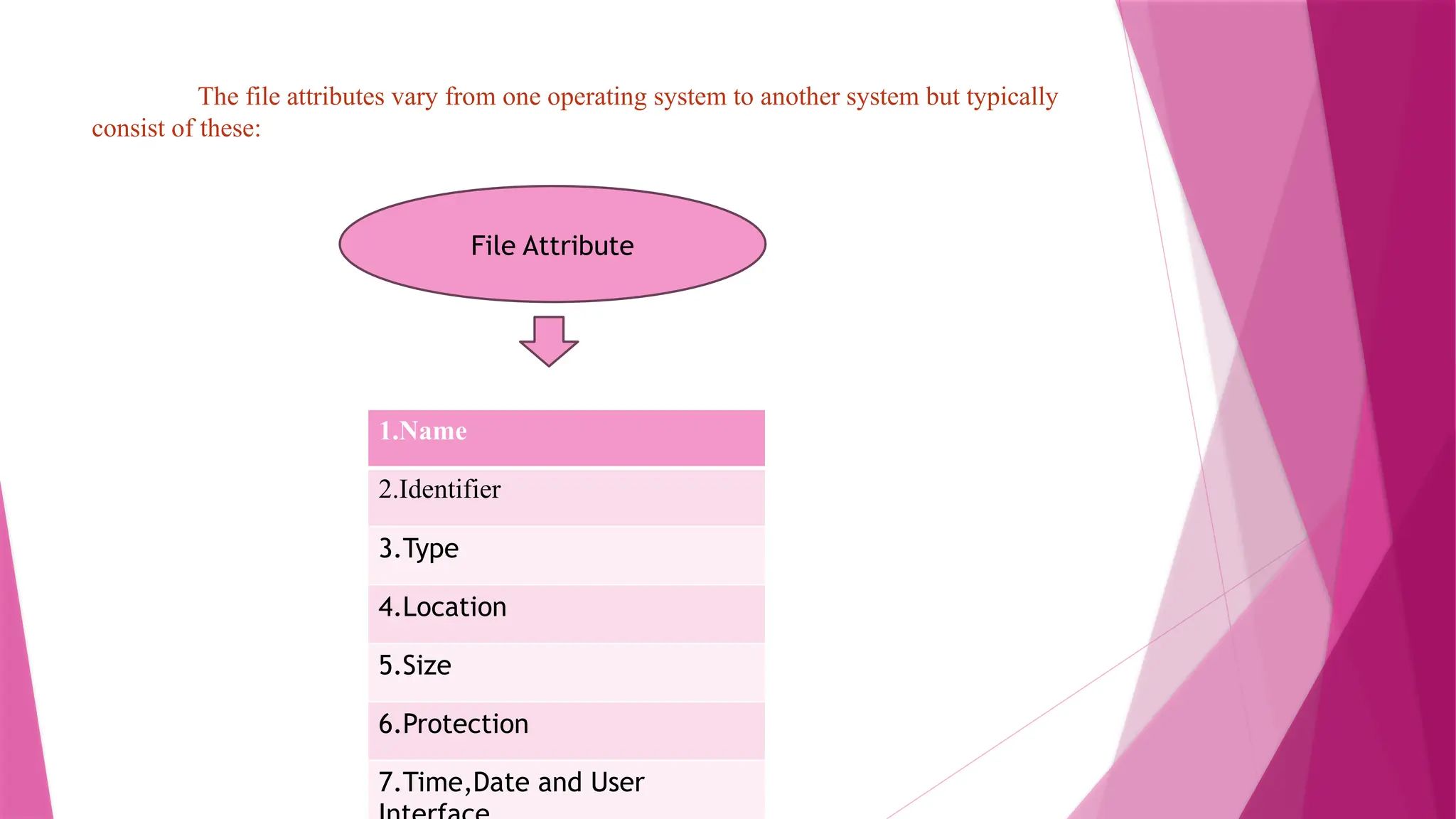
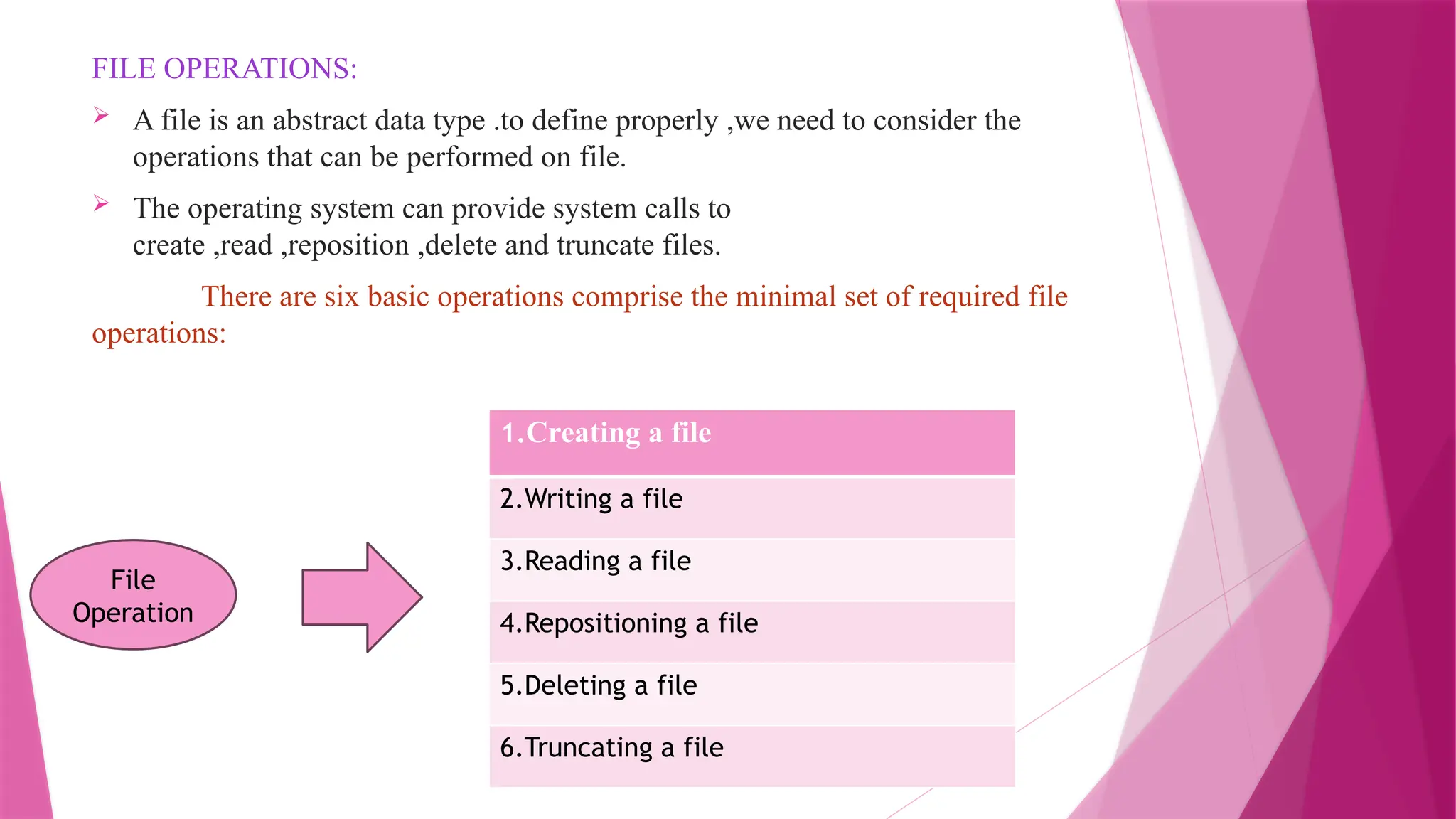
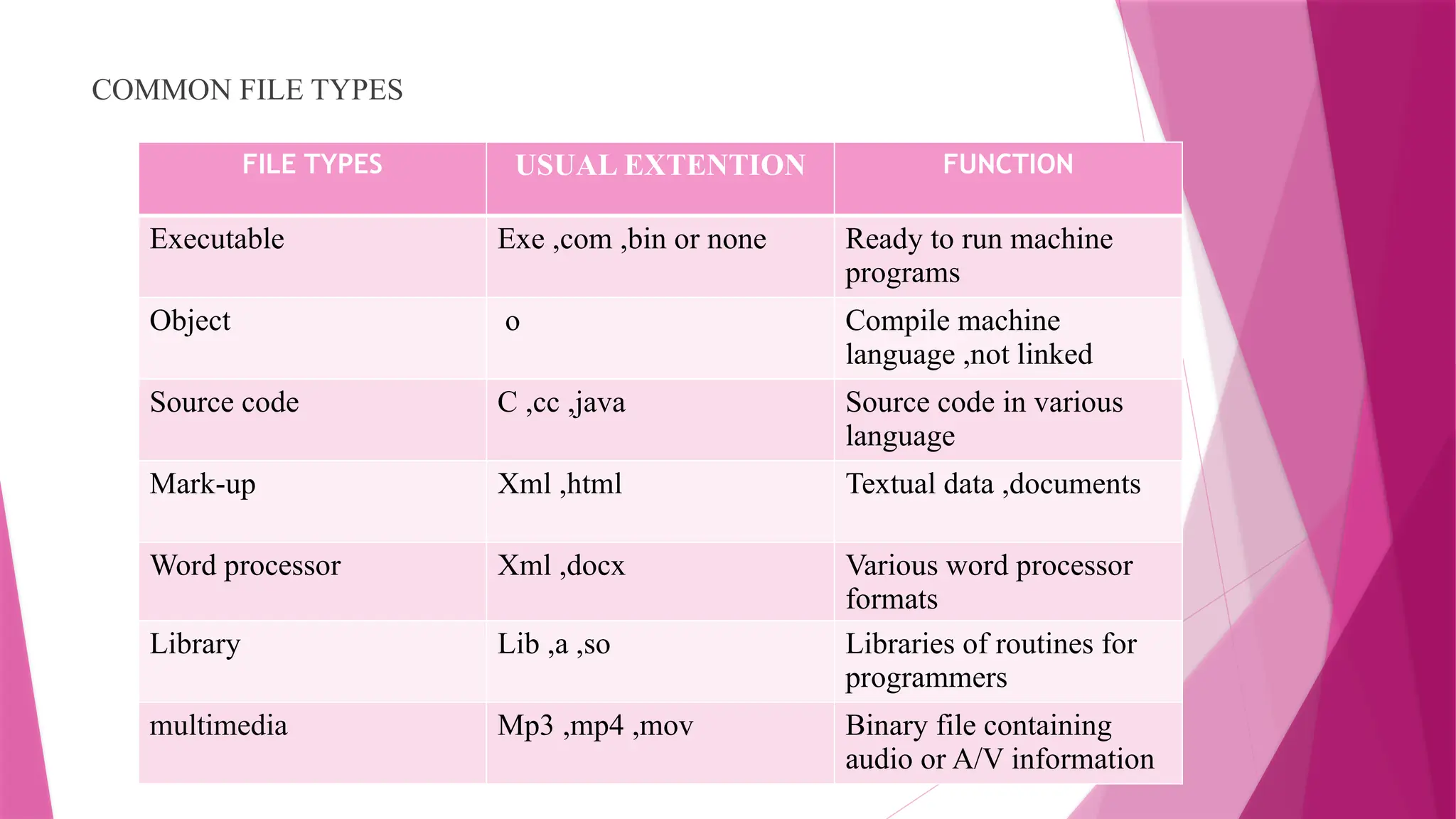
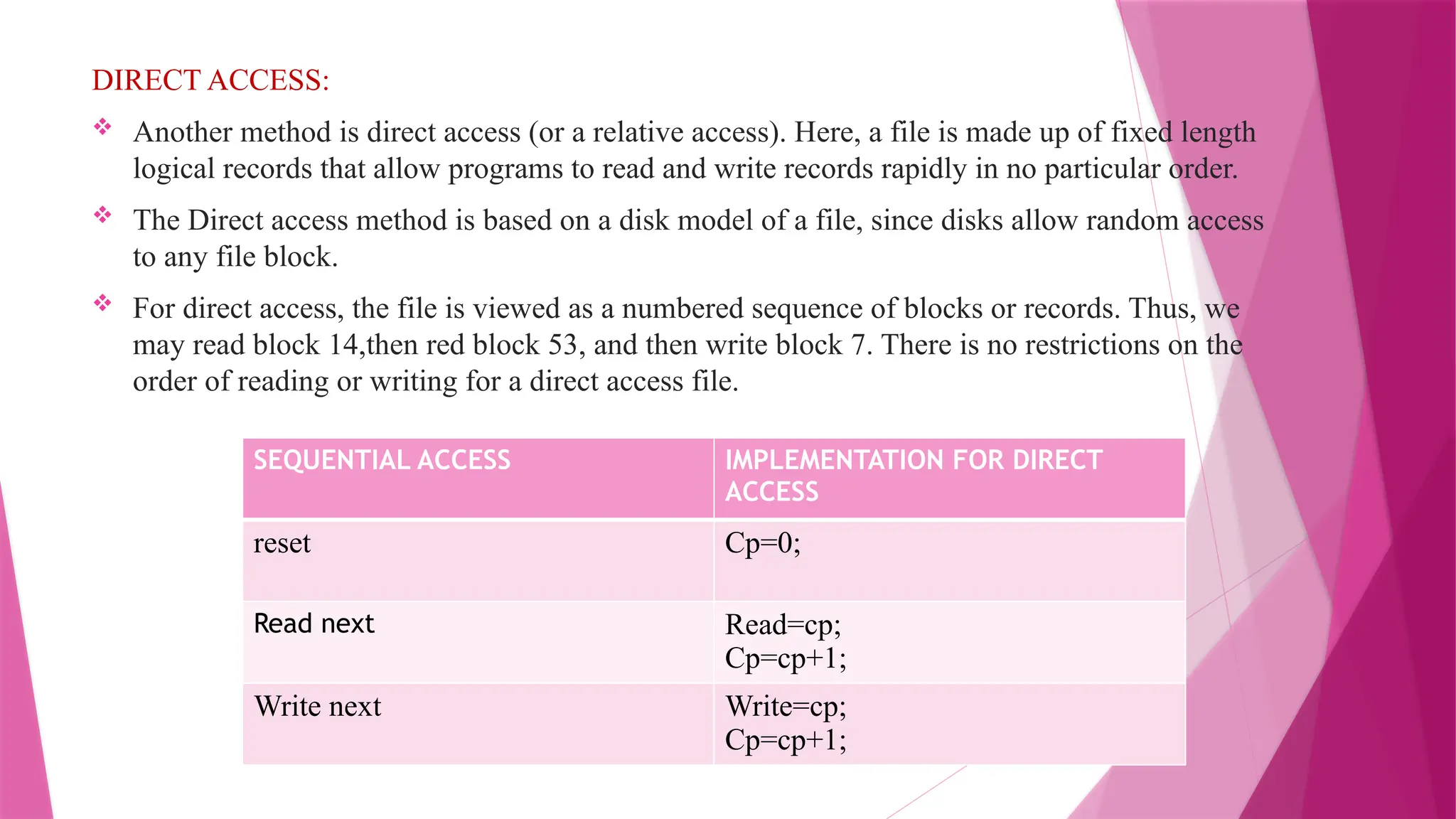
The document discusses the concept of files in operating systems, including their attributes such as name, identifier, type, location, size, protection, and timestamps. It explains various file operations like creating, writing, reading, deleting, and truncating files, as well as access methods such as sequential and direct access. Furthermore, it highlights the significance of file types, structures, and internal organization for proper file management in computer systems.