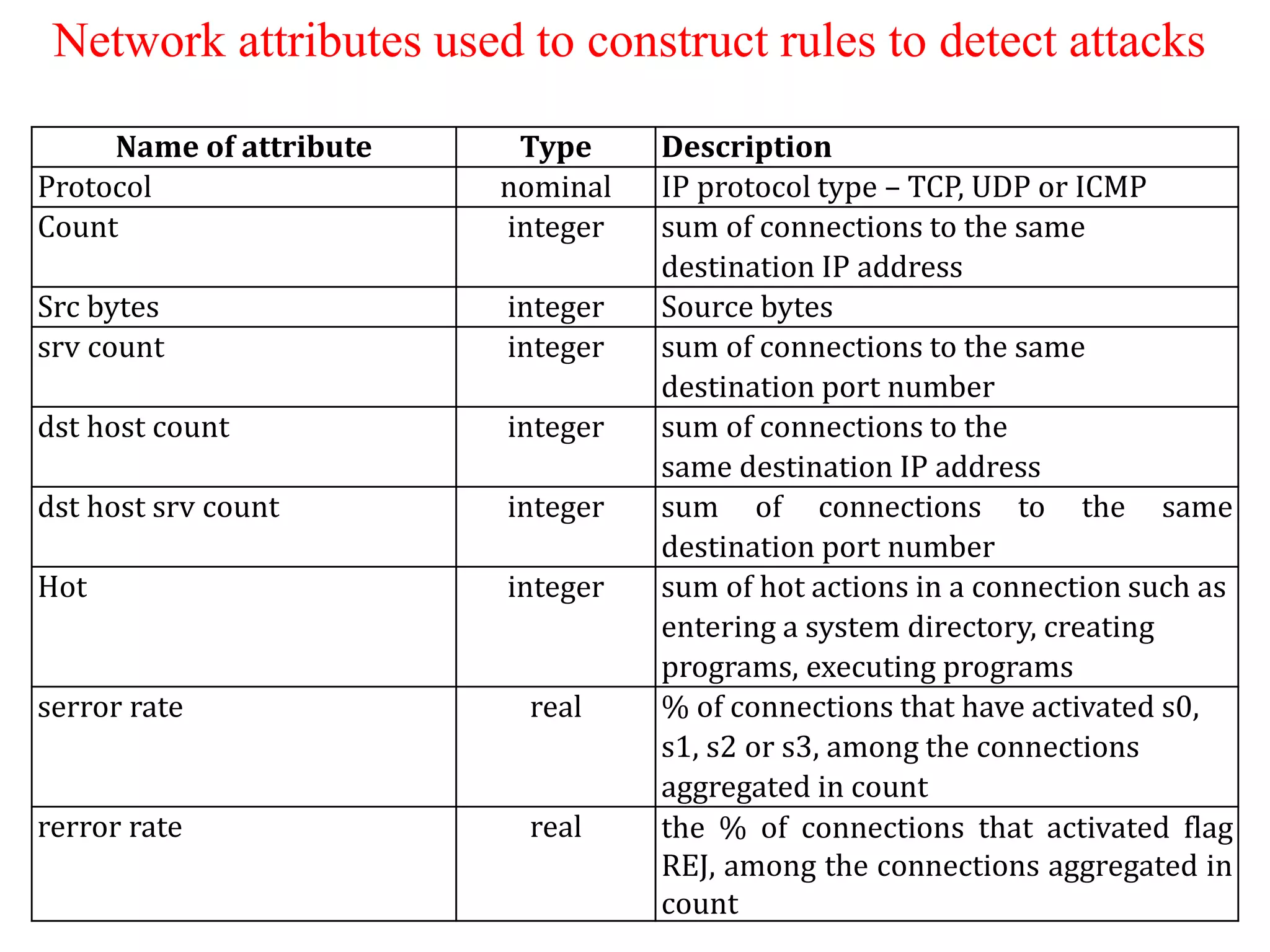
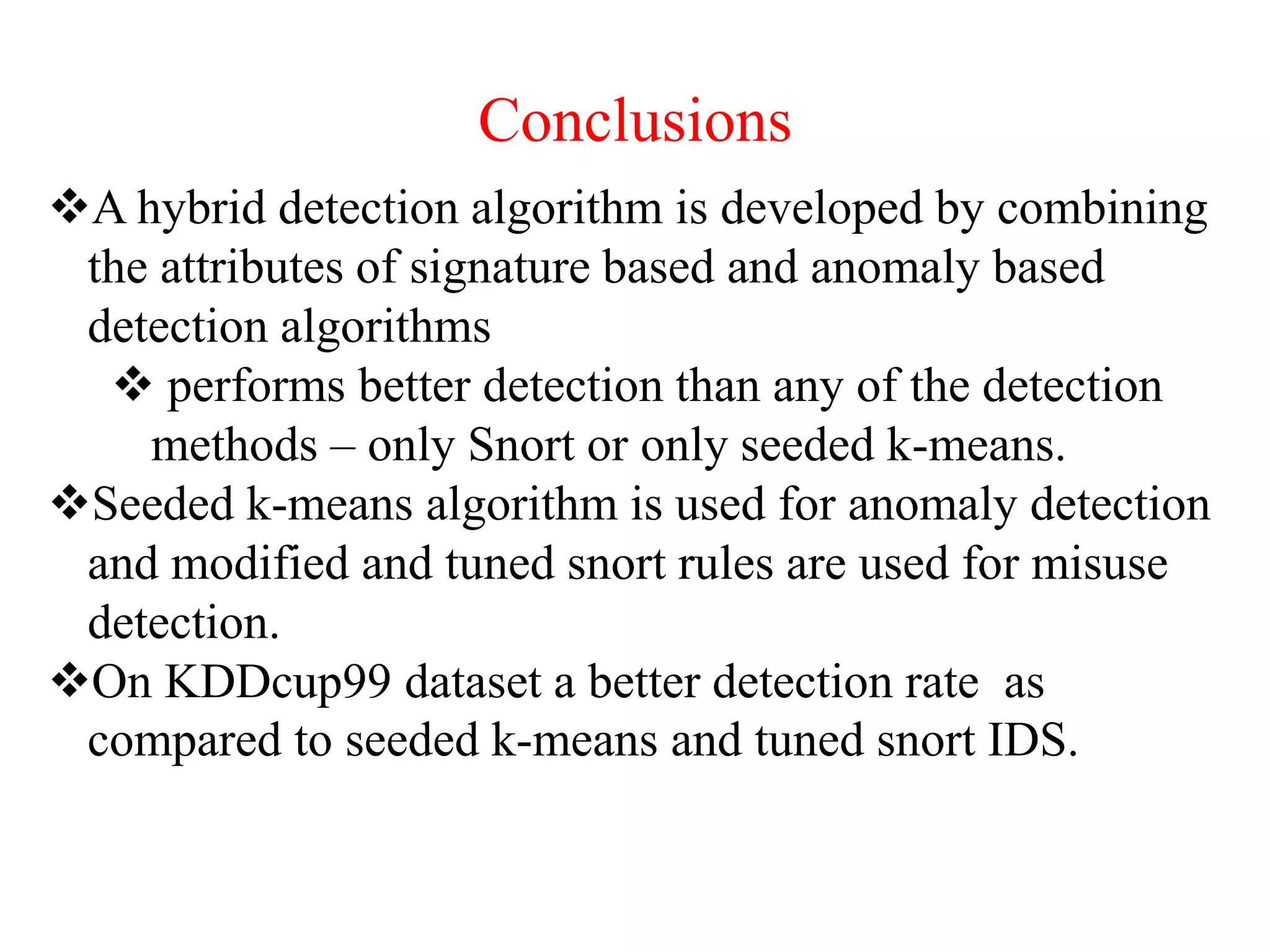
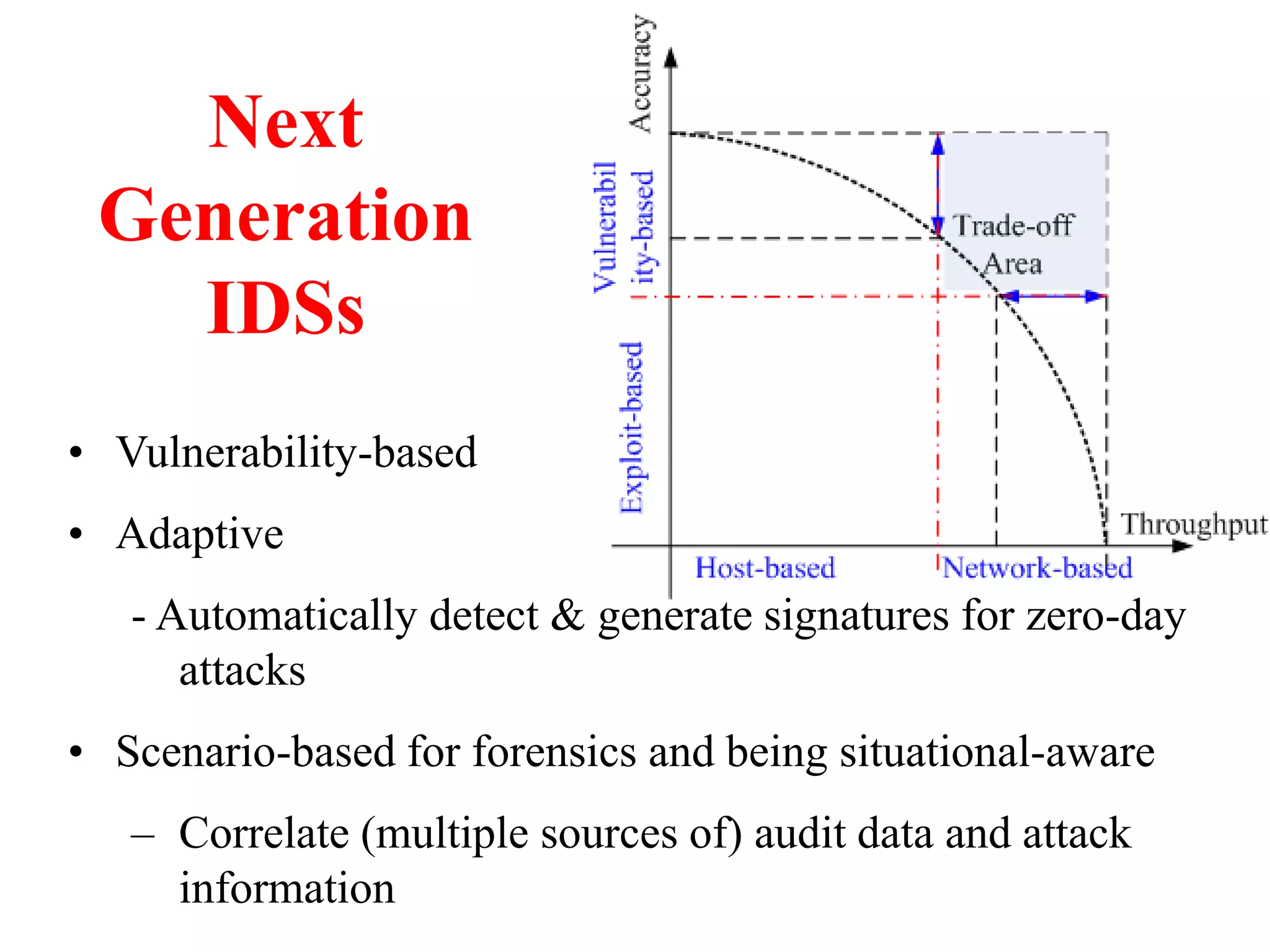
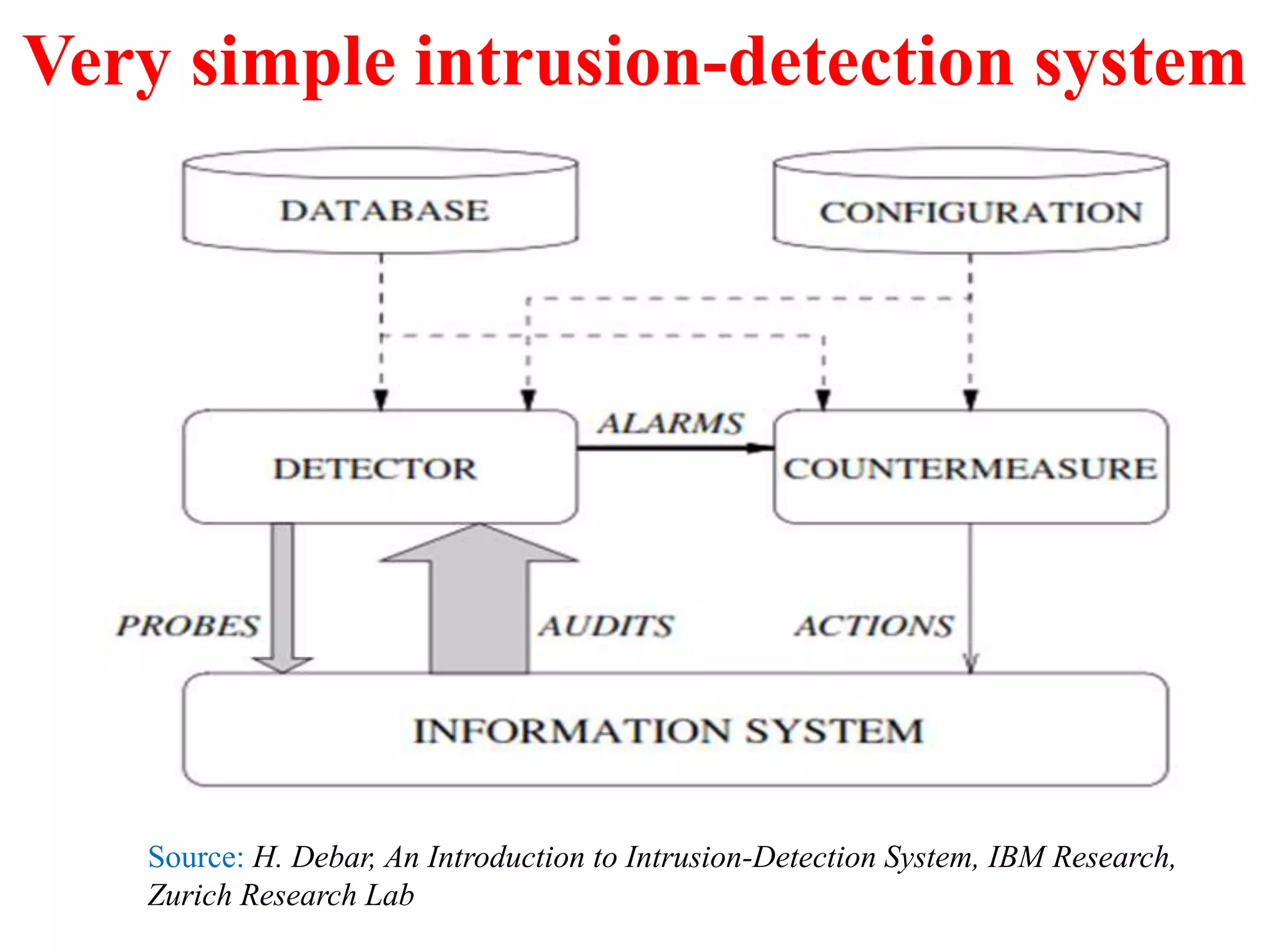
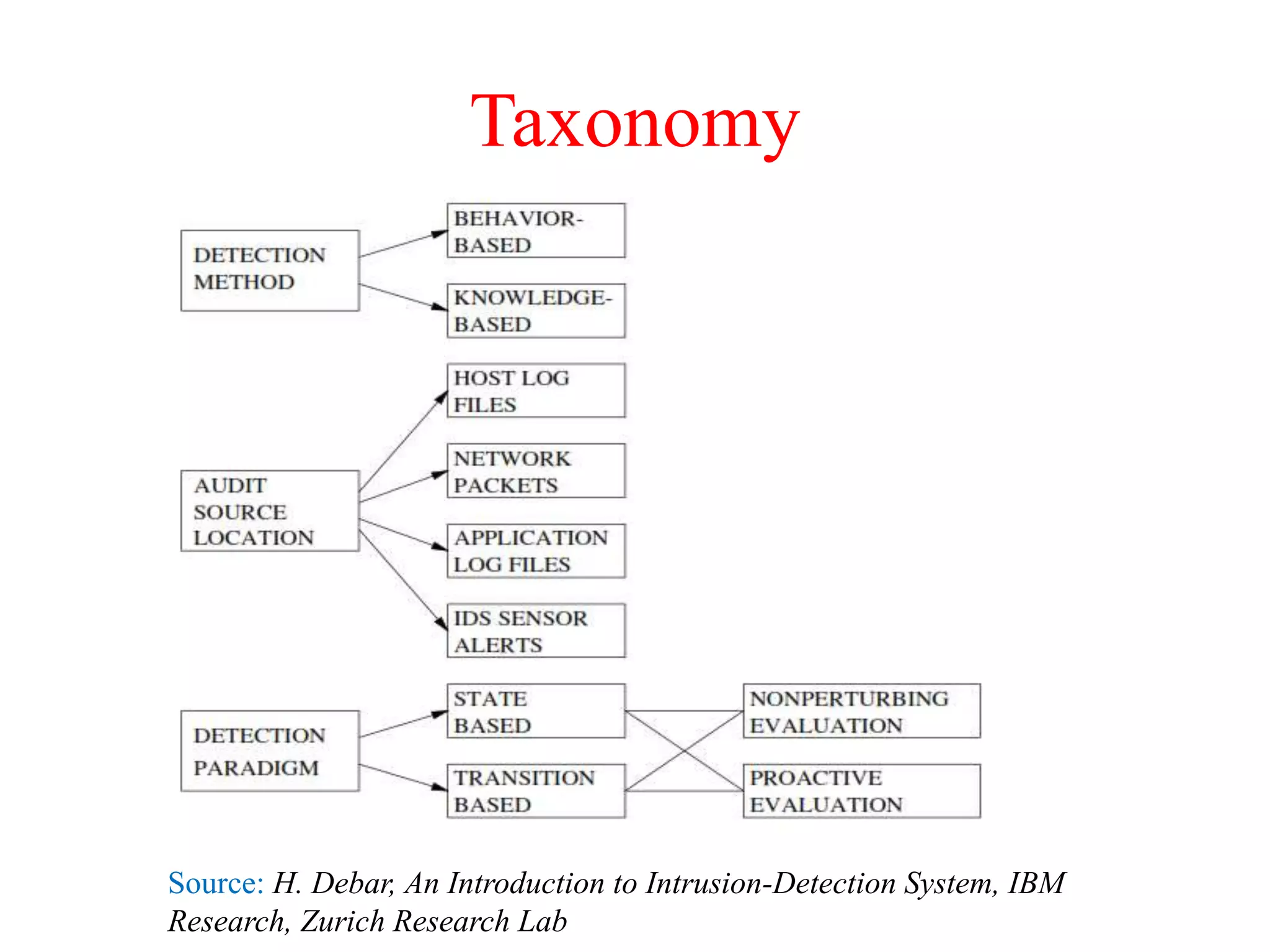
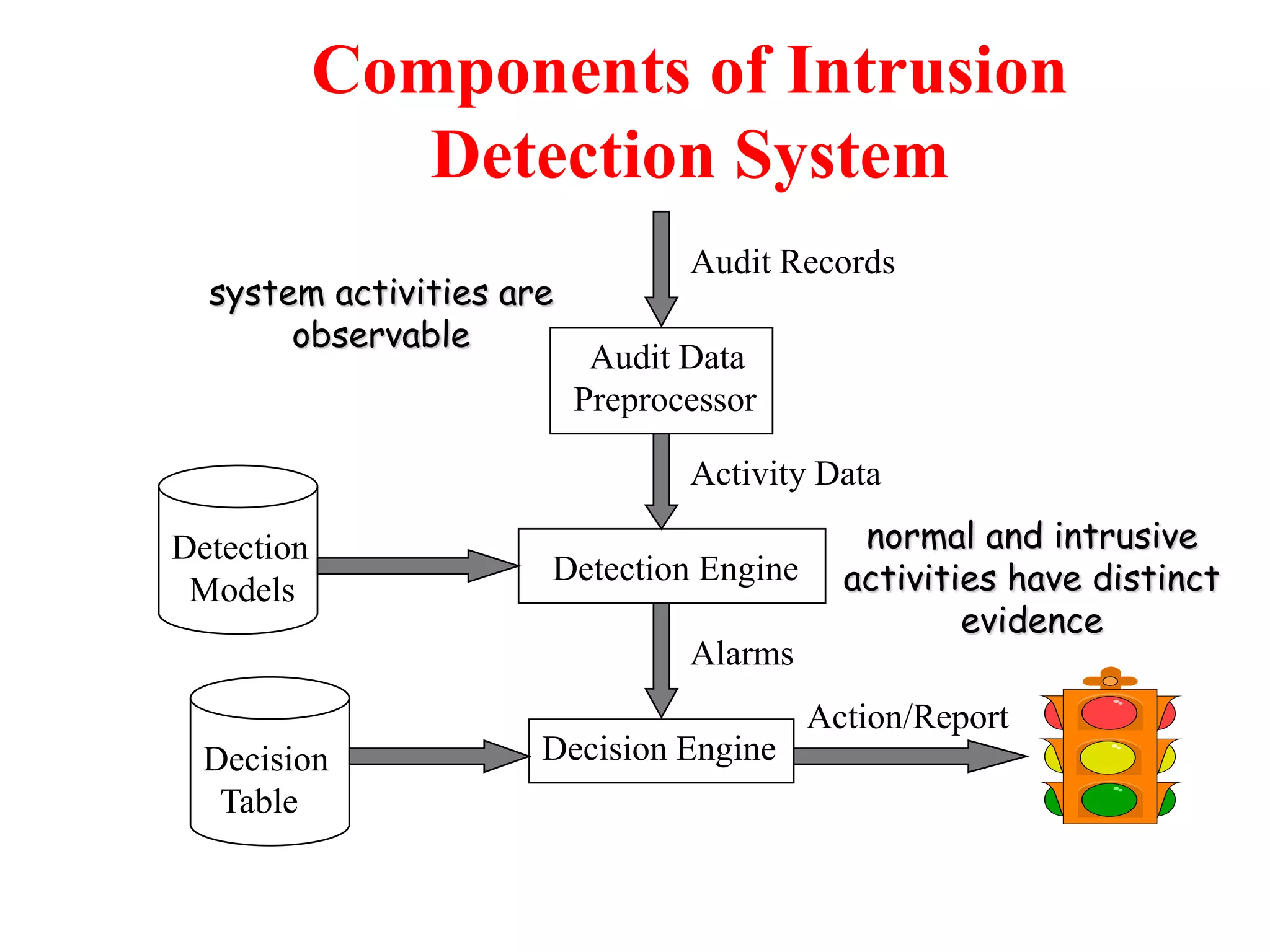
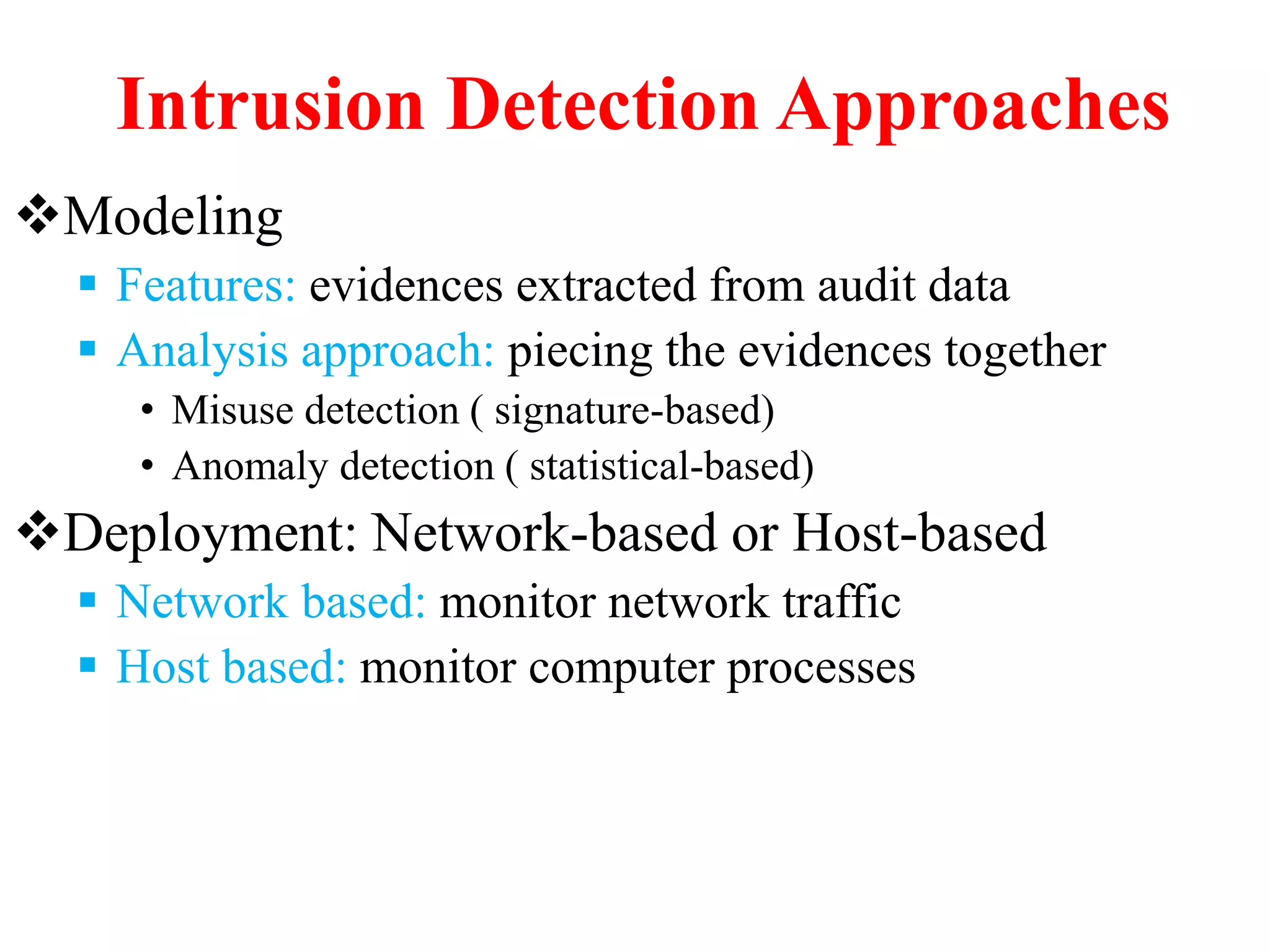
The document discusses intrusion detection systems (IDS) and their importance in securing information transmission amidst increasing risks of cyber threats. It elaborates on different detection methods, such as misuse-based and anomaly-based detection, as well as the architecture and functionality of IDS, including their benefits and limitations. Additionally, it introduces a hybrid IDS model that combines both detection approaches to enhance security measures.
![Misuse Detection
Intrusion
Patterns:
Sequences of
system calls,
patterns of
network traffic,
etc.
activities
pattern
matching
intrusion
Can’t detect new attacks
Example: if (traffic contains “x90+deZ^rn]{30}”) then “attack detected”
Advantage: Mostly accurate. But problems?](https://image.slidesharecdn.com/understandingintrusiondetectionpreventionsystems1-221122092333-43fff43f/75/Understanding-Intrusion-Detection-Prevention-Systems-1-pptx-11-2048.jpg)