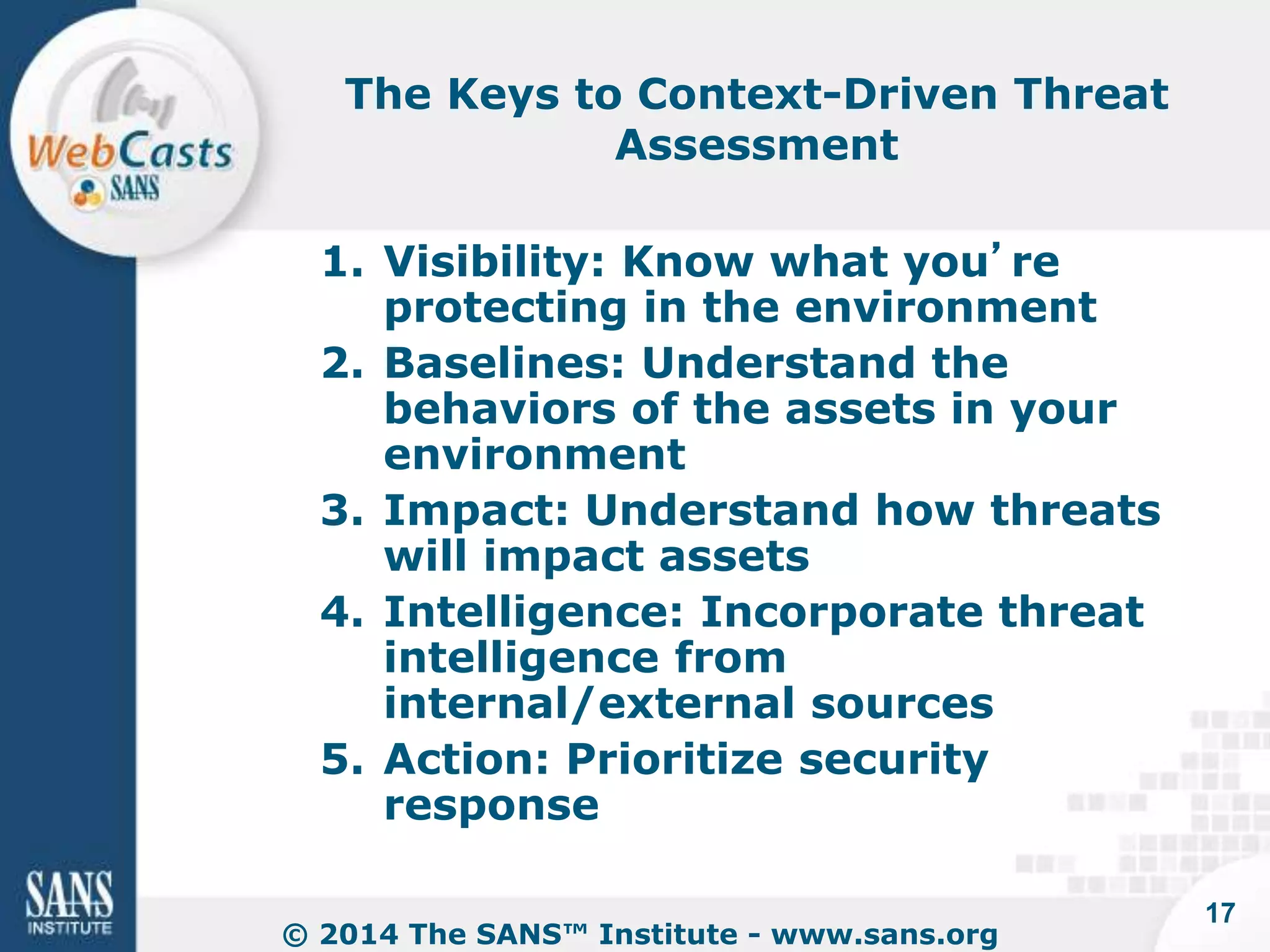
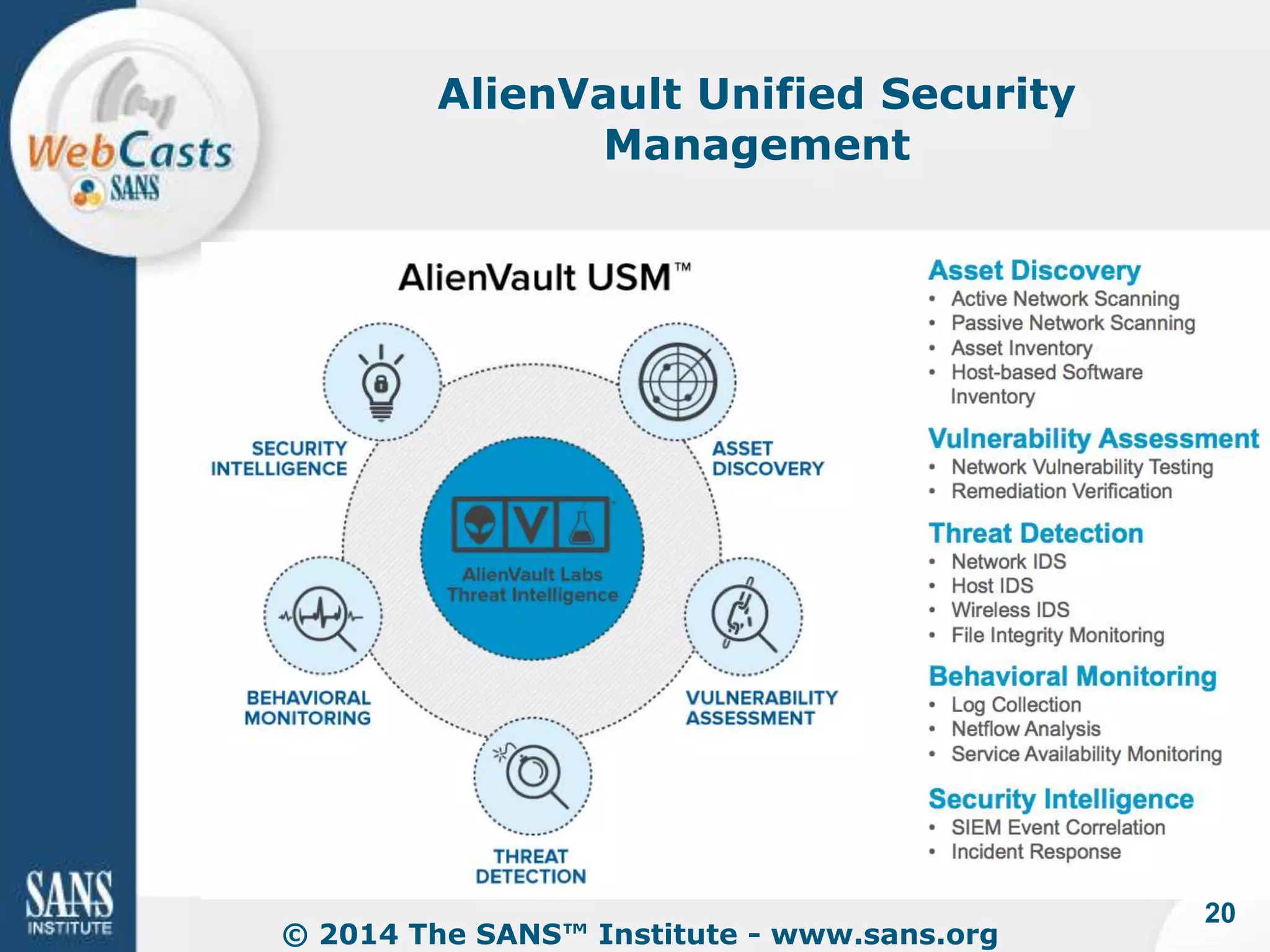
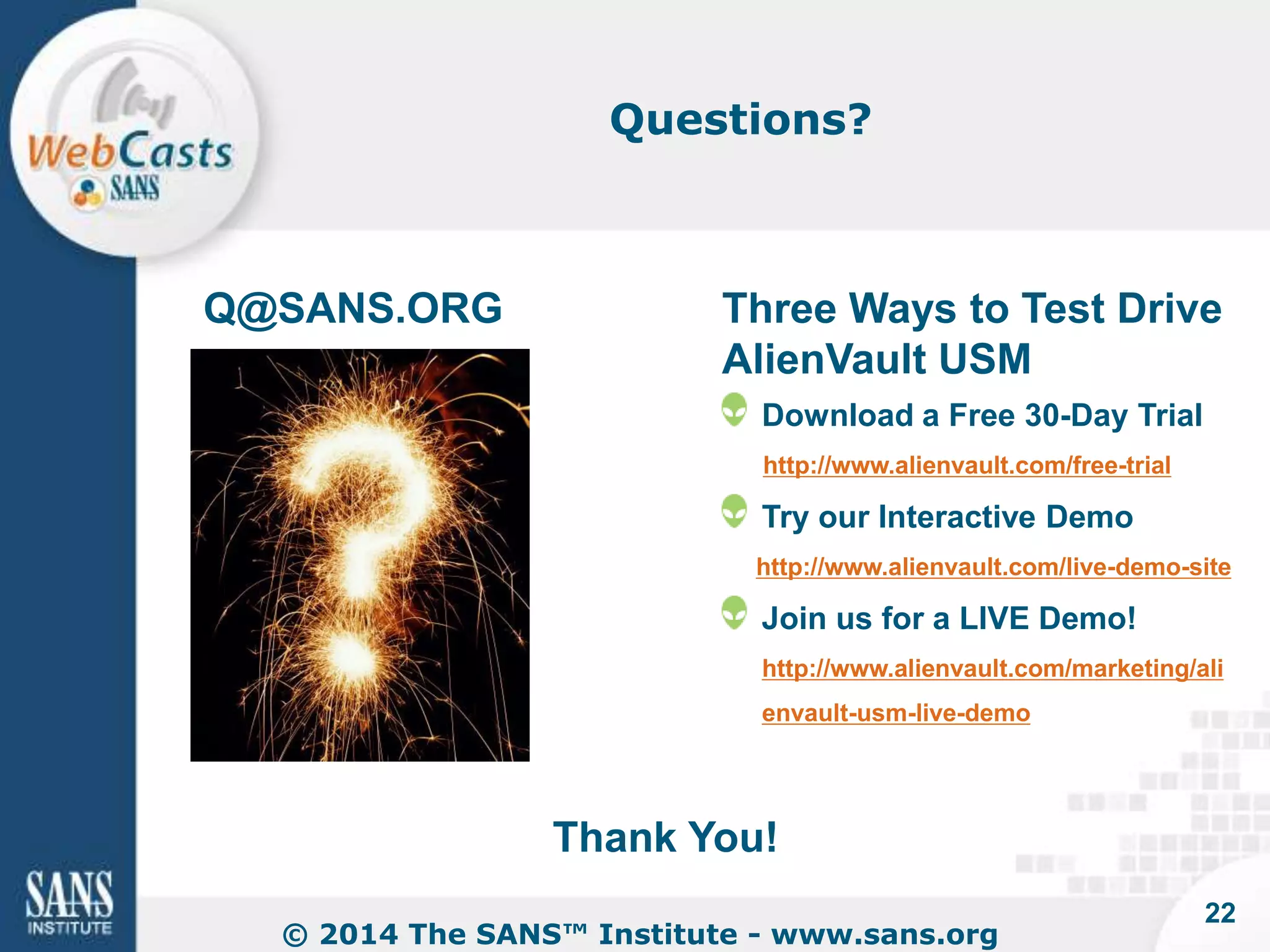
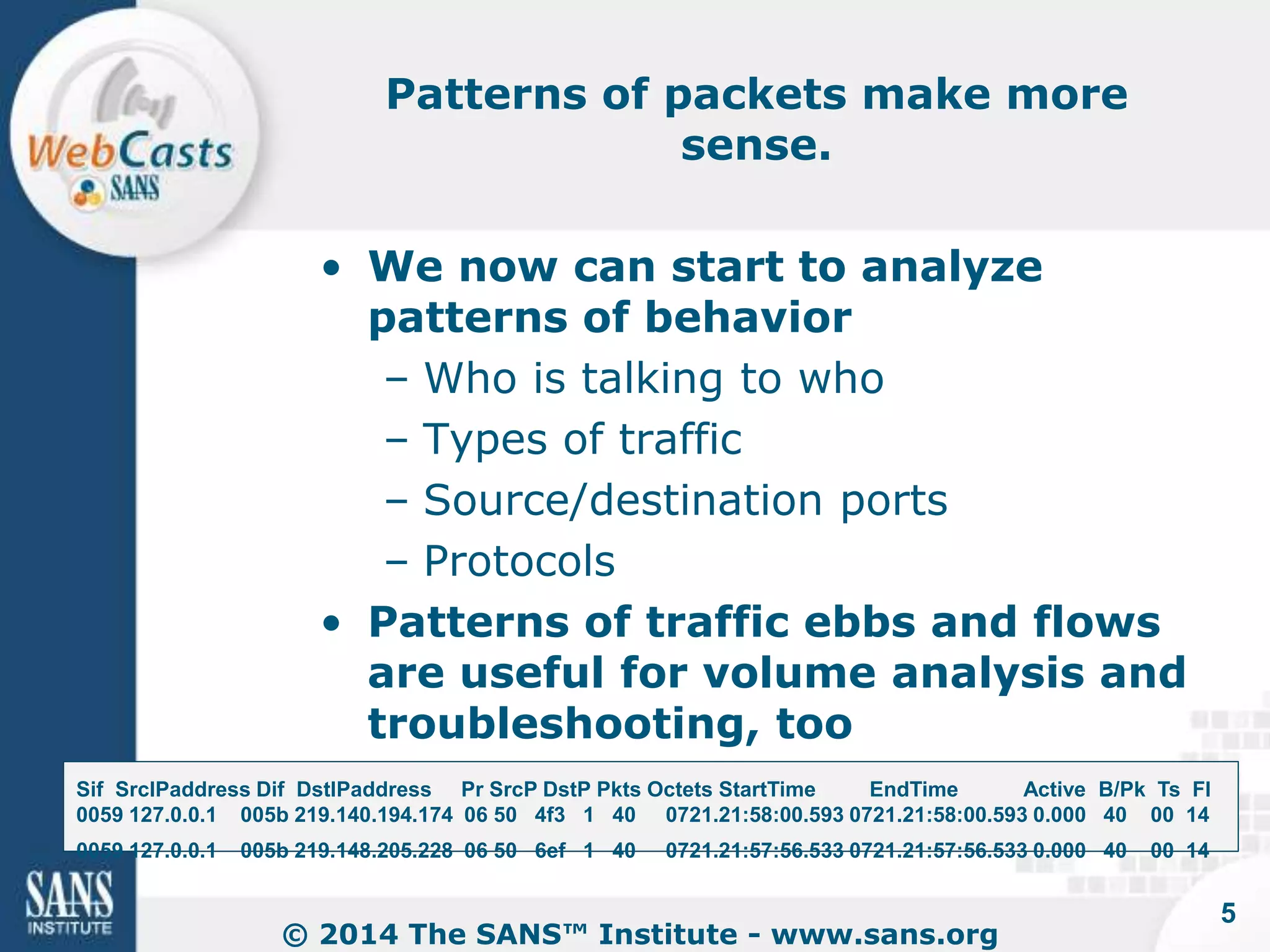
The document discusses the evolution of Intrusion Detection Systems (IDS) and Intrusion Prevention Systems (IPS), emphasizing the importance of context in threat detection. It highlights the transition from passive detection to proactive prevention, the necessity of integrating various data sources to build context, and the significance of behavioral analysis in improving alert accuracy. Ultimately, it suggests that modern IDS require ongoing tuning and correlation with threat intelligence for effective security management.

![Event Data, and Lots of It
© 2014 The SANS™ Institute - www.sans.org
8
[**] SQL Injection [**]
10/30-20:38:56.753145 192.168.1.52:2360 -> 192.168.1.61:80
TCP TTL:128 TOS:0x0 ID:22376 IpLen:20 DgmLen:809 DF
***AP*** Seq: 0xF69FDBE3 Ack: 0x3D5C8C4 Win: 0xF991 TcpLen: 20
=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=
Traditional IDS and IPS alerts
are
often overwhelming](https://image.slidesharecdn.com/2014-141203162350-conversion-gate02/75/The-Evolution-of-IDS-Why-Context-is-Key-8-2048.jpg)