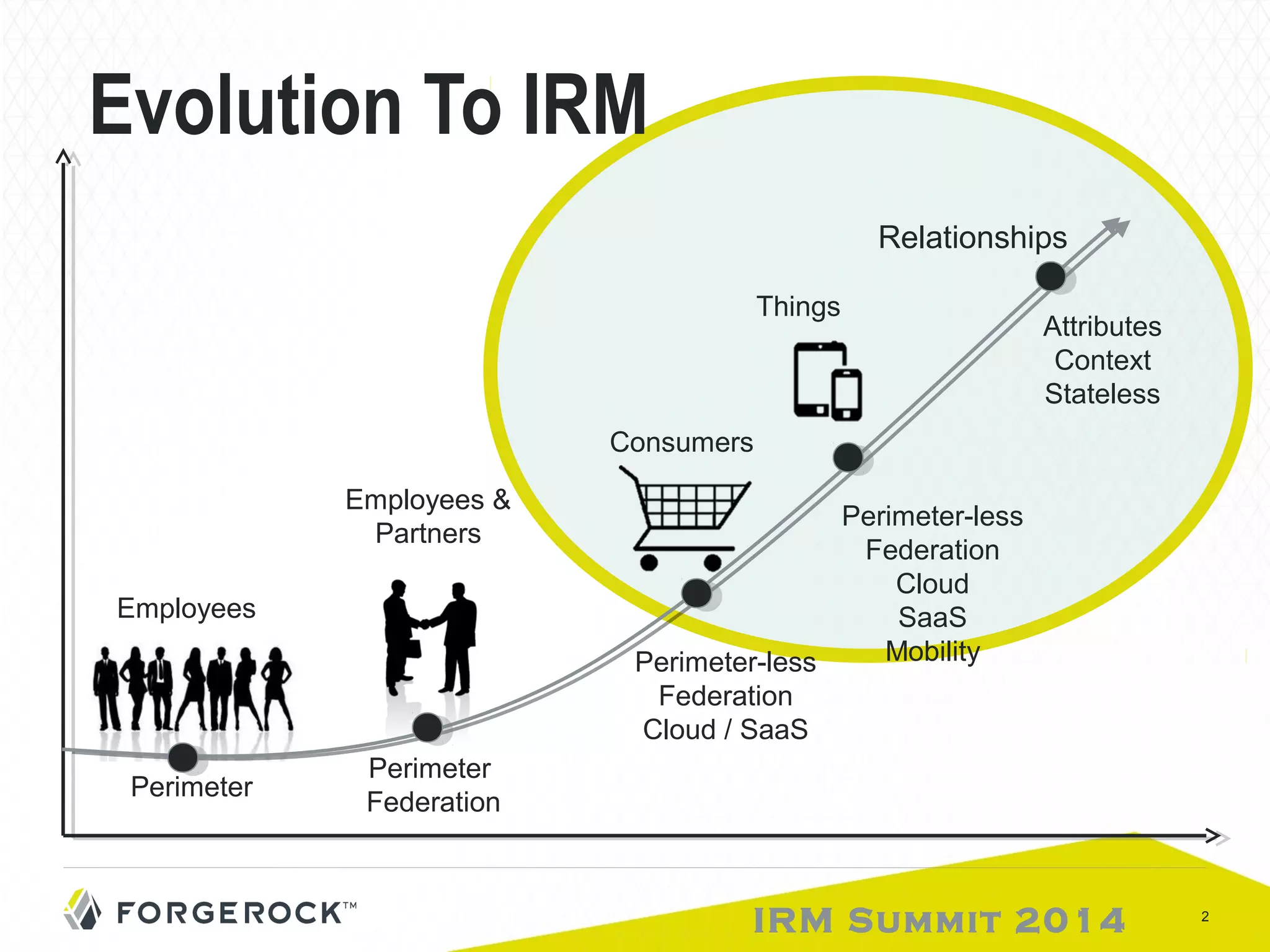
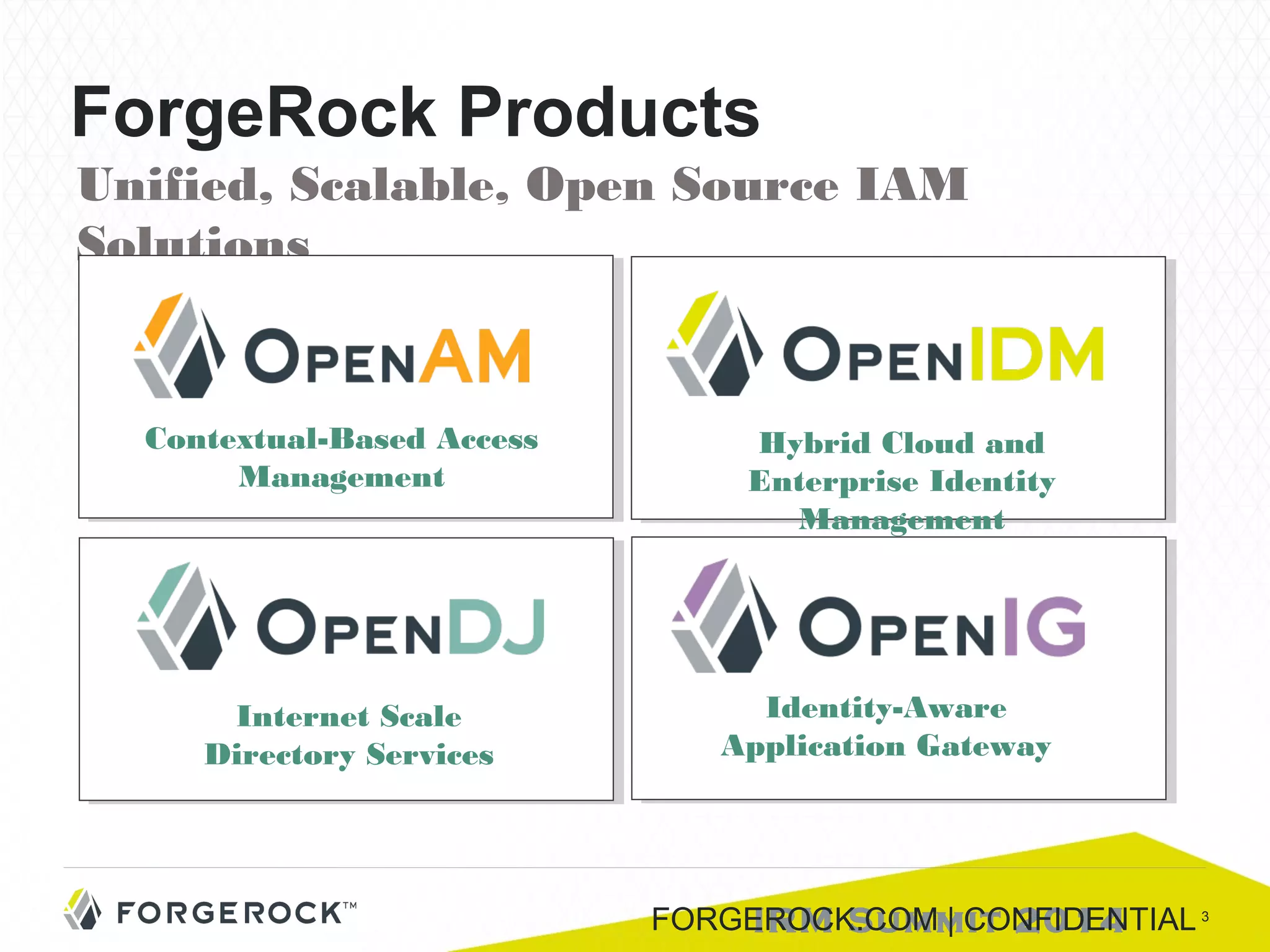
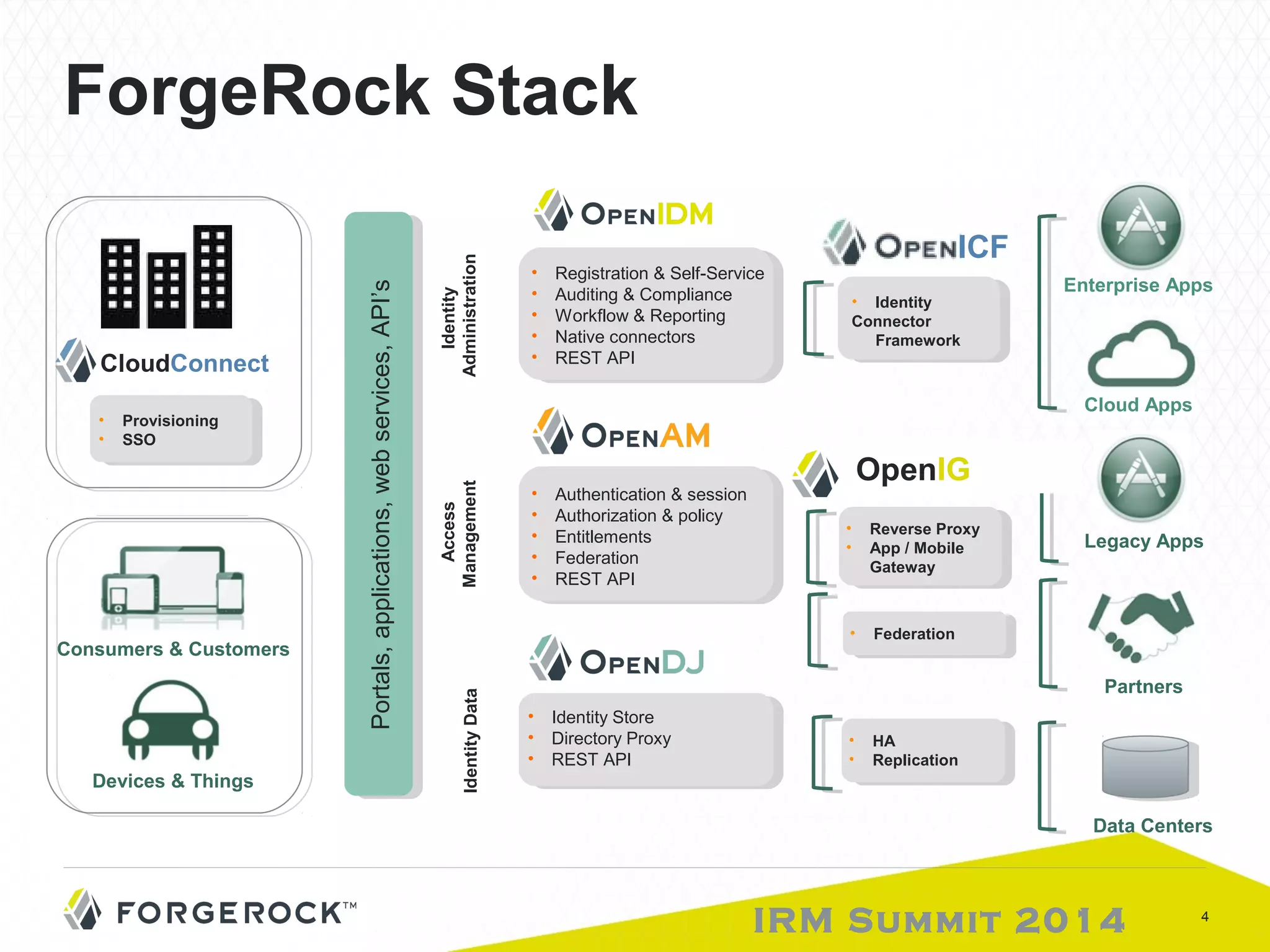
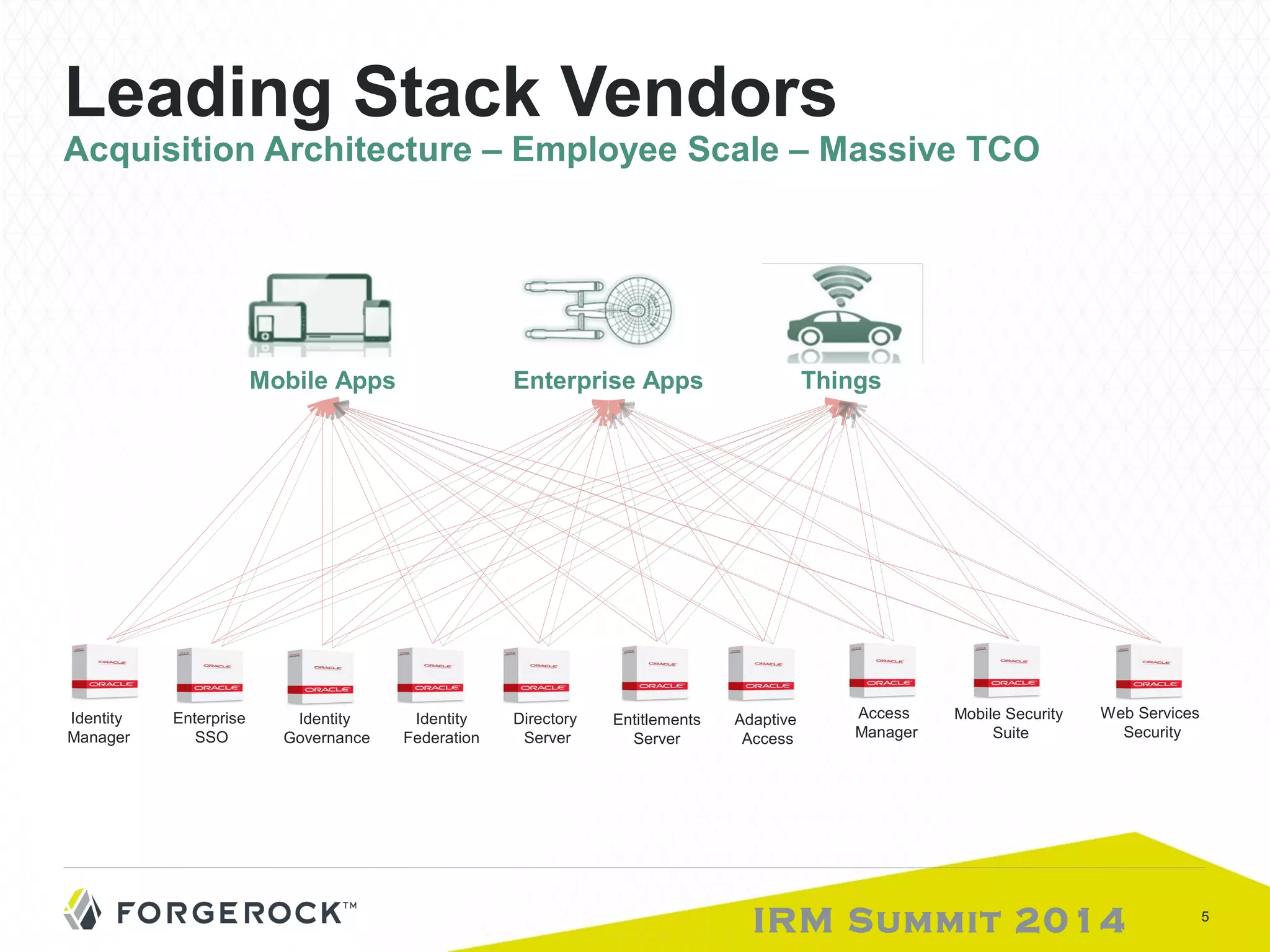
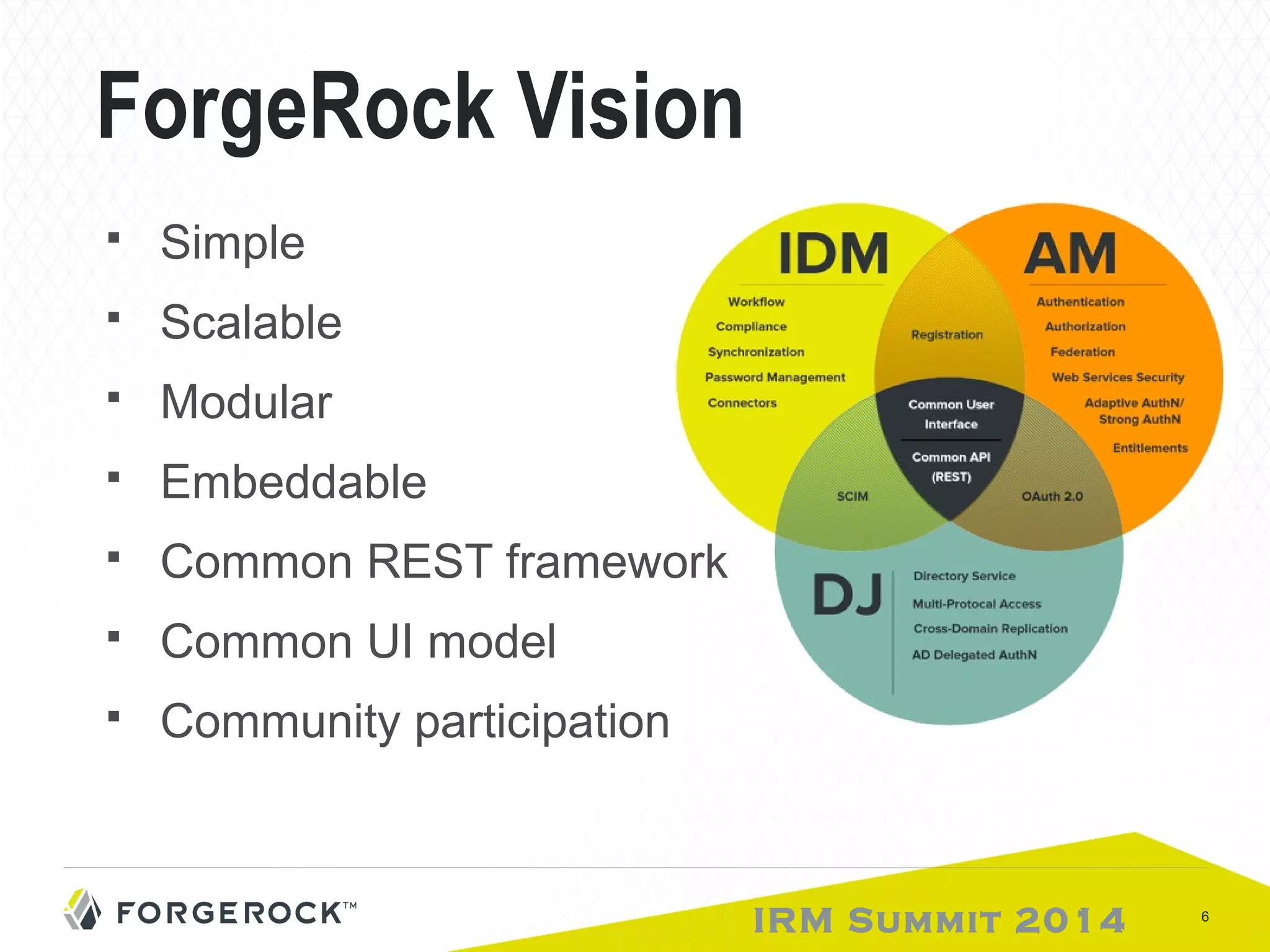
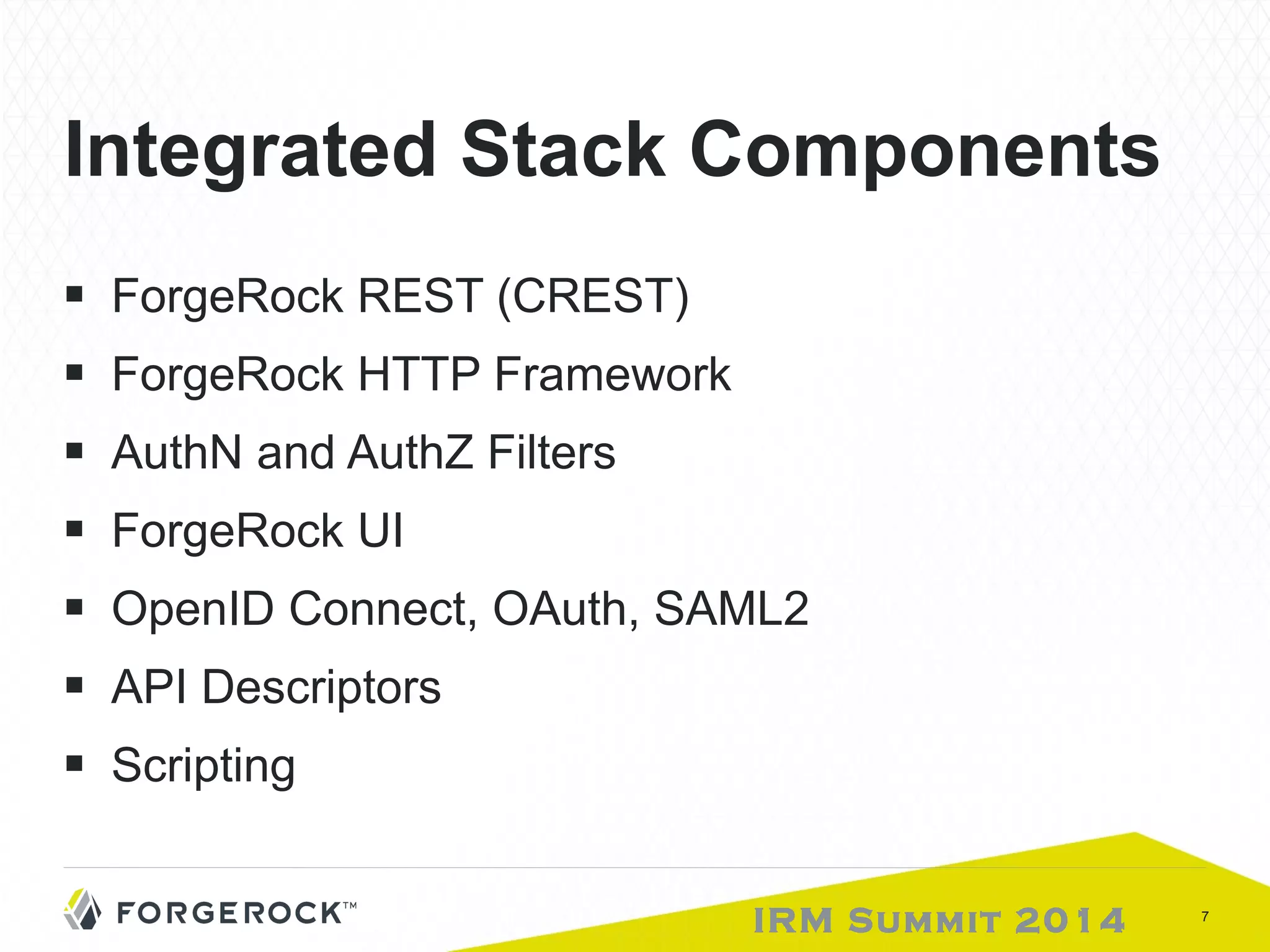
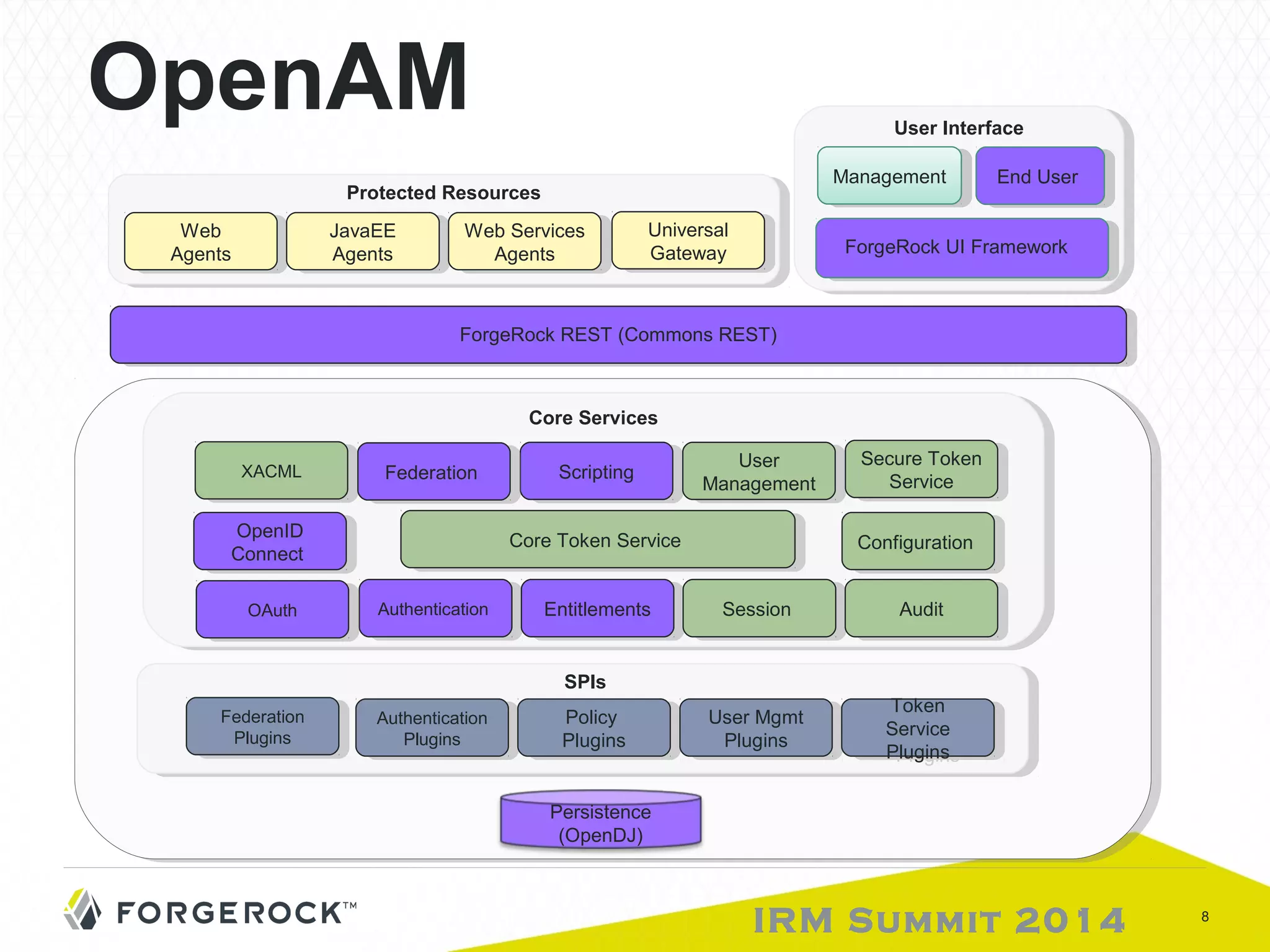
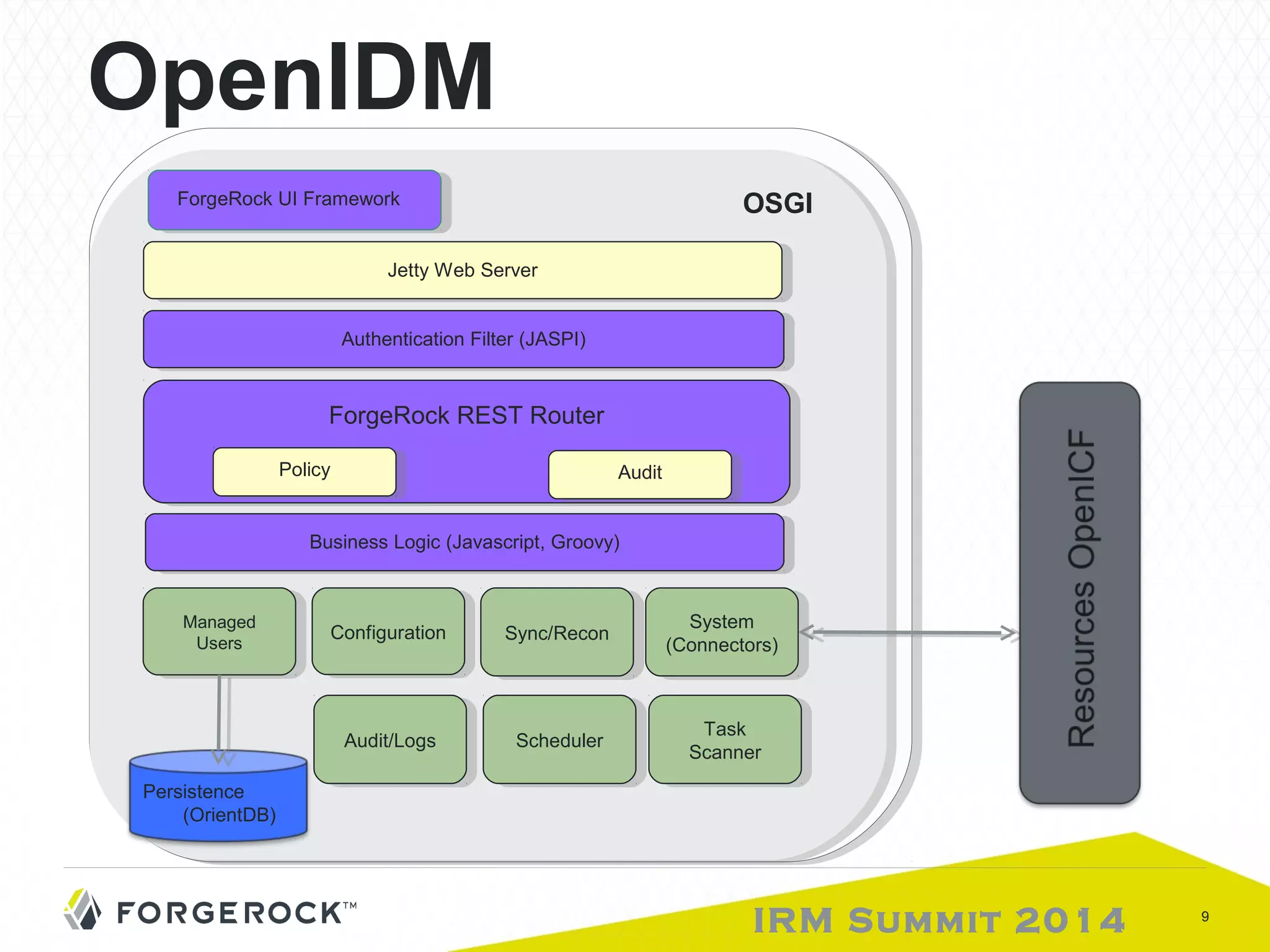
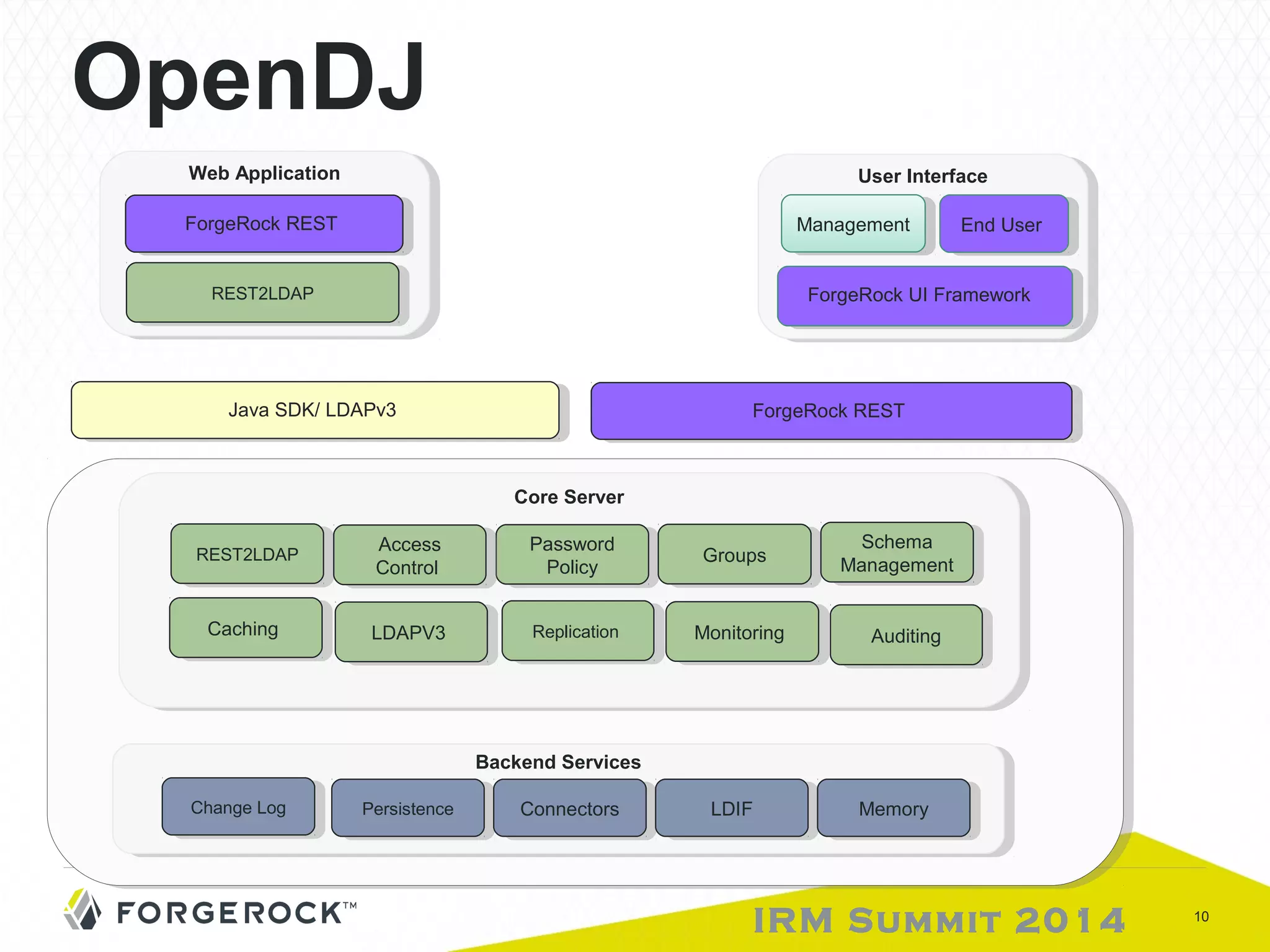
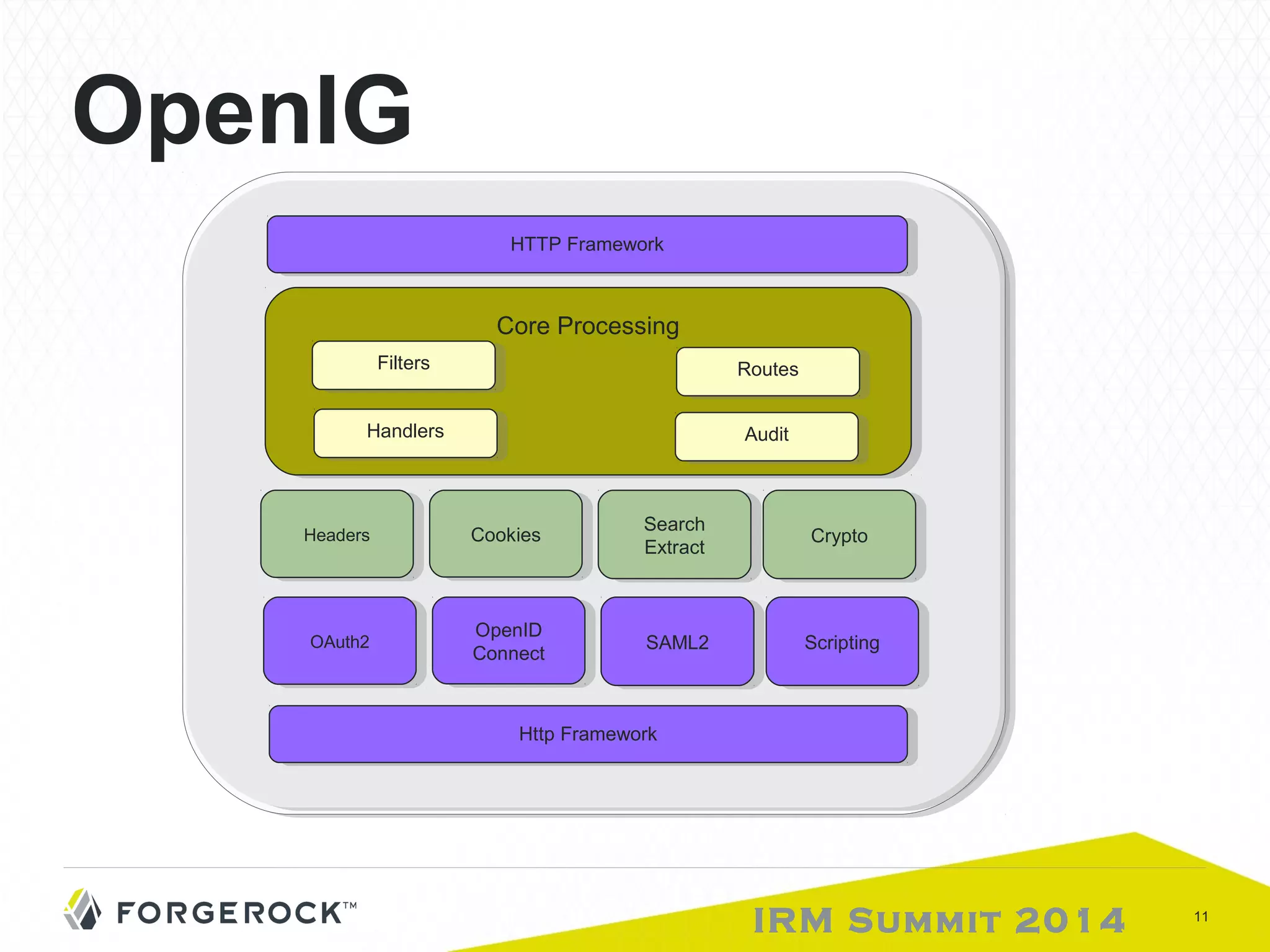
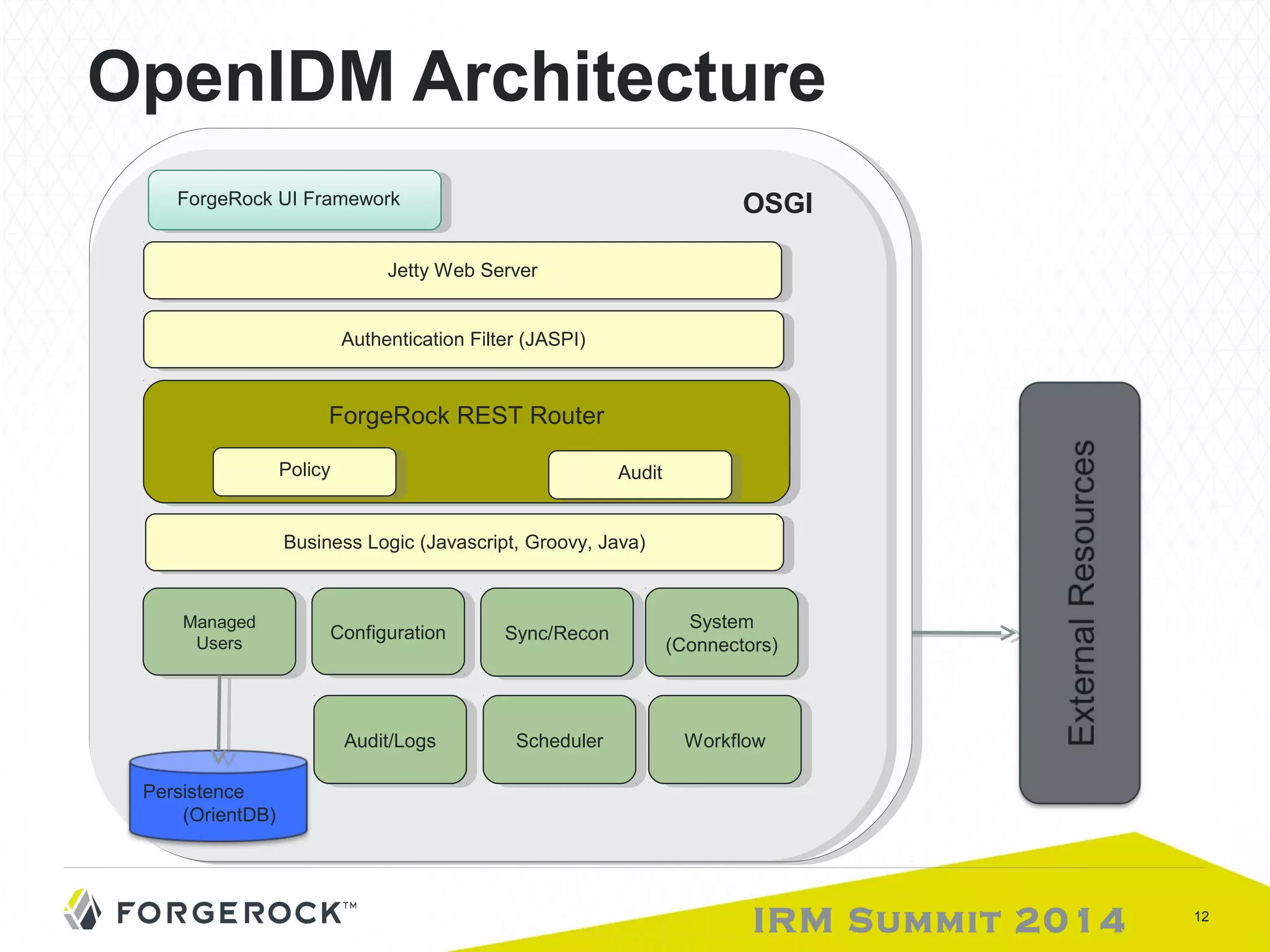
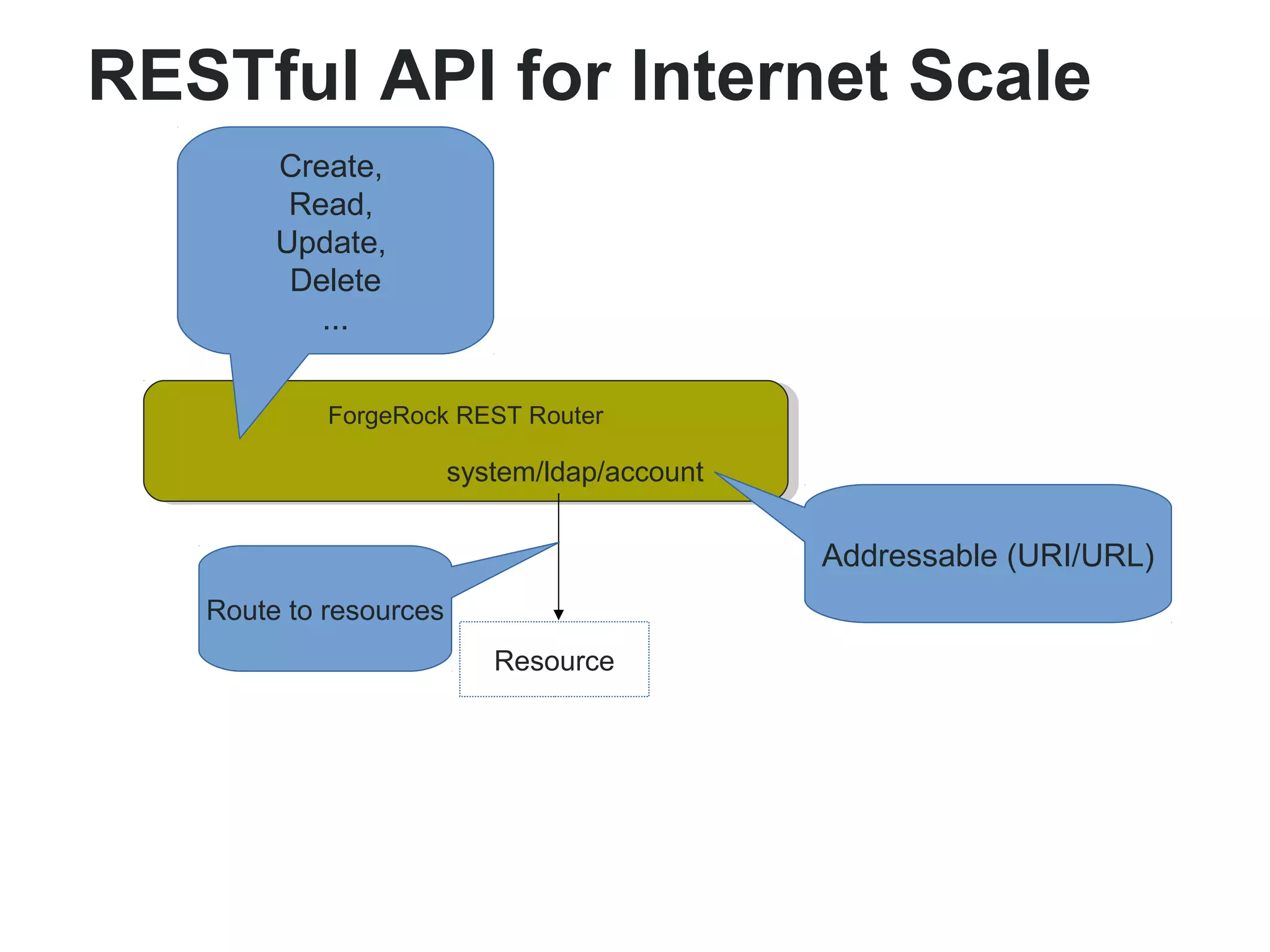
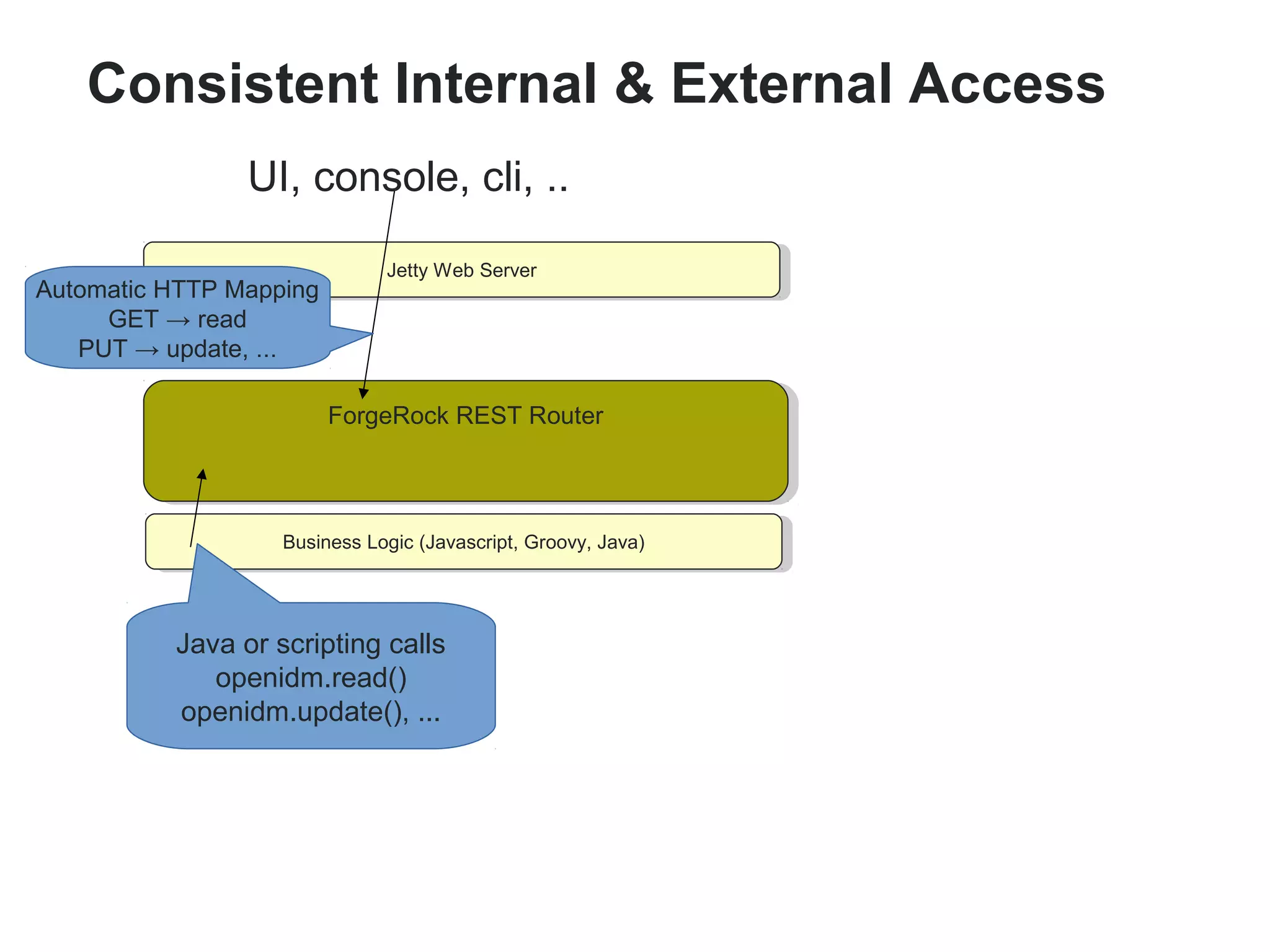
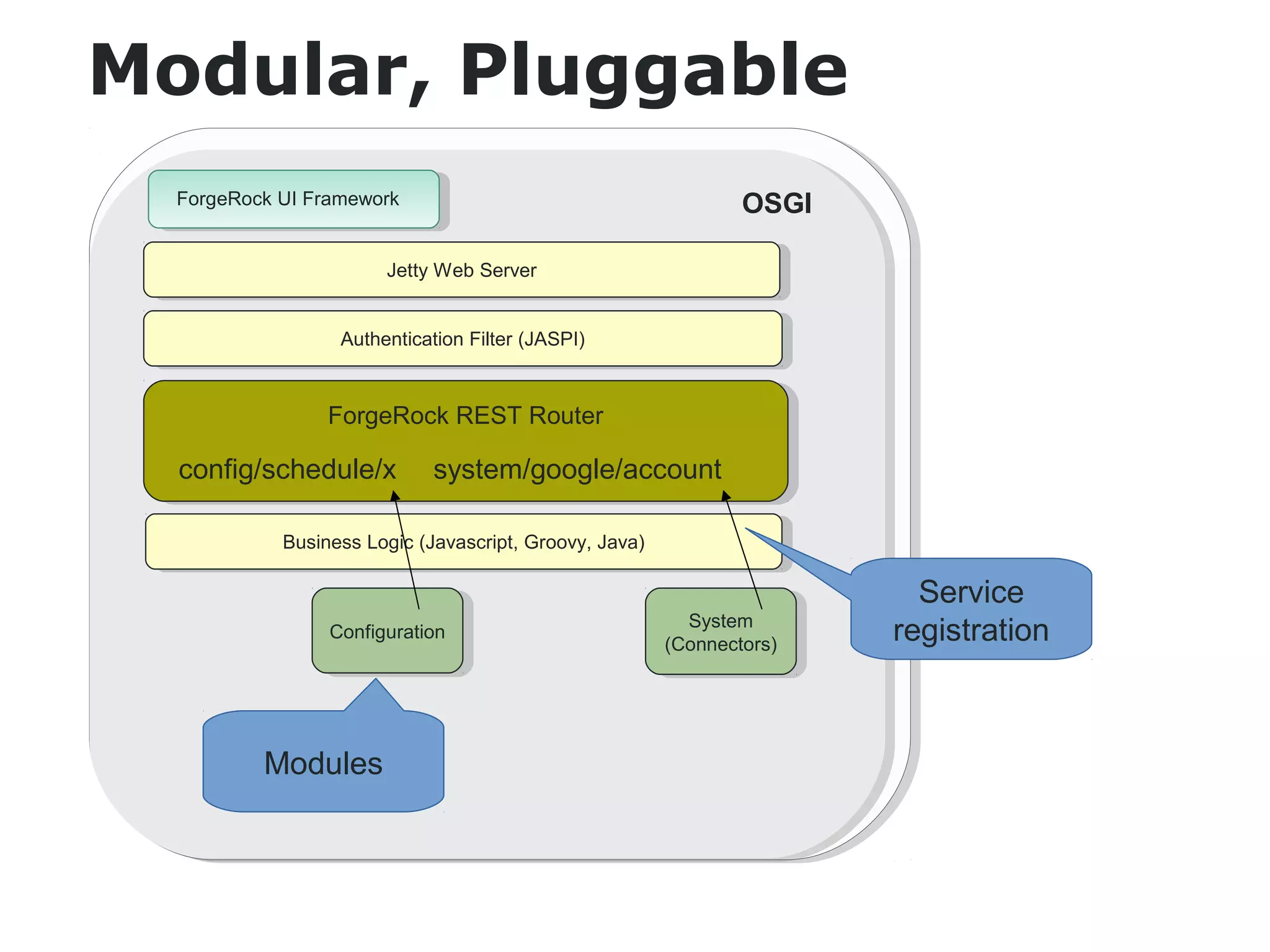
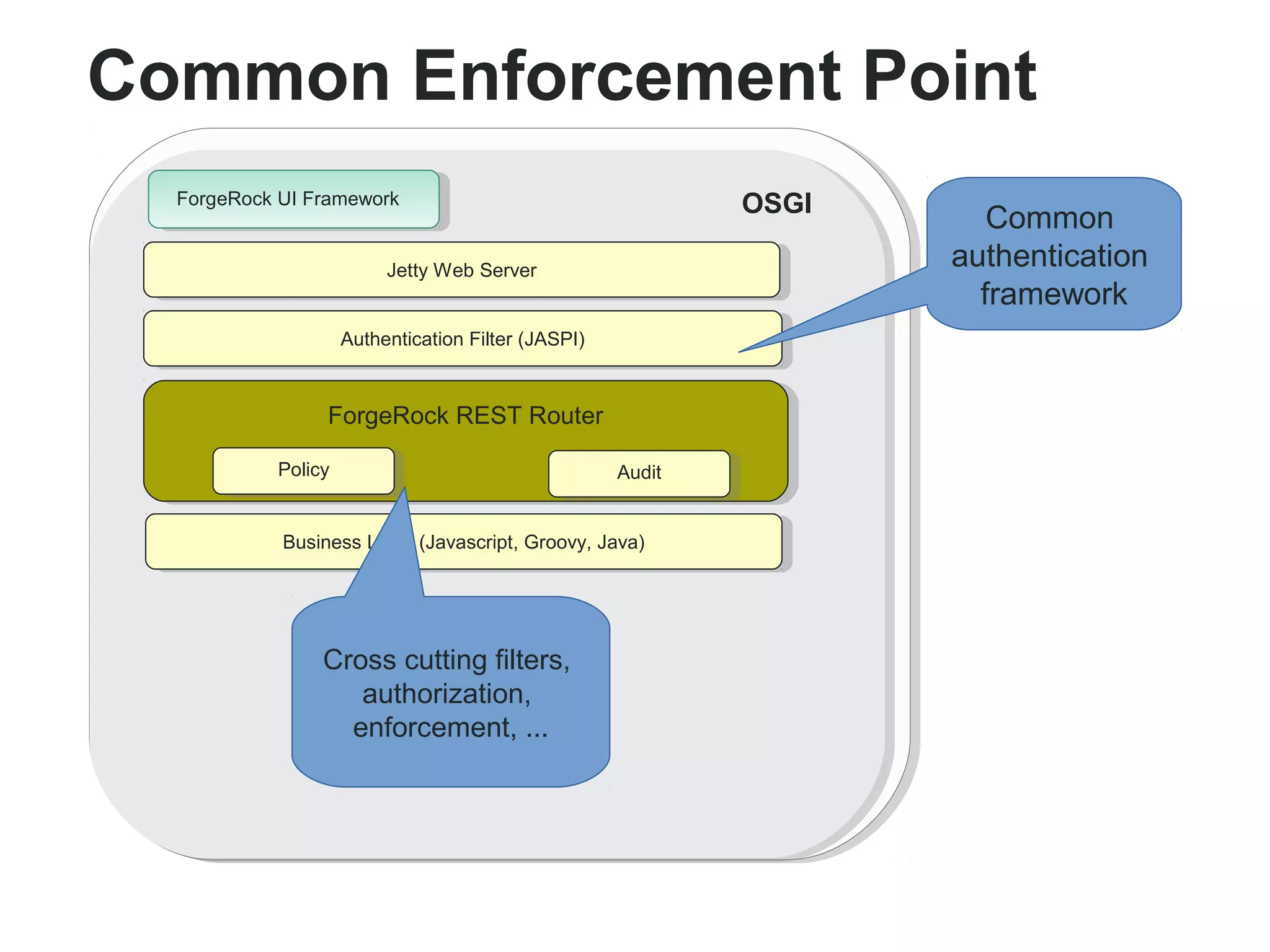
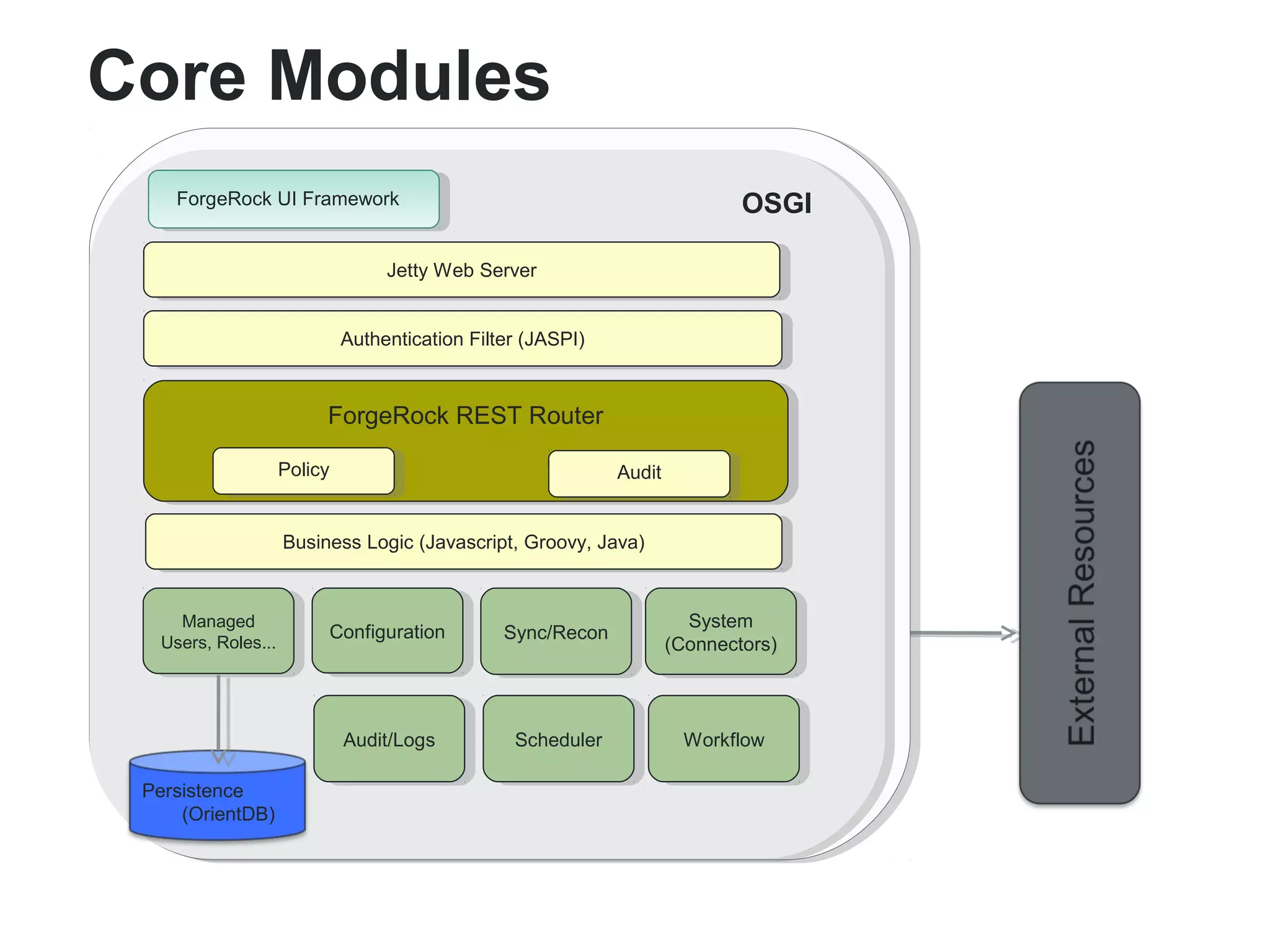
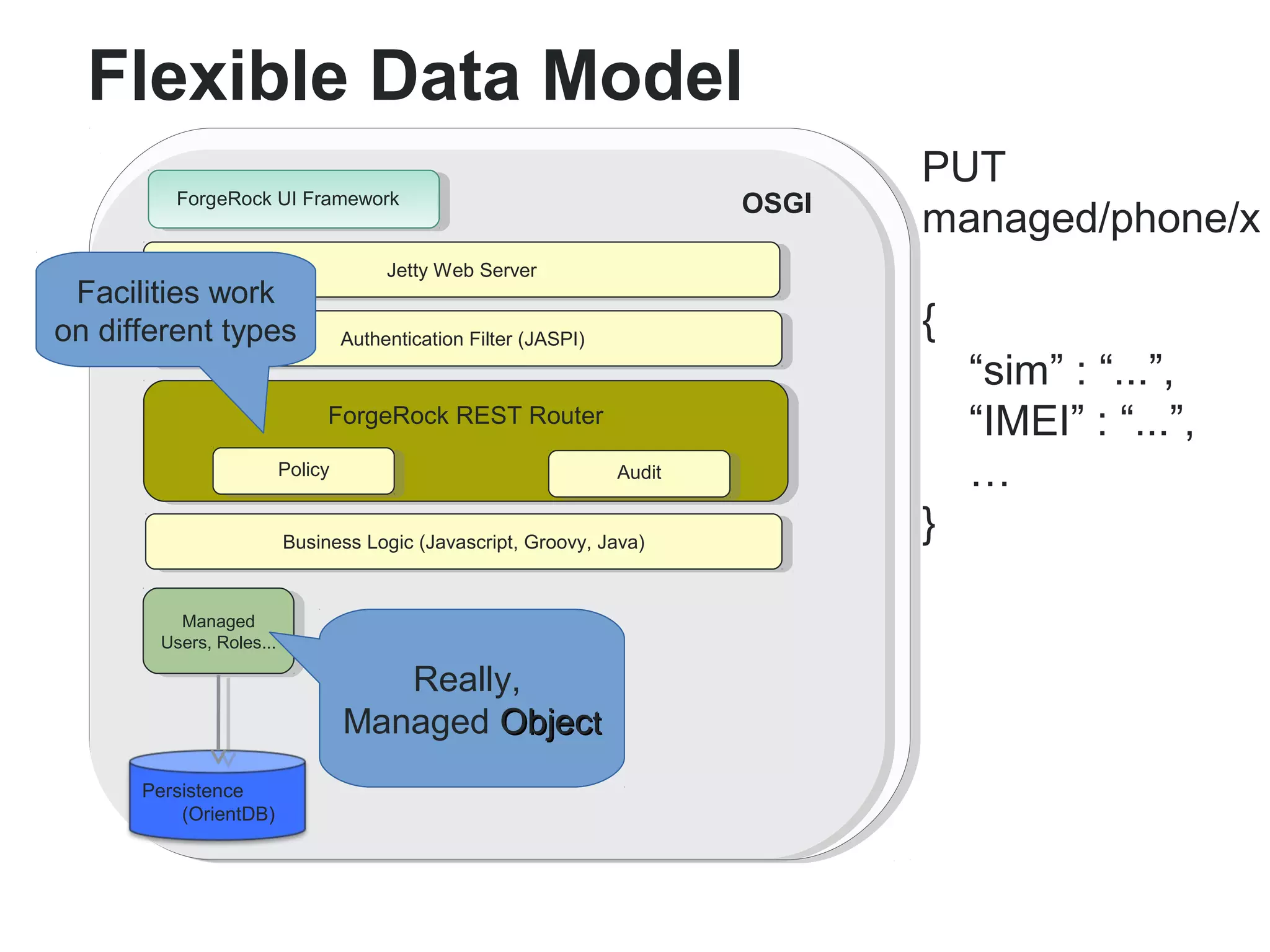
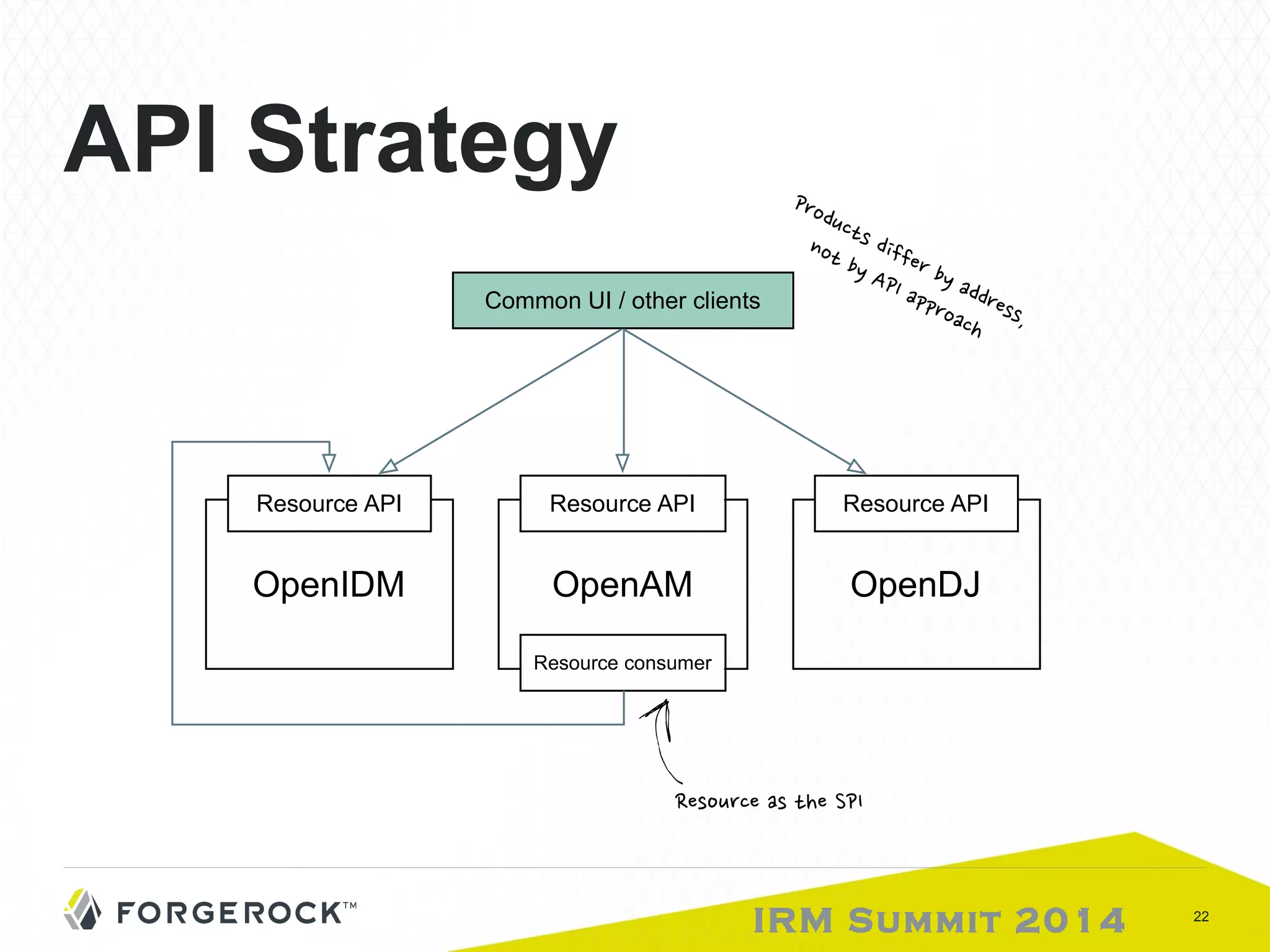
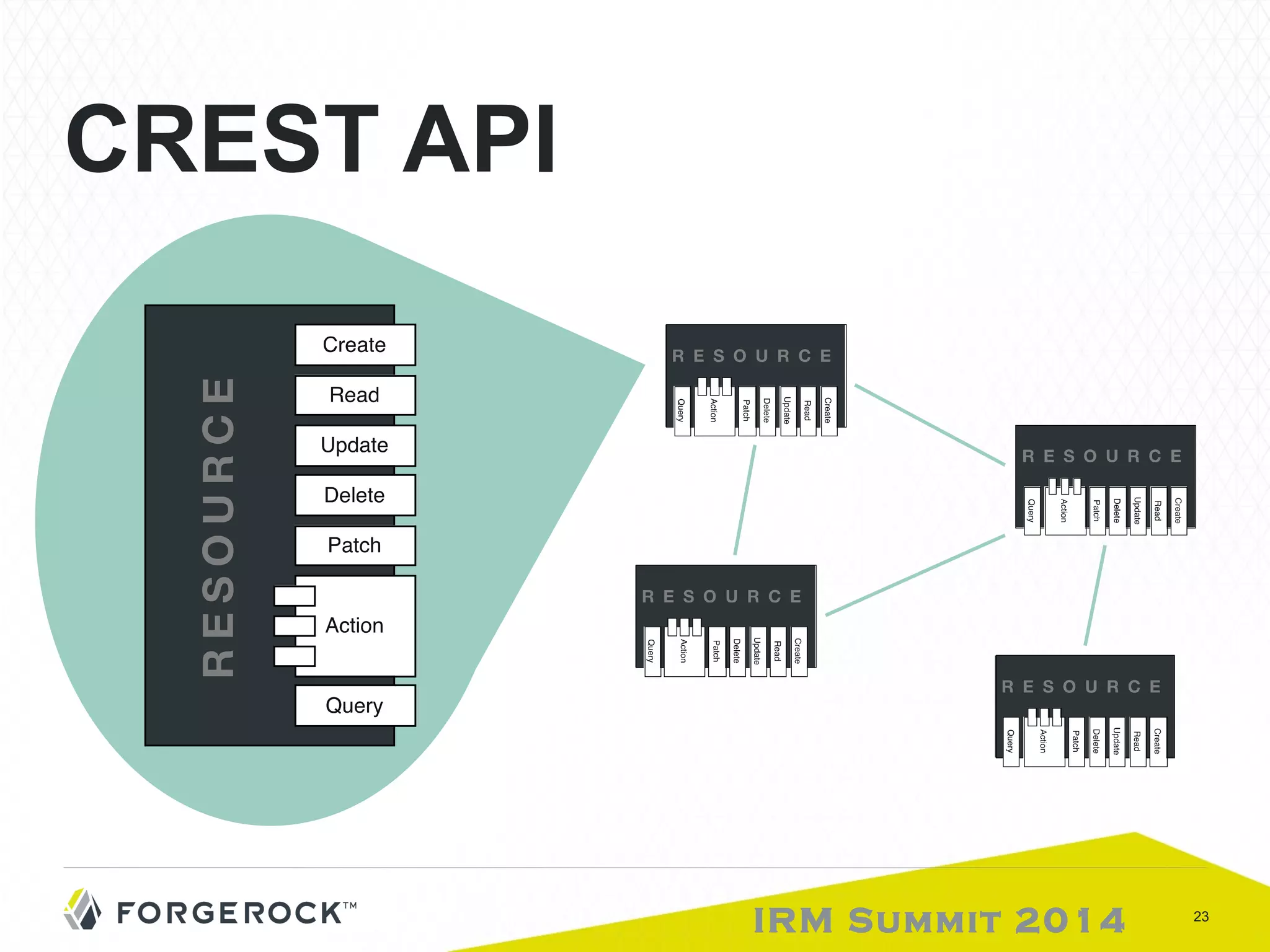
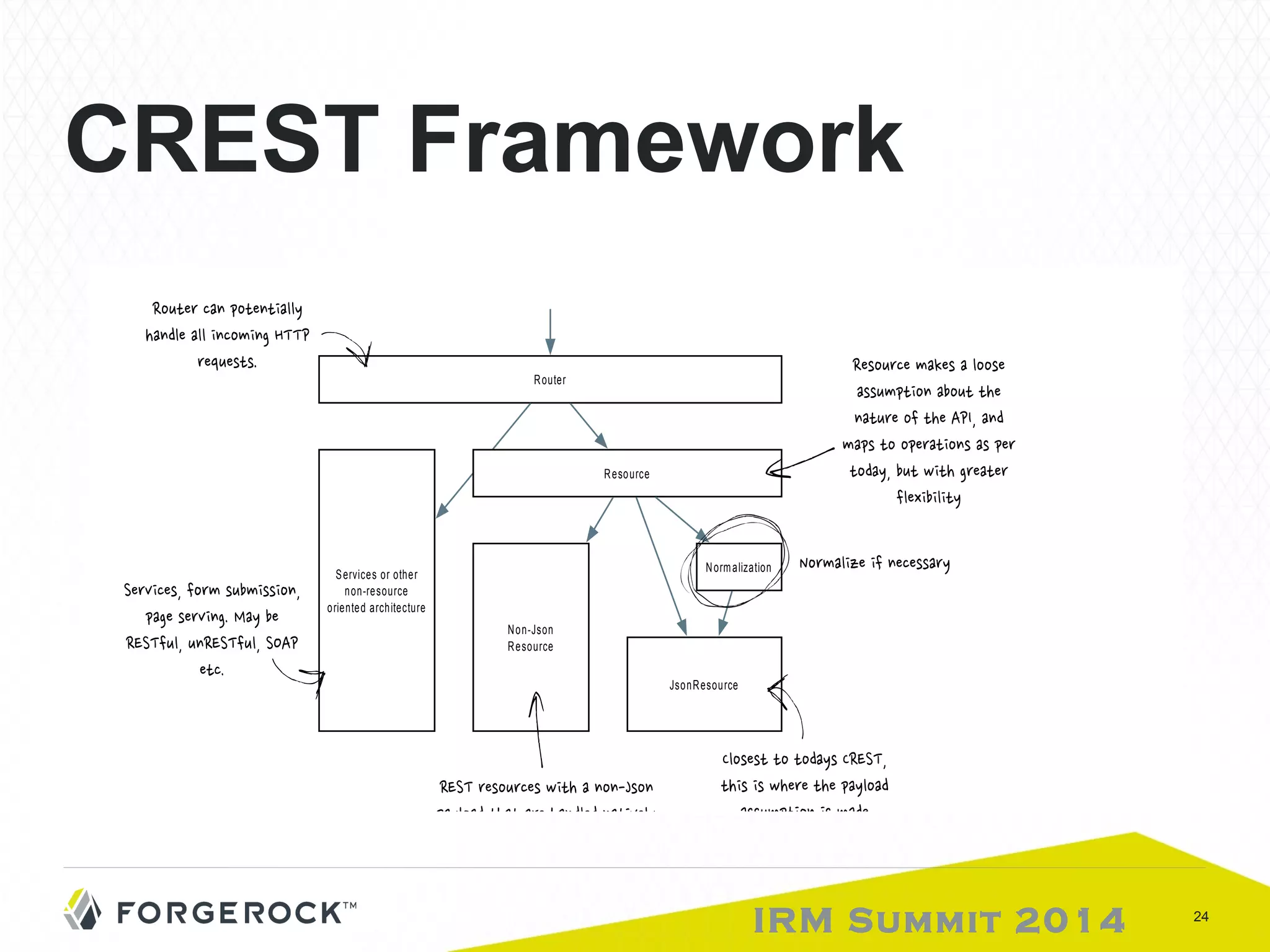
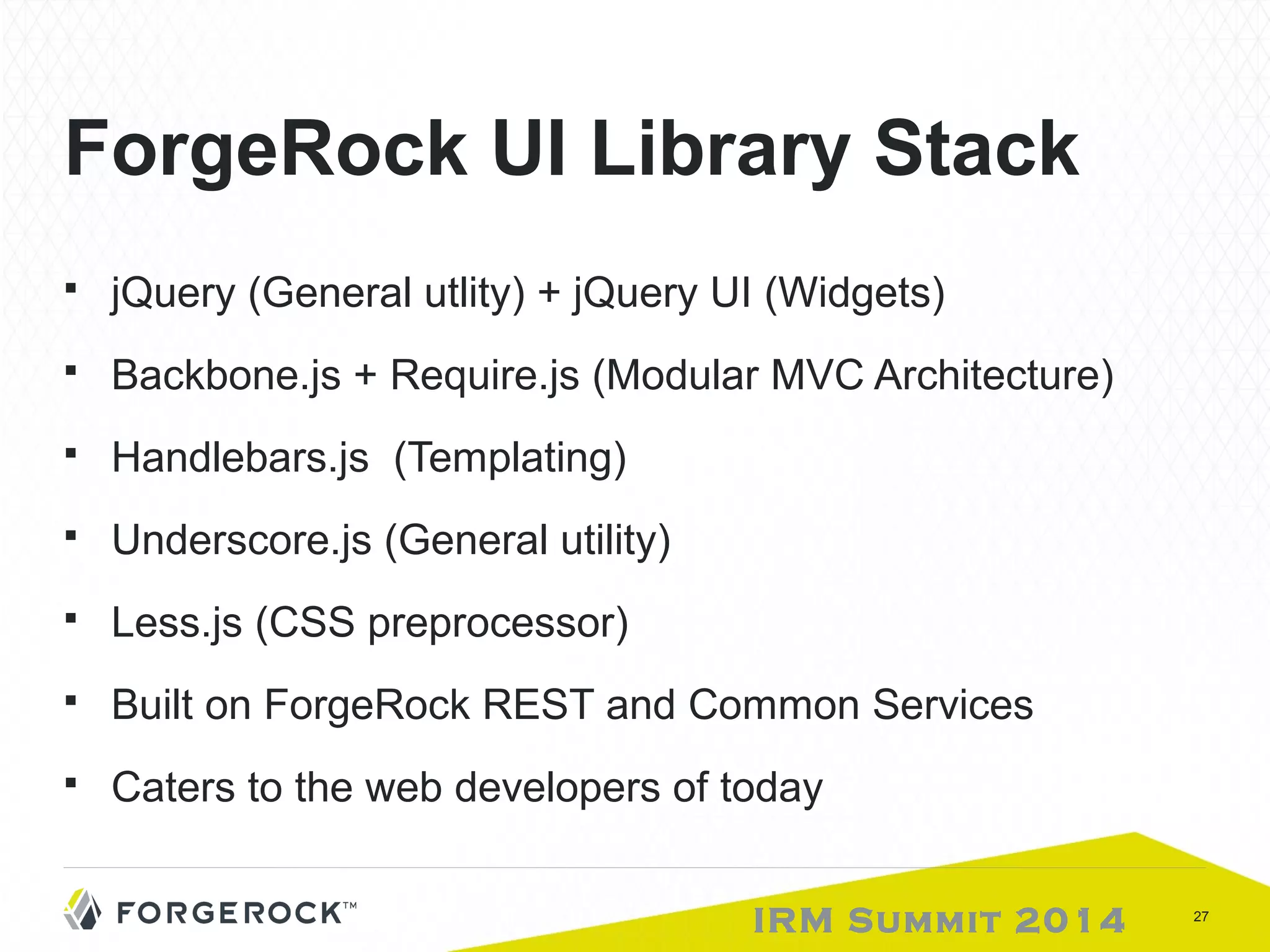
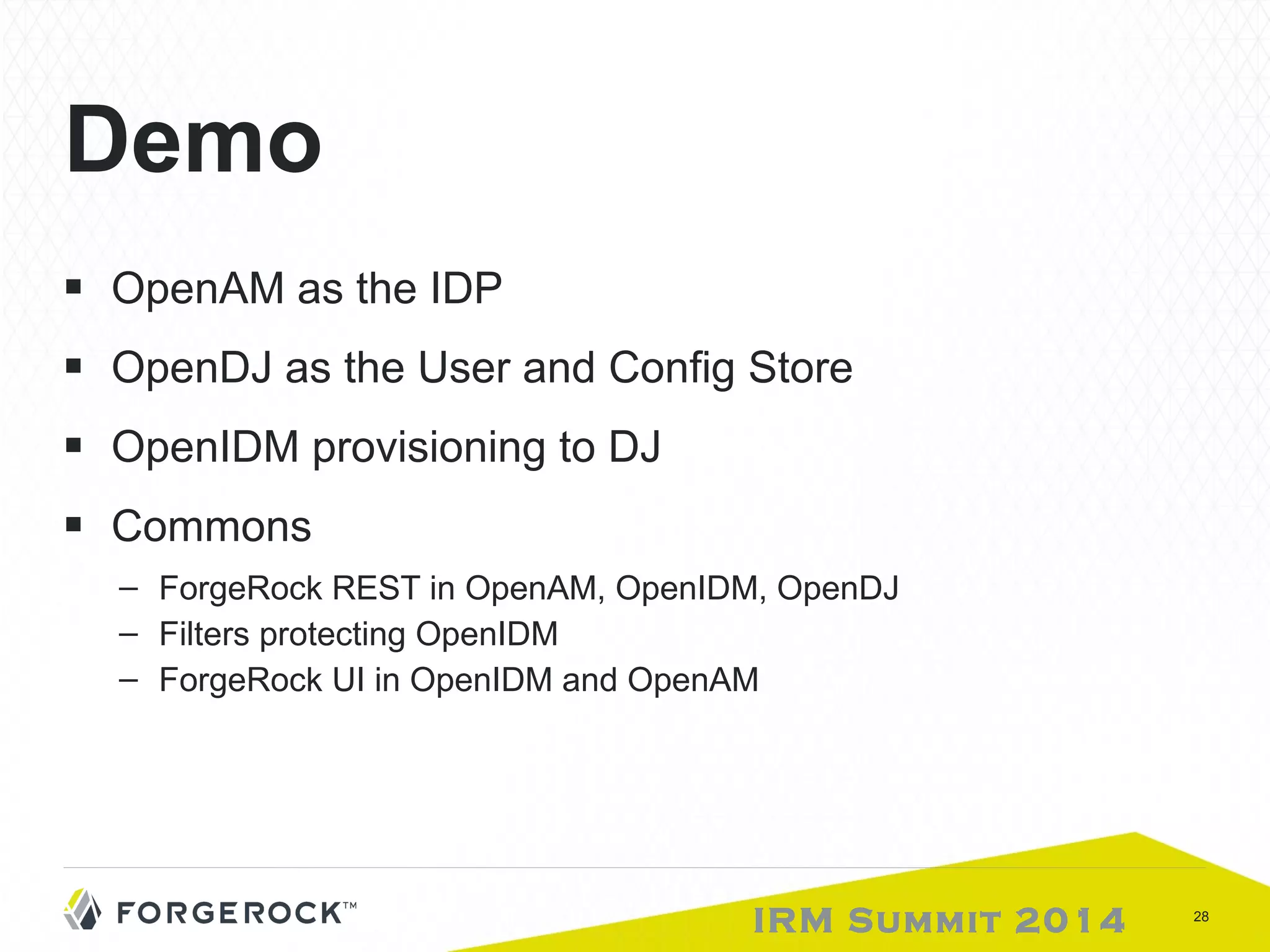
The document discusses the Forgerock Identity Stack showcased at the IRM Summit 2014, emphasizing its components for contextual-based access management, identity federation, and integration with cloud and enterprise applications. It outlines key features such as a unified IAM solution, user management services, RESTful APIs, and a modular architecture designed for scalability and ease of use. Additionally, it highlights the importance of community participation and flexible data management across various user and application environments.